Security
Defend your systems and your customers. Grow your business securely.
Defend your systems and your customers. Grow your business securely.
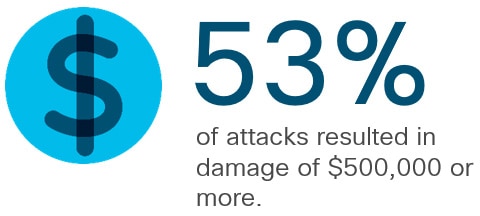
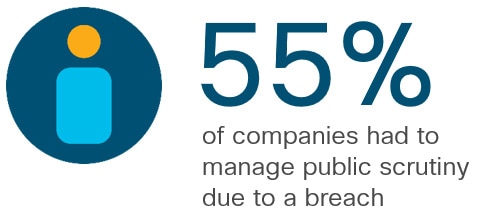
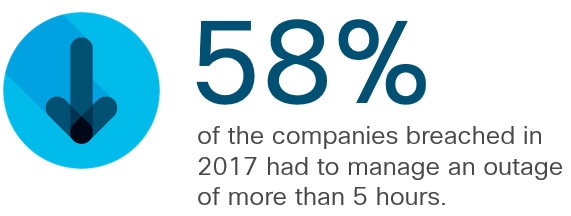
Cybercrime may cost businesses up to $2 trillion by 2019. Cyberattacks damage much more than just your IT network; they can also affect your brand reputation, your revenue and your future.
- Paolo Della Mea, Network Leader, General Electric
“… become more stable, effectively stand up to modern threats and maximise our profit.”
Sergey Prishchepa, Network Administrator, MBS (Ukraine)
“… innovate.”
Kjartan Are Vivelid, Wireless Network Engineer, IKT Adger (Norway)
- Ivan Tushev, CIO, UltraNET (Bulgaria)
“… stay alive and kicking.”
Christian Meyer, Head of Network and Security, UBP (Switzerland)
“…comply with our regulatory requirements and protect our customers' data. ”
Gareth Nicholson, Voice Engineer, Capital One (UK)
Discover how this global pharmaceutical company uses Cisco Umbrella to fight ransomware.
Under GDPR, you need to spot a breach, scope it, and report it in under 72 hours.
Learn more about threats such as WannaCry and Nyetya/ Petya and how to stop them before they get in.
Discover how our threat researchers at Talos are fighting hackers and improving IT security with threat intelligence.
Cisco Encrypted Traffic Analytics (ETA) helps you find malware within encrypted web traffic without decrypting it. Hackers have nowhere to hide.
Cisco Stealthwatch monitors network traffic in real time. It helps you spot suspicious network behaviour and speed up detection and response times.