NAS에서 LNS로 여러 홉을 수행하도록 L2TP 멀티홉을 구성
목차
소개
VPDN(Multihop Virtual Private Dialup Network)을 사용하면 L2TP LAC(Access Concentrator)에서 L2TP Network Server(LNS)로 이동하는 동안 여러 홉을 구성할 수 있습니다. 최대 4홉이 지원됩니다. 터널은 LNS(모든 hop)에서 종료되고 다음 hop 대상으로 다시 시작됩니다. 이 프로세스에서는 터널 전환을 허용합니다. ISP 간에 다중 호핑을 사용하여 도매 VPN(Access Virtual Private Network) 서비스를 제공할 수 있습니다.
이 시나리오에서는 L2F(Layer 2 Forwarding) 및 L2TP(Layer 2 Tunnel Protocol)가 모두 지원됩니다. 그러나 L2TP가 업계 표준이 되기 때문에 이 문서에서는 L2TP에 초점을 맞춥니다.
사전 요구 사항
표기 규칙
문서 규칙에 대한 자세한 내용은 Cisco 기술 팁 표기 규칙을 참조하십시오.
요구 사항
이 문서에 대한 특정 요건이 없습니다.
VPDN 프로세스에 대한 설명은 VPDN 이해를 참조하십시오.
사용되는 구성 요소
이 문서의 정보는 아래 소프트웨어 및 하드웨어 버전을 기반으로 합니다.
-
Cisco IOS® 소프트웨어 버전 12.3(6)
-
L2TP LAC(Access Concentrator): Cisco AS5400 Access Server
-
L2TP 네트워크 서버(LNS): Cisco 7200 라우터
이 문서의 정보는 특정 랩 환경의 디바이스를 토대로 작성되었습니다. 이 문서에 사용된 모든 디바이스는 초기화된(기본) 컨피그레이션으로 시작되었습니다. 라이브 네트워크에서 작업하는 경우, 사용하기 전에 모든 명령의 잠재적인 영향을 이해해야 합니다.
구성
이 섹션에는 이 문서에서 설명하는 기능을 구성하기 위한 정보가 표시됩니다.
참고: 이 문서에 사용된 명령에 대한 추가 정보를 찾으려면 명령 조회 도구(등록된 고객만 해당)를 사용합니다.
네트워크 다이어그램
이 문서에서는 아래 다이어그램에 표시된 네트워크 설정을 사용합니다.
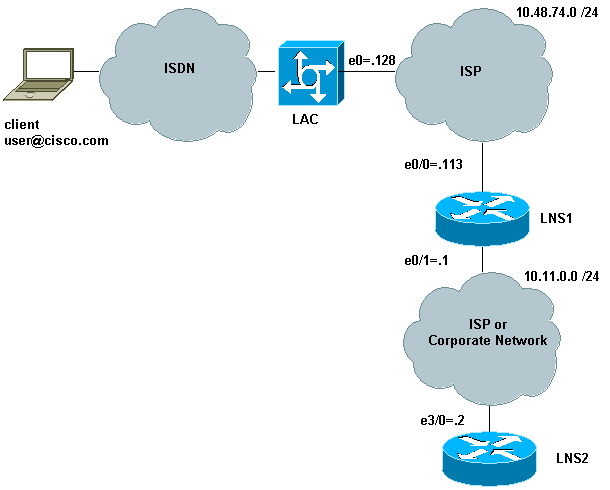
이 설정에서:
-
클라이언트는 ISDN을 사용하여 LAC에 전화를 겁니다(예: DSL을 대신 사용할 수 있음).
-
LAC는 E1 PRI(기본 속도 인터페이스)를 사용하여 통화를 수락합니다.
-
L2TP 디바이스 간에 이미 열려 있는 터널이 없습니다.
-
터널 및 세션 설정은 도메인 이름을 기반으로 합니다. 인증 또는 권한 부여를 위한 AAA 서버가 없습니다.
-
두 개의 LNS를 사용합니다.
프로세스는 다음과 같습니다.
-
클라이언트가 LAC에 전화를 겁니다. 클라이언트와 LAC는 LCP 옵션을 협상합니다. 인증 단계가 수행되며 LAC는 사용자 이름(user@cisco.com)과 비밀번호를 가져옵니다. 도메인 이름(이 예에서는 cisco.com)에 따라 터널을 열고 LNS1에 대한 세션을 엽니다.
-
LAC와 LNS1 간에 L2TP 세션이 열리면 LNS1은 사용자 이름과 비밀번호(user@cisco.com, 비밀번호)와 함께 LAC와 클라이언트 간에 협상된 LCP 옵션을 가져옵니다.
-
LNS1에는 해당 컨피그레이션에서 동일한 도메인(cisco.com)을 가진 VPDN 그룹이 있습니다. LNS2에 대한 터널 및 세션을 엽니다. 이러한 구성이 없는 경우 클라이언트를 인증하고 IP 주소를 협상하고 경로를 설치하여 PPP 세션을 종료합니다.
-
LNS1과 LNS2 간에 L2TP 세션이 열리면 LNS2는 사용자 및 비밀번호(user@cisco.com, 비밀번호)와 함께 LAC와 클라이언트 간에 협상된 LCP 옵션을 가져옵니다. 사용자를 인증하고 IPCP를 협상하며 경로를 설치합니다.
구성
이 문서에서는 아래 표시된 구성을 사용합니다. 최소 명령 수는 여기에서 사용됩니다. 예를 들어, LAC는 세션을 종료하지 않으므로 Dialer1 또는 Group-async1 인터페이스에서 IP 주소를 구성할 필요가 없습니다. LNS1은 PPP 세션을 종료하지 않으므로 virtual-template1에는 IP 주소가 없습니다.
| LAC |
|---|
version 12.3 service timestamps debug datetime msec service timestamps log datetime msec service password-encryption ! hostname LAC ! boot-start-marker no boot startup-test boot-end-marker ! enable password 7 02050D480809 ! ! ! resource-pool disable spe default-firmware spe-firmware-2 no aaa new-model ip subnet-zero no ip domain lookup ! ip cef ! -- Enables VPDN. vpdn enable ! -- VPDN tunnel authorization is based first on the domain name ! -- (the default is DNIS). ! vpdn search-order domain ! ! -- The LAC opens an L2TP tunnel and session to 10.48.74.113 (LNS1) ! -- using the password LACLNS1 for users whose domain-name is cisco.com. vpdn-group 1 request-dialin protocol l2tp domain cisco.com initiate-to ip 10.48.74.113 l2tp tunnel password LACLNS1 ! isdn switch-type primary-net5 ! ! no voice hpi capture buffer no voice hpi capture destination ! ! controller E1 7/0 pri-group timeslots 1-31 ! interface FastEthernet0/0 ip address 10.48.74.128 255.255.255.0 duplex auto speed auto ! interface Serial7/0:15 no ip address encapsulation ppp dialer rotary-group 1 isdn switch-type primary-net5 ! interface Group-Async1 no ip address encapsulation ppp async mode interactive ppp authentication chap callin group-range 1/00 3/107 ! interface Dialer1 no ip address encapsulation ppp ppp authentication chap callin ! ip classless no ip http server ! ! voice-port 7/0:D ! line con 0 exec-timeout 0 0 line aux 0 line vty 0 4 line 1/00 1/107 modem InOut transport input all line 3/00 3/107 modem InOut transport input all ! scheduler allocate 10000 400 ! end |
| LNS1 |
|---|
version 12.3 service timestamps debug datetime msec service timestamps log datetime msec no service password-encryption ! hostname LNS1 ! boot-start-marker boot-end-marker ! enable password cisco ! clock timezone CET 1 no aaa new-model ip subnet-zero ip cef ! ! no ip domain lookup ! ! -- Enables VPDN. vpdn enable ! -- Enables VPDN multihop. vpdn multihop ! !-- LNS1 accepts L2TP tunnel/session from the router named LAC. !-- The password LACLNS1 is used between LAC and LNS1 for authentication. !-- The virtual-template 1 is used for the PPP phase. vpdn-group FromLAC accept-dialin protocol l2tp virtual-template 1 terminate-from hostname LAC l2tp tunnel password 0 LACLNS1 ! ! -- The LNS1 opens a L2TP tunnel and session to 10.11.0.2 (LNS2) ! -- using the password LNS1LNS2 for users whose domain-name is cisco.com. vpdn-group TowardsLNS2 request-dialin protocol l2tp domain cisco.com initiate-to ip 10.11.0.2 l2tp tunnel password 0 LNS1LNS2 ! ! interface Ethernet0/0 ip address 10.48.74.113 255.255.255.0 no ip proxy-arp half-duplex ! interface Ethernet0/1 ip address 10.11.0.1 255.255.255.0 half-duplex ! interface Virtual-Template1 no ip address ppp authentication chap callin ! no ip http server ip classless ! ! dial-peer cor custom ! line con 0 exec-timeout 0 0 line aux 0 line vty 0 4 exec-timeout 0 0 password ww login ! ntp clock-period 17208915 ntp server 10.48.75.134 ! ! end |
| LNS2 |
|---|
version 12.3 service timestamps debug datetime msec service timestamps log datetime msec no service password-encryption ! hostname LNS2 ! boot-start-marker boot-end-marker ! enable password cisco ! username user@cisco.com password 0 cisco no aaa new-model ip subnet-zero ! ! ip cef ! !-- Enables VPDN. vpdn enable ! !-- LNS2 accepts L2TP tunnel/session from the router named LNS1. !-- The password LNS1LNS2 is used between LNS1 and LNS2 for authentication. !-- The virtual-template 1 is used for the PPP phase. vpdn-group FromLNS1 ! Default L2TP VPDN group accept-dialin protocol l2tp virtual-template 1 l2tp tunnel password 0 LNS1LNS2 ! ! interface Loopback0 ip address 192.168.1.1 255.255.255.0 ! interface Ethernet3/0 ip address 10.11.0.2 255.255.255.0 duplex half ! interface Virtual-Template1 ip unnumbered Loopback0 peer default ip address pool VpdnUsers ppp authentication chap callin ! ip local pool VpdnUsers 192.168.1.2 192.168.1.254 ip classless no ip http server ! ! line con 0 exec-timeout 0 0 transport preferred all transport output all stopbits 1 line aux 0 transport preferred all transport output all stopbits 1 line vty 0 4 login transport preferred all transport input all transport output all ! ! ! end |
다음을 확인합니다.
이 섹션에서는 컨피그레이션이 제대로 작동하는지 확인하는 데 사용할 수 있는 정보를 제공합니다.
일부 show 명령은 출력 인터프리터 툴 에서 지원되는데(등록된 고객만), 이 툴을 사용하면 show 명령 출력의 분석 결과를 볼 수 있습니다.
-
show vpdn - 활성 L2TP 또는 L2F 프로토콜 터널에 대한 정보와 VPDN의 메시지 식별자를 표시합니다.
-
show caller user user detail - 발신자 정보를 표시합니다.
LAC, LNS1 및 LNS2에서 이 명령을 사용한 출력은 다음과 같습니다.
LAC#show vpdn L2TP Tunnel and Session Information Total tunnels 1 sessions 1 LocID RemID Remote Name State Remote Address Port Sessions VPDN Group 18693 28416 LNS1 est 10.48.74.113 1701 1 1 LocID RemID TunID Intf Username State Last Chg Uniq ID 19 21 18693 Se7/0:3 user@cisco.com est 00:02:04 28 %No active L2F tunnels %No active PPTP tunnels LAC#
LNS1에는 2개의 터널이 있으며 각 터널에는 하나의 세션이 있습니다.
LNS1#show vpdn L2TP Tunnel and Session Information Total tunnels 2 sessions 2 LocID RemID Remote Name State Remote Address Port Sessions VPDN Group 28416 18693 LAC est 10.48.74.128 1701 1 FromLAC LocID RemID TunID Intf Username State Last Chg Uniq ID 21 19 28416 SSS Circuit user@cisco.com est 00:02:25 13 LocID RemID Remote Name State Remote Address Port Sessions VPDN Group 30255 35837 LNS2 est 10.11.0.2 1701 1 TowardsLNS2 LocID RemID TunID Intf Username State Last Chg Uniq ID 22 9 30255 SSS Circuit user@cisco.com est 00:02:25 13 %No active L2F tunnels %No active PPTP tunnels LNS1#
LNS2#show vpdn
L2TP Tunnel and Session Information Total tunnels 1 sessions 1
LocID RemID Remote Name State Remote Address Port Sessions VPDN Group
35837 30255 LNS1 est 10.11.0.1 1701 1 FromLNS1
LocID RemID TunID Intf Username State Last Chg Uniq ID
9 22 35837 Vi2.1 user@cisco.com est 00:03:22 8
%No active L2F tunnels
%No active PPTP tunnels
LNS2#
LNS2#show caller user user@cisco.com detail
User: user@cisco.com, line Vi2.1, service PPPoVPDN
Connected for 00:03:33, Idle for 00:00:58
Timeouts: Limit Remaining Timer Type
- - -
PPP: LCP Open, CHAP (<-), IPCP
LCP: -> peer, AuthProto, MagicNumber
<- peer, MagicNumber, EndpointDisc
NCP: Open IPCP
IPCP: <- peer, Address
-> peer, Address
IP: Local 192.168.1.1, remote 192.168.1.2
Counts: 56 packets input, 2562 bytes
57 packets output, 2570 bytes
LNS2#
문제 해결
이 섹션에서는 컨피그레이션 문제를 해결하는 데 사용할 수 있는 정보를 제공합니다.
문제 해결 명령
일부 show 명령은 출력 인터프리터 툴 에서 지원되는데(등록된 고객만), 이 툴을 사용하면 show 명령 출력의 분석 결과를 볼 수 있습니다.
참고: debug 명령을 실행하기 전에 디버그 명령에 대한 중요 정보를 참조하십시오.
LAC의 문제 해결 명령
-
debug isdn q931 - 로컬 라우터(사용자측)와 네트워크 간의 ISDN 네트워크 연결(레이어 3)의 통화 설정 및 해제 정보를 표시합니다.
-
debug vpdn event - VPDN에 대한 일반 터널 설정 또는 종료의 일부인 L2TP 오류 및 이벤트를 표시합니다.
-
debug vpdn 오류 - L2TPv3(Layer 2 Tunnel Protocol Version 3) 및 주변 레이어 2 터널링 인프라의 문제를 해결합니다.
-
debug vpdn l2x-events - 프로토콜별 조건에서 발생한 이벤트를 표시합니다.
-
vpdn l2x-errors - 프로토콜별 조건에서 발생하는 오류를 표시합니다.
-
debug ppp negotiation - 클라이언트가 PPP 협상을 통과하는지 표시합니다. 어떤 옵션(예: 콜백 또는 MLP)과 협상 중인 프로토콜(예: IP 및 IPX)을 확인할 수 있습니다.
LNS1의 문제 해결 명령
-
디버그 vpdn 이벤트
-
디버그 vpdn 오류
-
디버그 vpdn l2x 이벤트
-
vpdn l2x-erro
-
디버그 ppp 협상
-
debug vtemplate error - 가상 액세스 인터페이스가 가상 템플릿에서 복제될 때부터 통화가 종료될 때 가상 액세스 인터페이스가 중단될 때까지 가상 액세스 인터페이스에 대한 복제 정보를 표시합니다.
-
debug vtemplate event - 가상 액세스 인터페이스가 가상 템플릿에서 복제될 때부터 통화가 종료될 때 가상 액세스 인터페이스가 중단될 때까지 가상 액세스 인터페이스에 대한 복제 정보를 표시합니다.
LNS2의 문제 해결 명령
LNS1과 동일하지만 다음 명령을 추가로 사용하면 됩니다.
-
debug ip peer - 주소 활동을 표시하고 풀 그룹을 정의할 때 추가 출력을 포함합니다.
디버그 출력 - LAC
LAC의 디버그 출력은 다음과 같습니다.
LAC#
*Apr 23 08:55:23.579: ISDN Se7/0:15 Q931: RX <- SETUP pd = 8 callref = 0x256F
Sending Complete
Bearer Capability i = 0x8890
Standard = CCITT
Transer Capability = Unrestricted Digital
Transfer Mode = Circuit
Transfer Rate = 64 kbit/s
Channel ID i = 0xA18384
Preferred, Channel 4
Calling Party Number i = 0xA1, '8101'
Plan:ISDN, Type:National
Called Party Number i = 0x81, '7070'
Plan:ISDN, Type:Unknown
Locking Shift to Codeset 6
Codeset 6 IE 0x28 i = 'TAC BRI 8101'
*Apr 23 08:55:23.583: ISDN Se7/0:15 Q931: TX -> CALL_PROC pd = 8 callref = 0xA56F
Channel ID i = 0xA98384
Exclusive, Channel 4
*Apr 23 08:55:23.583: ISDN Se7/0:15 Q931: TX -> CONNECT pd = 8 callref = 0xA56F
Channel ID i = 0xA98384
Exclusive, Channel 4
*Apr 23 08:55:23.583: Se7/0:3 PPP: Using dialer call direction
*Apr 23 08:55:23.583: Se7/0:3 PPP: Treating connection as a callin
*Apr 23 08:55:23.583: Se7/0:3 PPP: Phase is ESTABLISHING, Passive Open
*Apr 23 08:55:23.583: Se7/0:3 LCP: State is Listen
*Apr 23 08:55:23.607: ISDN Se7/0:15 Q931: RX <- CONNECT_ACK pd = 8
callref = 0x256F
*Apr 23 08:55:23.695: Se7/0:3 LCP: I CONFREQ [Listen] id 180 len 31
*Apr 23 08:55:23.695: Se7/0:3 LCP: MagicNumber 0x9028FFED (0x05069028FFED)
*Apr 23 08:55:23.695: Se7/0:3 LCP: MRRU 1524 (0x110405F4)
*Apr 23 08:55:23.695: Se7/0:3 LCP: EndpointDisc 1 user@cisco.com
*Apr 23 08:55:23.695: Se7/0:3 LCP: (0x1311017573657240636973636F2E636F)
*Apr 23 08:55:23.695: Se7/0:3 LCP: (0x6D)
*Apr 23 08:55:23.695: Se7/0:3 LCP: O CONFREQ [Listen] id 1 len 15
*Apr 23 08:55:23.695: Se7/0:3 LCP: AuthProto CHAP (0x0305C22305)
*Apr 23 08:55:23.695: Se7/0:3 LCP: MagicNumber 0x050E44FB (0x0506050E44FB)
*Apr 23 08:55:23.695: Se7/0:3 LCP: O CONFREJ [Listen] id 180 len 8
*Apr 23 08:55:23.695: Se7/0:3 LCP: MRRU 1524 (0x110405F4)
*Apr 23 08:55:23.727: Se7/0:3 LCP: I CONFACK [REQsent] id 1 len 15
*Apr 23 08:55:23.727: Se7/0:3 LCP: AuthProto CHAP (0x0305C22305)
*Apr 23 08:55:23.727: Se7/0:3 LCP: MagicNumber 0x050E44FB (0x0506050E44FB)
*Apr 23 08:55:23.751: Se7/0:3 LCP: I CONFREQ [ACKrcvd] id 181 len 27
*Apr 23 08:55:23.751: Se7/0:3 LCP: MagicNumber 0x9028FFED (0x05069028FFED)
*Apr 23 08:55:23.751: Se7/0:3 LCP: EndpointDisc 1 user@cisco.com
*Apr 23 08:55:23.751: Se7/0:3 LCP: (0x1311017573657240636973636F2E636F)
*Apr 23 08:55:23.751: Se7/0:3 LCP: (0x6D)
*Apr 23 08:55:23.751: Se7/0:3 LCP: O CONFACK [ACKrcvd] id 181 len 27
*Apr 23 08:55:23.751: Se7/0:3 LCP: MagicNumber 0x9028FFED (0x05069028FFED)
*Apr 23 08:55:23.751: Se7/0:3 LCP: EndpointDisc 1 user@cisco.com
*Apr 23 08:55:23.751: Se7/0:3 LCP: (0x1311017573657240636973636F2E636F)
*Apr 23 08:55:23.751: Se7/0:3 LCP: (0x6D)
*Apr 23 08:55:23.751: Se7/0:3 LCP: State is Open
*Apr 23 08:55:23.751: Se7/0:3 PPP: Phase is AUTHENTICATING, by this end
*Apr 23 08:55:23.751: Se7/0:3 CHAP: O CHALLENGE id 1 len 24 from "LAC"
*Apr 23 08:55:23.803: Se7/0:3 CHAP: I RESPONSE id 1 len 35 from "user@cisco.com"
*Apr 23 08:55:23.803: Se7/0:3 PPP: Phase is FORWARDING, Attempting Forward
*Apr 23 08:55:23.807: Tnl/Sn 18693/19 L2TP: Session FS enabled
*Apr 23 08:55:23.807: Tnl/Sn 18693/19 L2TP: Session state change
from idle to wait-for-tunnel
*Apr 23 08:55:23.807: Se7/0:3 Tnl/Sn 18693/19 L2TP: Create session
*Apr 23 08:55:23.807: Tnl 18693 L2TP: SM State idle
*Apr 23 08:55:23.807: Tnl 18693 L2TP: O SCCRQ
*Apr 23 08:55:23.807: Tnl 18693 L2TP: Control channel retransmit delay
set to 1 seconds
*Apr 23 08:55:23.807: Tnl 18693 L2TP: Tunnel state change from idle to
wait-ctl-reply
*Apr 23 08:55:23.807: Tnl 18693 L2TP: SM State wait-ctl-reply
*Apr 23 08:55:23.815: Tnl 18693 L2TP: I SCCRP from LNS1
*Apr 23 08:55:23.815: Tnl 18693 L2TP: Got a challenge from remote peer, LNS1
*Apr 23 08:55:23.815: Tnl 18693 L2TP: Got a response from remote peer, LNS1
*Apr 23 08:55:23.815: Tnl 18693 L2TP: Tunnel Authentication success
*Apr 23 08:55:23.815: Tnl 18693 L2TP: Tunnel state change from
wait-ctl-reply to established
*Apr 23 08:55:23.815: Tnl 18693 L2TP: O SCCCN to LNS1 tnlid 28416
*Apr 23 08:55:23.815: Tnl 18693 L2TP: Control channel retransmit
delay set to 1 seconds
*Apr 23 08:55:23.815: Tnl 18693 L2TP: SM State established
*Apr 23 08:55:23.815: Se7/0:3 Tnl/Sn 18693/19 L2TP: O ICRQ to LNS1 28416/0
*Apr 23 08:55:23.815: Se7/0:3 Tnl/Sn 18693/19 L2TP: Session state change
from wait-for-tunnel to wai
t-reply
*Apr 23 08:55:23.831: Se7/0:3 Tnl/Sn 18693/19 L2TP: O ICCN to LNS1 28416/21
*Apr 23 08:55:23.831: Tnl 18693 L2TP: Control channel retransmit delay
set to 1 seconds
*Apr 23 08:55:23.831: Se7/0:3 Tnl/Sn 18693/19 L2TP: Session state change
from wait-reply to establis
hed
*Apr 23 08:55:23.831: Se7/0:3 Tnl/Sn 18693/19 L2TP: VPDN session up
*Apr 23 08:55:23.831: Se7/0:3 PPP: Phase is FORWARDED, Session Forwarded
*Apr 23 08:55:23.831: Se7/0:3 PPP: Process pending packets
LAC#
디버그 출력 - LNS1
LNS1의 디버그 출력은 다음과 같습니다.
LNS1# .Apr 23 08:57:08.900: L2TP: I SCCRQ from LAC tnl 18693 .Apr 23 08:57:08.900: Tnl 28416 L2TP: Got a challenge in SCCRQ, LAC .Apr 23 08:57:08.900: Tnl 28416 L2TP: New tunnel created for remote LAC, address 10.48.74.128 .Apr 23 08:57:08.904: Tnl 28416 L2TP: O SCCRP to LAC tnlid 18693 .Apr 23 08:57:08.904: Tnl 28416 L2TP: Control channel retransmit delay set to 1 seconds .Apr 23 08:57:08.904: Tnl 28416 L2TP: Tunnel state change from idle to wait-ctl-reply .Apr 23 08:57:08.908: Tnl 28416 L2TP: I SCCCN from LAC tnl 18693 .Apr 23 08:57:08.908: Tnl 28416 L2TP: Got a Challenge Response in SCCCN from LAC .Apr 23 08:57:08.912: Tnl 28416 L2TP: Tunnel Authentication success .Apr 23 08:57:08.912: Tnl 28416 L2TP: Tunnel state change from wait-ctl-reply to established .Apr 23 08:57:08.912: Tnl 28416 L2TP: SM State established .Apr 23 08:57:08.912: Tnl 28416 L2TP: I ICRQ from LAC tnl 18693 .Apr 23 08:57:08.916: Tnl/Sn 28416/21 L2TP: Session FS enabled .Apr 23 08:57:08.916: Tnl/Sn 28416/21 L2TP: Session state change from idle to wait-connect .Apr 23 08:57:08.916: Tnl/Sn 28416/21 L2TP: New session created .Apr 23 08:57:08.916: Tnl/Sn 28416/21 L2TP: O ICRP to LAC 18693/19 .Apr 23 08:57:08.920: Tnl 28416 L2TP: Control channel retransmit delay set to 1 seconds .Apr 23 08:57:08.924: Tnl/Sn 28416/21 L2TP: I ICCN from LAC tnl 18693, cl 19 .Apr 23 08:57:08.924: user@cisco.com Tnl/Sn 28416/21 L2TP: Session state change from wait-connect to wait-for-service-selection .Apr 23 08:57:08.932: ppp13 PPP: Phase is ESTABLISHING .Apr 23 08:57:08.932: ppp13 LCP: I FORCED rcvd CONFACK len 11 .Apr 23 08:57:08.932: ppp13 LCP: AuthProto CHAP (0x0305C22305) .Apr 23 08:57:08.936: ppp13 LCP: MagicNumber 0x050E44FB (0x0506050E44FB) .Apr 23 08:57:08.936: ppp13 LCP: I FORCED sent CONFACK len 23 .Apr 23 08:57:08.936: ppp13 LCP: MagicNumber 0x9028FFED (0x05069028FFED) .Apr 23 08:57:08.936: ppp13 LCP: EndpointDisc 1 user@cisco.com .Apr 23 08:57:08.936: ppp13 LCP: (0x1311017573657240636973636F2E636F) .Apr 23 08:57:08.936: ppp13 LCP: (0x6D) .Apr 23 08:57:08.940: ppp13 PPP: Phase is FORWARDING, Attempting Forward .Apr 23 08:57:08.948: Tnl/Sn 30255/22 L2TP: Session FS enabled .Apr 23 08:57:08.952: Tnl/Sn 30255/22 L2TP: Session state change from idle to wait-for-tunnel .Apr 23 08:57:08.952: uid:13 Tnl/Sn 30255/22 L2TP: Create session .Apr 23 08:57:08.952: Tnl 30255 L2TP: SM State idle .Apr 23 08:57:08.952: Tnl 30255 L2TP: O SCCRQ .Apr 23 08:57:08.956: Tnl 30255 L2TP: Control channel retransmit delay set to 1 seconds .Apr 23 08:57:08.956: Tnl 30255 L2TP: Tunnel state change from idle to wait-ctl-reply .Apr 23 08:57:08.956: Tnl 30255 L2TP: SM State wait-ctl-reply .Apr 23 08:57:08.960: Tnl 30255 L2TP: I SCCRP from LNS2 .Apr 23 08:57:08.960: Tnl 30255 L2TP: Got a challenge from remote peer, LNS2 .Apr 23 08:57:08.964: Tnl 30255 L2TP: Got a response from remote peer, LNS2 .Apr 23 08:57:08.964: Tnl 30255 L2TP: Tunnel Authentication success .Apr 23 08:57:08.964: Tnl 30255 L2TP: Tunnel state change from wait-ctl-reply to established .Apr 23 08:57:08.964: Tnl 30255 L2TP: O SCCCN to LNS2 tnlid 35837 .Apr 23 08:57:08.968: Tnl 30255 L2TP: Control channel retransmit delay set to 1 seconds .Apr 23 08:57:08.968: Tnl 30255 L2TP: SM State established .Apr 23 08:57:08.968: uid:13 Tnl/Sn 30255/22 L2TP: O ICRQ to LNS2 35837/0 .Apr 23 08:57:08.968: uid:13 Tnl/Sn 30255/22 L2TP: Session state change from wait-for-tunnel to wait-reply .Apr 23 08:57:08.972: uid:13 Tnl/Sn 30255/22 L2TP: O ICCN to LNS2 35837/9 .Apr 23 08:57:08.976: Tnl 30255 L2TP: Control channel retransmit delay set to 1 seconds .Apr 23 08:57:08.976: uid:13 Tnl/Sn 30255/22 L2TP: Session state change from wait-reply to established .Apr 23 08:57:08.976: uid:13 Tnl/Sn 30255/22 L2TP: VPDN session up .Apr 23 08:57:08.980: ppp13 PPP: Phase is FORWARDED, Session Forwarded .Apr 23 08:57:08.984: user@cisco.com Tnl/Sn 28416/21 L2TP: Session state change from wait-for-service-selection to established .Apr 23 08:57:08.984: user@cisco.com Tnl/Sn 28416/21 L2TP: VPDN session up .Apr 23 08:57:08.984: ppp13 PPP: Process pending ncp packets LNS1#
디버그 출력 - LNS2
LNS2의 디버그 출력은 다음과 같습니다.
LNS2# *Apr 23 08:57:59.615: L2TP: I SCCRQ from LNS1 tnl 30255 *Apr 23 08:57:59.615: Tnl 35837 L2TP: Got a challenge in SCCRQ, LNS1 *Apr 23 08:57:59.615: Tnl 35837 L2TP: New tunnel created for remote LNS1, address 10.11 .0.1 *Apr 23 08:57:59.615: Tnl 35837 L2TP: O SCCRP to LNS1 tnlid 30255 *Apr 23 08:57:59.615: Tnl 35837 L2TP: Control channel retransmit delay set to 1 seconds *Apr 23 08:57:59.615: Tnl 35837 L2TP: Tunnel state change from idle to wait-ctl-reply *Apr 23 08:57:59.623: Tnl 35837 L2TP: I SCCCN from LNS1 tnl 30255 *Apr 23 08:57:59.623: Tnl 35837 L2TP: Got a Challenge Response in SCCCN from LNS1 *Apr 23 08:57:59.623: Tnl 35837 L2TP: Tunnel Authentication success *Apr 23 08:57:59.623: Tnl 35837 L2TP: Tunnel state change from wait-ctl-reply to establ ished *Apr 23 08:57:59.623: Tnl 35837 L2TP: SM State established *Apr 23 08:57:59.627: Tnl 35837 L2TP: I ICRQ from LNS1 tnl 30255 *Apr 23 08:57:59.627: Tnl/Sn 35837/9 L2TP: Session FS enabled *Apr 23 08:57:59.627: Tnl/Sn 35837/9 L2TP: Session state change from idle to wait-conne ct *Apr 23 08:57:59.627: Tnl/Sn 35837/9 L2TP: New session created *Apr 23 08:57:59.627: Tnl/Sn 35837/9 L2TP: O ICRP to LNS1 30255/22 *Apr 23 08:57:59.627: Tnl 35837 L2TP: Control channel retransmit delay set to 1 seconds *Apr 23 08:57:59.635: Tnl/Sn 35837/9 L2TP: I ICCN from LNS1 tnl 30255, cl 22 *Apr 23 08:57:59.635: user@cisco.com Tnl/Sn 35837/9 L2TP: Session state change from wait - connect to wait-for-service-selection *Apr 23 08:57:59.635: ppp8 PPP: Phase is ESTABLISHING *Apr 23 08:57:59.635: ppp8 LCP: I FORCED rcvd CONFACK len 11 *Apr 23 08:57:59.635: ppp8 LCP: AuthProto CHAP (0x0305C22305) *Apr 23 08:57:59.635: ppp8 LCP: MagicNumber 0x050E44FB (0x0506050E44FB) *Apr 23 08:57:59.635: ppp8 LCP: I FORCED sent CONFACK len 23 *Apr 23 08:57:59.635: ppp8 LCP: MagicNumber 0x9028FFED (0x05069028FFED) *Apr 23 08:57:59.635: ppp8 LCP: EndpointDisc 1 user@cisco.com *Apr 23 08:57:59.635: ppp8 LCP: (0x1311017573657240636973636F2E636F) *Apr 23 08:57:59.635: ppp8 LCP: (0x6D) *Apr 23 08:57:59.635: ppp8 PPP: Phase is FORWARDING, Attempting Forward *Apr 23 08:57:59.639: ppp8 PPP: Phase is AUTHENTICATING, Unauthenticated User *Apr 23 08:57:59.639: ppp8 PPP: Phase is FORWARDING, Attempting Forward *Apr 23 08:57:59.639: VT[Vi2]:Sending vaccess request, id 0x73000015 *Apr 23 08:57:59.639: VT:Processing vaccess requests, 1 outstanding *Apr 23 08:57:59.639: VT:Create and clone subif, base Vi2 Vt1 *Apr 23 08:57:59.639: VT[Vi2.1]:Reuse subinterface, recycle queue size 1 *Apr 23 08:57:59.639: VT[Vi2.1]:Recycled subinterface becomes Vi2.1 *Apr 23 08:57:59.639: VT[Vi2.1]:Cloning a recycled vaccess *Apr 23 08:57:59.639: VT[Vi2.1]:Processing vaccess response, id 0x73000015, result success (1) *Apr 23 08:57:59.643: Vi2.1 Tnl/Sn 35837/9 L2TP: Virtual interface created for user@cisco.com, bandwidth 64 Kbps *Apr 23 08:57:59.643: Vi2.1 Tnl/Sn 35837/9 L2TP: VPDN session up *Apr 23 08:57:59.643: Vi2.1 Tnl/Sn 35837/9 L2TP: Session state change from wait-for-service-selection to established *Apr 23 08:57:59.643: Vi2.1 PPP: Phase is AUTHENTICATING, Authenticated User *Apr 23 08:57:59.643: Vi2.1 CHAP: O SUCCESS id 1 len 4 *Apr 23 08:57:59.643: Vi2.1 PPP: Phase is UP *Apr 23 08:57:59.643: Vi2.1 PPP: Process pending ncp packets *Apr 23 08:57:59.643: Vi2.1 IPCP: O CONFREQ [Closed] id 1 len 10 *Apr 23 08:57:59.643: Vi2.1 IPCP: Address 192.168.1.1 (0x0306C0A80101) *Apr 23 08:57:59.667: Vi2.1 IPCP: I CONFREQ [REQsent] id 125 len 10 *Apr 23 08:57:59.667: Vi2.1 IPCP: Address 0.0.0.0 (0x030600000000) *Apr 23 08:57:59.667: Vi2.1 AAA/AUTHOR/IPCP: Start. Her address 0.0.0.0, we want 0.0.0.0 *Apr 23 08:57:59.667: Vi2.1 AAA/AUTHOR/IPCP: Done. Her address 0.0.0.0, we want 0.0.0.0 *Apr 23 08:57:59.667: Vi2.1: Pools to search : VpdnUsers *Apr 23 08:57:59.667: Vi2.1: Pool VpdnUsers returned address = 192.168.1.2 *Apr 23 08:57:59.667: Vi2.1 IPCP: Pool returned 192.168.1.2 *Apr 23 08:57:59.667: Vi2.1 IPCP: O CONFNAK [REQsent] id 125 len 10 *Apr 23 08:57:59.667: Vi2.1 IPCP: Address 192.168.1.2 (0x0306C0A80102) *Apr 23 08:57:59.683: Vi2.1 IPCP: I CONFACK [REQsent] id 1 len 10 *Apr 23 08:57:59.683: Vi2.1 IPCP: Address 192.168.1.1 (0x0306C0A80101) *Apr 23 08:57:59.699: Vi2.1 IPCP: I CONFREQ [ACKrcvd] id 126 len 10 *Apr 23 08:57:59.699: Vi2.1 IPCP: Address 192.168.1.2 (0x0306C0A80102) *Apr 23 08:57:59.699: Vi2.1 IPCP: O CONFACK [ACKrcvd] id 126 len 10 *Apr 23 08:57:59.699: Vi2.1 IPCP: Address 192.168.1.2 (0x0306C0A80102) *Apr 23 08:57:59.699: Vi2.1 IPCP: State is Open *Apr 23 08:57:59.703: Vi2.1 IPCP: Install route to 192.168.1.2 *Apr 23 08:57:59.703: Vi2.1 IPCP: Add link info for cef entry 192.168.1.2 LNS2#
관련 정보
개정 이력
| 개정 | 게시 날짜 | 의견 |
|---|---|---|
1.0 |
19-Nov-2007 |
최초 릴리스 |
 피드백
피드백