ASA/PIX: Exemplo de Configuração de Endereçamento de Cliente VPN IPsec Usando Servidor DHCP com ASDM
Contents
Introdução
Este documento descreve como configurar o Cisco 5500 Series Adaptive Security Appliance (ASA) para fazer com que o servidor DHCP forneça o endereço IP do cliente para todos clientes VPN utilizando o Adaptive Security Device Manager (ASDM) ou a CLI. O ASDM oferece gerenciamento de segurança de nível mundial e monitoramento através de uma interface de gerenciamento baseada na Web intuitiva e fácil de usar. Quando a configuração de roteador Cisco estiver concluída, ela pode ser verificada usando o Cisco VPN Client.
Consulte Exemplo de Configuração de Autenticação do PIX/ASA 7.x e do Cisco VPN Client 4.x com IAS RADIUS (Contra o Ative Diretory) do Windows 2003 para configurar a conexão VPN de acesso remoto entre um Cisco VPN Client (4.x para Windows) e o PIX 500 Series Security Appliance 7.x. O usuário remoto do VPN Client autentica no Ative Diretory usando um servidor RADIUS do Microsoft Windows 2003 Internet Authentication Service (IAS).
Consulte Exemplo de Configuração do PIX/ASA 7.x e do Cisco VPN Client 4.x for Cisco Secure ACS Authentication para configurar uma conexão VPN de acesso remoto entre um Cisco VPN Client (4.x para Windows) e o PIX 500 Series Security Appliance 7.x usando um Cisco Secure Access Control Server (ACS versão 3.2) para autenticação estendida (Xauth).
Pré-requisitos
Requisitos
Este documento pressupõe que o ASA esteja totalmente operacional e configurado para permitir que o Cisco ASDM ou CLI faça alterações de configuração.
Observação: consulte Permitindo o Acesso HTTPS para ASDM ou PIX/ASA 7.x: Exemplo de configuração de SSH na interface interna e externa para permitir que o dispositivo seja configurado remotamente pelo ASDM ou Secure Shell (SSH).
Componentes Utilizados
As informações neste documento são baseadas nestas versões de software e hardware:
-
Software Cisco Adaptive Security Appliance versão 7.x ou posterior
-
Adaptive Security Device Manager versão 5.x e posterior
-
Cisco VPN Client versão 4.x e posterior
As informações neste documento foram criadas a partir de dispositivos em um ambiente de laboratório específico. Todos os dispositivos utilizados neste documento foram iniciados com uma configuração (padrão) inicial. Se a sua rede estiver ativa, certifique-se de que entende o impacto potencial de qualquer comando.
Produtos Relacionados
Essa configuração também pode ser usada com o Cisco PIX Security Appliance Versão 7.x ou posterior.
Conventions
Consulte as Convenções de Dicas Técnicas da Cisco para obter mais informações sobre convenções de documentos.
Informações de Apoio
Os VPNs de Acesso Remoto atendem ao requisito de força de trabalho móvel para conectar com segurança a rede da organização. Os usuários móveis podem configurar uma conexão segura usando o software do VPN Client instalado em seus PCs. O VPN Client inicia uma conexão com um dispositivo de site central configurado para aceitar essas solicitações. Neste exemplo, o dispositivo de local central é um ASA 5500 Series Adaptive Security Appliance que usa mapas de criptografia dinâmicos.
No gerenciamento de endereços do Security Appliance, temos que configurar endereços IP que conectam um cliente a um recurso na rede privada, através do túnel, e permitir que o cliente funcione como se estivesse diretamente conectado à rede privada. Além disso, estamos lidando apenas com os endereços IP privados que são atribuídos aos clientes. Os endereços IP atribuídos a outros recursos na sua rede privada fazem parte das suas responsabilidades de administração de rede, não do gerenciamento de VPN. Portanto, quando os endereços IP são discutidos aqui, queremos dizer aqueles endereços IP disponíveis em seu esquema de endereçamento de rede privada que permitem que o cliente funcione como um ponto final de túnel.
Configurar
Nesta seção, você encontrará informações para configurar os recursos descritos neste documento.
Nota:Use a Command Lookup Tool (somente clientes registrados) para obter mais informações sobre os comandos usados nesta seção.
Diagrama de Rede
Este documento utiliza a seguinte configuração de rede:
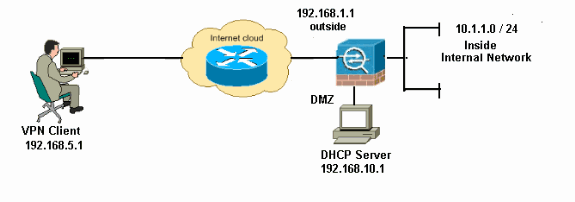
Observação: os esquemas de endereçamento IP usados nesta configuração não são legalmente roteáveis na Internet. São endereços RFC 1918 que foram usados em um ambiente de laboratório.
Configurar a VPN de Acesso Remoto (IPSec)
Procedimento ASDM
Conclua estas etapas para configurar a VPN de acesso remoto:
-
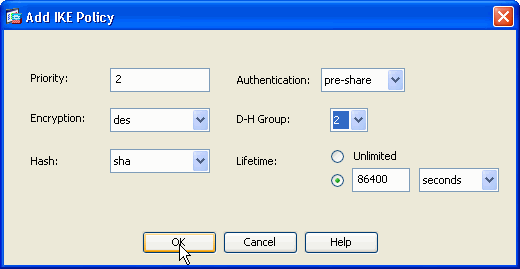
Escolha Configuration > Remote Access VPN > Network (Client) Access > Advanced > IPSec > IKE Policies > Add para criar uma política ISAKMP 2, como mostrado.
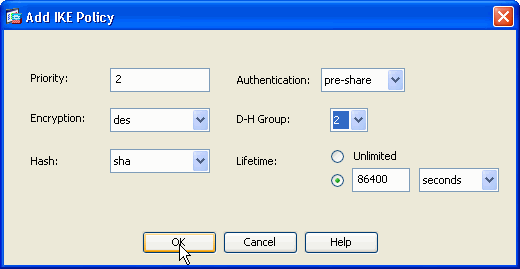
Clique em OK e em Aplicar.
-
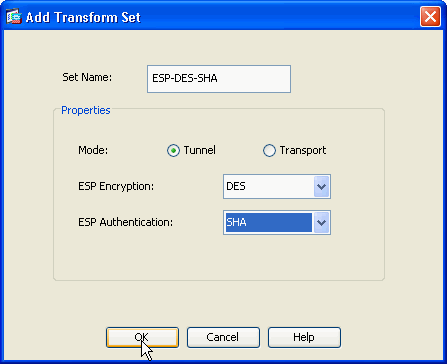
Escolha Configuration > Remote Access VPN > Network (Client) Access > Advanced > IPSec > IPSec Transform Sets > Add para criar o conjunto de transformação ESP-DES-SHA, como mostrado.
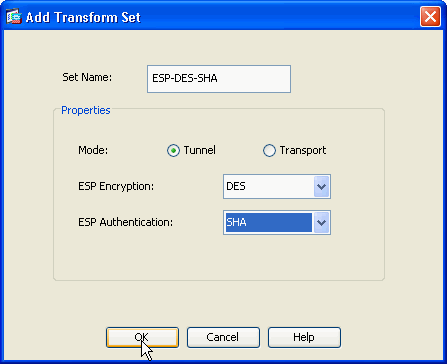
Clique em OK e em Aplicar.
-
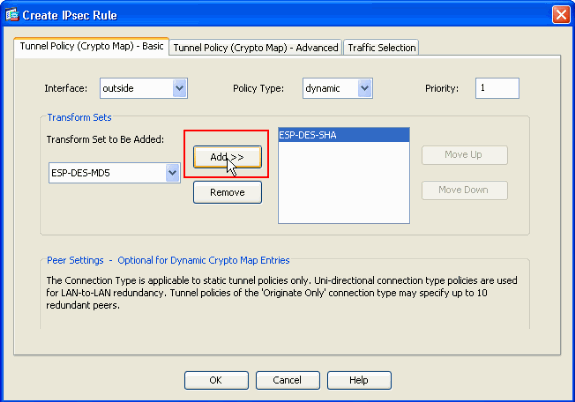
Escolha Configuration > Remote Access VPN > Network (Client) Access > Advanced > IPSec > Crypto Maps > Add para criar um mapa de criptografia com política dinâmica de prioridade 1, como mostrado.
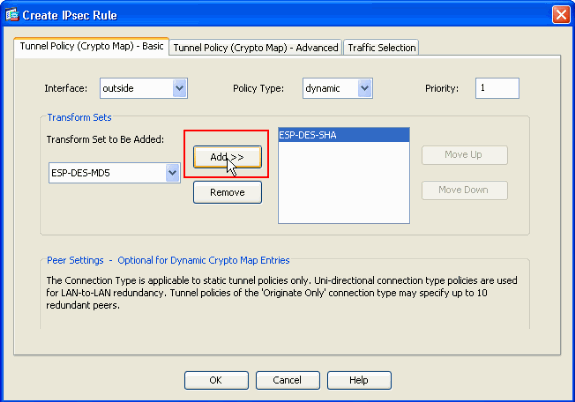
Clique em OK e em Aplicar.
-
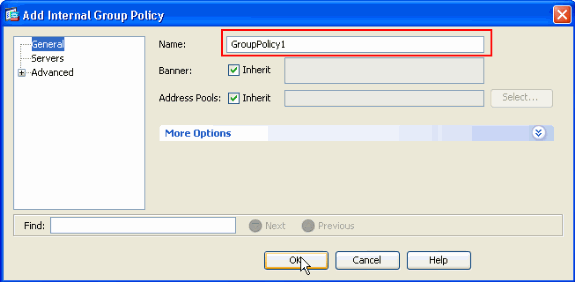
Escolha Configuration > Remote Access VPN > Network (Client) Access > Advanced > Group Policies > Add>Internal Group Policies para criar uma política de grupo (por exemplo GroupPolicy1), como mostrado.
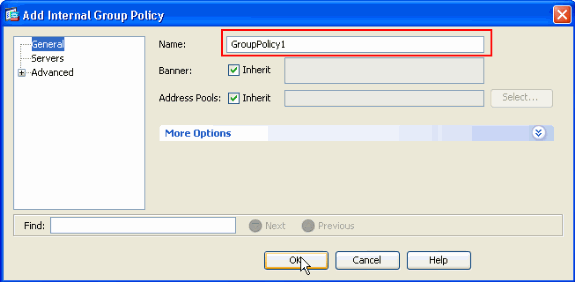
Clique em OK e em Aplicar.
-
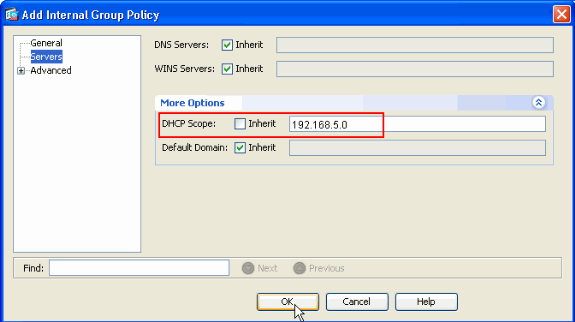
Escolha Configuration > Remote Access VPN > Network (Client) Access > Advanced > Group Policies > Add>Internal Group Policies>Servers>> para configurar o DHCP Scope para que os usuários do cliente VPN sejam atribuídos dinamicamente.
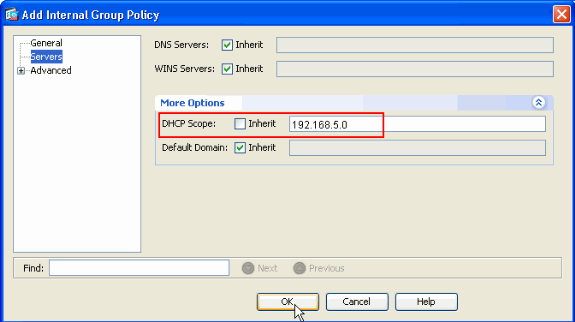
Clique em OK e em Aplicar.
Observação: a configuração do escopo DHCP é opcional. Consulte Configuração do Endereçamento DHCP para obter mais informações.
-
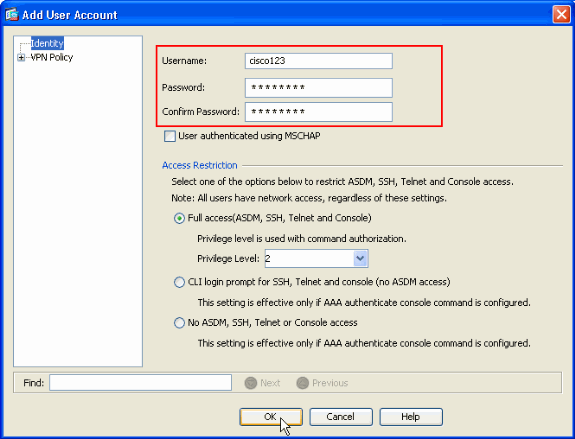
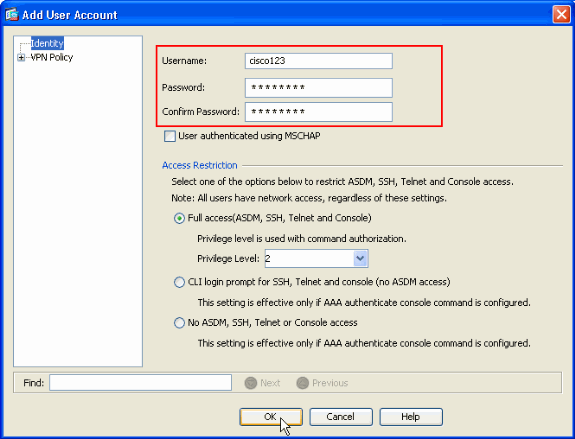
Selecione Configuration > Remote Access VPN > AAA Setup > Local Users > Add para criar a conta de usuário (por exemplo, username - cisco123 e Password - cisco123) para acesso ao cliente VPN.
-
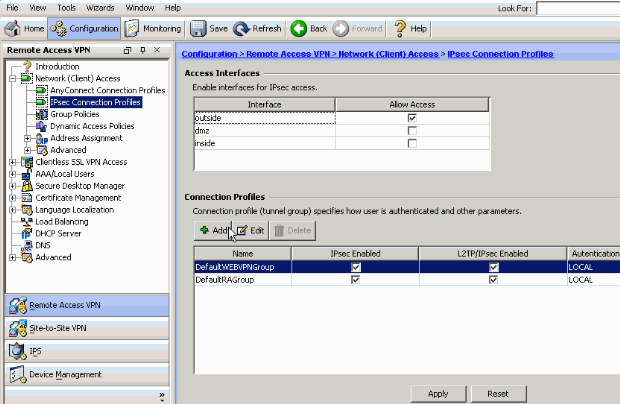
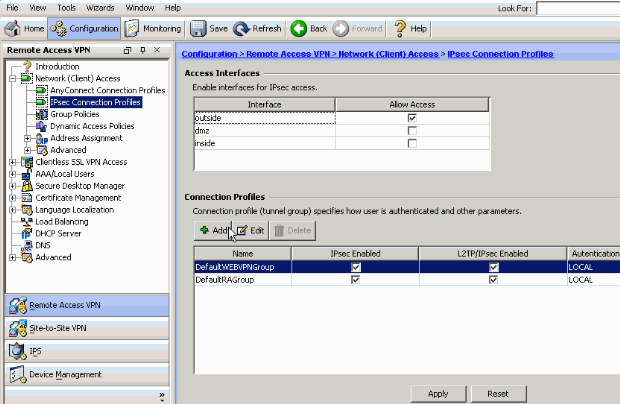
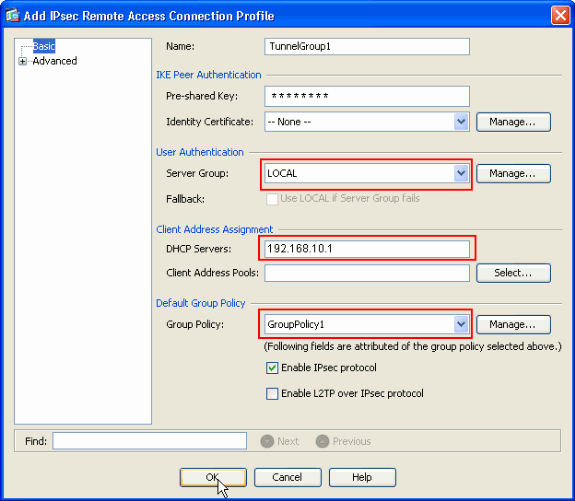
Escolha Configuration > Remote Access VPN > Network (Client) Access > IPSec Connection Profiles > Add> para adicionar um grupo de túneis (por exemplo, TunnelGroup1 e a chave pré-compartilhada como cisco123), como mostrado.
-
Na guia Basic, escolha o grupo de servidores como LOCAL para o campo User Authentication.
-
Escolha Group policy1 como a Política de grupo para o campo Default Group Policy.
-
Forneça o endereço IP do servidor DHCP no espaço fornecido para Servidores DHCP.
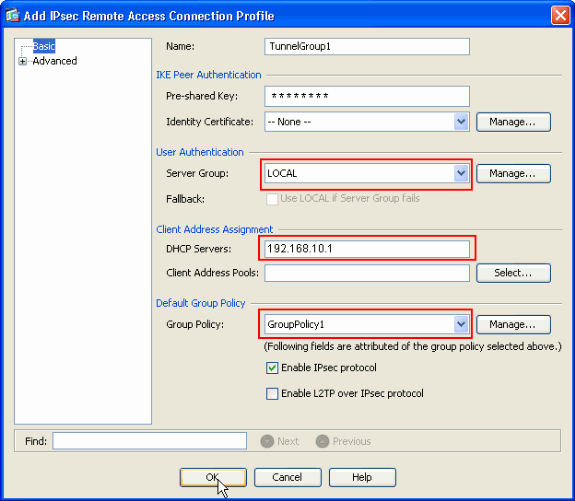
Click OK.
-
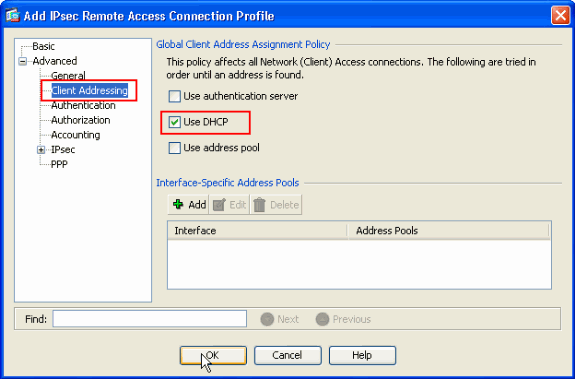
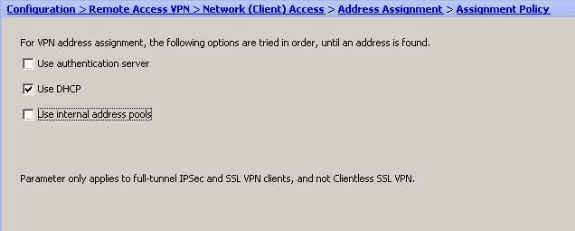
-
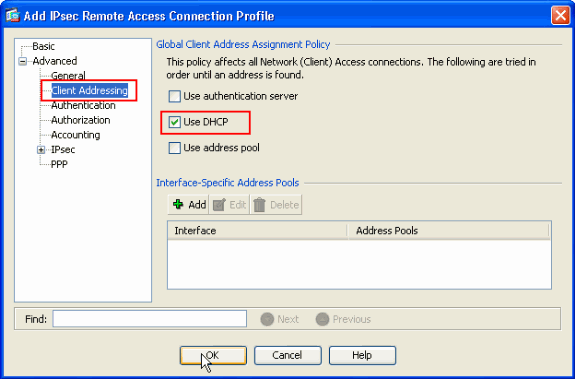
Escolha Advanced > Client Addressing > e marque a caixa de seleção Use DHCP para que o servidor DHCP atribua um endereço IP aos clientes VPN.
Observação: certifique-se de desmarcar as caixas de seleção para Usar servidor de autenticação e Usar pool de endereços.
Configuração do ASDM 6.x
A mesma configuração do ASDM funciona bem com a versão 6.x do ASDM, exceto por algumas pequenas modificações em termos de caminhos do ASDM. Os caminhos do ASDM para determinados campos tinham uma variação do ASDM versão 6.2 e posterior. As modificações, juntamente com os caminhos existentes, estão listadas abaixo. Aqui, as imagens gráficas não são anexadas nos casos em que permanecem as mesmas para todas as principais versões do ASDM.
-
Configuração > VPN de acesso remoto > Acesso à rede (cliente) > Avançado > IPSec > Políticas IKE > Adicionar
-
Configuração > VPN de acesso remoto > Acesso à rede (cliente) > Avançado > IPSec > Conjuntos de transformação IPSec > Adicionar
-
Configuração > VPN de Acesso Remoto > Acesso à Rede (Cliente) > Avançado > IPSec > Mapas de Criptografia > Adicionar
-
Escolha Configuration > Remote Access VPN > Network (Client) Access > Group Policies > Add > Internal Group Policies
-
Escolha Configuration > Remote Access VPN > Network (Client) Access > Group Policies > Add > Internal Group Policies > Servers
-
Selecione Configuration > Remote Access VPN > AAA Setup/Local Users > Local Users > Add
-
Configuração > VPN de acesso remoto > Acesso à rede (cliente) > Perfis de conexão IPSec > Adicionar
-
Selecione Configuration > Remote Access VPN > Network (Client) Access > Address Assignment > Assignment Policy (Configuração > VPN de acesso remoto > Acesso à rede (cliente) > Address Assignment Policy (Atribuição de endereço) > Assignment Policy (Política de atribuição)
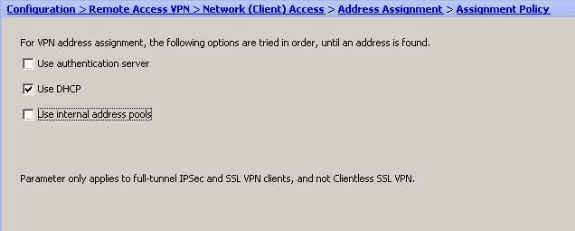
Todas essas três opções são ativadas por padrão. O Cisco ASA segue a mesma ordem para atribuir endereços aos clientes VPN. Quando você desmarca as outras duas opções, o Cisco ASA não verifica as opções do servidor aaa e do pool local. As opções ativadas por padrão podem ser verificadas pelo comando show run all | no comando vpn-add. Este é um exemplo de saída para sua referência:
vpn-addr-assign aaa vpn-addr-assign dhcp vpn-addr-assign local reuse-delay 0
Para obter mais informações sobre esse comando, consulte vpn-addr-assign .
Configurar o ASA/PIX usando CLI
Conclua estes passos para configurar o servidor DHCP para fornecer o endereço IP aos clientes VPN a partir da linha de comando. Consulte Configuração de VPNs de Acesso Remoto ou Cisco ASA 5500 Series Adaptive Security Appliances - Referências de Comandos para obter mais informações sobre cada comando usado.
| Execução da configuração no dispositivo ASA |
|---|
ASA# sh run ASA Version 8.0(2) ! !--- Specify the hostname for the Security Appliance. hostname ASA enable password 8Ry2YjIyt7RRXU24 encrypted names ! !--- Configure the outside and inside interfaces. interface Ethernet0/0 nameif inside security-level 100 ip address 10.1.1.1 255.255.255.0 ! interface Ethernet0/1 nameif outside security-level 0 ip address 192.168.1.1 255.255.255.0 ! interface Ethernet0/2 nameif DMZ security-level 50 ip address 192.168.10.2 255.255.255.0 !--- Output is suppressed. passwd 2KFQnbNIdI.2KYOU encrypted boot system disk0:/asa802-k8.bin ftp mode passive access-list 101 extended permit ip 10.1.1.0 255.255.255.0 192.168.5.0 255.255.255.0 pager lines 24 logging enable logging asdm informational mtu inside 1500 mtu outside 1500 mtu dmz 1500 no failover icmp unreachable rate-limit 1 burst-size 1 !--- Specify the location of the ASDM image for ASA to fetch the image for ASDM access. asdm image disk0:/asdm-613.bin no asdm history enable arp timeout 14400 global (outside) 1 192.168.1.5 nat (inside) 0 access-list 101 nat (inside) 1 0.0.0.0 0.0.0.0 route outside 0.0.0.0 0.0.0.0 192.168.1.2 1 timeout xlate 3:00:00 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout uauth 0:05:00 absolute dynamic-access-policy-record DfltAccessPolicy http server enable http 0.0.0.0 0.0.0.0 inside no snmp-server location no snmp-server contact snmp-server enable traps snmp authentication linkup linkdown coldstart crypto ipsec transform-set ESP-DES-SHA esp-des esp-sha-hmac crypto dynamic-map outside_dyn_map 1 set transform-set ESP-DES-SHA crypto map outside_map 1 ipsec-isakmp dynamic outside_dyn_map !--- Specifies the interface to be used with !--- the settings defined in this configuration. crypto map outside_map interface outside !--- PHASE 1 CONFIGURATION ---! !--- This configuration uses ISAKMP policy 2. !--- The configuration commands here define the Phase !--- 1 policy parameters that are used. crypto isakmp enable outside crypto isakmp policy 2 authentication pre-share encryption des hash sha group 2 lifetime 86400 no crypto isakmp nat-traversal !--- Specifies that the IP address to the vpn clients are assigned by the DHCP Server and now by AAA or the Local pool.The CLI vpn-addr-assign dhcp for VPN address assignment through DHCP Server is hidden in the CLI provided by show run command. no vpn-addr-assign aaa no vpn-addr-assign local telnet timeout 5 ssh timeout 5 console timeout 0 threat-detection basic-threat threat-detection statistics access-list ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map parameters message-length maximum 512 policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect netbios inspect rsh inspect rtsp inspect skinny inspect esmtp inspect sqlnet inspect sunrpc inspect tftp inspect sip inspect xdmcp ! service-policy global_policy global ! group-policy GroupPolicy1 internal group-policy GroupPolicy1 attributes !--- define the DHCP network scope in the group policy.This configuration is Optional dhcp-network-scope 192.168.5.0 !--- In order to identify remote access users to the Security Appliance, !--- you can also configure usernames and passwords on the device. username cisco123 password ffIRPGpDSOJh9YLq encrypted !--- Create a new tunnel group and set the connection !--- type to remote-access. tunnel-group TunnelGroup1 type remote-access !--- Define the DHCP server address to the tunnel group. tunnel-group TunnelGroup1 general-attributes default-group-policy GroupPolicy1 dhcp-server 192.168.10.1 !--- Enter the pre-shared-key to configure the authentication method. tunnel-group TunnelGroup1 ipsec-attributes pre-shared-key * prompt hostname context Cryptochecksum:e0725ca9ccc28af488ded9ee36b7822d : end ASA# |
Configuração do Cisco VPN Client
Tente se conectar ao Cisco ASA usando o Cisco VPN Client para verificar se o ASA foi configurado com êxito.
-
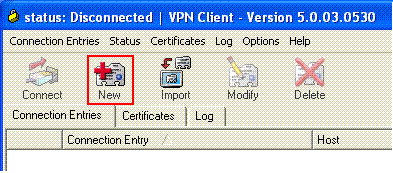
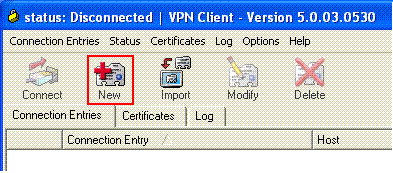
Selecione Start > Programs > Cisco Systems VPN Client > VPN Client.
-
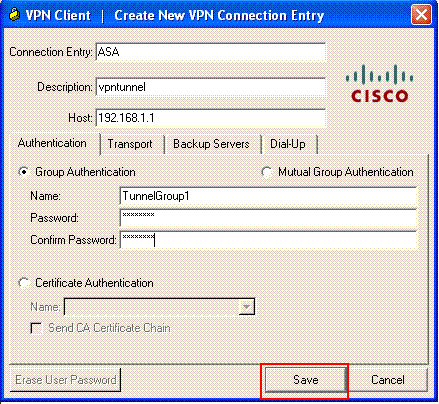
Clique em New para abrir a janela Create New VPN Connection Entry.
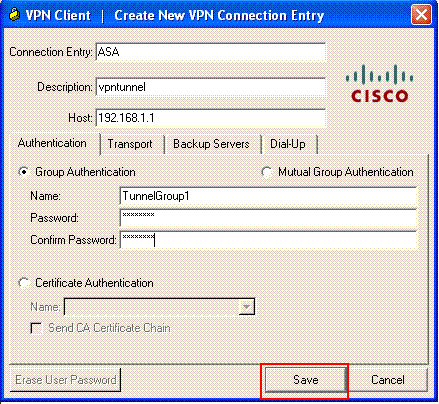
-
Preencha os detalhes da nova conexão.
Digite o nome da Entrada de Conexão juntamente com uma descrição. Insira o endereço IP externo do ASA na caixa Host. Em seguida, insira o nome (TunnelGroup1) e a senha (Pre-shared Key - cisco123) do Grupo de Túneis VPN conforme configurado no ASA. Click Save.
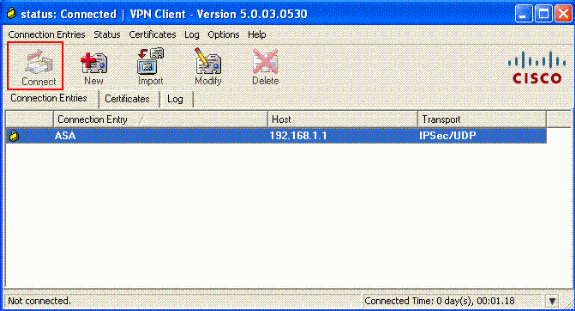
-
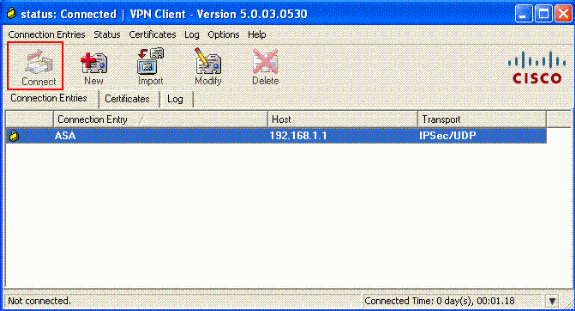
Clique na conexão que deseja usar e clique em Connect na janela principal do VPN Client.
-
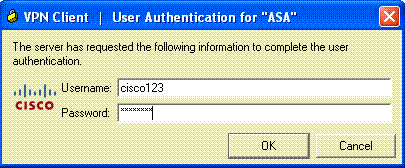
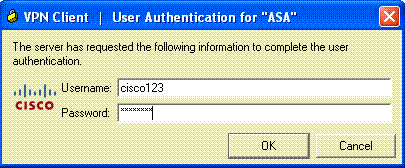
Quando solicitado, insira o nome de usuário : cisco123 e senha: cisco123 conforme configurado no ASA acima para xauth e clique em OK para se conectar à rede remota.
-
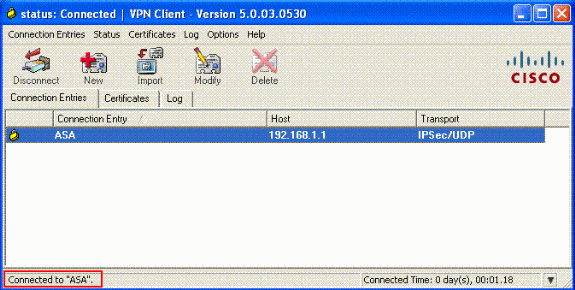
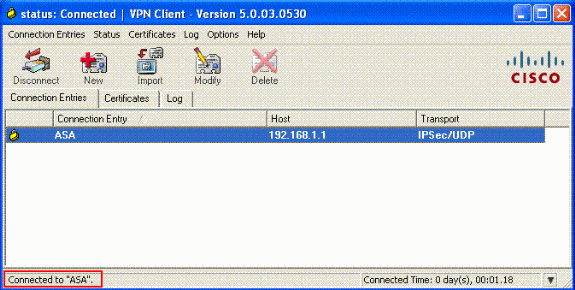
O VPN Client está conectado ao ASA no local central.
-
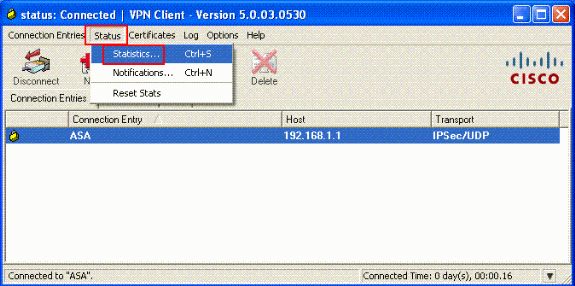
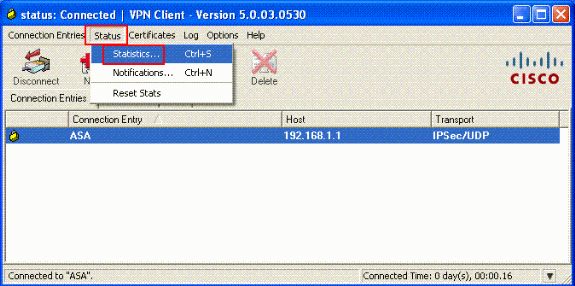
Depois que a conexão for estabelecida com êxito, selecione Statistics no menu Status para verificar os detalhes do túnel.
Verificar
comandos show
Use esta seção para confirmar se sua configuração funciona corretamente.
A Output Interpreter Tool ( somente clientes registrados) (OIT) oferece suporte a determinados comandos show. Use a OIT para exibir uma análise da saída do comando show.
-
show crypto isakmp sa — Mostra todas as Associações de Segurança (SAs) IKE atuais em um peer.
-
show crypto ipsec sa — Mostra as configurações usadas pelas SAs atuais.
ASA #show crypto ipsec sa
interface: outside
Crypto map tag: dynmap, seq num: 10, local addr: 192.168.1.1
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (192.168.5.1/255.255.255.255/0/0)
current_peer: 192.168.1.2, username: cisco123
dynamic allocated peer ip: 192.168.5.1
#pkts encaps: 55, #pkts encrypt: 55, #pkts digest: 55
#pkts decaps: 55, #pkts decrypt: 55, #pkts verify: 55
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts comp failed: 0, #pkts decomp failed: 0
#pre-frag successes: 0, #pre-frag failures: 0, #fragments created: 0
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
#send errors: 0, #recv errors: 0
local crypto endpt.: 192.168.1.1, remote crypto endpt.: 192.168.1.2
path mtu 1500, ipsec overhead 58, media mtu 1500
current outbound spi: C2C25E2B
inbound esp sas:
spi: 0x69F8C639 (1777911353)
transform: esp-des esp-md5-hmac none
in use settings ={RA, Tunnel, }
slot: 0, conn_id: 40960, crypto-map: dynmap
sa timing: remaining key lifetime (sec): 28337
IV size: 8 bytes
replay detection support: Y
outbound esp sas:
spi: 0xC2C25E2B (3267517995)
transform: esp-des esp-md5-hmac none
in use settings ={RA, Tunnel, }
slot: 0, conn_id: 40960, crypto-map: dynmap
sa timing: remaining key lifetime (sec): 28337
IV size: 8 bytes
replay detection support: Y
ASA #show crypto isakmp sa
Active SA: 1
Rekey SA: 0 (A tunnel will report 1 Active and 1 Rekey SA during rekey)
Total IKE SA: 1
1 IKE Peer: 192.168.1.2
Type : user Role : responder
Rekey : no State : AM_ACTIVE
Troubleshooting
Esta seção fornece informações que podem ser usadas para o troubleshooting da sua configuração. Um exemplo de saída de depuração também é mostrado.
Nota: Para obter mais informações sobre troubleshooting de VPN IPsec de Acesso Remoto, consulte Soluções de Troubleshooting de VPN IPSec de Acesso Remoto e L2L Mais Comuns
Cancele associações de segurança
Ao solucionar problemas, certifique-se de limpar as associações de segurança existentes depois de fazer uma alteração. No modo privilegiado do PIX, use estes comandos:
-
clear [crypto] ipsec sa — Exclui as SAs IPsec ativas. A criptografia da palavra-chave é opcional.
-
clear [crypto] isakmp sa — Exclui as SAs IKE ativas. A criptografia da palavra-chave é opcional.
Comandos para Troubleshooting
A Output Interpreter Tool ( somente clientes registrados) (OIT) oferece suporte a determinados comandos show. Use a OIT para exibir uma análise da saída do comando show.
Nota:Consulte Informações Importantes sobre Comandos de Depuração antes de usar comandos debug.
-
debug crypto ipsec 7 — Exibe as negociações de IPsec da Fase 2.
-
debug crypto isakmp 7 — Exibe as negociações ISAKMP da Fase 1.
Exemplo de saída de depuração
ASA 8.0
ASA#debug crypto isakmp 7
Jan 22 22:21:24 [IKEv1]: IP = 192.168.1.2, IKE_DECODE RECEIVED Message
(msgid=0) with payloads : HDR + SA (1) + KE (4) + NONCE (10) + ID (5) + VENDOR
(13) + VENDOR (13) + VENDOR (13) + VENDOR (13) + VENDOR (13) + NONE (0) total le
ngth : 856
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing SA payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing ke payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing ISA_KE payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing nonce payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing ID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, Received xauth V6 VID
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, Received DPD VID
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, Received Fragmentation VID
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, IKE Peer included IKE fragmenta
tion capability flags: Main Mode: True Aggressive Mode: False
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, Received NAT-Traversal ver 02 V
ID
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, processing VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: IP = 192.168.1.2, Received Cisco Unity client VID
Jan 22 22:21:24 [IKEv1]: IP = 192.168.1.2, Connection landed on tunnel_group Tun
nelGroup1
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, processin
g IKE SA payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, IKE SA Pr
oposal # 1, Transform # 13 acceptable Matches global IKE entry # 2
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing ISAKMP SA payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing ke payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing nonce payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, Generatin
g keys for Responder...
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing ID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing hash payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, Computing
hash for ISAKMP
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing Cisco Unity VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing xauth V6 VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing dpd vid payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing Fragmentation VID + extended capabilities payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, Send Alti
ga/Cisco VPN3000/Cisco ASA GW VID
Jan 22 22:21:24 [IKEv1]: IP = 192.168.1.2, IKE_DECODE SENDING Message (msgid=0)
with payloads : HDR + SA (1) + KE (4) + NONCE (10) + ID (5) + HASH (8) + VENDOR
(13) + VENDOR (13) + VENDOR (13) + VENDOR (13) + VENDOR (13) + NONE (0) total le
ngth : 368
Jan 22 22:21:24 [IKEv1]: IP = 192.168.1.2, IKE_DECODE RECEIVED Message (msgid=0)
with payloads : HDR + HASH (8) + NOTIFY (11) + VENDOR (13) + VENDOR (13) + NONE
(0) total length : 116
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, processin
g hash payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, Computing
hash for ISAKMP
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, processin
g notify payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, processin
g VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, Processin
g IOS/PIX Vendor ID payload (version: 1.0.0, capabilities: 00000408)
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, processin
g VID payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, Received
Cisco Unity client VID
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing blank hash payload
Jan 22 22:21:24 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, construct
ing qm hash payload
Jan 22 22:21:24 [IKEv1]: IP = 192.168.1.2, IKE_DECODE SENDING Message (msgid=e8a
1816d) with payloads : HDR + HASH (8) + ATTR (14) + NONE (0) total length : 68
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, IKE_DECODE RECEIVED Message (msgid=e8
a1816d) with payloads : HDR + HASH (8) + ATTR (14) + NONE (0) total length : 84
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, process_a
ttr(): Enter!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, IP = 192.168.1.2, Processin
g MODE_CFG Reply attributes.
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKEGetUserAttributes: primary DNS = cleared
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKEGetUserAttributes: secondary DNS = cleared
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKEGetUserAttributes: primary WINS = cleared
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKEGetUserAttributes: secondary WINS = cleared
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKEGetUserAttributes: IP Compression = disabled
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKEGetUserAttributes: Split Tunneling Policy = Disabled
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKEGetUserAttributes: Browser Proxy Setting = no-modify
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKEGetUserAttributes: Browser Proxy Bypass Local = disable
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, User (cisco123) authenticated.
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing blank hash payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing qm hash payload
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, IKE_DECODE SENDING Message (msgid=143
60de6) with payloads : HDR + HASH (8) + ATTR (14) + NONE (0) total length : 60
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, IKE_DECODE RECEIVED Message (msgid=14
360de6) with payloads : HDR + HASH (8) + ATTR (14) + NONE (0) total length : 56
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, process_attr(): Enter!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Processing cfg ACK attributes
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, IKE_DECODE RECEIVED Message (msgid=26
63a1dd) with payloads : HDR + HASH (8) + ATTR (14) + NONE (0) total length : 193
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, process_attr(): Enter!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Processing cfg Request attributes
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for IPV4 address!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for IPV4 net mask!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for DNS server address!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for WINS server address!
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, Received unsupported transaction mode attribute: 5
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for Banner!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for Save PW setting!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for Default Domain Name!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for Split Tunnel List!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for Split DNS!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for PFS setting!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for Client Browser Proxy Setting!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for backup ip-sec peer list!
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, Received unknown transaction mode attribute: 28684
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for Application Version!
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, Client Type: WinNT Client Application Version: 5.0.03.0530
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for FWTYPE!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for DHCP hostname for DDNS is: Wireless12
3!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, MODE_CFG: Received request for UDP Port!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Obtained IP addr (192.168.5.1) prior to initiating Mode Cfg (XAuth e
nabled)
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, Assigned private IP address 192.168.5.1 to remote user
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing blank hash payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Send Client Browser Proxy Attributes!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Browser Proxy set to No-Modify. Browser Proxy data will NOT be inclu
ded in the mode-cfg reply
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing qm hash payload
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, IKE_DECODE SENDING Message (msgid=266
3a1dd) with payloads : HDR + HASH (8) + ATTR (14) + NONE (0) total length : 158
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Delay Quick Mode processing, Cert/Trans Exch/RM DSID in progress
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Resume Quick Mode processing, Cert/Trans Exch/RM DSID completed
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, PHASE 1 COMPLETED
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, Keep-alive type for this connection:
DPD
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Starting P1 rekey timer: 950 seconds.
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, sending notify message
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing blank hash payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing qm hash payload
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, IKE_DECODE SENDING Message (msgid=f44
35669) with payloads : HDR + HASH (8) + NOTIFY (11) + NONE (0) total length : 84
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, IKE_DECODE RECEIVED Message (msgid=54
1f8e43) with payloads : HDR + HASH (8) + SA (1) + NONCE (10) + ID (5) + ID (5) +
NONE (0) total length : 1022
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, processing hash payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, processing SA payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, processing nonce payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, processing ID payload
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, Received remote Proxy Host data in ID Payload: Address 192.168.5.1, Proto
col 0, Port 0
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, processing ID payload
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, Received local IP Proxy Subnet data in ID Payload: Address 0.0.0.0, Mask
0.0.0.0, Protocol 0, Port 0
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, QM IsRekeyed old sa not found by addr
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, IKE Remote Peer configured for crypto map: dynmap
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, processing IPSec SA payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IPSec SA Proposal # 14, Transform # 1 acceptable Matches global IPS
ec SA entry # 10
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, IKE: requesting SPI!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKE got SPI from key engine: SPI = 0x31de01d8
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, oakley constucting quick mode
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing blank hash payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing IPSec SA payload
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, Overriding Initiator's IPSec rekeying duration from 2147483 to 28800 secon
ds
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing IPSec nonce payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing proxy ID
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Transmitting Proxy Id:
Remote host: 192.168.5.1 Protocol 0 Port 0
Local subnet: 0.0.0.0 mask 0.0.0.0 Protocol 0 Port 0
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Sending RESPONDER LIFETIME notification to Initiator
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, constructing qm hash payload
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, IKE_DECODE SENDING Message (msgid=541
f8e43) with payloads : HDR + HASH (8) + SA (1) + NONCE (10) + ID (5) + ID (5) +
NOTIFY (11) + NONE (0) total length : 176
Jan 22 22:21:31 [IKEv1]: IP = 192.168.1.2, IKE_DECODE RECEIVED Message (msgid=54
1f8e43) with payloads : HDR + HASH (8) + NONE (0) total length : 48
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, processing hash payload
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, loading all IPSEC SAs
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Generating Quick Mode Key!
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Generating Quick Mode Key!
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, Security negotiation complete for User (cisco123) Responder, Inbound SPI
= 0x31de01d8, Outbound SPI = 0x8b7597a9
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, IKE got a KEY_ADD msg for SA: SPI = 0x8b7597a9
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Pitcher: received KEY_UPDATE, spi 0x31de01d8
Jan 22 22:21:31 [IKEv1 DEBUG]: Group = TunnelGroup1, Username = cisco123, IP = 1
92.168.1.2, Starting P2 rekey timer: 27360 seconds.
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, Adding static route for client address: 192.168.5.1
Jan 22 22:21:31 [IKEv1]: Group = TunnelGroup1, Username = cisco123, IP = 192.168
.1.2, PHASE 2 COMPLETED (msgid=541f8e43)
Jan 22 22:21:41 [IKEv1]: IP = 192.168.1.2, IKE_DECODE RECEIVED Message (msgid=78
f7d3ae) with payloads : HDR + HASH (8) + NOTIFY (11) + NONE (0) total length : 8
0
ASA#debug crypto ipsec 7
!--- Deletes the old SAs.
ASA# IPSEC: Deleted inbound decrypt rule, SPI 0x7F3C985A
Rule ID: 0xD5567DB0
IPSEC: Deleted inbound permit rule, SPI 0x7F3C985A
Rule ID: 0xD4EF1DF0
IPSEC: Deleted inbound tunnel flow rule, SPI 0x7F3C985A
Rule ID: 0xD556AF60
IPSEC: Deleted inbound VPN context, SPI 0x7F3C985A
VPN handle: 0x0004678C
IPSEC: Deleted outbound encrypt rule, SPI 0xC921E280
Rule ID: 0xD517EE30
IPSEC: Deleted outbound permit rule, SPI 0xC921E280
Rule ID: 0xD5123250
IPSEC: Deleted outbound VPN context, SPI 0xC921E280
VPN handle: 0x00040AB4
!--- Creates new SAs.
ASA# IPSEC: New embryonic SA created @ 0xD4EF2390,
SCB: 0xD4EF22C0,
Direction: inbound
SPI : 0x7F3C985A
Session ID: 0x0000F000
VPIF num : 0x00000002
Tunnel type: ra
Protocol : esp
Lifetime : 240 seconds
IPSEC: New embryonic SA created @ 0xD556B118,
SCB: 0xD556B048,
Direction: outbound
SPI : 0xC921E280
Session ID: 0x0000F000
VPIF num : 0x00000002
Tunnel type: ra
Protocol : esp
Lifetime : 240 seconds
IPSEC: Completed host OBSA update, SPI 0xC921E280
IPSEC: Creating outbound VPN context, SPI 0xC921E280
Flags: 0x00000005
SA : 0xD556B118
SPI : 0xC921E280
MTU : 1500 bytes
VCID : 0x00000000
Peer : 0x00000000
SCB : 0x0133B741
Channel: 0xD4160FA8
IPSEC: Completed outbound VPN context, SPI 0xC921E280
VPN handle: 0x00040AB4
IPSEC: New outbound encrypt rule, SPI 0xC921E280
Src addr: 0.0.0.0
Src mask: 0.0.0.0
Dst addr: 192.168.5.1
Dst mask: 255.255.255.255
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 0
Use protocol: false
SPI: 0x00000000
Use SPI: false
IPSEC: Completed outbound encrypt rule, SPI 0xC921E280
Rule ID: 0xD517EE30
IPSEC: New outbound permit rule, SPI 0xC921E280
Src addr: 192.168.1.1
Src mask: 255.255.255.255
Dst addr: 192.168.1.2
Dst mask: 255.255.255.255
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 50
Use protocol: true
SPI: 0xC921E280
Use SPI: true
IPSEC: Completed outbound permit rule, SPI 0xC921E280
Rule ID: 0xD5123250
IPSEC: Completed host IBSA update, SPI 0x7F3C985A
IPSEC: Creating inbound VPN context, SPI 0x7F3C985A
Flags: 0x00000006
SA : 0xD4EF2390
SPI : 0x7F3C985A
MTU : 0 bytes
VCID : 0x00000000
Peer : 0x00040AB4
SCB : 0x0132B2C3
Channel: 0xD4160FA8
IPSEC: Completed inbound VPN context, SPI 0x7F3C985A
VPN handle: 0x0004678C
IPSEC: Updating outbound VPN context 0x00040AB4, SPI 0xC921E280
Flags: 0x00000005
SA : 0xD556B118
SPI : 0xC921E280
MTU : 1500 bytes
VCID : 0x00000000
Peer : 0x0004678C
SCB : 0x0133B741
Channel: 0xD4160FA8
IPSEC: Completed outbound VPN context, SPI 0xC921E280
VPN handle: 0x00040AB4
IPSEC: Completed outbound inner rule, SPI 0xC921E280
Rule ID: 0xD517EE30
IPSEC: Completed outbound outer SPD rule, SPI 0xC921E280
Rule ID: 0xD5123250
IPSEC: New inbound tunnel flow rule, SPI 0x7F3C985A
Src addr: 192.168.5.1
Src mask: 255.255.255.255
Dst addr: 0.0.0.0
Dst mask: 0.0.0.0
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 0
Use protocol: false
SPI: 0x00000000
Use SPI: false
IPSEC: Completed inbound tunnel flow rule, SPI 0x7F3C985A
Rule ID: 0xD556AF60
IPSEC: New inbound decrypt rule, SPI 0x7F3C985A
Src addr: 192.168.1.2
Src mask: 255.255.255.255
Dst addr: 192.168.1.1
Dst mask: 255.255.255.255
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 50
Use protocol: true
SPI: 0x7F3C985A
Use SPI: true
IPSEC: Completed inbound decrypt rule, SPI 0x7F3C985A
Rule ID: 0xD5567DB0
IPSEC: New inbound permit rule, SPI 0x7F3C985A
Src addr: 192.168.1.2
Src mask: 255.255.255.255
Dst addr: 192.168.1.1
Dst mask: 255.255.255.255
Src ports
Upper: 0
Lower: 0
Op : ignore
Dst ports
Upper: 0
Lower: 0
Op : ignore
Protocol: 50
Use protocol: true
SPI: 0x7F3C985A
Use SPI: true
IPSEC: Completed inbound permit rule, SPI 0x7F3C985A
Rule ID: 0xD4EF1DF0
VPN Client 5.0 para Windows
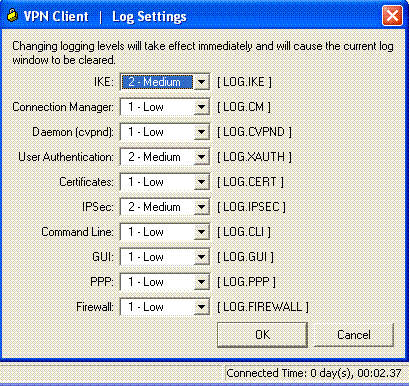
Selecione Log > Log settings para ativar os níveis de log no VPN Client.
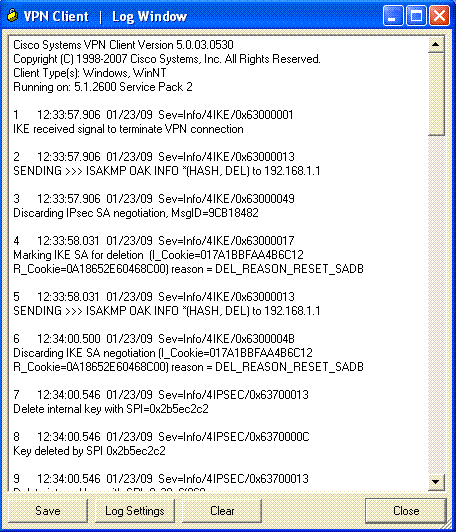
Selecione Log > Log Window para exibir as entradas de log no VPN Client.
Informações Relacionadas
- Página de suporte dos dispositivos de segurança adaptáveis Cisco ASA 5500 Series
- Referências de comandos do Cisco ASA 5500 Series Adaptive Security Appliances
- Página de suporte dos dispositivos de segurança Cisco PIX 500 Series
- Referência de Comandos dos Cisco PIX 500 Series Security Appliances
- Cisco Adaptive Security Device Manager
- Página de Suporte de Negociação IPSec/Protocolos IKE
Histórico de revisões
| Revisão | Data de publicação | Comentários |
|---|---|---|
1.0 |
23-Jan-2009
|
Versão inicial |
Contate a Cisco
- Abrir um caso de suporte

- (É necessário um Contrato de Serviço da Cisco)
 Feedback
Feedback