Cisco Secure Services Client Administrator Guide, Release 4.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 6, 2007
Chapter: SSC Admin Guide Appendix Network Flow Diagram
Network Decision Tree Flow Diagram
The following illustration provides an overview of the XML schema decision tree for configuring a network connection and serves as a graphical index to the corresponding sections in Chapter 2, "Schema Elements". Refer to the legend for a link to the detailed configuring steps and element descriptions.
Figure A-1 Network Configuring High Level Fow Diagram
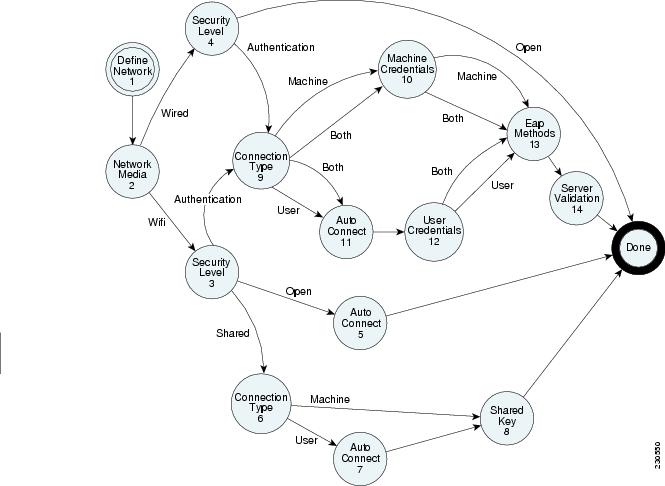
Legend for Figure A-1.
1. ![]() Configure a network
Configure a network
2. ![]() Choosing the network media
Choosing the network media
–![]() Choosing a Network Media Type
Choosing a Network Media Type
3. ![]() Wi-Fi security class
Wi-Fi security class
–![]() Choosing the Wi-Fi Network's Security Class
Choosing the Wi-Fi Network's Security Class
4. ![]() Wired security class
Wired security class
–![]() Choosing the Wired Network's Security Class
Choosing the Wired Network's Security Class
5. ![]() Wi-Fi open network, user connection occurrence
Wi-Fi open network, user connection occurrence
–![]() Configuring an Open Wi-Fi Network
Configuring an Open Wi-Fi Network
6. ![]() Wi-Fi shared key network, connection context
Wi-Fi shared key network, connection context
–![]() Configuring a Shared-key Wi-Fi Network
Configuring a Shared-key Wi-Fi Network
–![]() Configuring a Shared-key, Machine Network
Configuring a Shared-key, Machine Network
7. ![]() Wi-Fi shared key network, user connection occurrence
Wi-Fi shared key network, user connection occurrence
–![]() Configuring a Shared-key, User Network
Configuring a Shared-key, User Network
8. ![]() Wi-Fi shared key network, shared key
Wi-Fi shared key network, shared key
9. ![]() Wi-Fi/wired authentication network, connection context
Wi-Fi/wired authentication network, connection context
–![]() Configuring an Authenticating Wi-Fi Network
Configuring an Authenticating Wi-Fi Network
–![]() Configuring an Authenticating Wired Network
Configuring an Authenticating Wired Network
–![]() Choosing the Authentication Network's Connection Context
Choosing the Authentication Network's Connection Context
–![]() Configuring an Authenticating, Machine and User Network
Configuring an Authenticating, Machine and User Network
10. ![]() Wi-Fi/wired authentication network, machine connection context, credentials
Wi-Fi/wired authentication network, machine connection context, credentials
–![]() Configuring an Authenticating, Machine-only Network
Configuring an Authenticating, Machine-only Network
–![]() Configuring the Authenticating, Machine Credential Source Elements
Configuring the Authenticating, Machine Credential Source Elements
11. ![]() Wi-Fi/wired authentication network, user connection occurrence
Wi-Fi/wired authentication network, user connection occurrence
–![]() Configuring an Authenticating, User-Only Network
Configuring an Authenticating, User-Only Network
–![]() Configuring the Authenticating, User-Only Connection Occurrence Elements
Configuring the Authenticating, User-Only Connection Occurrence Elements
12. ![]() Wi-Fi/wired authentication network, user connection context, credentials
Wi-Fi/wired authentication network, user connection context, credentials
–![]() Configuring the Authenticating, User Credential Source (1) Elements
Configuring the Authenticating, User Credential Source (1) Elements
–![]() Configuring the Authenticating, User Credential Source (2) Elements
Configuring the Authenticating, User Credential Source (2) Elements
13. ![]() Wi-Fi/wired authentication network, EAP methods
Wi-Fi/wired authentication network, EAP methods
14. ![]() Wi-Fi/wired authentication network, server validation
Wi-Fi/wired authentication network, server validation
–![]() Configuring Server Validation
Configuring Server Validation
–![]() Configuring Certificate Trusted Server Rules
Configuring Certificate Trusted Server Rules
–![]() Configuring PAC Trusted Server Rules
Configuring PAC Trusted Server Rules
 Feedback
Feedback