Cisco Wireless Controller Configuration Guide, Release 8.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- April 20, 2015
Chapter: Packet Capture
Packet
Capture
Using the Debug Facility
Information About Using the Debug Facility
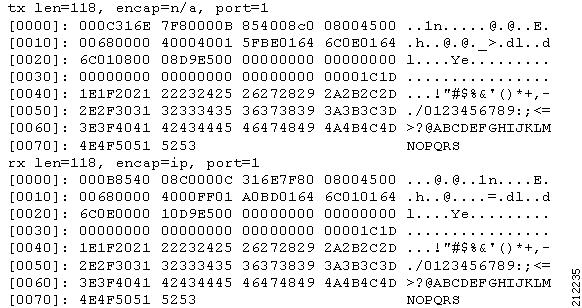
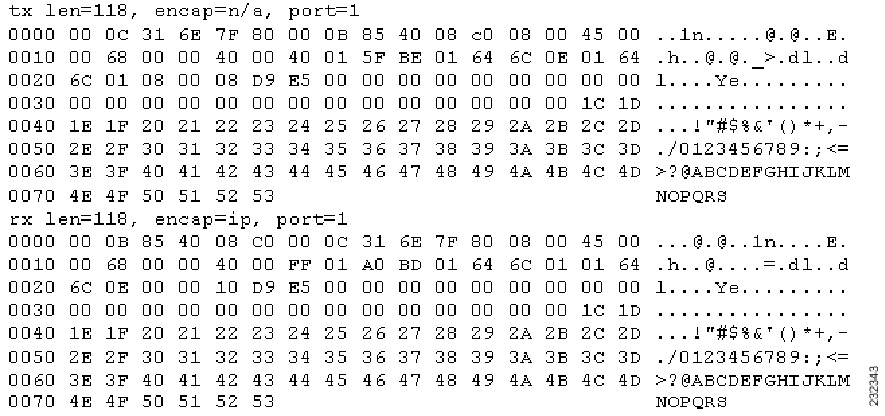
The debug facility enables you to display all packets going to and from the controller CPU. You can enable it for received packets, transmitted packets, or both. By default, all packets received by the debug facility are displayed. However, you can define access control lists (ACLs) to filter packets before they are displayed. Packets not passing the ACLs are discarded without being displayed.
Each ACL includes an action (permit, deny, or disable) and one or more fields that can be used to match the packet. The debug facility provides ACLs that operate at the following levels and on the following values:
At each level, you can define multiple ACLs. The first ACL that matches the packet is the one that is selected.
Configuring the Debug Facility (CLI)
Configuring Wireless Sniffing
Information About Wireless Sniffing
The controller enables you to configure an access point as a network “sniffer,” which captures and forwards all the packets on a particular channel to a remote machine that runs packet analyzer software. These packets contain information on time stamps, signal strength, packet sizes, and so on. Sniffers allow you to monitor and record network activity and to detect problems.
Prerequisites for Wireless Sniffing
To perform wireless sniffing, you need the following hardware and software:
-
A dedicated access point—An access point configured as a sniffer cannot simultaneously provide wireless access service on the network. To avoid disrupting coverage, use an access point that is not part of your existing wireless network.
-
A remote monitoring device—A computer capable of running the analyzer software.
-
Software and supporting files, plug-ins, or adapters—Your analyzer software may require specialized files before you can successfully enable
Restrictions on Wireless Sniffing
-
Supported third-party network analyzer software applications are as follows:
-
The latest version of Wireshark can decode the packets by going to the Analyze mode. Select decode as, and switch UDP5555 to decode as PEEKREMOTE..
-
You must disable IP-MAC address binding in order to use an access point in sniffer mode if the access point is joined to a Cisco WLC. To disable IP-MAC address binding, enter the config network ip-mac-binding disable command in the controller CLI.
-
You must enable WLAN 1 in order to use an access point in sniffer mode if the access point is joined to a Cisco WLC. If WLAN 1 is disabled, the access point cannot send packets.
Configuring Sniffing on an Access Point (GUI)
| Step 1 | Choose Wireless > Access Points > All APs to open the All APs page. |
| Step 2 | Click the name of the access point that you want to configure as the sniffer. The All APs > Details for page appears. |
| Step 3 | From the AP Mode drop-down list, choose Sniffer. |
| Step 4 | Click Apply. |
| Step 5 | Click OK when prompted that the access point will be rebooted. |
| Step 6 | Choose Wireless > Access Points > Radios > 802.11a/n (or 802.11b/g/n) to open the 802.11a/n (or 802.11b/g/n) Radios page. |
| Step 7 | Hover your cursor over the blue drop-down arrow for the desired access point and choose Configure. The 802.11a/n/ac (or 802.11b/g/n) Cisco APs > Configure page appears. |
| Step 8 | Select the Sniff check box to enable sniffing on this access point, or leave it unselected to disable sniffing. The default value is unchecked. |
| Step 9 | If you enabled sniffing in Step 8, follow these steps: |
| Step 10 | Click Apply. |
| Step 11 | Click Save Configuration. |
Configuring Sniffing on an Access Point (CLI)
| Step 1 | Configure the access point as a sniffer by entering this command: config ap mode sniffer Cisco_AP where Cisco_AP is the access point configured as the sniffer. | ||
| Step 2 | When warned that the access point will be rebooted and asked if you want to continue, enter Y. The access point reboots in sniffer mode. | ||
| Step 3 | Enable sniffing on the access point by entering this command: config ap sniff {802.11a | 802.11b} enable channel server_IP_address Cisco_AP
| ||
| Step 4 | Save your changes by entering this command: | ||
| Step 5 | See the sniffer configuration settings for an access point by entering this command: |
 Feedback
Feedback