- Preface
- Overview
- Using the Web-Browser and CLI Interfaces
- Ports and Interfaces
- Configuring Controller Settings
- Configuring VideoStream
- Configuring Security Solutions
- WLANs
- Controlling Lightweight Access Points
- Controlling Mesh Access Points
- Managing Controller Software and Configurations
- Managing User Accounts
- Radio Resource Management
- Configuring Cisco CleanAir
- FlexConnect
- Mobility Groups
- Configuring Mobile Concierge
- Troubleshooting
- Index
Cisco Wireless LAN Controller Configuration Guide, Release 7.3
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- August 25, 2012
Chapter: Configuring Security Solutions
- Cisco Unified Wireless Network Solution Security
- Configuring RADIUS
- Configuring TACACS+
- Configuring Maximum Local Database Entries
- Configuring Local Network Users on the Controller
- Configuring Password Policies
- Configuring LDAP
- Configuring Local EAP
- Configuring the System for SpectraLink NetLink Telephones
- Information About Management Frame Protection
- Restrictions for Management Frame Protection
- Configuring Management Frame Protection (GUI)
- Viewing the Management Frame Protection Settings (GUI)
- Configuring Management Frame Protection (CLI)
- Viewing the Management Frame Protection Settings (CLI)
- Debugging Management Frame Protection Issues (CLI)
Configuring Security Solutions
This chapter describes security solutions for wireless LANs. It contains these sections:
- Cisco Unified Wireless Network Solution Security
- Configuring RADIUS
- Configuring TACACS+
- Configuring Maximum Local Database Entries
- Configuring Local Network Users on the Controller
- Configuring Password Policies
- Configuring LDAP
- Configuring Local EAP
- Configuring the System for SpectraLink NetLink Telephones
- Configuring RADIUS NAC Support
- Using Management Over Wireless
- Using Dynamic Interfaces for Management
- Configuring DHCP Option 82
- Configuring and Applying Access Control Lists
- Configuring Management Frame Protection
- Configuring Client Exclusion Policies
- Configuring Identity Networking
- Configuring AAA Override
- Managing Rogue Devices
- Classifying Rogue Access Points
- Configuring Cisco TrustSec SXP
- Configuring Cisco Intrusion Detection System
- Configuring IDS Signatures
- Configuring wIPS
- Configuring Wi-Fi Direct Client Policy
- Configuring Web Auth Proxy
- Detecting Active Exploits
Cisco Unified Wireless Network Solution Security
Security Overview
The Cisco Unified Wireless Network (UWN) security solution bundles potentially complicated Layer 1, Layer 2, and Layer 3 802.11 Access Point security components into a simple policy manager that customizes system-wide security policies on a per-WLAN basis. The Cisco UWN security solution provides simple, unified, and systematic security management tools.
One of the biggest hurdles to WLAN deployment in the enterprise is WEP encryption, which is a weak standalone encryption method. A newer problem is the availability of low-cost access points, which can be connected to the enterprise network and used to mount man-in-the-middle and denial-of-service attacks.
Layer 1 Solutions
The Cisco UWN security solution ensures that all clients gain access within a user-set number of attempts. If a client fails to gain access within that limit, it is automatically excluded (blocked from access) until the user-set timer expires. The operating system can also disable SSID broadcasts on a per-WLAN basis.
Layer 2 Solutions
If a higher level of security and encryption is required, you can also implement industry-standard security solutions such as Extensible Authentication Protocol (EAP), Wi-Fi Protected Access (WPA), and WPA2. The Cisco UWN solution WPA implementation includes AES (Advanced Encryption Standard), TKIP and Michael (temporal key integrity protocol and message integrity code checksum) dynamic keys, or WEP (Wired Equivalent Privacy) static keys. Disabling is also used to automatically block Layer 2 access after a user-set number of failed authentication attempts.
Regardless of the wireless security solution selected, all Layer 2 wired communications between controllers and lightweight access points are secured by passing data through CAPWAP tunnels.
Restrictions for Layer 2 Solutions
Cisco Aironet client adapter version 4.2 does not authenticate if WPA/WPA2 is used with CCKM as auth key management and a 2 second latency between the controller and AP.
Layer 3 Solutions
The WEP problem can be further solved using industry-standard Layer 3 security solutions such as passthrough VPNs (virtual private networks).
The Cisco UWN solution supports local and RADIUS MAC (media access control) filtering. This filtering is best suited to smaller client groups with a known list of 802.11 access card MAC addresses.
The Cisco UWN solution supports local and RADIUS user/password authentication. This authentication is best suited to small to medium client groups.
Integrated Security Solutions
The integrated security solutions are as follows:
Cisco Unified Wireless Network (UWN) solution operating system security is built around a 802.1X AAA (authorization, authentication and accounting) engine, which allows users to rapidly configure and enforce a variety of security policies across the Cisco UWN solution.
The controllers and lightweight access points are equipped with system-wide authentication and authorization protocols across all ports and interfaces, maximizing system security.
Operating system security policies are assigned to individual WLANs, and lightweight access points simultaneously broadcast all (up to 16) configured WLANs, which can eliminate the need for additional access points, which can increase interference and degrade system throughput.
Operating system security uses the RRM function to continually monitor the air space for interference and security breaches and to notify the user when they are detected.
Operating system security works with industry-standard authorization, authentication, and accounting (AAA) servers.
Configuring RADIUS
Information About RADIUS
Remote Authentication Dial-In User Service (RADIUS) is a client/server protocol that provides centralized security for users attempting to gain management access to a network. It serves as a backend database similar to local and TACACS+ and provides authentication and accounting services:
-
Authentication—The process of verifying users when they attempt to log into the controller.
Users must enter a valid username and password in order for the controller to authenticate users to the RADIUS server. If multiple databases are configured, you can specify the sequence in which the backend database must be tired.
-
Accounting—The process of recording user actions and changes.
Whenever a user successfully executes an action, the RADIUS accounting server logs the changed attributes, the user ID of the person who made the change, the remote host where the user is logged in, the date and time when the command was executed, the authorization level of the user, and a description of the action performed and the values provided. If the RADIUS accounting server becomes unreachable, users are able to continue their sessions uninterrupted.
RADIUS uses User Datagram Protocol (UDP) for its transport. It maintains a database and listens on UDP port 1812 for incoming authentication requests and UDP port 1813 for incoming accounting requests. The controller, which requires access control, acts as the client and requests AAA services from the server. The traffic between the controller and the server is encrypted by an algorithm defined in the protocol and a shared secret key configured on both devices.
You can configure multiple RADIUS accounting and authentication servers. For example, you may want to have one central RADIUS authentication server but several RADIUS accounting servers in different regions. If you configure multiple servers of the same type and the first one fails or becomes unreachable, the controller automatically tries the second one, then the third one if necessary, and so on.
When a management user is authenticated using a RADIUS server, only the PAP protocol is used. For web authentication users, PAP, MSCHAPv2 and MD5 security mechanisms are supported.
RADIUS Server Support
-
You can configure up to 17 RADIUS authentication and accounting servers each.
-
If multiple RADIUS servers are configured for redundancy, the user database must be identical in all the servers for the backup to work properly.
-
One Time Passwords (OTPs) are supported on the controller using RADIUS. In this configuration, the controller acts as a transparent passthrough device. The controller forwards all client requests to the RADIUS server without inspecting the client behavior. When using OTP, the client must establish a single connection to the controller to function properly. The controller currently does not have any intelligence or checks to correct a client that is trying to establish multiple connections.
-
To create a read-only controller user on the RADIUS sever, you must set the service type to NAS prompt instead of Callback NAS prompt. If you set the service type to Callback NAS Prompt, the user authentication fails while setting it to NAS prompt gives the user read-only access to the controller.
Also, the Callback Administrative service type gives the user the lobby ambassador privileges to the controller.
-
If RADIUS servers are mapped per WLAN, then controller do not use RADIUS server from the global list on that WLAN.
Radius ACS Support
Primary and Fallback RADIUS Servers
The primary RADIUS server (the server with the lowest server index) is assumed to be the most preferable server for the controller. If the primary server becomes unresponsive, the controller switches to the next active backup server (the server with the next lowest server index). The controller continues to use this backup server, unless you configure the controller to fall back to the primary RADIUS server when it recovers and becomes responsive or to a more preferable server from the available backup servers.
Configuring RADIUS on the ACS
Configuring RADIUS (GUI)
| Step 1 | Choose . | ||
| Step 2 | Perform one of the following:
This page lists any RADIUS servers that have already been configured. | ||
| Step 3 | From the
Call Station ID Type drop-down list,
choose the option that is sent to the RADIUS server in the Access-Request
message. The following options are available:
| ||
| Step 4 | Enable RADIUS-to-controller key transport using AES key wrap protection by checking the Use AES Key Wrap check box. The default value is unchecked. This feature is required for FIPS customers. | ||
| Step 5 | From the MAC Delimiter drop-down list, choose the option that is sent to the RADIUS server in the Access-Request message. The following options are available: | ||
| Step 6 | Click Apply. Perform one of the following: | ||
| Step 7 | If you are adding a new server, choose a number from the Server Index (Priority) drop-down list to specify the priority order of this server in relation to any other configured RADIUS servers providing the same service. | ||
| Step 8 | If you are adding a new server, enter the
IP address of the RADIUS server in the
Server
IP Address text box.
| ||
| Step 9 | From the Shared Secret Format drop-down list, choose ASCII or Hex to specify the format of the shared secret key to be used between the controller and the RADIUS server. The default value is ASCII. | ||
| Step 10 | In the
Shared
Secret and
Confirm
Shared Secret text boxes, enter the shared secret key to be used
for authentication between the controller and the server.
| ||
| Step 11 | If you are
configuring a new RADIUS authentication server and want to enable AES key wrap,
which makes the shared secret between the controller and the RADIUS server more
secure, follow these steps:
| ||
| Step 12 | If you are adding a new server, enter the RADIUS server’s UDP port number for the interface protocols in the Port Number text box. The valid range is 1 to 65535, and the default value is 1812 for authentication and 1813 for accounting. | ||
| Step 13 | From the Server Status text box, choose Enabled to enable this RADIUS server or choose Disabled to disable it. The default value is enabled. | ||
| Step 14 | If you are configuring a new RADIUS authentication server, choose Enabled from the Support for RFC 3576 drop-down list to enable RFC 3576, which is an extension to the RADIUS protocol that allows dynamic changes to a user session, or choose Disabled to disable this feature. The default value is Enabled. RFC 3576 includes support for disconnecting users and changing authorizations applicable to a user session and supports disconnect and change-of-authorization (CoA) messages. Disconnect messages cause a user session to be terminated immediately where CoA messages modify session authorization attributes such as data filters. | ||
| Step 15 | In the
Server
Timeout text box, enter the number of seconds between
retransmissions. The valid range is 2 to 30 seconds, and the default value is 2
seconds.
Check the Key Wrap check box.
| ||
| Step 16 | Check the Network User check box to enable network user authentication (or accounting), or uncheck it to disable this feature. The default value is unchecked. If you enable this feature, this entry is considered the RADIUS authentication (or accounting) server for network users. If you did not configure a RADIUS server entry on the WLAN, you must enable this option for network users. | ||
| Step 17 | If you are configuring a RADIUS authentication server, check the Management check box to enable management authentication, or uncheck the check box to disable this feature. The default value is checked. If you enable this feature, this entry is considered the RADIUS authentication server for management users, and authentication requests go to the RADIUS server. | ||
| Step 18 | Enter the Management Retransmit Timeout value, which denotes the network login retransmission timeout for the server. | ||
| Step 19 | Check the
IPSec check box
to enable the IP security mechanism, or uncheck the check box to disable this
feature. The default value is unchecked.
| ||
| Step 20 | If you enabled IPsec in
Step 17,
follow these steps to configure additional IPsec parameters:
| ||
| Step 21 | Click Apply. | ||
| Step 22 | Click Save Configuration. | ||
| Step 23 | Repeat the previous steps if you want to configure any additional services on the same server or any additional RADIUS servers. | ||
| Step 24 | Specify the
RADIUS server fallback behavior, as follows:
| ||
| Step 25 | Specify the order of authentication when multiple databases are configured by choosing Security > Priority Order > Management User. The Priority Order > Management User page appears. | ||
| Step 26 | In the Order Used for Authentication text
box, specify which servers have priority when the controller attempts to
authenticate management users. Use the
> and
<
buttons to move servers between the Not Used and Order
Used for Authentication text boxes. After the desired servers appear in the
Order Used for
Authentication text box, use the
Up and
Down buttons to
move the priority server to the top of the list.
By default, the local database is always queried first. If the username is not found, the controller switches to the RADIUS server if configured for RADIUS or to the TACACS+ server if configured for TACACS+. The default setting is local and then RADIUS. | ||
| Step 27 | Click Apply. | ||
| Step 28 | Click Save Configuration. |
Configuring RADIUS (CLI)
Specify whether the IP address, system MAC address, AP MAC address, AP Ethernet MAC address of the originator will be sent to the RADIUS server in the Access-Request message by entering this command:
config radius callStationIdType {ipaddr | macaddr | ap-macaddr-only | ap-macaddr-ssid | | | ap-group-name | ap-location | ap-name | ap-name-ssid | flex-group-name | vlan-id}

Note
The default is System MAC Address.

Caution
Do not use Call Station ID Type for IPv6-only clients.
Specify the delimiter to be used in the MAC addresses that are sent to the RADIUS authentication or accounting server in Access-Request messages by entering this command:
config radius {auth | acct} mac-delimiter {colon | hyphen | single-hyphen | none}
Configure a RADIUS authentication server by entering these commands:
-
config radius auth add index server_ip_address port_number {ascii | hex} shared_secret—Adds a RADIUS authentication server.
-
config radius auth keywrap {enable | disable}—Enables AES key wrap, which makes the shared secret between the controller and the RADIUS server more secure. AES key wrap is designed for Federal Information Processing Standards (FIPS) customers and requires a key-wrap compliant RADIUS authentication server.
-
config radius auth keywrap add {ascii | hex} kek mack index—Configures the AES key wrap attributes
-
config radius auth rfc3576 {enable | disable} index—Enables or disables RFC 3576, which is an extension to the RADIUS protocol that allows dynamic changes to a user session. RFC 3576 includes support for disconnecting users and changing authorizations applicable to a user session and supports disconnect and change-of-authorization (CoA) messages. Disconnect messages cause a user session to be terminated immediately where CoA messages modify session authorization attributes such as data filters.
-
config radius auth retransmit-timeout index timeout—Configures the retransmission timeout value for a RADIUS authentication server.
-
config radius auth mgmt-retransmit-timeout index timeout—Configures the default management login retransmission timeout for a RADIUS authentication server.
-
config radius auth network index {enable | disable}—Enables or disables network user authentication. If you enable this feature, this entry is considered the RADIUS authentication server for network users. If you did not configure a RADIUS server entry on the WLAN, you must enable this option for network users.
-
config radius auth management index {enable | disable}—Enables or disables management authentication. If you enable this feature, this entry is considered the RADIUS authentication server for management users, and authentication requests go to the RADIUS server.
-
config radius auth ipsec {enable | disable} index—Enables or disables the IP security mechanism.
-
config radius auth ipsec authentication {hmac-md5 | hmac-sha1} index—Configures the authentication protocol to be used for IP security.
-
config radius auth ipsec encryption {3des | aes | des | none} index—Configures the IP security encryption mechanism.
-
config radius auth ipsec ike dh-group {group-1 | group-2 | group-5} index—Configures the IKE Diffie-Hellman group.
-
config radius auth ipsec ike lifetime interval index—Configures the timeout interval for the session.
-
config radius auth ipsec ike phase1{aggressive | main} index—Configures the Internet Key Exchange (IKE) protocol.
-
config radius auth ipsec ike auth-method {PSK | certificate} index—Configures the IKE authentication methods. By default PSK is be used for IPSEC sessions.
-
config radius auth ipsec ike auth-mode pre-shared-key index hex/asciisecret—Configures the IPSEC pre-shared key.
-
config radius auth {enable | disable} index—Enables or disables a RADIUS authentication server.
-
config radius auth delete index—Deletes a previously added RADIUS authentication server.
-
Configure a RADIUS accounting server by entering these commands:
-
config radius acct add index server_ip_address port# {ascii | hex} shared_secret—Adds a RADIUS accounting server.
-
config radius acct server-timeout index timeout—Configures the retransmission timeout value for a RADIUS accounting server.
-
config radius acct network index {enable | disable}—Enables or disables network user accounting. If you enable this feature, this entry is considered the RADIUS accounting server for network users. If you did not configure a RADIUS server entry on the WLAN, you must enable this option for network users.
-
config radius acct ipsec {enable | disable} index—Enables or disables the IP security mechanism.
-
config radius acct ipsec authentication {hmac-md5 | hmac-sha1} index—Configures the authentication protocol to be used for IP security.
-
config radius acct ipsec encryption { 3des | aes | des | none} index—Configures the IP security encryption mechanism.
-
config radius acct ipsec ike dh-group {group-1 | group-2 | group-5} index—Configures the IKE Diffie Hellman group.
-
config radius acct ipsec ike lifetime interval index—Configures the timeout interval for the session.
-
config radius acct ipsec ike phase1{aggressive | main} index—Configures the Internet Key Exchange (IKE) protocol.
-
config radius acct {enable | disable} index—Enables or disables a RADIUS accounting server.
-
config radius acct delete index—Deletes a previously added RADIUS accounting server.
-
config radius auth callStationIdType {ap-macaddr-only | ap-macaddr-ssid}—Sets the Called Station ID type to be AP’s radio MAC address or AP’s radio MAC address with SSID in the <AP radio MAC address>:<SSID> format.
-
config radius auth callStationIdType {ipaddr | macaddr}—Sets the Called Station ID type to use the IP address (only Layer 3) or system's MAC address.
-
Configure the RADIUS server fallback behavior by entering this command:
config radius fallback-test mode {off | passive | active}
-
passive causes the controller to revert to a server with a lower priority from the available backup servers without using extraneous probe messages. The controller simply ignores all inactive servers for a time period and retries later when a RADIUS message needs to be sent.
-
active causes the controller to revert to a server with a lower priority from the available backup servers by using RADIUS probe messages to proactively determine whether a server that has been marked inactive is back online. The controller simply ignores all inactive servers for all active RADIUS requests. Once the primary server receives a response from the recovered ACS server, the active fallback RADIUS server no longer sends probe messages to the server requesting the active probe authentication.
If you enabled Active mode in Step 5, enter these commands to configure additional fallback parameters:
Configure the order of authentication when multiple databases are configured by entering this command:
config aaa auth mgmt AAA_server_type AAA_server_type
where AAA_server_type is local, radius, or tacacs.
To see the current management authentication server order, enter the show aaa auth command.
See RADIUS statistics by entering these commands:
-
show radius summary—Shows a summary of RADIUS servers and statistics with AP Ethernet MAC configurations.
-
show radius auth statistics—Shows the RADIUS authentication server statistics.
-
show radius acct statistics—Shows the RADIUS accounting server statistics.
-
show radius rfc3576 statistics—Shows a summary of the RADIUS RFC-3576 server.
-
See active security associations by entering these commands:
Clear the statistics for one or more RADIUS servers by entering this command:
Make sure that the controller can reach the RADIUS server by entering this command:
RADIUS Authentication Attributes Sent by the Controller
The following tables identify the RADIUS authentication attributes sent between the controller and the RADIUS server in access-request and access-accept packets.
| 1 | User-Name |
| 2 | Password |
| 3 | CHAP-Password |
| 4 | NAS-IP-Address |
| 5 | NAS-Port |
| 6 | Service-Type |
| 12 | Framed-MTU |
| 30 | Called-Station-ID (MAC address) |
| 31 | Calling-Station-ID (MAC address) |
| 32 | NAS-Identifier |
| 33 | Proxy-State |
| 60 | CHAP-Challenge |
| 61 | NAS-Port-Type |
| 79 | EAP-Message |
| 1 | Cisco-LEAP-Session-Key |
| 2 | Cisco-Keywrap-Msg-Auth-Code |
| 3 | Cisco-Keywrap-NonCE |
| 4 | Cisco-Keywrap-Key |
| 5 | Cisco-URL-Redirect |
| 6 | Cisco-URL-Redirect-ACL |
 Note | These Cisco-specific attributes are not supported: Auth-Algo-Type and SSID. |
|
Attribute ID |
Description |
|---|---|
| 6 | Service-Type. To specify read-only or read-write access to controllers through RADIUS authentication, you must set the Service-Type attribute (6) on the RADIUS server to Callback NAS Prompt for read-only access or to Administrative for read-write privileges. |
| 8 | Framed-IP-Address |
| 25 | Class |
| 26 | Vendor-Specific |
| 27 | Timeout |
| 29 | Termination-Action |
| 40 | Acct-Status-Type |
| 64 | Tunnel-Type |
| 79 | EAP-Message |
| 81 | Tunnel-Group-ID |
 Note | Message authentication is not supported. |
| 11 | MS-CHAP-Challenge |
| 16 | MS-MPPE-Send-Key |
| 17 | MS-MPPE-Receive-Key |
| 25 | MS-MSCHAP2-Response |
| 26 | MS-MSCHAP2-Success |
| 1 | VAP-ID |
| 3 | DSCP |
| 4 | 8021P-Type |
| 5 | VLAN-Interface-Name |
| 6 | ACL-Name |
| 7 | Data-Bandwidth-Average-Contract |
| 8 | Real-Time-Bandwidth-Average-Contract |
| 9 | Data-Bandwidth-Burst-Contract |
| 10 | Real-Time-Bandwidth-Burst-Contract |
| 11 | Guest-Role-Name |
| 13 | Data-Bandwidth-Average-Contract-US |
| 14 | Real-Time-Bandwidth-Average-Contract-US |
| 15 | Data-Bandwidth-Burst-Contract-US |
| 16 | Real-Time-Bandwidth-Burst-Contract-US |
RADIUS Accounting Attributes
| 1 | User-Name |
| 4 | NAS-IP-Address |
| 5 | NAS-Port |
| 8 | Framed-IP-Address |
| 25 | Class |
| 30 | Called-Station-ID (MAC address) |
| 31 | Calling-Station-ID (MAC address) |
| 32 | NAS-Identifier |
| 40 | Accounting-Status-Type |
| 41 | Accounting-Delay-Time (Stop and interim messages only) |
| 42 | Accounting-Input-Octets (Stop and interim messages only) |
| 43 | Accounting-Output-Octets (Stop and interim messages only) |
| 44 | Accounting-Session-ID |
| 45 | Accounting-Authentic |
| 46 | Accounting-Session-Time (Stop and interim messages only) |
| 47 | Accounting-Input-Packets (Stop and interim messages only) |
| 48 | Accounting-Output-Packets (Stop and interim messages only) |
| 49 | Accounting-Terminate-Cause (Stop messages only) |
| 52 | Accounting-Input-Gigawords |
| 53 | Accounting-Output-Gigawords |
| 55 | Event-Timestamp |
| 64 | Tunnel-Type |
| 65 | Tunnel-Medium-Type |
| 81 | Tunnel-Group-ID |
| 1 | Start | ||
| 2 | Stop | ||
| 3 | Interim-Update
|
||
| 7 | Accounting-On | ||
| 8 | Accounting-Off | ||
| 9-14 | Reserved for Tunneling Accounting | ||
| 15 | Reserved for Failed |
Configuring TACACS+
Information About TACACS+
Terminal Access Controller Access Control System Plus (TACACS+) is a client/server protocol that provides centralized security for users attempting to gain management access to a controller. It serves as a backend database similar to local and RADIUS. However, local and RADIUS provide only authentication support and limited authorization support while TACACS+ provides three services:
-
Authentication—The process of verifying users when they attempt to log into the controller.
Users must enter a valid username and password in order for the controller to authenticate users to the TACACS+ server. The authentication and authorization services are tied to one another. For example, if authentication is performed using the local or RADIUS database, then authorization would use the permissions associated with the user in the local or RADIUS database (which are read-only, read-write, and lobby-admin) and not use TACACS+. Similarly, when authentication is performed using TACACS+, authorization is tied to TACACS+.

Note
When multiple databases are configured, you can use the controller GUI or CLI to specify the sequence in which the backend databases should be tried.
-
Authorization—The process of determining the actions that users are allowed to take on the controller based on their level of access.
For TACACS+, authorization is based on privilege (or role) rather than specific actions. The available roles correspond to the seven menu options on the controller GUI: MONITOR, WLAN, CONTROLLER, WIRELESS, SECURITY, MANAGEMENT, and COMMANDS. An additional role, LOBBY, is available for users who require only lobby ambassador privileges. The roles to which users are assigned are configured on the TACACS+ server. Users can be authorized for one or more roles. The minimum authorization is MONITOR only, and the maximum is ALL, which authorizes the user to execute the functionality associated with all seven menu options. For example, a user who is assigned the role of SECURITY can make changes to any items appearing on the Security menu (or designated as security commands in the case of the CLI). If users are not authorized for a particular role (such as WLAN), they can still access that menu option in read-only mode (or the associated CLI show commands). If the TACACS+ authorization server becomes unreachable or unable to authorize, users are unable to log into the controller.

Note
If users attempt to make changes on a controller GUI page that are not permitted for their assigned role, a message appears indicating that they do not have sufficient privilege. If users enter a controller CLI command that is not permitted for their assigned role, a message may appear indicating that the command was successfully executed although it was not. In this case, the following additional message appears to inform users that they lack sufficient privileges to successfully execute the command: “Insufficient Privilege! Cannot execute command!”
-
Accounting—The process of recording user actions and changes.
Whenever a user successfully executes an action, the TACACS+ accounting server logs the changed attributes, the user ID of the person who made the change, the remote host where the user is logged in, the date and time when the command was executed, the authorization level of the user, and a description of the action performed and the values provided. If the TACACS+ accounting server becomes unreachable, users are able to continue their sessions uninterrupted.
TACACS+ uses Transmission Control Protocol (TCP) for its transport, unlike RADIUS which uses User Datagram Protocol (UDP). It maintains a database and listens on TCP port 49 for incoming requests. The controller, which requires access control, acts as the client and requests AAA services from the server. The traffic between the controller and the server is encrypted by an algorithm defined in the protocol and a shared secret key configured on both devices.
You can configure up to three TACACS+ authentication, authorization, and accounting servers each. For example, you may want to have one central TACACS+ authentication server but several TACACS+ authorization servers in different regions. If you configure multiple servers of the same type and the first one fails or becomes unreachable, the controller automatically tries the second one and then the third one if necessary.
 Note | If multiple TACACS+ servers are configured for redundancy, the user database must be identical in all the servers for the backup to work properly. |
-
You must configure TACACS+ on both your CiscoSecure Access Control Server (ACS) and your controller. You can configure the controller through either the GUI or the CLI.
-
TACACS+ is supported on CiscoSecure ACS version 3.2 and later releases. See the CiscoSecure ACS documentation for the version that you are running.
-
One Time Passwords (OTPs) are supported on the controller using TACACS. In this configuration, the controller acts as a transparent passthrough device. The controller forwards all client requests to the TACACS server without inspecting the client behavior. When using OTP, the client must establish a single connection to the controller to function properly. The controller currently does not have any intelligence or checks to correct a client that is trying to establish multiple connections.
-
We recommend that you increase the retransmit timeout value for TACACS+ authentication, authorization, and accounting servers if you experience repeated reauthentication attempts or the controller falls back to the backup server when the primary server is active and reachable. The default retransmit timeout value is 2 seconds and you can increase the retransmit timeout value to a maximum of 30 seconds.
TACACS+ VSA
The Internet Engineering Task Force (IETF) draft standard specifies a method for communicating vendor-specific attributes (VSAs) between the network access server and the TACACS+ server. The IETF uses attribute 26. VSAs allow vendors to support their own extended attributes that are not suitable for general use.
The Cisco TACACS+ implementation supports one vendor-specific option using the format recommended in the IETF specification. The Cisco vendor ID is 9, and the supported option is vendor type 1, which is named cisco-av-pair. The value is a string with the following format:
protocol : attribute separator value *
The protocol is a Cisco attribute for a particular type of authorization, the separator is = (equal sign) for mandatory attributes, and * (asterisk) indicates optional attributes.
Configuring TACACS+ on the ACS
| Step 1 | Choose Network Configuration on the ACS main page. | ||||
| Step 2 | Choose
Add Entry under AAA
Clients to add your controller to the server. The Add AAA Client page appears.
| ||||
| Step 3 | In the AAA Client Hostname text box, enter the name of your controller. | ||||
| Step 4 | In the AAA Client IP Address text box, enter the IP address of your controller. | ||||
| Step 5 | In the
Shared Secret
text box, enter the shared secret key to be used for
authentication between the server and the controller.
| ||||
| Step 6 | From the Authenticate Using drop-down list, choose TACACS+ (Cisco IOS). | ||||
| Step 7 | Click Submit + Apply to save your changes. | ||||
| Step 8 | On the ACS main page, in the left navigation pane, choose Interface Configuration. | ||||
| Step 9 | Choose TACACS+ (Cisco IOS). The TACACS+ (Cisco) page appears. | ||||
| Step 10 | Under TACACS+ Services, select the Shell (exec) check box. | ||||
| Step 11 | Under New Services, select the first check box and enter ciscowlc in the Service text box and common in the Protocol text box. | ||||
| Step 12 | Under Advanced Configuration Options, select the Advanced TACACS+ Features check box. | ||||
| Step 13 | Click Submit to save your changes. | ||||
| Step 14 | On the ACS main page, in the left navigation pane, choose System Configuration. | ||||
| Step 15 | Choose Logging. | ||||
| Step 16 | When the Logging Configuration page appears, enable all of the events that you want to be logged and save your changes. | ||||
| Step 17 | On the ACS main page, in the left navigation pane, choose Group Setup. | ||||
| Step 18 | From the Group drop-down
list, choose a previously created group.
| ||||
| Step 19 | Click Edit Settings. The Group Setup page appears. | ||||
| Step 20 | Under TACACS+ Settings, select the ciscowlc common check box. | ||||
| Step 21 | Select the Custom Attributes check box. | ||||
| Step 22 | In the text box below Custom
Attributes, specify the roles that you want to assign to this group. The
available roles are MONITOR, WLAN, CONTROLLER, WIRELESS, SECURITY, MANAGEMENT,
COMMANDS, ALL, and LOBBY. The first seven correspond to the menu options on the
controller GUI and allow access to those particular controller features. If a
user is not entitled for a particular task, the user is still allowed to access
that task in read-only mode. You can enter one or multiple roles, depending on
the group's needs. Use ALL to specify all seven roles or LOBBY to specify the
lobby ambassador role. Enter the roles using this format:
For example, to specify the WLAN, CONTROLLER, and SECURITY roles for a particular user group, you would enter the following text: role1=WLAN role2=CONTROLLER role3=SECURITY? To give a user group access to all seven roles, you would enter the following text: role1=ALL?
| ||||
| Step 23 | Click Submit to save your changes. |
Configuring TACACS+ (GUI)
| Step 1 | Choose Security > AAA > TACACS+. | ||||
| Step 2 | Perform one of the following:
The TACACS+ (Authentication, Authorization, or Accounting) Servers page appears. This page lists any TACACS+ servers that have already been configured. | ||||
| Step 3 | Perform one of the following: | ||||
| Step 4 | If you are adding a new server, choose a number from the Server Index (Priority) drop-down list to specify the priority order of this server in relation to any other configured TACACS+ servers providing the same service. You can configure up to three servers. If the controller cannot reach the first server, it tries the second one in the list and then the third if necessary. | ||||
| Step 5 | If you are adding a new server, enter the IP address of the TACACS+ server in the Server IP Address text box. | ||||
| Step 6 | From the Shared Secret Format drop-down list, choose ASCII or Hex to specify the format of the shared secret key to be used between the controller and the TACACS+ server. The default value is ASCII. | ||||
| Step 7 | In the
Shared
Secret and
Confirm
Shared Secret text boxes, enter the shared secret key to be used
for authentication between the controller and the server.
| ||||
| Step 8 | If you are adding a new server, enter the TACACS+ server’s TCP port number for the interface protocols in the Port Number text box. The valid range is 1 to 65535, and the default value is 49. | ||||
| Step 9 | In the Server Status text box, choose Enabled to enable this TACACS+ server or choose Disabled to disable it. The default value is Enabled. | ||||
| Step 10 | In the
Server
Timeout text box, enter the number of seconds between
retransmissions. The valid range is 5 to 30 seconds, and the default value is 5
seconds.
| ||||
| Step 11 | Click Apply. | ||||
| Step 12 | Click Save Configuration. | ||||
| Step 13 | Repeat the previous steps if you want to configure any additional services on the same server or any additional TACACS+ servers. | ||||
| Step 14 | Specify the order of authentication when multiple databases are configured by choosing Security > Priority Order > Management User. The Priority Order > Management User page appears. | ||||
| Step 15 | In the
Order
Used for Authentication text box, specify which servers have
priority when the controller attempts to authenticate management users.
Use the > and < buttons to move servers between the Not Used and Order Used for Authentication text boxes. After the desired servers appear in the Order Used for Authentication text box, use the Up and Down buttons to move the priority server to the top of the list. By default, the local database is always queried first. If the username is not found, the controller switches to the RADIUS server if configured for RADIUS or to the TACACS+ server if configured for TACACS+. The default setting is local and then RADIUS. | ||||
| Step 16 | Click Apply. | ||||
| Step 17 | Click Save Configuration. |
Configuring TACACS+ (CLI)
Configure a TACACS+ authentication server by entering these commands:
-
config tacacs auth add index server_ip_address port# {ascii | hex} shared_secret—Adds a TACACS+ authentication server.
-
config tacacs auth delete index—Deletes a previously added TACACS+ authentication server.
-
config tacacs auth (enable | disable} index—Enables or disables a TACACS+ authentication server.
-
config tacacs auth server-timeout index timeout—Configures the retransmission timeout value for a TACACS+ authentication server.
-
Configure a TACACS+ authorization server by entering these commands:
-
config tacacs athr add index server_ip_address port# {ascii | hex} shared_secret—Adds a TACACS+ authorization server.
-
config tacacs athr delete index—Deletes a previously added TACACS+ authorization server.
-
config tacacs athr (enable | disable} index—Enables or disables a TACACS+ authorization server.
-
config tacacs athr server-timeout index timeout—Configures the retransmission timeout value for a TACACS+ authorization server.
-
Configure a TACACS+ accounting server by entering these commands:
-
config tacacs acct add index server_ip_address port# {ascii | hex} shared_secret—Adds a TACACS+ accounting server.
-
config tacacs acct delete index—Deletes a previously added TACACS+ accounting server.
-
config tacacs acct (enable | disable} index—Enables or disables a TACACS+ accounting server.
-
config tacacs acct server-timeout index timeout—Configures the retransmission timeout value for a TACACS+ accounting server.
-
See TACACS+ statistics by entering these commands:
Clear the statistics for one or more TACACS+ servers by entering this command:
Configure the order of authentication when multiple databases are configured by entering this command. The default setting is local and then radius.
config aaa auth mgmt [radius | tacacs]
See the current management authentication server order by entering the show aaa auth command.Make sure the controller can reach the TACACS+ server by entering this command:
Enable or disable TACACS+ debugging by entering this command:
Save your changes by entering this command:
Viewing the TACACS+ Administration Server Logs
| Step 1 | On the ACS main page, in the left navigation pane, choose Reports and Activity. |
| Step 2 | Under Reports, choose TACACS+ Administration. Click the .csv file corresponding to the date of the logs you want to view. The TACACS+ Administration .csv page appears. 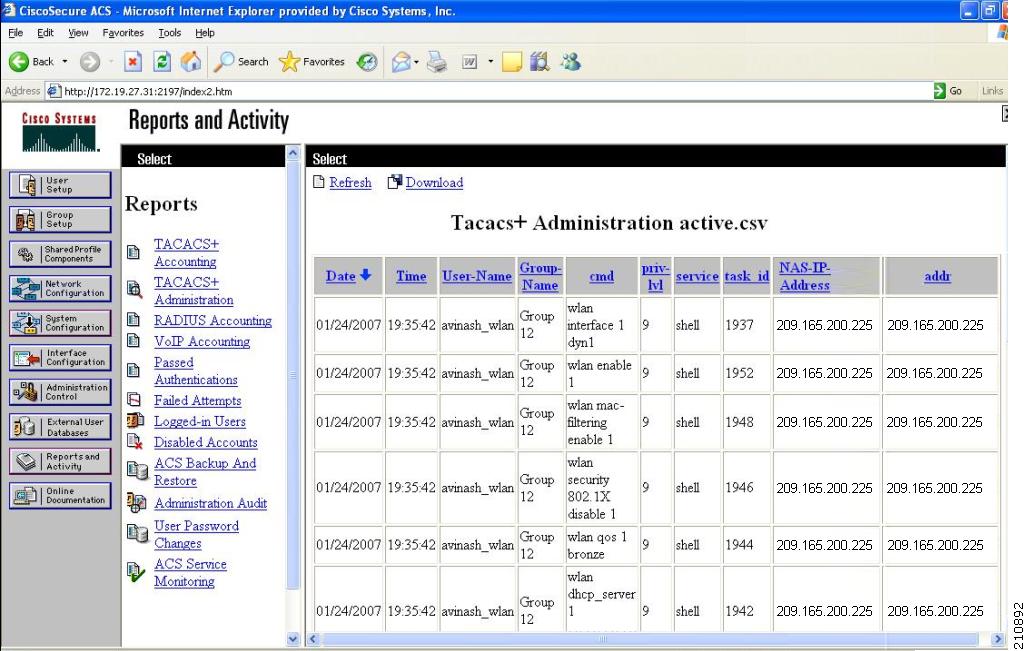 |
Configuring Maximum Local Database Entries
Information About Configuring Maximum Local Database Entries
You can configure the controller to specify the maximum number of local database entries used for storing user authentication information. The database entries include local management users (including lobby ambassadors), local network users (including guest users), MAC filter entries, exclusion list entries, and access point authorization list entries. Together they cannot exceed the configured maximum value.
Configuring Maximum Local Database Entries (GUI)
| Step 1 | Choose Security > AAA > General to open the General page. |
| Step 2 | In the Maximum Local Database Entries text box, enter a value for the maximum number of entries that can be added to the local database the next time the controller reboots. The currently configured value appears in parentheses to the right of the text box. The valid range is 512 to 2048, and the default setting is 2048. The Number of Entries, Already Used text box shows the number of entries currently in the database. |
| Step 3 | Click Apply to commit your changes. |
| Step 4 | Click Save Configuration to save your settings. |
Configuring Maximum Local Database Entries (CLI)
| Step 1 | Specify the maximum number of entries that can be added to the local database the next time the controller reboots by entering this command: |
| Step 2 | Save your changes by entering this command: save config |
| Step 3 | View the maximum number of database entries and the current database contents by entering this command: show database summary |
Configuring Local Network Users on the Controller
Information About Local Network Users on Controller
You can add local network users to the local user database on the controller. The local user database stores the credentials (username and password) of all the local network users. These credentials are then used to authenticate the users. For example, local EAP may use the local user database as its backend database to retrieve user credentials.
 Note | The controller passes client information to the RADIUS authentication server first. If the client information does not match a RADIUS database entry, the RADIUS authentication server replies with an authentication failure message. If the RADIUS authentication server does not reply, then the local user database is queried. Clients located in this database are granted access to network services if the RADIUS authentication fails or does not exist. |
Configuring Local Network Users for the Controller (GUI)
| Step 1 | Choose
Security >
AAA >
Local Net Users
to open the Local Net Users page.
| ||
| Step 2 | Perform one of the following: | ||
| Step 3 | If you are adding a new user, enter a username for the
local user in the
User
Name text box. You can enter up to 49 alphanumeric characters.
| ||
| Step 4 | In the Password and Confirm Password text boxes, enter a password for the local user. You can enter up to 49 alphanumeric characters. | ||
| Step 5 | If you are adding a new user, select the Guest User check box if you want to limit the amount of time that the user has access to the local network. The default setting is unselected. | ||
| Step 6 | If you are adding a new user and you selected the Guest User check box, enter the amount of time (in seconds) that the guest user account is to remain active in the Lifetime text box. The valid range is 60 to 2,592,000 seconds (30 days) inclusive, and the default setting is 86,400 seconds. | ||
| Step 7 | If you are adding a new user, you selected the
Guest
User check box, and you want to assign a QoS role to this guest
user, select the
Guest User Role check
box. The default setting is unselected.
| ||
| Step 8 | If you are adding a new user and you selected the Guest User Role check box, choose the QoS role that you want to assign to this guest user from the Role drop-down list. | ||
| Step 9 | From the WLAN Profile drop-down list, choose the name of the WLAN that is to be accessed by the local user. If you choose Any WLAN, which is the default setting, the user can access any of the configured WLANs. | ||
| Step 10 | In the Description text box, enter a descriptive title for the local user (such as “User 1”). | ||
| Step 11 | Click Apply to commit your changes. | ||
| Step 12 | Click Save Configuration to save your changes. |
Configuring Local Network Users for the Controller (CLI)
Configure a local network user by entering these commands:
-
config netuser add username password wlan wlan_id userType permanent description description—Adds a permanent user to the local user database on the controller.
-
config netuser add username password {wlan | guestlan} {wlan_id | guest_lan_id} userType guestlifetime seconds description description—Adds a guest user on a WLAN or wired guest LAN to the local user database on the controller. 
Note
Instead of adding a permanent user or a guest user to the local user database from the controller, you can choose to create an entry on the RADIUS server for the user and enable RADIUS authentication for the WLAN on which web authentication is performed.
- config netuser delete username
-
See information related to the local network users configured on the controller by entering these commands:
Save your changes by entering this command:
Additional References
To know more about configuring local network users, see Configuring Local EAP.
Configuring Password Policies
Information About Password Policies
The password policies allows you to enforce strong password checks on newly created passwords for additional management users of controller and access point. The following are the requirements enforced on the new password:
When the controller is upgraded from old version, all the old passwords are maintained as it is, even though the passwords are weak. After the system upgrade, if strong password checks are enabled, the same is enforced from that time and the strength of previously added passwords will not be checked or altered.
Depending on the settings done in the Password Policy page, the local management and access point user configuration is affected.
Configuring Password Policies (GUI)
| Step 1 | Choose Security > AAA > Password Policies to open the Password Policies page. |
| Step 2 | Select the Password must contain characters from at least 3 different classes check box if you want your password to contain characters from at least three of the following classes: lower case letters, upper case letters, digits, and special characters. |
| Step 3 | Select the No character can be repeated more than 3 times consecutively check box if you do not want character in the new password to repeat more than three times consecutively. |
| Step 4 | Select the Password cannot be the default words like cisco, admin check box if you do not want the password to contain words such as Cisco, ocsic, admin, nimda, or any variant obtained by changing the capitalization of letters or by substituting 1, |, or! or substituting 0 for o or substituting $ for s. |
| Step 5 | Select the Password cannot contain username or reverse of username check box if you do not want the password to contain a username or the reverse letters of a username. |
| Step 6 | Click Apply to commit your changes. |
| Step 7 | Click Save Configuration to save your changes. |
Configuring Password Policies (CLI)
Enable or disable strong password check for AP and WLC by entering this command:
config switchconfig strong-pwd {case-check | consecutive-check | default-check | username-check | all-checks} {enable | disable}
whereSee the configured options for strong password check by entering this command:
Information similar to the following appears:
802.3x Flow Control Mode......................... Disabled FIPS prerequisite features....................... Disabled secret obfuscation............................... Enabled Strong Password Check Features: case-check ...........Enabled consecutive-check ....Enabled default-check .......Enabled username-check ......Enabled
Configuring LDAP
This section explains how to configure a Lightweight Directory Access Protocol (LDAP) server as a backend database, similar to a RADIUS or local user database.
Information About LDAP
An LDAP backend database allows the controller to query an LDAP server for the credentials (username and password) of a particular user. These credentials are then used to authenticate the user. For example, local EAP may use an LDAP server as its backend database to retrieve user credentials.
 Note | From Release 8.0, IPv6 can also be used to configure the LDAP server on the controller. |
Fallback LDAP Servers
The LDAP servers are configured on a WLAN for authentication. You require at least two LDAP servers to configure them for fallback behavior. A maximum of three LDAP servers can be configured for the fallback behavior per WLAN. The servers are listed in the priority order for authentication. If the first LDAP server becomes irresponsive, then the controller switches to the next LDAP server. If the second LDAP server becomes irresponsive, then the controller switches again to the third LDAP server.
The LDAP backend database supports these local EAP methods: EAP-TLS, EAP-FAST/GTC, and PEAPv1/GTC. LEAP, EAP-FAST/MSCHAPv2, EAP-FAST/EAP-GTC and PEAPv0/MSCHAPv2 are also supported, but only if the LDAP server is set up to return a clear-text password.
Cisco wireless LAN controllers support Local EAP authentication against external LDAP databases such as Microsoft Active Directory and Novell’s eDirectory. For more information about configuring the controller for Local EAP authentication against Novell’s eDirectory, see the Configure Unified Wireless Network for Authentication Against Novell's eDirectory Database whitepaper at http://www.cisco.com/c/en/us/support/docs/wireless/4400-series-wireless-lan-controllers/112137-novell-edirectory-00.html
Configuring LDAP (GUI)
| Step 1 | Choose Security > AAA > LDAP to open the LDAP Servers page. | ||
| Step 2 | Perform one of
the following:
| ||
| Step 3 | If you are adding a new server, enter the IP
address of the LDAP server in the
Server
IP Address text box.
| ||
| Step 4 | If you are adding a new server, enter the LDAP
server’s TCP port number in the
Port
Number text box. The valid range is 1 to 65535, and the default
value is 389.
| ||
| Step 5 | From the Server Mode drop-down list, choose None. | ||
| Step 6 | Select the Enable Server Status check box to enable this LDAP server or unselect it to disable it. The default value is disabled. | ||
| Step 7 | From the Simple Bind drop-down list, choose Anonymous or Authenticated to specify the local authentication bind method for the LDAP server. The Anonymous method allows anonymous access to the LDAP server. The Authenticated method requires that a username and password be entered to secure access. The default value is Anonymous. | ||
| Step 8 | If you chose
Authenticated in the previous step, follow these
steps:
| ||
| Step 9 | In the User Base DN text box, enter the distinguished name
(DN) of the subtree in the LDAP server that contains a list of all the users.
For example, ou=organizational unit, .ou=next organizational unit, and
o=corporation.com. If the tree containing users is the base DN, type.
o=corporation.com
or dc=corporation,dc=com | ||
| Step 10 | In the User Attribute text box, enter the name of the attribute in the user record that contains the username. You can obtain this attribute from your directory server. | ||
| Step 11 | In the User Object Type text box, enter the value of the LDAP objectType attribute that identifies the record as a user. Often, user records have several values for the objectType attribute, some of which are unique to the user and some of which are shared with other object types. | ||
| Step 12 | In the Server Timeout text box, enter the number of seconds between retransmissions. The valid range is 2 to 30 seconds, and the default value is 2 seconds. | ||
| Step 13 | Click Apply to commit your changes. | ||
| Step 14 | Click Save Configuration to save your changes. | ||
| Step 15 | Specify LDAP as the priority backend database
server for local EAP authentication as follows:
| ||
| Step 16 | (Optional) Assign
specific LDAP servers to a WLAN as follows:
| ||
| Step 17 | Specify the
LDAP server fallback behavior, as follows:
|
Configuring LDAP (CLI)
Configure an LDAP server by entering these commands:
-
config ldap add index server_ip_address port# user_base user_attr user_type — Adds an LDAP server.
-
config ldap delete index—Deletes a previously added LDAP server.
-
config ldap {enable | disable} index—Enables or disables an LDAP server.
-
config ldap simple-bind {anonymous index | authenticated index username username password password}—Specifies the local authentication bind method for the LDAP server. The anonymous method allows anonymous access to the LDAP server whereas the authenticated method requires that a username and password be entered to secure access. The default value is anonymous. The username can contain up to 80 characters.
If the username starts with “cn=” (in lowercase letters), the controller assumes that the username includes the entire LDAP database path and does not append the user base DN. This designation allows the authenticated bind user to be outside the user base DN.
- config ldap retransmit-timeout index timeout—Configures the number of seconds between retransmissions for an LDAP server.
-
Specify LDAP as the priority backend database server by entering this command:
config local-auth user-credentials ldap
If you enter the config local-auth user-credentials ldap local command, local EAP attempts to authenticate clients using the LDAP backend database and fails over to the local user database if the LDAP servers are not reachable. If the user is not found, the authentication attempt is rejected. If you enter the config local-auth user-credentials local ldap command, local EAP attempts to authenticate using only the local user database. It does not fail over to the LDAP backend database.
(Optional) Assign specific LDAP servers to a WLAN by entering these commands:
- config wlan ldap
add
wlan_id
server_index—Links a configured LDAP server to a WLAN.
The LDAP servers specified in this command apply only to WLANs with web authentication enabled. They are not used by local EAP.
- config wlan ldap delete wlan_id {all | index}—Deletes a specific or all configured LDAP server(s) from a WLAN.
- config wlan ldap
add
wlan_id
server_index—Links a configured LDAP server to a WLAN.
View information pertaining to configured LDAP servers by entering these commands:
-
show ldap summary—Shows a summary of the configured LDAP servers.
Idx Server Address Port Enabled --- --------------- ---- ------- 1 2.3.1.4 389 No 2 10.10.20.22 389 Yes
-
show ldap index—Shows detailed LDAP server information. Information like the following appears:
Server Index..................................... 2 Address.......................................... 10.10.20.22 Port............................................. 389 Enabled.......................................... Yes User DN.......................................... ou=active,ou=employees,ou=people, o=cisco.com User Attribute................................... uid User Type........................................ Person Retransmit Timeout............................... 2 seconds Bind Method ..................................... Authenticated Bind Username................................. user1
-
show ldap statistics—Shows LDAP server statistics.
Server Index..................................... 1 Server statistics: Initialized OK................................. 0 Initialization failed.......................... 0 Initialization retries......................... 0 Closed OK...................................... 0 Request statistics: Received....................................... 0 Sent........................................... 0 OK............................................. 0 Success........................................ 0 Authentication failed.......................... 0 Server not found............................... 0 No received attributes......................... 0 No passed username............................. 0 Not connected to server........................ 0 Internal error................................. 0 Retries........................................ 0 Server Index..................................... 2 ..
-
show wlan wlan_id—Shows the LDAP servers that are applied to a WLAN.
-
Make sure the controller can reach the LDAP server by entering this command: ping server_ip_address
Save your changes by entering this command:
Enable or disable debugging for LDAP by entering this command: debug aaa ldap {enable | disable}
Additional References
For more information about configuring LEAP, see the Configuring Local EAP section
Configuring Local EAP
Information About Local EAP
Local EAP is an authentication method that allows users and wireless clients to be authenticated locally. It is designed for use in remote offices that want to maintain connectivity to wireless clients when the backend system becomes disrupted or the external authentication server goes down. When you enable local EAP, the controller serves as the authentication server and the local user database, which removes dependence on an external authentication server. Local EAP retrieves user credentials from the local user database or the LDAP backend database to authenticate users. Local EAP supports LEAP, EAP-FAST, EAP-TLS, P EAPv0/MSCHAPv2, and PEAPv1/GTC authentication between the controller and wireless clients.
 Note | The LDAP backend database supports these local EAP methods: EAP-TLS, EAP-FAST/GTC, and PEAPv1/GTC. LEAP, EAP-FAST/MSCHAPv2, and PEAPv0/MSCHAPv2 are also supported but only if the LDAP server is set up to return a clear-text password. |
 Note | Cisco wireless LAN controllers support Local EAP authentication against external LDAP databases such as Microsoft Active Directory and Novell’s eDirectory. For more information about configuring the controller for Local EAP authentication against Novell’s eDirectory, see the Configure Unified Wireless Network for Authentication Against Novell's eDirectory Database whitepaper at http://www.cisco.com/c/en/us/support/docs/wireless/4400-series-wireless-lan-controllers/112137-novell-edirectory-00.html |
If any RADIUS servers are configured on the controller, the controller tries to authenticate the wireless clients using the RADIUS servers first. Local EAP is attempted only if no RADIUS servers are found, either because the RADIUS servers timed out or no RADIUS servers were configured. If four RADIUS servers are configured, the controller attempts to authenticate the client with the first RADIUS server, then the second RADIUS server, and then local EAP. If the client attempts to then reauthenticate manually, the controller tries the third RADIUS server, then the fourth RADIUS server, and then local EAP. If you never want the controller to try to authenticate clients using an external RADIUS server, enter these CLI commands in this order:
Restrictions on Local EAP
Configuring Local EAP (GUI)
 Note | EAP-TLS, P EAPv0/MSCHAPv2, and PEAPv1/GTC use certificates for authentication, and EAP-FAST uses either certificates or PACs. The controller is shipped with Cisco-installed device and Certificate Authority (CA) certificates. However, if you want to use your own vendor-specific certificates, they must be imported on the controller. |
| Step 1 | If you are configuring local EAP to use one of the EAP types listed in the note above, make sure that the appropriate certificates and PACs (if you will use manual PAC provisioning) have been imported on the controller. |
| Step 2 | If you want the controller to retrieve user credentials from the local user database, make sure that you have properly configured the local network users on the controller. |
| Step 3 | If you want the controller to retrieve user credentials from an LDAP backend database, make sure that you have properly configured an LDAP server on the controller. |
| Step 4 | Specify the order in which
user credentials are retrieved from the backend database servers as follows:
|
| Step 5 | Specify values
for the local EAP timers as follows:
|
| Step 6 | Specify values for the
Advanced EAP parameters as follows:
|
| Step 7 | Create a local EAP profile,
which specifies the EAP authentication types that are supported on the wireless
clients as follows:
|
| Step 8 | If you created an EAP-FAST
profile, follow these steps to configure the EAP-FAST parameters:
|
| Step 9 | Enable local EAP on a WLAN
as follows:
|
| Step 10 | Click Save Configuration to save your changes. |
Configuring Local EAP (CLI)
 Note | EAP-TLS, P EAPv0/MSCHAPv2, and PEAPv1/GTC use certificates for authentication, and EAP-FAST uses either certificates or PACbs. The controller is shipped with Cisco-installed device and Certificate Authority (CA) certificates. However, if you want to use your own vendor-specific certificates, they must be imported on the controller. |
| Step 1 | If you are configuring local EAP to use one of the EAP types listed in the note above, make sure that the appropriate certificates and PACs (if you will use manual PAC provisioning) have been imported on the controller. | ||||||
| Step 2 | If you want the controller to retrieve user credentials from the local user database, make sure that you have properly configured the local network users on the controller. | ||||||
| Step 3 | If you want the controller to retrieve user credentials from an LDAP backend database, make sure that you have properly configured an LDAP server on the controller. | ||||||
| Step 4 | Specify the order in which
user credentials are retrieved from the local and/or LDAP databases by entering
this command:
config local-auth user-credentials {local | ldap}
| ||||||
| Step 5 | Specify values for
the local EAP timers by entering these commands:
| ||||||
| Step 6 | Create a local
EAP profile by entering this command:
config local-auth eap-profile add profile_name
| ||||||
| Step 7 | Add an EAP
method to a local EAP profile by entering this command:
config local-auth
eap-profile method add
method
profile_name
The supported methods are leap, fast, tls, and peap.
| ||||||
| Step 8 | Configure
EAP-FAST parameters if you created an EAP-FAST profile by entering this
command:
config local-auth method fast ? where ? is one of the following:
| ||||||
| Step 9 | Configure
certificate parameters per profile by entering these commands:
| ||||||
| Step 10 | Enable local
EAP and attach an EAP profile to a WLAN by entering this command:
config wlan local-auth enable profile_name wlan_id
| ||||||
| Step 11 | Save your changes by entering this command: | ||||||
| Step 12 | View
information pertaining to local EAP by entering these commands:
| ||||||
| Step 13 | (Optional) Troubleshoot local
EAP sessions by entering these commands:
|
Additional References
See the Managing Controller Software and Configurations section for instructions on importing certificates and PACs.
See the Configuring Local Network Users on the Controller section for instructions on configuring local network users on the controller.
See the Configuring LDAP section for instruction on configuring LDAP.
Configuring the System for SpectraLink NetLink Telephones
Information About SpectraLink NetLink Telephones
For the best integration with the Cisco UWN solution, SpectraLink NetLink Telephones require an extra operating system configuration step: enable long preambles. The radio preamble (sometimes called a header) is a section of data at the head of a packet that contains information that wireless devices need when sending and receiving packets. Short preambles improve throughput performance, so they are enabled by default. However, some wireless devices, such as SpectraLink NetLink phones, require long preambles.
Configuring SpectraLink NetLink Phones
Enabling Long Preambles (GUI)
| Step 1 | Choose Wireless > 802.11b/g/n > Network to open the 802.11b/g Global Parameters page. | ||
| Step 2 | If the Short Preamble check box is selected, continue with this procedure. However, if the Short Preamble check box is unselected (which means that long preambles are enabled), the controller is already optimized for SpectraLink NetLink phones and you do not need to continue this procedure. | ||
| Step 3 | Unselect the Short Preamble check box to enable long preambles. | ||
| Step 4 | Click Apply to update the controller configuration.
| ||
| Step 5 | Choose Commands > Reboot > Reboot > Save and Reboot to reboot the controller. Click OK in response to this prompt: Configuration will be saved and the controller will be rebooted. Click ok to confirm. | ||
| Step 6 | Log back onto the controller GUI to verify that the controller is properly configured. | ||
| Step 7 | Choose Wireless > 802.11b/g/n > Network to open the 802.11b/g Global Parameters page. If the Short Preamble check box is unselected, the controller is optimized for SpectraLink NetLink phones. |
Enabling Long Preambles (CLI)
| Step 1 | Log on to the controller CLI. |
| Step 2 | Enter the show 802.11b command and select the Short preamble mandatory parameter. If the parameter indicates that short preambles are enabled, continue with this procedure. This example shows that short preambles are enabled: Short Preamble mandatory....................... Enabled However, if the parameter shows that short preambles are disabled (which means that long preambles are enabled), the controller is already optimized for SpectraLink NetLink phones and you do not need to continue this procedure. |
| Step 3 | Disable the 802.11b/g network by entering this command: You cannot enable long preambles on the 802.11a network. |
| Step 4 | Enable long preambles by entering this command: |
| Step 5 | Reenable the 802.11b/g network by entering this command: |
| Step 6 | Enter the reset system command to reboot the controller. Enter y when the prompt to save the system changes is displayed. The controller reboots. |
| Step 7 | Verify that the controller is properly configured by logging back into the CLI and entering the show 802.11b command to view these parameters: 802.11b Network................................ Enabled Short Preamble mandatory....................... Disabled These parameters show that the 802.11b/g network is enabled and that short preambles are disabled. |
Configuring Enhanced Distributed Channel Access (CLI)
To configure 802.11 enhanced distributed channel access (EDCA) parameters to support SpectraLink phones, use the following CLI commands:
config advanced edca-parameter {custom-voice | optimized-video-voice | optimized-voice | svp-voice | wmm-default}
custom-voice enables custom voice EDCA parameters
optimized-video-voice enables combined video-voice-optimized parameters
optimized-voice enables non-SpectraLink voice-optimized parameters
svp-voice enables SpectraLink voice priority (SVP) parameters
wmm-default enables wireless multimedia (WMM) default parameters
 Note | To propagate this command to all access points connected to the controller, make sure to disable and then reenable the 802.11b/g network after entering this command. |
Configuring RADIUS NAC Support
Information About RADIUS NAC Support
The Cisco Identity Services Engine (ISE) is a next-generation, context-based access control solution that provides the functions of Cisco Secure Access Control System (ACS) and Cisco Network Admission Control (NAC) in one integrated platform.
ISE has been introduced in the 7.0.116.0 release of the Cisco Unified Wireless Network. ISE can be used to provide advanced security for your deployed network. It is an authentication server that you can configure on your controller. When a client associates to the controller on a RADIUS NAC–enabled WLAN, the controller forwards the request to the ISE server.
The ISE server validates the user in the database and on successful authentication, the URL and pre-AUTH ACL are sent to the client. The client then moves to the Posture Required state and is redirected to the URL returned by the ISE server.
 Note | The client moves to the Central Web Authentication state, if the URL returned by the ISE server has the keyword 'cwa'. |
The NAC agent in the client triggers the posture validation process. On successful posture validation by the ISE server, the client is moved to the run state.
 Note | Flex local switching with Radius NAC support is added in Release 7.2.110.0. It is not supported in 7.0 Releases and 7.2 Releases. Downgrading 7.2.110.0 and later releases to either 7.2 or 7.0 releases will require you to reconfigure the WLAN for Radius NAC feature to work. |
Device Registration
Device registration enables you to authenticate and provision new devices on the WLAN with RADIUS NAC enabled. When the device is registered on the WLAN, it can use the network based on the configured ACL.
Central Web Authentication
In the case of Central Web Authentication (CWA), the web-authentication occurs on the ISE server. The web portal in the ISE server provides a login page to the client. Once the credentials are verified on the ISE server, the client is provisioned. The client remains in the POSTURE_REQD state until a CoA is reached. The credentials and ACLs are received from the ISE server.
Local Web Authentication
Local web authentication is not supported for RADIUS NAC.
| RADIUS NAC Enabled | Yes | No | Yes |
| L2 None | No | PSK, Static WEP, CKIP | No |
| L3 None | N/A | Internal/External | N/A |
| MAC Filtering Enabled | Yes | No | Yes |
Restrictions for RADIUS NAC Support
-
A RADIUS NAC-enabled WLAN supports Open Authentication and MAC filtering.
-
Radius NAC functionality does not work if the configured accounting server is different from authentication (ISE) server. You should configure the same server as the authentication and accounting server in case ISE functionalities are used. If ISE is used only for ACS functionality, the accounting server can be flexible.
-
When clients move from one WLAN to another, the controller retains the client’s audit session ID if it returns to the WLAN before the idle timeout occurs. As a result, when clients join the controller before the idle timeout session expires, they are immediately moved to RUN state. The clients are validated if they reassociate with the controller after the session timeout.
-
Suppose you have two WLANs, where WLAN 1 is configured on a controller (WLC1) and WLAN2 is configured on another controller (WLC2) and both are RADIUS NAC enabled. The client first connects to WLC1 and moves to the RUN state after posture validation. Assume that the client now moved to WLC2. If the client connects back to WLC1 before the PMK expires for this client in WLC1, the posture validation is skipped for the client. The client directly moves to RUN state by passing posture validation as the controller retains the old audit session ID for the client that is already known to ISE.
-
When deploying RADIUS NAC in your wireless network, do not configure a primary and secondary ISE server. Instead, we recommend that you configure HA between the two ISE servers. Having a primary and secondary ISE setup will require a posture validation to happen before the clients move to RUN state. If HA is configured, the client is automatically moved to RUN state in the fallback ISE server.
-
The controller software configured with RADIUS NAC does not support a change of authorization (CoA) on the service port.
-
Do not swap AAA server indexes in a live network because clients might get disconnected and have to reconnect to the RADIUS server, which might result in log messages to be appended to the ISE server logs.
-
During slow roaming, the client goes through posture validation.
-
Guest tunneling mobility is supported for ISE NAC–enabled WLANs.
-
With RADIUS NAC enabled, the RADIUS server overwrite interface is not supported.
-
Any DHCP communication between client and server. We parse the DHCP profiling only once. This is sent to the ISE server only once.
-
If the AAA url-redirect-acl and url-redirect attributes are expected from the AAA server, the AAA override feature must be enabled on the controller.
Configuring RADIUS NAC Support (GUI)
Configuring RADIUS NAC Support (CLI)
Using Management Over Wireless
Information About Management over Wireless
The management over wireless feature allows you to monitor and configure local controllers using a wireless client. This feature is supported for all management tasks except uploads to and downloads from (transfers to and from) the controller.
Restrictions on Management over Wireless
Enabling Management over Wireless (GUI)
| Step 1 | Choose Management > Mgmt Via Wireless to open the Management Via Wireless page. |
| Step 2 | Select the Enable Controller Management to be accessible from Wireless Clients check box to enable management over wireless for the WLAN or unselect it to disable this feature. The default value is unselected. |
| Step 3 | Click Apply to commit your changes. |
| Step 4 | Click Save Configuration to save your changes. |
Enabling Management over Wireless (CLI)
Using Dynamic Interfaces for Management
Information About Using Dynamic Interfaces for Management
You can access the controller with one of its dynamic interface IP addresses. Both the wired and wireless clients can access the dynamic interface of the controller using the CLI and GUI. To access the GUI of the controller enter the dynamic interface IP address of the controller in the address field of either Internet Explorer or Mozilla Firefox browser. For wired clients, you must enable management of dynamic interface and must ensure that the wired client is in the VLAN that is mapped to the dynamic interface.
A device, when the management using dynamic interfaces is disabled, can open an SSH connection, if the protocol is enabled. However, you are not prompted to log on. Additionally, the management address remains accessible from a dynamic interface VLAN, unless a CPU ACL is in place. When management using dynamic interface is enabled along with CPU ACL, the CPU ACL has more priority.
-
Source wired client from Cisco WLC's dynamic interface VLAN accesses the management interface VLAN and tries for management access.
-
Source wired client from Cisco WLC's management interface VLAN accesses the dynamic interface VLAN and tries for management access.
-
Source wired client from Cisco WLC's dynamic interface VLAN accesses the dynamic interface VLAN tries and tries for management access.
-
Source wired client from Layer 3 VLAN interface accesses the dynamic interface or the management interface and tries for management access.
Here, management is not the management interface but the configuration access. If the Cisco WLC configuration is accessed from any other IP address on the Cisco WLC other than the management IP, it is management using dynamic interface.
Configuring Management using Dynamic Interfaces (CLI)
Enable or disable management using dynamic interfaces by entering this command:
config network mgmt-via-dynamic-interface {enable | disable}
Configuring DHCP Option 82
Information About DHCP Option 82
DHCP option 82 provides additional security when DHCP is used to allocate network addresses. It enables the controller to act as a DHCP relay agent to prevent DHCP client requests from untrusted sources. You can configure the controller to add option 82 information to DHCP requests from clients before forwarding the requests to the DHCP server.
The access point forwards all DHCP requests from a client to the controller. The controller adds the DHCP option 82 payload and forwards the request to the DHCP server. The payload can contain the MAC address or the MAC address and SSID of the access point, depending on how you configure this option.
 Note | Any DHCP packets that already include a relay agent option are dropped at the controller. |
For DHCP option 82 to operate correctly, DHCP proxy must be enabled.
Restrictions on DHCP Option 82
Configuring DHCP Option 82 (GUI)
| Step 1 | Choose to open the DHCP Parameters page. |
| Step 2 | Select the Enable DHCP Proxy check box to enable DHCP proxy. |
| Step 3 | Choose a DHCP Option 82 format from the drop-down list. You can choose either binary or ascii to specify the format of the DHCP option 82 payload. |
| Step 4 | Choose a DHCP Option 82 Remote ID field
format from the drop-down list to specify the format of the DHCP option 82
payload.
For more information about the options available, see the Controller Online Help. |
| Step 5 | Enter the DHCP timeout value in the DHCP Timeout field. The timeout value is globally applicable. You can specify the DHCP timeout value in range from 5 to 120 seconds. |
| Step 6 | Click Apply. |
| Step 7 | Click Save Configuration . |
What to Do Next
On the controller CLI, you can enable DHCP option 82 on the dynamic interface to which the WLAN is associated by entering this command:
config interface dhcp dynamic-interface interface-name option-82 enableConfiguring DHCP Option 82 (CLI)
Configure the format of the DHCP option 82 payload by entering one of these commands:
- config dhcp opt-82 remote-id ap_mac—Adds the radio MAC address of the access point to the DHCP option 82 payload.
- config dhcp opt-82 remote-id ap_mac:ssid—Adds the radio MAC address and SSID of the access point to the DHCP option 82 payload.
- config dhcp opt-82 remote-id ap-ethmac—Adds the Ethernet MAC address of the access point to the DHCP option 82 payload.
Enable DHCP Option 82 on the dynamic interface to which the WLAN is associated by entering this command:
config interface dhcp dynamic-interface interface-name option-82 enable
See the status of DHCP option 82 on the dynamic interface by entering the show interface detailed dynamic-interface-namecommand.
Additional References
In order for DHCP option 82 to operate correctly, DHCP proxy must be enabled.
Configuring and Applying Access Control Lists
Information About Access Control Lists
An Access Control List (ACL) is a set of rules used to limit access to a particular interface (for example, if you want to restrict a wireless client from pinging the management interface of the controller). After ACLs are configured on the controller, they can be applied to the management interface, the AP-manager interface, any of the dynamic interfaces, or a WLAN to control data traffic to and from wireless clients or to the controller central processing unit (CPU) to control all traffic destined for the CPU.
You may also want to create a preauthentication ACL for web authentication. Such an ACL could be used to allow certain types of traffic before authentication is complete.
Both IPv4 and IPv6 ACL are supported. IPv6 ACLs support the same options as IPv4 ACLs including source, destination, source and destination ports.
 Note | You can enable only IPv4 traffic in your network by blocking IPv6 traffic. That is, you can configure an IPv6 ACL to deny all IPv6 traffic and apply it on specific or all WLANs. |
Restrictions for Access Control Lists
-
You can define up to 64 ACLs, each with up to 64 rules (or filters) for both IPv4 and IPv6. Each rule has parameters that affect its action. When a packet matches all of the parameters for a rule, the action set for that rule is applied to the packet.
-
When you apply CPU ACLs on a Cisco 5508 WLC or a Cisco WiSM2, you must permit traffic towards the virtual interface IP address for web authentication.
-
All ACLs have an implicit “deny all rule” as the last rule. If a packet does not match any of the rules, it is dropped by the controller.
-
If you are using an external web server with a Cisco 5508 WLC or a WLC network module, you must configure a preauthentication ACL on the WLAN for the external web server.
-
If you apply an ACL to an interface or a WLAN, wireless throughput is degraded when downloading from a 1-GBps file server. To improve throughput, remove the ACL from the interface or WLAN, move the ACL to a neighboring wired device with a policy rate-limiting restriction, or connect the file server using 100 Mbps rather than 1 Gbps.
-
Multicast traffic received from wired networks that is destined to wireless clients is not processed by WLC ACLs. Multicast traffic initiated from wireless clients, destined to wired networks or other wireless clients on the same controller, is processed by WLC ACLs.
-
ACLs are configured on the controller directly or configured through Cisco Prime Infrastructure templates. The ACL name must be unique.
-
You can configure ACL per client (AAA overridden ACL) or on either an interface or a WLAN. The AAA overridden ACL has the highest priority. However, each interface, WLAN, or per client ACL configuration that you apply can override one another.
-
If peer-to-peer blocking is enabled, traffic is blocked between peers even if the ACL allows traffic between them.
-
Authentication traffic has to go through the Cisco WLC for this feature to be supported, even if DNS-based ACL is local to the AP.
-
When you create an ACL, it is recommended to perform the two actions (create an ACL or ACL rule and apply the ACL or ACL rule) continuously either from CLI or GUI.
-
In Cisco Wireless Releases prior to 8.0.100.0, the behavior of the Redirect-URL-ACL (as returned via RADIUS attributes) may have been incorrect. The ACL was applied in only the Ingress direction (traffic destined for the LAN or distribution system) of the radio interface. These ACLs should also be applied in the Egress direction (traffic destined for the wireless client). Therefore, after upgrading to a Cisco Wireless Release 8.0 or a later release, you may need to adjust the ACL to accommodate the correction of this behavior.
 Note | ACL ID 0 is not supported in Cisco WLC. Foreign WLC does not send url-redirect-acl to anchor WLC if the received ACL attribute from RADIUS/ISE is mapped to ACL ID 0. It causes web redirect failure on wireless client later. |
Configuring and Applying Access Control Lists (GUI)
Configuring Access Control Lists
| Step 1 | Choose to open the Access Control Lists page. | ||
| Step 2 | If you want to see if packets are hitting any of the ACLs
configured on your controller, select the
Enable Counters
check box and click
Apply. Otherwise,
leave the check box unselected, which is the default value. This feature is
useful when troubleshooting your system.
| ||
| Step 3 | Add a new ACL by clicking New. The Access Control Lists > New page appears. | ||
| Step 4 | In the Access Control List Name text box, enter a name for the new ACL. You can enter up to 32 alphanumeric characters. | ||
| Step 5 | Choose the ACL type. There are two types of ACL supported, IPv4 and IPv6. | ||
| Step 6 | Click Apply. When the Access Control Lists page reappears, click the name of the new ACL. | ||
| Step 7 | When the Access Control Lists > Edit page appears, click Add New Rule. The Access Control Lists > Rules > New page appears. | ||
| Step 8 | Configure a rule
for this ACL as follows:
| ||
| Step 9 | Click Save Configuration to save your changes. | ||
| Step 10 | Repeat this procedure to add any additional ACLs. |
Applying an Access Control List to an Interface
| Step 1 | Choose Controller > Interfaces. | ||
| Step 2 | Click the name of the desired interface. The Interfaces > Edit page for that interface appears. | ||
| Step 3 | Choose the desired ACL from the ACL Name drop-down list
and click
Apply. The default is None.
| ||
| Step 4 | Click Save Configuration to save your changes. |
Applying an Access Control List to the Controller CPU
| Step 1 | Choose Security > Access Control Lists > CPU Access Control Lists to open the CPU Access Control Lists page. | ||||
| Step 2 | Select the Enable CPU ACL check box to enable a designated ACL to control the IPv4 traffic to the controller CPU or unselect the check box to disable the CPU ACL feature and remove any ACL that had been applied to the CPU. The default value is unselected. | ||||
| Step 3 | From the ACL Name drop-down list, choose the ACL that will
control the IPv4 traffic to the controller CPU. None is the default value when
the CPU ACL feature is disabled. If you choose None while the Enable CPU ACL
check box is selected, an error message appears indicating that you must choose
an ACL.
| ||||
| Step 4 | Select the Enable CPU IPv6 ACL check box to enable a designated ACL to control the IPv6 traffic to the controller CPU or unselect the check box to disable the CPU ACL feature and remove any ACL that had been applied to the CPU. The default value is unselected. | ||||
| Step 5 | From the IPv6 ACL Name drop-down list, choose the ACL that will control the IPv6 traffic to the controller CPU. None is the default value when the CPU ACL feature is disabled. If you choose None while the Enable CPU IPv6 ACL check box is selected, an error message appears indicating that you must choose an ACL. | ||||
| Step 6 | Click Apply to commit your changes. | ||||
| Step 7 | Click Save Configuration to save your changes. |
Applying an Access Control List to a WLAN
| Step 1 | Choose WLANs to open the WLANs page. | ||
| Step 2 | Click the ID number of the desired WLAN to open the WLANs > Edit page. | ||
| Step 3 | Choose the Advanced tab to open the WLANs > Edit (Advanced) page. | ||
| Step 4 | From the Override Interface ACL drop-down list, choose the IPv4 or IPv6 ACL that you want to apply to this WLAN. The ACL that you choose overrides any ACL that is configured for the interface. None is the default value.
| ||
| Step 5 | Click Apply. | ||
| Step 6 | Click Save Configuration. |
Applying a Preauthentication Access Control List to a WLAN
| Step 1 | Choose WLANs to open the WLANs page. |
| Step 2 | Click the ID number of the desired WLAN to open the WLANs > Edit page. |
| Step 3 | Choose the Security and Layer 3 tabs to open the WLANs > Edit (Security > Layer 3) page. |
| Step 4 | Select the Web Policy check box. |
| Step 5 | From the Preauthentication ACL drop-down list, choose the desired ACL and click Apply. None is the default value. |
| Step 6 | Click Save Configuration to save your changes. |
Configuring and Applying Access Control Lists (CLI)
Configuring Access Control Lists
| Step 1 | See all of the ACLs that are configured on the controller by entering this command: | ||
| Step 2 | See detailed information for a particular ACL by entering this command: show [ipv6] acl detailed acl_name The Counter text box increments each time a packet matches an ACL rule, and the DenyCounter text box increments each time a packet does not match any of the rules.
| ||
| Step 3 | Enable or disable ACL counters for your controller by entering this command: config acl counter {start | stop}
| ||
| Step 4 | Add a new ACL by entering this command: config [ipv6] acl create acl_name. You can enter up to 32 alphanumeric characters for the acl_name parameter.
| ||
| Step 5 | Add a rule for an ACL by entering this command: config [ipv6] acl rule add acl_name rule_index | ||
| Step 6 | Configure an ACL rule by entering config [ipv6] acl rule command: | ||
| Step 7 | Save your settings by entering this command:
|
Applying Access Control Lists
| Step 1 | Perform the following to
apply an IPv4 ACL:
| ||||
| Step 2 | Perform the following to apply an IPv6 ACL: | ||||
| Step 3 | To apply an ACL to a WLAN, enter this command: | ||||
| Step 4 | To apply a pre-authentication ACL to a WLAN, enter this command: | ||||
| Step 5 | Save your changes by entering this command: save config |
Configuring Management Frame Protection
Information About Management Frame Protection
Management frame protection (MFP) provides security for the otherwise unprotected and unencrypted 802.11 management messages passed between access points and clients. MFP provides both infrastructure and client support.
-
Infrastructure MFP—Protects management frames by detecting adversaries that are invoking denial-of-service attacks, flooding the network with associations and probes, interjecting as rogue access points, and affecting network performance by attacking the QoS and radio measurement frames. Infrastructure MFP is a global setting that provides a quick and effective means to detect and report phishing incidents.
Specifically, infrastructure MFP protects 802.11 session management functions by adding message integrity check information elements (MIC IEs) to the management frames emitted by access points (and not those emitted by clients), which are then validated by other access points in the network. Infrastructure MFP is passive. It can detect and report intrusions but has no means to stop them.
-
Client MFP—Shields authenticated clients from spoofed frames, preventing many of the common attacks against wireless LANs from becoming effective. Most attacks, such as deauthentication attacks, revert to simply degrading performance by contending with valid clients.
Specifically, client MFP encrypts management frames are sent between access points and CCXv5 clients so that both the access points and clients can take preventative action by dropping spoofed class 3 management frames (that is, management frames passed between an access point and a client that is authenticated and associated). Client MFP leverages the security mechanisms defined by IEEE 802.11i to protect the following types of class 3 unicast management frames: disassociation, deauthentication, and QoS (WMM) action. Client MFP protects a client-access point session from the most common type of denial-of-service attack. It protects class 3 management frames by using the same encryption method used for the session’s data frames. If a frame received by the access point or client fails decryption, it is dropped, and the event is reported to the controller.
To use client MFP, clients must support CCXv5 MFP and must negotiate WPA2 using either TKIP or AES-CCMP. EAP or PSK may be used to obtain the PMK. CCKM and controller mobility management are used to distribute session keys between access points for Layer 2 and Layer 3 fast roaming.

Note
To prevent attacks using broadcast frames, access points supporting CCXv5 will not emit any broadcast class 3 management frames (such as disassociation, deauthentication, or action). CCXv5 clients and access points must discard broadcast class 3 management frames.
Client MFP supplements infrastructure MFP rather than replaces it because infrastructure MFP continues to detect and report invalid unicast frames sent to clients that are not client-MFP capable as well as invalid class 1 and 2 management frames. Infrastructure MFP is applied only to management frames that are not protected by client MFP.
Infrastructure MFP consists of three main components:
-
Management frame protection—The access point protects the management frames it transmits by adding a MIC IE to each frame. Any attempt to copy, alter, or replay the frame invalidates the MIC, causing any receiving access point configured to detect MFP frames to report the discrepancy. MFP is supported for use with Cisco Aironet lightweight access points.
-
Management frame validation—In infrastructure MFP, the access point validates every management frame that it receives from other access points in the network. It ensures that the MIC IE is present (when the originator is configured to transmit MFP frames) and matches the content of the management frame. If it receives any frame that does not contain a valid MIC IE from a BSSID belonging to an access point that is configured to transmit MFP frames, it reports the discrepancy to the network management system. In order for the timestamps to operate properly, all controllers must be Network Time Protocol (NTP) synchronized.
-
Event reporting—The access point notifies the controller when it detects an anomaly, and the controller aggregates the received anomaly events and can report the results through SNMP traps to the network management system.

Note
Client MFP uses the same event reporting mechanisms as infrastructure MFP.
Infrastructure MFP is disabled by default and can be enabled globally. When you upgrade from a previous software release, infrastructure MFP is disabled globally if access point authentication is enabled because the two features are mutually exclusive. Once infrastructure MFP is enabled globally, signature generation (adding MICs to outbound frames) can be disabled for selected WLANs, and validation can be disabled for selected access points.
Client MFP is enabled by default on WLANs that are configured for WPA2. It can be disabled, or it can be made mandatory (in which case, only clients that negotiate MFP are allowed to associate) on selected WLANs.
Restrictions for Management Frame Protection
Lightweight access points support infrastructure MFP in local and monitor modes and in FlexConnect mode when the access point is connected to a controller. They support client MFP in local, FlexConnect, and bridge modes.
Client MFP is supported for use only with CCXv5 clients using WPA2 with TKIP or AES-CCMP.
Non-CCXv5 clients may associate to a WLAN if client MFP is disabled or optional.
Error reports generated on a FlexConnect access point in standalone mode cannot be forwarded to the controller and are dropped.
Configuring Management Frame Protection (GUI)
| Step 1 | Choose Security> Wireless Protection Policies > AP Authentication/MFP to open the AP Authentication Policy page. | ||
| Step 2 | Enable infrastructure MFP globally for the controller by choosing Management Frame Protection from the Protection Type drop-down list. | ||
| Step 3 | Click
Apply to commit your changes.
| ||
| Step 4 | Configure client MFP for a
particular WLAN after infrastructure MFP has been enabled globally for the
controller as follows:
| ||
| Step 5 | Click Save Configuration to save your settings. |
Viewing the Management Frame Protection Settings (GUI)
To see the controller’s current global MFP settings, choose Security > Wireless Protection Policies > Management Frame Protection. The Management Frame Protection Settings page appears.
On this page, you can see the following MFP settings:
-
The Management Frame Protection field shows if infrastructure MFP is enabled globally for the controller.
-
The Controller Time Source Valid field indicates whether the controller time is set locally (by manually entering the time) or through an external source (such as the NTP/SNTP server). If the time is set by an external source, the value of this field is “True.” If the time is set locally, the value is “False.” The time source is used for validating the timestamp on management frames between access points of different controllers within a mobility group.
-
The Client Protection field shows if client MFP is enabled for individual WLANs and whether it is optional or required.
Configuring Management Frame Protection (CLI)
Enable or disable infrastructure MFP globally for the controller by entering this command: config wps mfp infrastructure {enable | disable}
Enable or disable client MFP on a specific WLAN by entering this command:
config wlan mfp client {enable | disable} wlan_id [required ]
If you enable client MFP and use the optional required parameter, clients are allowed to associate only if MFP is negotiated.
Viewing the Management Frame Protection Settings (CLI)
See the controller’s current MFP settings by entering this command:
show wps mfp summary
See the current MFP configuration for a particular WLAN by entering this command:
show wlan wlan_id
See whether client MFP is enabled for a specific client by entering this command:
See MFP statistics for the controller by entering this command: show wps mfp statistics

Note
This report contains no data unless an active attack is in progress. This table is cleared every 5 minutes when the data is forwarded to any network management stations.
Debugging Management Frame Protection Issues (CLI)
Use this command if you experience any problems with MFP:
debug wps mfp ? {enable | disable}
where ? is one of the following:
client—Configures debugging for client MFP messages.
capwap—Configures debugging for MFP messages between the controller and access points.
detail—Configures detailed debugging for MFP messages.
report—Configures debugging for MFP reporting.
mm—Configures debugging for MFP mobility (inter-controller) messages.
Configuring Client Exclusion Policies
Configuring Client Exclusion Policies (GUI)
| Step 1 | Choose to open the Client Exclusion Policies page. |
| Step 2 | Select any of these check boxes if you want the controller to exclude clients for the condition specified. The default value for each exclusion policy is enabled.
|
| Step 3 | Click Apply. |
| Step 4 | Click Save Configuration. |
Configuring Client Exclusion Policies (CLI)
| Step 1 | Enable or disable the controller to exclude clients on the sixth 802.11 association attempt, after five consecutive failures by entering this command: config wps client-exclusion 802.11-assoc {enable | disable} |
| Step 2 | Enable or disable the controller to exclude clients on the sixth 802.11 authentication attempt, after five consecutive failures by entering this command: |
| Step 3 | Enable or disable the controller to exclude clients on the fourth 802.1X authentication attempt, after three consecutive failures by entering this command: config wps client-exclusion 802.1x-auth {enable | disable} |
| Step 4 | Configure the
controller to exclude clients that reaches the maximum failure 802.1X
authentication attempt with the RADIUS server by entering this command:
config wps client-exclusion
802.1x-auth
max-1x-aaa-fail-attempts
You can configure the maximum failure 802.1X authentication attempt from 1 to 3 and the default value is 3. |
| Step 5 | Enable or disable the controller to exclude clients if the IP address is already assigned to another device by entering this command: config wps client-exclusion ip-theft {enable | disable} |
| Step 6 | Enable or disable the controller to exclude clients on the fourth web authentication attempt, after three consecutive failures by entering this command: |
| Step 7 | Enable or disable the controller to exclude clients for all of the above reasons by entering this command: |
| Step 8 | Use the
following command to add or delete client exclusion entries.
config exclusionlist {add MAC [description] | delete MAC | description MAC [description]} |
| Step 9 | Save your changes by entering this command: save config |
| Step 10 | See a list of
clients that have been dynamically excluded, by entering this command:
Information similar to the following appears: Dynamically Disabled Clients ---------------------------- MAC Address Exclusion Reason Time Remaining (in secs) ----------- ---------------- ------------------------ 00:40:96:b4:82:55 802.1X Failure 51 |
| Step 11 | See the client
exclusion policy configuration settings by entering this command:
Information similar to the following appears: Auto-Immune Auto-Immune.................................... Disabled Client Exclusion Policy Excessive 802.11-association failures.......... Enabled Excessive 802.11-authentication failures....... Enabled Excessive 802.1x-authentication................ Enabled IP-theft....................................... Enabled Excessive Web authentication failure........... Enabled Maximum 802.1x-AAA failure attempts............ 3 Signature Policy Signature Processing........................ Enabled |
Configuring Identity Networking
Information About Identity Networking
In most wireless LAN systems, each WLAN has a static policy that applies to all clients associated with an SSID. Although powerful, this method has limitations because it requires clients to associate with different SSIDs to inherit different QoS and security policies.
However, the Cisco Wireless LAN solution supports identity networking, which allows the network to advertise a single SSID but allows specific users to inherit different QoS or security policies based on their user profiles. The specific policies that you can control using identity networking are as follows:
ACL—When the ACL attribute is present in the RADIUS Access Accept, the system applies the ACL name to the client station after it authenticates, which overrides any ACLs that are assigned to the interface.
VLAN—When a VLAN Interface-name or VLAN tag is present in a RADIUS Access Accept, the system places the client on a specific interface.

NoteThe VLAN feature only supports MAC filtering, 802.1X, and WPA. The VLAN feature does not support web authentication or IPsec.
-

NoteWhen any of the other RADIUS attributes (QoS-Level, ACL-Name, Interface-Name, or VLAN-Tag), which are described later in this section, are returned, the Tunnel Attributes must also be returned.
The operating system’s local MAC filter database has been extended to include the interface name, allowing local MAC filters to specify to which interface the client should be assigned. A separate RADIUS server can also be used, but the RADIUS server must be defined using the Security menus.
RADIUS Attributes Used in Identity Networking
QoS-Level
This section explains the RADIUS attributes used in identity networking.
This attribute indicates the QoS level to be applied to the mobile client's traffic within the switching fabric, as well as over the air. This example shows a summary of the QoS-Level Attribute format. The text boxes are transmitted from left to right.
0 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Type | Length | Vendor-Id +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ Vendor-Id (cont.) | Vendor type | Vendor length | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | QoS Level | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
ACL-Name
This attribute indicates the ACL name to be applied to the client. A summary of the ACL-Name Attribute format is shown below. The text boxes are transmitted from left to right.
0 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Type | Length | Vendor-Id +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ Vendor-Id (cont.) | Vendor type | Vendor length | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | ACL Name... +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-
Interface Name
This attribute indicates the VLAN Interface a client is to be associated to. A summary of the Interface-Name Attribute format is shown below. The text boxes are transmitted from left to right.
0 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Type | Length | Vendor-Id +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ Vendor-Id (cont.) | Vendor type | Vendor length | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Interface Name... +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-
VLAN Tag
This attribute indicates the group ID for a particular tunneled session and is also known as the Tunnel-Private-Group-ID attribute.
This attribute might be included in the Access-Request packet if the tunnel initiator can predetermine the group resulting from a particular connection and should be included in the Access-Accept packet if this tunnel session is to be treated as belonging to a particular private group. Private groups may be used to associate a tunneled session with a particular group of users. For example, it may be used to facilitate routing of unregistered IP addresses through a particular interface. It should be included in Accounting-Request packets which contain Acct-Status-Type attributes with values of either Start or Stop and which pertain to a tunneled session.
A summary of the Tunnel-Private-Group-ID Attribute format is shown below. The text boxes are transmitted from left to right.
0 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Type | Length | Tag | String... +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
Tag – The Tag text box is one octet in length and is intended to provide a means of grouping attributes in the same packet which refer to the same tunnel. If the value of the Tag text box is greater than 0x00 and less than or equal to 0x1F, it should be interpreted as indicating which tunnel (of several alternatives) this attribute pertains. If the Tag text box is greater than 0x1F, it should be interpreted as the first byte of the following String text box.
String – This text box must be present. The group is represented by the String text box. There is no restriction on the format of group IDs.

NoteWhen any of the other RADIUS attributes (QoS-Level, ACL-Name, Interface-Name, or VLAN-Tag) are returned, the Tunnel Attributes must also be returned.
Tunnel Attributes
RFC 2868 defines RADIUS tunnel attributes used for authentication and authorization, and RFC2867 defines tunnel attributes used for accounting. Where the IEEE 802.1X authenticator supports tunneling, a compulsory tunnel may be set up for the Supplicant as a result of the authentication.
In particular, it may be desirable to allow a port to be placed into a particular VLAN, defined in IEEE 8021Q, based on the result of the authentication. This configuration can be used, for example, to allow a wireless host to remain on the same VLAN as it moves within a campus network.
The RADIUS server typically indicates the desired VLAN by including tunnel attributes within the Access-Accept. However, the IEEE 802.1X authenticator may also provide a hint as to the VLAN to be assigned to the Supplicant by including Tunnel attributes within the AccessRequest.
For use in VLAN assignment, the following tunnel attributes are used:
The VLAN ID is 12 bits, with a value between 1 and 4094, inclusive. Because the Tunnel-Private-Group-ID is of type String as defined in RFC 2868, for use with IEEE 802.1X, the VLANID integer value is encoded as a string.
When Tunnel attributes are sent, it is necessary to fill in the Tag text box. As noted in RFC 2868, section 3.1:
The Tag text box is one octet in length and is intended to provide a means of grouping attributes in the same packet that refer to the same tunnel. Valid values for this text box are 0x01 through 0x1F, inclusive. If the Tag text box is unused, it must be zero (0x00).
For use with Tunnel-Client-Endpoint, Tunnel-Server-Endpoint, Tunnel-Private-Group-ID, Tunnel-Assignment-ID, Tunnel-Client-Auth-ID or Tunnel-Server-Auth-ID attributes (but not Tunnel-Type, Tunnel-Medium-Type, Tunnel-Password, or Tunnel-Preference), a tag text box of greater than 0x1F is interpreted as the first octet of the following text box.
Unless alternative tunnel types are provided, (e.g. for IEEE 802.1X authenticators that may support tunneling but not VLANs), it is only necessary for tunnel attributes to specify a single tunnel. As a result, where it is only desired to specify the VLANID, the tag text box should be set to zero (0x00) in all tunnel attributes. Where alternative tunnel types are to be provided, tag values between 0x01 and 0x1F should be chosen.
Configuring AAA Override
Information About AAA Override
The AAA Override option of a WLAN enables you to configure the WLAN for identity networking. It enables you to apply VLAN tagging, Quality of Service (QoS), and Access Control Lists (ACLs) to individual clients based on the returned RADIUS attributes from the AAA server.
AAA Override for IPv6 ACLs
In order to support centralized access control through a centralized AAA server such as the Cisco Identity Services Engine (ISE) or ACS, the IPv6 ACL can be provisioned on a per-client basis using AAA Override attributes. In order to use this feature, the IPv6 ACL must be configured on the controller and the WLAN must be configured with the AAA Override feature enabled. The actual named AAA attribute for an IPv6 ACL is Airespace-IPv6-ACL-Name, which is similar to the Airespace-ACL-Name attribute that is used for provisioning an IPv4-based ACL. The AAA attribute returned contents should be a string equal to the name of the IPv6 ACL as configured on the controller.
 Note | From Release 7.5, the upstream AAA override rate limiting value is same as the downstream AAA override rate limiting value. |
Restrictions for AAA Override
-
If a client moves to a new interface due to the AAA override and then you apply an ACL to that interface, the ACL does not take effect until the client reauthenticates. To work around this issue, apply the ACL and then enable the WLAN so that all clients connect to the ACL that is already configured on the interface, or disable and then reenable the WLAN after you apply the interface so that the clients can reauthenticate.
-
When the interface group is mapped to a WLAN and clients connect to the WLAN, the client does not get the IP address in a round robin fashion. The AAA override with interface group is supported.
-
Most of the configuration for allowing AAA override is done at the RADIUS server, where you should configure the Access Control Server (ACS) with the override properties you would like it to return to the controller (for example, Interface-Name, QoS-Level, and VLAN-Tag).
-
On the controller, enable the Allow AAA Override configuration parameter using the GUI or CLI. Enabling this parameter allows the controller to accept the attributes returned by the RADIUS server. The controller then applies these attributes to its clients.
Updating the RADIUS Server Dictionary File for Proper QoS Values
If you are using a Steel-Belted RADIUS (SBR), FreeRadius, or similar RADIUS server, clients may not obtain the correct QoS values after the AAA override feature is enabled. For these servers, which allow you to edit the dictionary file, you need to update the file to reflect the proper QoS values: Silver is 0, Gold is 1, Platinum is 2, and Bronze is 3. To update the RADIUS server dictionary file, follow these steps:
 Note | This issue does not apply to the Cisco Secure Access Control Server (ACS). |
To update the RADIUS server dictionary file, follow these steps:
Save the following text to the Radius_Install_Directory\Service folder as ciscowlan.dct:
################################################################################ # CiscoWLAN.dct- Cisco Wireless Lan Controllers # # (See README.DCT for more details on the format of this file) ################################################################################ # Dictionary - Cisco WLAN Controllers # # Start with the standard Radius specification attributes # @radius.dct # # Standard attributes supported by Airespace # # Define additional vendor specific attributes (VSAs) # MACRO Airespace-VSA(t,s) 26 [vid=14179 type1=%t% len1=+2 data=%s%] ATTRIBUTE WLAN-Id Airespace-VSA(1, integer) cr ATTRIBUTE Aire-QoS-Level Airespace-VSA(2, integer) r VALUE Aire-QoS-Level Bronze 3 VALUE Aire-QoS-Level Silver 0 VALUE Aire-QoS-Level Gold 1 VALUE Aire-QoS-Level Platinum 2 ATTRIBUTE DSCP Airespace-VSA(3, integer) r ATTRIBUTE 802.1P-Tag Airespace-VSA(4, integer) r ATTRIBUTE Interface-Name Airespace-VSA(5, string) r ATTRIBUTE ACL-Name Airespace-VSA(6, string) r # This should be last. ################################################################################ # CiscoWLAN.dct - Cisco WLC dictionary ##############################################################################
Open the dictiona.dcm file (in the same directory) and add the line “@ciscowlan.dct.”
Open the vendor.ini file (in the same directory) and add the following text:
vendor-product = Cisco WLAN Controller dictionary = ciscowlan ignore-ports = no port-number-usage = per-port-type help-id =
Launch the SBR Administrator (or other RADIUS Administrator).
Add a RADIUS client (if not already added). Choose Cisco WLAN Controller from the Make/Model drop-down list.
Configuring AAA Override (GUI)
| Step 1 | Choose WLANs to open the WLANs page. |
| Step 2 | Click the ID number of the WLAN that you want to configure. The WLANs > Edit page appears. |
| Step 3 | Choose the Advanced tab. |
| Step 4 | Select the Allow AAA Override check box to enable AAA override or unselect it to disable this feature. The default value is disabled. |
| Step 5 | Click Apply. |
| Step 6 | Click Save Configuration. |
Configuring AAA Override (CLI)
Configure override of user policy through AAA on a WLAN by entering this command: config wlan aaa-override {enable | disable} wlan-id
For wlan-id, enter a value between 1 and 16.
Configure debugging of 802.1X AAA interactions by entering this command: debug dot1x aaa {enable | disable}
Managing Rogue Devices
Information About Rogue Devices
Rogue access points can disrupt wireless LAN operations by hijacking legitimate clients and using plain-text or other denial-of-service or man-in-the-middle attacks. That is, a hacker can use a rogue access point to capture sensitive information, such as usernames and passwords. The hacker can then transmit a series of Clear to Send (CTS) frames. This action mimics an access point, informing a particular client to transmit, and instructing all the other clients to wait, which results in legitimate clients being unable to access network resources. Wireless LAN service providers have a strong interest in banning rogue access points from the air space.
Because rogue access points are inexpensive and readily available, employees sometimes plug unauthorized rogue access points into existing LANs and build ad hoc wireless networks without their IT department's knowledge or consent. These rogue access points can be a serious breach of network security because they can be plugged into a network port behind the corporate firewall. Because employees generally do not enable any security settings on the rogue access point, it is easy for unauthorized users to use the access point to intercept network traffic and hijack client sessions. Even more alarming, wireless users frequently publish unsecured access point locations, increasing the odds of having enterprise security breached.
-
The containment frames are sent immediately after the authorization and associations are detected. The enhanced containment algorithm provides more effective containment of ad hoc clients.
-
In a dense RF environment, where maximum rogue access points are suspected, the chances of detecting rogue access points by a local mode access point and FlexConnect mode access point in channel 157 or channel 161 are less when compared to other channels. To mitigate this problem, we recommend that you use dedicated monitor mode access points.
-
The local and FlexConnect mode access points are designed to serve associated clients. These access points spend relatively less time performing off-channel scanning: about 50 milliseconds on each channel. If you want to perform high rogue detection, a monitor mode access point must be used. Alternatively, you can reduce the scan intervals from 180 seconds to a lesser value, for example, 120 or 60 seconds, ensuring that the radio goes off-channel more frequently, which improves the chances of rogue detection. However, the access point will still spend about 50 milliseconds on each channel.
-
Rogue detection is disabled by default for OfficeExtend access points because these access points, which are deployed in a home environment, are likely to detect a large number of rogue devices.
-
Client card implementations might mitigate the effectiveness of ad hoc containment.
-
It is possible to classify and report rogue access points through the use of rogue states and user-defined classification rules that enable rogues to automatically move between states.
-
Each controller limits the number of rogue containment to three per radio (or six per radio for access points in the monitor mode).
-
Rogue Location Discovery Protocol (RLDP) detects rogue access points that are configured for open authentication.
-
RLDP detects rogue access points that use a broadcast Basic Service Set Identifier (BSSID), that is, the access point broadcasts its Service Set Identifier in beacons.
-
RLDP detects only those rogue access points that are on the same network. If an access list in the network prevents the sending of RLDP traffic from the rogue access point to the controller, RLDP does not work.
-
RLDP does not work on 5-GHz dynamic frequency selection (DFS) channels. However, RLDP works when the managed access point is in the monitor mode on a DFS channel.
-
If RLDP is enabled on mesh APs, and the APs perform RLDP tasks, the mesh APs are dissociated from the controller. The workaround is to disable RLDP on mesh APs.
-
If RLDP is enabled on nonmonitor APs, client connectivity outages occur when RLDP is in process.
-
If the rogue is manually contained, the rogue entry is retained even after the rogue expires.
-
If the rogue is contained by any other means, such as auto, rule, and AwIPS preventions, the rogue entry is deleted when it expires.
-
The controller will request to AAA server for rogue client validation only once. As a result, if rogue client validation fails on the first attempt then the rogue client will not be detected as a threat any more. To avoid this, add the valid client entries in the authentication server before enabling Validate Rogue Clients Against AAA.
-
In the 7.4 and earlier releases, if a rogue that was already classified by a rule was not reclassified. In the 7.5 release, this behavior is enhanced to allow reclassification of rogues based on the priority of the rogue rule. The priority is determined by using the rogue report that is received by the controller.
- The rogue detector AP fails to co-relate and contain the wired rogue AP on a 5Mhz channel because the MAC address of the rogue AP for WLAN, LAN, 11a radio and 11bg radio are configured with a difference of +/-1 of the rogue BSSID. In the 8.0 release, this behavior is enhanced by increasing the range of MAC address, that the rogue detector AP co-relates the wired ARP MAC and rogue BSSID, by +/-3.
-
The rogue access points with open authentication can be detected on wire. The NAT wired or rogue wired detection is not supported in by WLC (both RLDP and rogue detector AP). The non-adjacent MAC address is supported by rogue detector mode of AP and not by RLDP.
 Note | A rogue AP or client or adhoc containment configuration is not saved after the reload. You have to configure all the rogues again after the reload. |
 Note | No separate command exists for controlling rogue client traps. However, you can enable or disable rogue client traps using the config trapflags rogueap {enable | disable} command, which is also used for rouge APs. In GUI configuration also, you should use the rogue AP flag under Management->SNMP->TrapControl->Security->Rogue AP to control rogue clients. |
Rogue Location Discovery Protocol
Rogue Location Discovery Protocol (RLDP) is an active approach, which is used when rogue AP has no authentication (Open Authentication) configured. This mode, which is disabled by default, instructs an active AP to move to the rogue channel and connect to the rogue as a client. During this time, the active AP sends de-authentication messages to all connected clients and then shuts down the radio interface. Then, it associates to the rogue AP as a client. The AP then tries to obtain an IP address from the rogue AP and forwards a User Datagram Protocol (UDP) packet (port 6352) that contains the local AP and rogue connection information to the controller through the rogue AP. If the controller receives this packet, the alarm is set to notify the network administrator that a rogue AP was discovered on the wired network with the RLDP feature.
RLDP has 100 % accuracy in rouge AP detection. It detects Open APs and NAT APs.
 Note | Use the debug dot11 rldp enable command in order to check if the Lightweight AP associates and receives a DHCP address from the rogue AP. This command also displays the UDP packet sent by the Lightweight AP to the controller. |
A sample of a UDP (destination port 6352) packet sent by the Lightweight AP is shown here: 0020 0a 01 01 0d 0a 01 .......(.*...... 0030 01 1e 00 07 85 92 78 01 00 00 00 00 00 00 00 00 ......x......... 0040 00 00 00 00 00 00 00 00 00 00
The first 5 bytes of the data contain the DHCP address given to the local mode AP by the rogue AP. The next 5 bytes are the IP address of the controller, followed by 6 bytes that represent the rogue AP MAC address. Then, there are 18 bytes of zeroes.
-
Identify the closest Unified AP to the rogue using signal strength values.
-
The AP then connects to the rogue as a WLAN client, attempting three associations before timing out.
-
If association is successful, the AP then uses DHCP to obtain an IP address.
-
If an IP address was obtained, the AP (acting as a WLAN client) sends a UDP packet to each of the controller's IP addresses.
-
If the controller receives even one of the RLDP packets from the client, that rogue is marked as on-wire with a severity of critical.
 Note | The RLDP packets are unable to reach the controller if filtering rules are placed between the controller's network and the network where the rogue device is located. |
-
RLDP only works with open rogue APs broadcasting their SSID with authentication and encryption disabled.
-
RLDP requires that the Managed AP acting as a client is able to obtain an IP address via DHCP on the rogue network.
-
Manual RLDP can be used to attempt an RLDP trace on a rogue multiple number of times.
-
During RLDP process, the AP is unable to serve clients. This negatively impacts performance and connectivity for local mode APs. To avoid this case, RLDP can be selectively enabled for Monitor Mode AP only.
-
RLDP does not attempt to connect to a rogue AP operating in a 5GHz DFS channel.
 Note | RLDP is not supported for use with Cisco autonomous rogue access points. These access points drop the DHCP Discover request sent by the RLDP client. Also, RLDP is not supported if the rogue access point channel requires dynamic frequency selection (DFS). If the automatic RLDP attempt does not detect the rogue (due to a noisy RF environment, for example), the controller does not retry. However, you can initiate RLDP manually on a rogue device. |
Detecting Rogue Devices
The controller continuously monitors all the nearby access points and automatically discovers and collects information on rogue access points and clients. When the controller discovers a rogue access point, it uses the Rogue Location Discovery Protocol (RLDP) and the rogue detector mode access point is connected to determine if the rogue is attached to your network.
Controller initiates RLDP on rogue devices that have open authenticated and configured. If RLDP uses Flexconnect or local mode access points, then clients are disconnected for that moment. After the RLDP cycle, the clients are reconnected to the access points. As and when rogue access points are seen (auto-configuration), the RLDP process is initiated.
You can configure the controller to use RLDP on all the access points or only on the access points configured for the monitor (listen-only) mode. The latter option facilitates automated rogue access point detection in a crowded radio frequency (RF) space, allowing monitoring without creating unnecessary interference and without affecting the regular data access point functionality. If you configure the controller to use RLDP on all the access points, the controller always chooses the monitor access point for RLDP operation if a monitor access point and a local (data) access point are both nearby. If RLDP determines that the rogue is on your network, you can choose to contain the detected rogue either manually or automatically.
RLDP detects on wire presence of the rogue access points that are configured with open authentication only once, which is the default retry configuration. Retries can be configured using the config rogue ap rldp retries command.
- Enter the RLDP initiation
command manually from the controller CLI. The equivalent GUI option for
initiating RLDP is not supported.
config rogue ap rldp initiate mac-address
- Schedule RLDP from the
controller CLI. The equivalent GUI option for scheduling RLDP is not supported.
config rogue ap rldp schedule
- Auto RLDP. You can configure auto RLDP on controller either from controller CLI or GUI but keep in mind the following guidelines:
Individual rogue containment involves sending a sequence of unicast disassociation and deauthentication frames.
Cisco Prime Infrastructure Interaction and Rogue Detection
Cisco Prime Infrastructure supports rule-based classification and uses the classification rules configured on the controller. The controller sends traps to Cisco Prime Infrastructure after the following events:
-
If an unknown access point moves to the Friendly state for the first time, the controller sends a trap to Cisco Prime Infrastructure only if the rogue state is Alert. It does not send a trap if the rogue state is Internal or External.
-
If a rogue entry is removed after the timeout expires, the controller sends a trap to Cisco Prime Infrastructure for rogue access points categorized as Malicious (Alert, Threat) or Unclassified (Alert). The controller does not remove rogue entries with the following rogue states: Contained, Contained Pending, Internal, and External.
Configuring Rogue Detection (GUI)
| Step 1 | Make sure that rogue detection is enabled on the corresponding access points. Rogue detection is enabled by default for all access points joined to the controller (except for OfficeExtend access points). However, you can enable or disable rogue detection for individual access points by selecting or unselecting the Rogue Detection check box on the All APs > Details for (Advanced) page. | ||
| Step 2 | Choose
.
The Rogue Policies page is displayed. | ||
| Step 3 | Choose one of the following options from the Rogue Location Discovery Protocol drop-down list: | ||
| Step 4 | In the
Expiration Timeout for Rogue AP and Rogue Client
Entries text box, enter the number of seconds after which the rogue
access point and client entries expire and are removed from the list. The valid
range is 240 to 3600 seconds, and the default value is 1200 seconds.
| ||
| Step 5 | To use the AAA server or local database to validate if rogue clients are valid clients, select the Validate Rogue Clients Against AAA check box. By default, the check box is unselected. | ||
| Step 6 | If necessary, select the Detect and Report Ad-Hoc Networks check box to enable ad hoc rogue detection and reporting. By default, the check box is selected. | ||
| Step 7 | In the Rogue Detection Report Interval text box, enter the time interval, in seconds, at which APs should send the rogue detection report to the controller. The valid range is 10 seconds to 300 seconds, and the default value is 10 seconds. | ||
| Step 8 | In the
Rogue Detection Minimum
RSSI text box, enter the minimum Received Signal Strength Indicator
(RSSI) value that a rogue entry should have for APs to detect the rogue and for
a rogue entry to be created in the controller. The valid range is –128 dBm to
–0 dBm, and the default value is 0 dBm.
| ||
| Step 9 | In the
Rogue
Detection Transient Interval text box, enter the time interval at
which a rogue should be scanned for by the AP after the first time the rogue is
scanned. After the rogue is scanned for consistently, updates are sent
periodically to the controller. Thus, the APs filter the transient rogues,
which are active for a very short period and are then silent. The valid range
is between 120 seconds to 1800 seconds, and the default value is 0.
The rogue detection transient interval is applicable to the monitor mode APs only. | ||
| Step 10 | If you want the controller to
automatically contain certain rogue devices, enable the following parameters.
By default, these parameters are in disabled state.
| ||
| Step 11 | Click Apply. | ||
| Step 12 | Click Save Configuration. |
Configuring Rogue Detection (CLI)
| Step 1 | Ensure that rogue detection is enabled on the desired
access points. Rogue detection is enabled by default for all the access points
that are associated with the controller. You can enable or disable rogue
detection for individual access points by entering this command:
config rogue detection {enable | disable} cisco-ap command.
| ||||||||
| Step 2 | Enable, disable, or initiate
RLDP by entering these commands:
| ||||||||
| Step 3 | Specify the
number of seconds after which the rogue access point and client entries expire
and are removed from the list by entering this command:
config rogue ap
timeout
seconds
The valid range for the seconds parameter is 240 to 3600 seconds (inclusive). The default value is 1200 seconds.
| ||||||||
| Step 4 | Enable or disable ad hoc rogue detection and reporting by entering this command: | ||||||||
| Step 5 | Enable or disable the AAA server or local database to validate if rogue clients are valid clients by entering this command: | ||||||||
| Step 6 | Specify the time
interval, in seconds, at which APs should send the rogue detection report to
the controller by entering this command:
config rogue detection monitor-ap report-interval time in sec The valid range for the time in sec parameter is 10 seconds to 300 seconds. The default value is 10 seconds.
| ||||||||
| Step 7 | Specify the
minimum RSSI value that rogues should have for APs to detect them and for the
rogue entries to be created in the controller by entering this command:
config rogue detection min-rssi rssi in dBm The valid range for the rssi in dBm parameter is –128 dBm to 0 dBm. The default value is 0 dBm.
| ||||||||
| Step 8 | Specify the time
interval at which rogues have to be consistently scanned for by APs after the
first time the rogues are scanned for by entering this command:
config rogue detection monitor-ap transient-rogue-interval time in sec The valid range for the time in sec parameter is 120 seconds to 1800 seconds. The default value is 0.
| ||||||||
| Step 9 | If you want the controller to
automatically contain certain rogue devices, enter these commands.
| ||||||||
| Step 10 | Configure ad
hoc rogue classification by entering these commands:
| ||||||||
| Step 11 | Configure RLDP
scheduling by entering this command:
| ||||||||
| Step 12 | Save your
changes by entering this command:
|
Classifying Rogue Access Points
Information About Classifying Rogue Access Points
The controller software enables you to create rules that can organize and display rogue access points as Friendly, Malicious, or Unclassified.
By default, none of the classification rules are enabled. Therefore, all unknown access points are categorized as Unclassified. When you create a rule, configure conditions for it, and enable the rule, the unclassified access points are reclassified. Whenever you change a rule, it is applied to all access points (friendly, malicious, and unclassified) in the Alert state only.
 Note | Rule-based rogue classification does not apply to ad hoc rogues and rogue clients. |
 Note | You can configure up to 64 rogue classification rules per controller. |
-
The controller verifies that the unknown access point is in the friendly MAC address list. If it is, the controller classifies the access point as Friendly.
-
If the unknown access point is not in the friendly MAC address list, the controller starts applying rogue classification rules.
-
If the rogue is already classified as Malicious, Alert or Friendly, Internal or External, the controller does not reclassify it automatically. If the rogue is classified differently, the controller reclassifies it automatically only if the rogue is in the Alert state.
-
The controller applies the first rule based on priority. If the rogue access point matches the criteria specified by the rule, the controller classifies the rogue according to the classification type configured for the rule.
-
If the rogue access point does not match any of the configured rules, the controller classifies the rogue as Unclassified.
-
The controller repeats the previous steps for all rogue access points.
-
If RLDP determines that the rogue access point is on the network, the controller marks the rogue state as Threat and classifies it as Malicious automatically, even if no rules are configured. You can then manually contain the rogue (unless you have configured RLDP to automatically contain the rogue), which would change the rogue state to Contained. If the rogue access point is not on the network, the controller marks the rogue state as Alert, and you can manually contain the rogue.
-
If desired, you can manually move the access point to a different classification type and rogue state.
| Friendly |
|
| Malicious |
|
| Unclassified |
|
As mentioned previously, the controller can automatically change the classification type and rogue state of an unknown access point based on user-defined rules, or you can manually move the unknown access point to a different classification type and rogue state.
| Friendly (Internal, External, Alert) | Malicious (Alert) |
| Friendly (Internal, External, Alert) | Unclassified (Alert) |
| Friendly (Alert) | Friendly (Internal, External) |
| Malicious (Alert, Threat) | Friendly (Internal, External) |
| Malicious (Contained, Contained Pending) | Malicious (Alert) |
| Unclassified (Alert, Threat) | Friendly (Internal, External) |
| Unclassified (Contained, Contained Pending) | Unclassified (Alert) |
| Unclassified (Alert) | Malicious (Alert) |
If the rogue state is Contained, you have to uncontain the rogue access point before you can change the classification type. If you want to move a rogue access point from Malicious to Unclassified, you must delete the access point and allow the controller to reclassify it.
Restrictions for Classifying Rogue Access Points
-
Classifying Custom type rogues is tied to rogue rules. Therefore, it is not possible to manually classify a rogue as Custom. Custom class change can occur only using rogue rules.
-
There are traps that are sent for containment by rule and for every 30 minutes for rogue classification change. For custom classification, the first trap does not contain the severity score because the trap has existed before the custom classification. The severity score is obtained from the subsequent trap that is generated after 30 minutes if the rogue is classified.
-
Rogue rules are applied on every incoming new rogue report in the controller in the order of their priority.
-
Once a rogue satisfies a higher priority rule and classified, it does not move down the priority list for the same report.
-
Previously classified rogue gets re-classified on every new rogue report with the following restrictions: -
Rogues which are classified as friendly by rule and whose state is set to ALERT, go through re-classification on receiving the new rogue report.
-
If a rogue is classified as friendly by the administrator manually, then the state is INTERNAL and it does not get re-classified on successive rogue reports.
-
If rogue is classified as malicious, irrespective of the state it does not get re-classified on subsequent rogue reports.
-
-
Transition of the rogue's state from friendly to malicious is possible by multiple rogue rules if some attribute is missing in new rogue report.
-
Transition of the rogue's state from malicious to any other classification is not possible by any rogue rule.
Configuring Rogue Classification Rules (GUI)
| Step 1 | Choose
to open the Rogue Rules page.
Any rules that have already been created are listed in priority order. The name, type, and status of each rule is provided.
| ||
| Step 2 | Create a new
rule as follows:
| ||
| Step 3 | Edit a rule as
follows:
| ||
| Step 4 | Click Save Configuration. | ||
| Step 5 | If you want to
change the order in which rogue classification rules are applied, follow these
steps:
| ||
| Step 6 | Classify any
rogue access points as friendly and add them to the friendly MAC address list
as follows:
|
Viewing and Classifying Rogue Devices (GUI)
 Caution | When you choose to contain a rogue device, the following warning appears: “There may be legal issues following this containment. Are you sure you want to continue?” The 2.4- and 5-GHz frequencies in the Industrial, Scientific, and Medical (ISM) band are open to the public and can be used without a license. As such, containing devices on another party’s network could have legal consequences. |
| Step 1 | Choose Monitor > Rogues. | ||||||
| Step 2 | Choose the following options
to view the different types of rogue access points detected by the controller:
The respective rogue APs pages provide the following information: the MAC address and SSID of the rogue access point, channel number, the number of radios that detected the rogue access point, the number of clients connected to the rogue access point, and the current status of the rogue access point.
| ||||||
| Step 3 | Get more details
about a rogue access point by clicking the MAC address of the access point. The
Rogue AP Detail page appears.
This page provides the following information: the MAC address of the rogue device, the type of rogue device (such as an access point), whether the rogue device is on the wired network, the dates and times when the rogue device was first and last reported, and the current status of the device. The Class Type text box shows the current classification for this rogue access point:
| ||||||
| Step 4 | If you want to
change the classification of this device, choose a different classification
from the Class Type drop-down list.
| ||||||
| Step 5 | From the Update
Status drop-down list, choose one of the following options to specify how the
controller should respond to this rogue access point:
The bottom of the page provides information on both the access points that detected this rogue access point and any clients that are associated to it. To see more details for any of the clients, click Edit to open the Rogue Client Detail page. | ||||||
| Step 6 | Click Apply. | ||||||
| Step 7 | Click Save Configuration. | ||||||
| Step 8 | View any rogue clients that are connected to the controller by choosing Rogue Clients. The Rogue Clients page appears. This page shows the following information: the MAC address of the rogue client, the MAC address of the access point to which the rogue client is associated, the SSID of the rogue client, the number of radios that detected the rogue client, the date and time when the rogue client was last reported, and the current status of the rogue client. | ||||||
| Step 9 | Obtain more details about a rogue client by clicking the MAC address of the client. The Rogue Client Detail page appears. This page provides the following information: the MAC address of the rogue client, the MAC address of the rogue access point to which this client is associated, the SSID and IP address of the rogue client, the dates and times when the rogue client was first and last reported, and the current status of the rogue client. | ||||||
| Step 10 | From the Update
Status drop-down list, choose one of the following options to specify how the
controller should respond to this rogue client:
The bottom of the page provides information on the access points that detected this rogue client. | ||||||
| Step 11 | Click Apply. | ||||||
| Step 12 | If desired, you can test the controller’s connection to this client by clicking Ping. | ||||||
| Step 13 | Click Save Configuration. | ||||||
| Step 14 | See any ad-hoc
rogues detected by the controller by choosing
Adhoc Rogues. The
Adhoc Rogues page appears.
This page shows the following information: the MAC address, BSSID, and SSID of the ad-hoc rogue, the number of radios that detected the ad-hoc rogue, and the current status of the ad-hoc rogue. | ||||||
| Step 15 | Obtain more
details about an ad-hoc rogue by clicking the MAC address of the rogue. The
Adhoc Rogue Detail page appears.
This page provides the following information: the MAC address and BSSID of the ad-hoc rogue, the dates and times when the rogue was first and last reported, and the current status of the rogue. | ||||||
| Step 16 | From the Update Status drop-down list, choose one of the following options to specify how the controller should respond to this ad-hoc rogue: | ||||||
| Step 17 | From the Maximum
number of APs to contain the rogue drop-down list, choose one of the following
options to specify the maximum number of access points used to contain this
ad-hoc rogue:
1,
2,
3, or
4.
The bottom of
the page provides information on the access points that detected this ad-hoc
rogue.
| ||||||
| Step 18 | Click Apply. | ||||||
| Step 19 | Click Save Configuration. | ||||||
| Step 20 | View any access
points that have been configured to be ignored by choosing
Rogue AP
Ignore-List. The Rogue AP Ignore-List page appears.
This page shows the MAC addresses of any access points that are configured to be ignored. The rogue-ignore list contains a list of any autonomous access points that have been manually added to Cisco Prime Infrastructure maps by the users. The controller regards these autonomous access points as rogues even though the Prime Infrastructure is managing them. The rogue-ignore list allows the controller to ignore these access points. The list is updated as follows:
|
Configuring Rogue Classification Rules (CLI)
| Step 1 | Create a rule
by entering this command:
config rogue rule add ap priority priority classify {friendly | malicious} rule-name If you later want to change the priority of this rule and shift others in the list accordingly, enter the config rogue rule priority priority rule-name command. If you later want to change the classification of this rule, enter the config rogue rule classify {friendly | malicious} rule-name command. If you ever want to delete all of the rogue classification rules or a specific rule, enter the {config rogue rule delete {all | rule-name} command. | ||||||
| Step 2 | Disable all
rules or a specific rule by entering this command:
config rogue rule disable {all | rule_name}
| ||||||
| Step 3 | Add conditions
to a rule that the rogue access point must meet by entering this command:
config rogue rule condition ap set condition_type condition_value rule_name The following condition types are available:
| ||||||
| Step 4 | Specify whether a detected rogue access point must meet all or any of the conditions specified by the rule in order for the rule to be matched and the rogue access point to adopt the classification type of the rule by entering this command: | ||||||
| Step 5 | Enable all rules
or a specific rule by entering this command:
config rogue rule
enable {all |
rule_name}
| ||||||
| Step 6 | Add a new friendly access point entry to the friendly MAC address list or delete an existing friendly access point entry from the list by entering this command: | ||||||
| Step 7 | Save your changes by entering this command: | ||||||
| Step 8 | View the rogue classification rules that are configured on the controller by entering this command: show rogue rule summary | ||||||
| Step 9 | View detailed information for a specific rogue classification rule by entering this command: |
Viewing and Classifying Rogue Devices (CLI)
View a list of all rogue access points detected by the controller by entering this command: show rogue ap summary
See a list of the friendly rogue access points detected by the controller by entering this command:
See a list of the malicious rogue access points detected by the controller by entering this command:
See a list of the unclassified rogue access points detected by the controller by entering this command:
See detailed information for a specific rogue access point by entering this command:
See the rogue report (which shows the number of rogue devices detected on different channel widths) for a specific 802.11a/n radio by entering this command:
See a list of all rogue clients that are associated to a rogue access point by entering this command:
See a list of all rogue clients detected by the controller by entering this command:
See detailed information for a specific rogue client by entering this command:
See a list of all ad-hoc rogues detected by the controller by entering this command:
See detailed information for a specific ad-hoc rogue by entering this command:
See a summary of ad hoc rogues based on their classification by entering this command:
show rogue adhoc {friendly | malicious | unclassified} summary
See a list of rogue access points that are configured to be ignore by entering this command:

Note
See the Viewing and Classifying Rogue Devices (GUI) section for more information on the rogue-ignore access point list.
Classify a rogue access point as friendly by entering this command:
config rogue ap classify friendly state {internal | external} ap_mac_address
internal means that the controller trusts this rogue access point.
external means that the controller acknowledges the presence of this rogue access point.

Note
A rogue access point cannot be moved to the Friendly class if its current state is Contain.
Mark a rogue access point as malicious by entering this command:
config rogue ap classify malicious state {alert | contain} ap_mac_address
alert means that the controller forwards an immediate alert to the system administrator for further action.
contain means that the controller contains the offending device so that its signals no longer interfere with authorized clients.

Note
A rogue access point cannot be moved to the Malicious class if its current state is Contain.
Mark a rogue access point as unclassified by entering this command:
config rogue ap classify unclassified state {alert | contain} ap_mac_address

Note
A rogue access point cannot be moved to the Unclassified class if its current state is Contain.
alert means that the controller forwards an immediate alert to the system administrator for further action.
contain means that the controller contains the offending device so that its signals no longer interfere with authorized clients.
Choose the maximum number of access points used to contain the ad-hoc rogue by entering this command:
config rogue ap classify unclassified state contain rogue_ap_mac_address 1, 2, 3, or 4
-
1—Specifies targeted rogue access point will be contained by one access point. This is the lowest containment level.
-
2—Specifies targeted rogue access point will be contained by two access points.
-
3—Specifies targeted rogue access point will be contained by three access points.
-
4—Specifies targeted rogue access point will be contained by four access points. This is the highest containment level.
-
Specify how the controller should respond to a rogue client by entering one of these commands:
config rogue client alert client_mac_address—The controller forwards an immediate alert to the system administrator for further action.
config rogue client contain client_mac_address—The controller contains the offending device so that its signals no longer interfere with authorized clients.
Specify how the controller should respond to an ad-hoc rogue by entering one these commands:
config rogue adhoc alert rogue_mac_address—The controller forwards an immediate alert to the system administrator for further action.
config rogue adhoc contain rogue_mac_address—The controller contains the offending device so that its signals no longer interfere with authorized clients.
config rogue adhoc external rogue_mac_address—The controller acknowledges the presence of this ad-hoc rogue.
Configuring Cisco TrustSec SXP
Information About Cisco TrustSec SXP
Cisco TrustSec enables organizations to secure their networks and services through identity-based access control to anyone, anywhere, anytime. The solution also offers data integrity and confidentiality services, policy-based governance, and centralized monitoring, troubleshooting, and reporting services. TrustSec can be combined with personalized, professional service offerings to simplify solution deployment and management, and is a foundational security component to Cisco Borderless Networks.
The Cisco TrustSec security architecture builds secure networks by establishing domains of trusted network devices. Each device in the domain is authenticated by its peers. Communication on the links between devices in the domain is secured with a combination of encryption, message integrity check, and data-path replay protection mechanisms. Cisco TrustSec uses the device and user credentials acquired during authentication for classifying the packets by security groups (SGs) as they enter the network. This packet classification is maintained by tagging packets on ingress to the Cisco TrustSec network so that they can be correctly identified to apply security and other policy criteria along the data path. The tag, called the security group tag (SGT), allows the network to enforce the access control policy by enabling the endpoint device to act upon the SGT to filter traffic.
One of the components of Cisco TrustSec architecture is the security group-based access control. In the security group-based access control component, access policies in the Cisco TrustSec domain are topology-independent, based on the roles (as indicated by security group number) of source and destination devices rather than on network addresses. Individual packets are tagged with the security group number of the source.
Cisco devices use the SGT Exchange Protocol (SXP) to propagate SGTs across network devices that do not have hardware support for Cisco TrustSec. SXP is the software solution to avoid CTS hardware upgrade on all switches. WLC will be supporting SXP as part of TrustSec Architecture. The SXP sends SGT information to the CTS-enabled switches so that appropriate role-based access control lists (RBACLs) can be activated depending on the role information represented by the SGT. By default, the controller always works in the Speaker mode. To implement the SXP on a network, only the egress distribution switch needs to be CTS-enabled, and all the other switches can be non-CTS-capable switches.
The SXP runs between any access layer and distribution switch or between two distribution switches. The SXP uses TCP as the transport layer. CTS authentication is performed for any host (client) joining the network on the access layer switch similar to an access switch with CTS-enabled hardware. The access layer switch is not CTS hardware enabled. Therefore, data traffic is not encrypted or cryptographically authenticated when it passes through the access layer switch. The SXP is used to pass the IP address of the authenticated device, that is a wireless client, and the corresponding SGT up to the distribution switch. If the distribution switch is CTS hardware enabled, the switch inserts the SGT into the packet on behalf of the access layer switch. If the distribution switch is not CTS hardware enabled, the SXP on the distribution switch passes the IP-SGT mapping to all the distribution switches that have CTS hardware. On the egress side, the enforcement of the RBACL occurs at the egress L3 interface on the distribution switch.
For more information about Cisco TrustSec, see http://www.cisco.com/c/en/us/solutions/enterprise-networks/trustsec/index.html.
Restrictions for Cisco TrustSec SXP
-
SXP is supported only in centrally switched networks that have central authentication.
-
By default, SXP is supported for APs that work in local mode only.
-
The configuration of the default password should be consistent for both controller and the switch.
-
Fault tolerance is not supported because fault tolerance requires local switching on APs.
-
Static IP-SGT mapping for local authentication of users is not supported.
-
IP-SGT mapping requires authentication with external ACS servers.
-
In auto-anchor/guest-anchor mobility the SGT information passed by the RADIUS server to foreign WLC can be communicated to the anchor WLC through the EoIP/CAPWAP mobility tunnel. The anchor WLC can then build the SGT-IP mapping and communicate it to another peer via SXP.
Configuring Cisco TrustSec SXP (GUI)
| Step 1 | Choose Security > TrustSec SXP to open the SXP Configuration page. This page lists the following SXP configuration details:
This page also displays the following information about SXP connections:
|
| Step 2 | From the SXP State drop-down list, choose Enabled to enable Cisco TrustSec SXP. |
| Step 3 | Enter the default password that should be used to make an SXP connection. We recommend that the password contain a minimum of 6 characters. |
| Step 4 | In the Retry Period box, enter the time in seconds that determines how often the Cisco TrustSec software retries for an SXP connection. |
| Step 5 | Click Apply. |
Creating a New SXP Connection (GUI)
Configuring Cisco TrustSec SXP (CLI)
Enable or disable the SXP on the controller by entering this command:
Configure the default password for MD5 Authentication of SXP messages by entering this command:
Configure the IP address of the next hop switch with which the controller is connected by entering this command:
Configure the interval between connection attempts by entering this command:
config cts sxp retry period time-in-seconds
Remove an SXP connection by entering this command:
See a summary of SXP configuration by entering this command:
Information similar to the following appears:
SXP State........................................ Enable SXP Mode......................................... Speaker Default Password................................. **** Default Source IP................................ 209.165.200.224 Connection retry open period .................... 120
See the list of SXP connections that are configured by entering this command:
Information similar to the following appears:
Total num of SXP Connections..................... 1 SXP State........................................ Enable Peer IP Source IP Connection Status --------------- --------------- ----------------- 209.165.200.229 209.165.200.224 On
Configuring Cisco Intrusion Detection System
Information About Cisco Intrusion Detection System
The Cisco Intrusion Detection System/Intrusion Prevention System (CIDS/CIPS) instructs controllers to block certain clients from accessing the wireless network when attacks involving these clients are detected at Layer 3 through Layer 7. This system offers significant network protection by helping to detect, classify, and stop threats including worms, spyware/adware, network viruses, and application abuse. Two methods are available to detect potential attacks:
You can configure IDS sensors to detect various types of IP-level attacks in your network. When the sensors identify an attack, they can alert the controller to shun the offending client. When you add a new IDS sensor, you register the controller with that IDS sensor so that the controller can query the sensor to get the list of shunned clients.
Shunned Clients
When an IDS sensor detects a suspicious client, it alerts the controller to shun this client. The shun entry is distributed to all controllers within the same mobility group. If the client to be shunned is currently joined to a controller in this mobility group, the anchor controller adds this client to the dynamic exclusion list, and the foreign controller removes the client. The next time that the client tries to connect to a controller, the anchor controller rejects the handoff and informs the foreign controller that the client is being excluded.
Additional Information
The Cisco wireless intrusion prevention system (wIPS) is also supported on the controller through Cisco Prime Infrastructure. See the Configuring wIPS section for more information.
Configuring IDS Sensors (GUI)
| Step 1 | Choose
to open the CIDS Sensors List
page.
| ||
| Step 2 | Click New to add a new IDS sensor to the list. The CIDS Sensor Add page is displayed. | ||
| Step 3 | From the
Index drop-down list, choose a number (between 1 and
5) to determine the sequence in which the controller consults the IDS sensors.
For example, if you choose 1, the controller consults this IDS sensor first.
Cisco WLC supports up to five IDS sensors. | ||
| Step 4 | In the Server Address text box, enter the IP address of your IDS server. | ||
| Step 5 | In the
Port text box, enter the number of the HTTPS port
through which the controller has to communicate with the IDS sensor.
We recommend that you set this parameter to 443 because the sensor uses this value to communicate by default. The default value is 443 and the range is 1 to 65535. | ||
| Step 6 | In the
Username text box, enter the name that the
controller uses to authenticate to the IDS sensor.
| ||
| Step 7 | In the Password and Confirm Password text boxes, enter the password that the controller uses to authenticate to the IDS sensor. | ||
| Step 8 | In the
Query
Interval text box, enter the time (in seconds) for how often the
controller should query the IDS server for IDS events.
The default is 60 seconds and the range is 10 to 3600 seconds. | ||
| Step 9 | Check the State check box to register the controller with this IDS sensor or uncheck this check box to disable registration. The default value is disabled. | ||
| Step 10 | Enter a 40-hexadecimal-character security key in the
Fingerprint text box. This key is used to verify the
validity of the sensor and is used to prevent security attacks.
| ||
| Step 11 | Click Apply. Your new IDS sensor appears in the list of sensors on the CIDS Sensors List page. | ||
| Step 12 | Click Save Configuration. |
Viewing Shunned Clients (GUI)
| Step 1 | Choose Security > Advanced > CIDS > Shunned Clients to open the CIDS Shun List page. This page shows the IP address and MAC address of each shunned client, the length of time that the client’s data packets should be blocked by the controller as requested by the IDS sensor, and the IP address of the IDS sensor that discovered the client. | ||
| Step 2 | Click Re-sync to purge and reset the list as desired.
|
Configuring IDS Sensors (CLI)
| Step 1 | Add an IDS sensor by entering this command: config wps cids-sensor add index ids_ip_address username password. The index parameter determines the sequence in which the controller consults the IDS sensors. The controller supports up to five IDS sensors. Enter a number (between 1 and 5) to determine the priority of this sensor. For example, if you enter 1, the controller consults this IDS sensor first.
| ||
| Step 2 | (Optional) Specify the number of the HTTPS port through which the controller is to communicate with the IDS sensor by entering this command: config wps cids-sensor port index port For the port-number parameter, you can enter a value between 1 and 65535. The default value is 443. This step is optional because we recommend that you use the default value of 443. The sensor uses this value to communicate by default. | ||
| Step 3 | Specify how often the controller should query the IDS server for IDS events by entering this command: config wps cids-sensor interval index interval For the interval parameter, you can enter a value between 10 and 3600 seconds. The default value is 60 seconds. | ||
| Step 4 | Enter a 40-hexadecimal-character security key used to verify the validity of the sensor by entering this command: config wps cids-sensor fingerprint index sha1 fingerprint You can get the value of the fingerprint by entering show tls fingerprint on the sensor’s console.
| ||
| Step 5 | Enable or disable this controller’s registration with an IDS sensor by entering this command: config wps cids-sensor {enable | disable} index | ||
| Step 6 | Enable or disable protection from DoS attacks by entering this command: The default value is disabled.
| ||
| Step 7 | Save your settings by entering this command: save config | ||
| Step 8 | See the IDS sensor configuration by entering one of these commands: | ||
| Step 9 | The second command provides more information than the first. | ||
| Step 10 | See the auto-immune configuration setting by entering this command:
Information similar to the following appears: Auto-Immune Auto-Immune.................................... Disabled Client Exclusion Policy Excessive 802.11-association failures.......... Enabled Excessive 802.11-authentication failures....... Enabled Excessive 802.1x-authentication................ Enabled IP-theft....................................... Enabled Excessive Web authentication failure........... Enabled Signature Policy Signature Processing........................... Enabled | ||
| Step 11 | Obtain debug information regarding IDS sensor configuration by entering this command: debug wps cids enable
|
Viewing Shunned Clients (CLI)
| Step 1 | View the list of clients to be shunned by entering this command: show wps shun-list | ||
| Step 2 | Force the controller to synchronize with other controllers in the mobility group for the shun list by entering this command: config wps shun-list re-sync
|
Configuring IDS Signatures
Information About IDS Signatures
You can configure IDS signatures, or bit-pattern matching rules used to identify various types of attacks in incoming 802.11 packets, on the controller. When the signatures are enabled, the access points joined to the controller perform signature analysis on the received 802.11 data or management frames and report any discrepancies to the controller. If an attack is detected, appropriate mitigation is initiated.
Cisco supports 17 standard signatures. These signatures are divided into six main groups. The first four groups contain management signatures, and the last two groups contain data signatures.
Broadcast deauthentication frame signatures—During a broadcast deauthentication frame attack, a hacker sends an 802.11 deauthentication frame to the broadcast MAC destination address of another client. This attack causes the destination client to disassociate from the access point and lose its connection. If this action is repeated, the client experiences a denial of service. When the broadcast deauthentication frame signature (precedence 1) is used to detect such an attack, the access point listens for clients transmitting broadcast deauthentication frames that match the characteristics of the signature. If the access point detects such an attack, it alerts the controller. Depending on how your system is configured, the offending device is contained so that its signals no longer interfere with authorized clients, or the controller forwards an immediate alert to the system administrator for further action, or both.
NULL probe response signatures—During a NULL probe response attack, a hacker sends a NULL probe response to a wireless client adapter. As a result, the client adapter locks up. When a NULL probe response signature is used to detect such an attack, the access point identifies the wireless client and alerts the controller. The NULL probe response signatures are as follows:

NoteController does not log historical NULL Probe IDS events within the Signature Events Summary output.
Management frame flood signatures—During a management frame flood attack, a hacker floods an access point with 802.11 management frames. The result is a denial of service to all clients associated or attempting to associate to the access point. This attack can be implemented with different types of management frames: association requests, authentication requests, reassociation requests, probe requests, disassociation requests, deauthentication requests, and reserved management subtypes.
When a management frame flood signature is used to detect such an attack, the access point identifies management frames matching the entire characteristic of the signature. If the frequency of these frames is greater than the value of the frequency set in the signature, an access point that hears these frames triggers an alarm. The controller generates a trap and forwards it to Cisco Prime Infrastructure.
Wellenreiter signature—Wellenreiter is a wireless LAN scanning and discovery utility that can reveal access point and client information. When the Wellenreiter signature (precedence 17) is used to detect such an attack, the access point identifies the offending device and alerts the controller.
EAPOL flood signature—During an EAPOL flood attack, a hacker floods the air with EAPOL frames that contain 802.1X authentication requests. As a result, the 802.1X authentication server cannot respond to all of the requests and fails to send successful authentication responses to valid clients. The result is a denial of service to all affected clients. When the EAPOL flood signature (precedence 12) is used to detect such an attack, the access point waits until the maximum number of allowed EAPOL packets is exceeded. It then alerts the controller and proceeds with the appropriate mitigation.
NetStumbler signatures—NetStumbler is a wireless LAN scanning utility that reports access point broadcast information (such as operating channel, RSSI information, adapter manufacturer name, SSID, WEP status, and the latitude and longitude of the device running NetStumbler when a GPS is attached). If NetStumbler succeeds in authenticating and associating to an access point, it sends a data frame with the following strings, depending on the NetStumbler version:
When a NetStumbler signature is used to detect such an attack, the access point identifies the offending device and alerts the controller. The NetStumbler signatures are as follows:
A standard signature file exists on the controller by default. You can upload this signature file from the controller, or you can create a custom signature file and download it to the controller or modify the standard signature file to create a custom signature.
Configuring IDS Signatures (GUI)
Uploading or Downloading IDS Signatures
| Step 1 | If desired, create your own custom signature file. | ||
| Step 2 | Make sure that you have a
Trivial File Transfer Protocol (TFTP) server available. Follow these guidelines
when setting up a TFTP server:
| ||
| Step 3 | If you are downloading a custom signature file (*.sig), copy it to the default directory on your TFTP server. | ||
| Step 4 | Choose Commands to open the Download File to Controller page. | ||
| Step 5 | Perform one of
the following:
| ||
| Step 6 | From the
Transfer Mode drop-down list, choose
TFTP,
FTP, or
SFTP.
The SFTP option was added in Release 7.4. | ||
| Step 7 | In the IP Address text box, enter the IP address of the TFTP, FTP, or SFTP server. | ||
| Step 8 | If you are
downloading the signature file using a TFTP server, enter the maximum number of
times that the controller should attempt to download the signature file in the
Maximum retries text box.
The range is 1 to 254 and the default value is 10. | ||
| Step 9 | If you are
downloading the signature file using a TFTP server, enter the amount of time in
seconds before the controller times out while attempting to download the
signature file in the
Timeout text box.
The range is 1 to 254 seconds and the default is 6 seconds. | ||
| Step 10 | In the File Path text box, enter the path of the signature file to be downloaded or uploaded. The default value is “/.” | ||
| Step 11 | In the
File Name text box, enter the name of the
signature file to be downloaded or uploaded.
| ||
| Step 12 | If you are using
an FTP or SFTP server, follow these steps:
| ||
| Step 13 | Choose Download to download the signature file to the controller or Upload to upload the signature file from the controller. |
Enabling or Disabling IDS Signatures
| Step 1 | Choose or Custom Signatures to open the Standard Signatures page or the Custom Signatures page. The Standard Signatures page shows the list of Cisco-supplied signatures that are currently on the controller. The Custom Signatures page shows the list of customer-supplied signatures that are currently on the controller. This page shows the following information for each signature:
|
| Step 2 | Perform one of the following:
|
| Step 3 | Click Apply to commit your changes. |
| Step 4 | Click the precedence number of the desired signature to enable or disable an individual signature. The Standard Signature (or Custom Signature) > Detail page appears. This page shows much of the same information as the Standard Signatures and Custom Signatures pages but provides these additional details:
|
| Step 5 | In the Measurement Interval text box, enter the number of seconds that must elapse before the signature frequency threshold is reached within the configured interval. The range is 1 to 3600 seconds, and the default value varies per signature. |
| Step 6 | In the Signature Frequency text box, enter the number of matching packets per interval that must be identified at the individual access point level before an attack is detected. The range is 1 to 32,000 packets per interval, and the default value varies per signature. |
| Step 7 | In the Signature MAC Frequency text box, enter the number of matching packets per interval that must be identified per client per access point before an attack is detected. The range is 1 to 32,000 packets per interval, and the default value varies per signature. |
| Step 8 | In the Quiet Time text box, enter the length of time (in seconds) after which no attacks have been detected at the individual access point level and the alarm can stop. The range is 60 to 32,000 seconds, and the default value varies per signature. |
| Step 9 | Select the State check box to enable this signature to detect security attacks or unselect it to disable this signature. The default value is enabled (or selected). |
| Step 10 | Click Apply to commit your changes. The Standard Signatures or Custom Signatures page reflects the signature’s updated state. |
| Step 11 | Click Save Configuration to save your changes. |
Viewing IDS Signature Events (GUI)
| Step 1 | Choose Security > Wireless Protection Policies > Signature Events Summary to open the Signature Events Summary page. |
| Step 2 | Click the Signature Type for the signature to see more information on the attacks detected by a particular signature. The Signature Events Detail page appears. |
| Step 3 | Click the Detail link for that attack to see more information for a particular attack. The Signature Events Track Detail page appears. |
Configuring IDS Signatures (CLI)
| Step 1 | If desired, create your own custom signature file. | ||
| Step 2 | Make sure that you have a TFTP server available. | ||
| Step 3 | Copy the custom signature file (*.sig) to the default directory on your TFTP server. | ||
| Step 4 | Specify the download or upload mode by entering the transfer {download | upload} mode tftp command. | ||
| Step 5 | Specify the type of file to be downloaded or uploaded by entering the transfer {download | upload} datatype signature command. | ||
| Step 6 | Specify the IP address of the
TFTP server by entering the
transfer {download |
upload}
serverip
tftp-server-ip-address command.
| ||
| Step 7 | Specify the download or upload path by entering the transfer {download | upload} path absolute-tftp-server-path-to-file command. | ||
| Step 8 | Specify the file to be
downloaded or uploaded by entering the
transfer
{download |
upload}
filename
filename.sig command.
| ||
| Step 9 | Enter the transfer {download | upload} start command and answer y to the prompt to confirm the current settings and start the download or upload. | ||
| Step 10 | Specify the number of seconds
that must elapse before the signature frequency threshold is reached within the
configured interval by entering this command:
config wps signature interval signature_id interval where signature_id is a number used to uniquely identify a signature. The range is 1 to 3600 seconds, and the default value varies per signature. | ||
| Step 11 | Specify the
number of matching packets per interval that must be identified at the
individual access point level before an attack is detected by entering this
command:
config wps signature frequencysignature_id frequency The range is 1 to 32,000 packets per interval, and the default value varies per signature. | ||
| Step 12 | Specify the number of matching packets per
interval that must be identified per client per access point before an attack
is detected by entering this command:
config wps signature mac-frequency signature_id mac_frequency The range is 1 to 32,000 packets per interval, and the default value varies per signature. | ||
| Step 13 | Specify the length of time (in seconds) after which
no attacks have been detected at the individual access point level and the
alarm can stop by entering by entering this command:
config wps signature quiet-time signature_id quiet_time The range is 60 to 32,000 seconds, and the default value varies per signature. | ||
| Step 14 | Perform one of
the following:
| ||
| Step 15 | Save your changes by entering this command: save config | ||
| Step 16 | If desired, you
can reset a specific signature or all signatures to default values. To do so,
enter this command:
config wps signature
reset {signature_id |
all}
|
Viewing IDS Signature Events (CLI)
See whether IDS signature processing is enabled or disabled on the controller by entering this command:

NoteIf IDS signature processing is disabled, all signatures are disabled, regardless of the state configured for individual signatures.
See individual summaries of all of the standard and custom signatures installed on the controller by entering this command:
See the number of attacks detected by the enabled signatures by entering this command:
See more information on the attacks detected by a particular standard or custom signature by entering this command:
show wps signature events {standard | custom} precedence# summary
See information on attacks that are tracked by access points on a per-signature and per-channel basis by entering this command:
show wps signature events {standard | custom} precedence# detailed per-signature source_mac
See information on attacks that are tracked by access points on an individual-client basis (by MAC address) by entering this command:
show wps signature events {standard | custom} precedence# detailed per-mac source_mac
Configuring wIPS
Information About wIPS
The Cisco Adaptive Wireless Intrusion Prevention System (wIPS) uses an advanced approach to wireless threat detection and performance management. It combines network traffic analysis, network device and topology information, signature-based techniques, and anomaly detection to deliver highly accurate and complete wireless threat prevention. With a fully infrastructure-integrated solution, you can continually monitor wireless traffic on both the wired and wireless networks and use that network intelligence to analyze attacks from many sources to accurately pinpoint and proactively prevent attacks, rather than wait until damage or exposure has occurred.
Cisco Adaptive wIPS is a part of the Cisco 3300 Series Mobility Services Engine (MSE), which centralizes the processing of intelligence collected by the continuous monitoring of Cisco Aironet APs. With Cisco Adaptive wIPS functionalities and Cisco Prime Infrastructure integration into the Cisco MSE, the wIPS can configure and monitor wIPS policies and alarms and report threats.
 Note | If your wIPS deployment consists of a Cisco WLC, access point, and Cisco MSE, you must set all the three entities to the UTC time zone. |
Cisco Adaptive wIPS is not configured on the Cisco WLC. Instead, the Cisco Prime Infrastructure forwards the profile configuration to the wIPS service, which forwards the profile to the Cisco WLC. The profile is stored in flash memory on the Cisco WLC and sent to APs when they join the Cisco WLC. When an access point disassociates and joins another Cisco WLC, it receives the wIPS profile from the new Cisco WLC.
Local-mode or FlexConnect mode APs with a subset of wIPS capabilities are referred to as Enhanced Local Mode access point or ELM AP. You can configure an access point to work in the wIPS mode if the AP is in any of the following modes:
The regular local mode or FlexConnect mode AP is extended with a subset of wIPS capabilities. This feature enables you to deploy your APs to provide protection without needing a separate overlay network.
wIPS ELM has the limited capability of detecting off-channel alarms. AN AP periodically goes off-channel, and monitors the nonserving channels for a short duration, and triggers alarms if any attack is detected on the channel. But off-channel alarm detection is best effort, and it takes a longer time to detect attacks and trigger alarms, which might cause the ELM AP to intermittently detect an alarm and clear it because it is not visible. APs in any of the above modes can periodically send alarms based on the policy profile to the wIPS service through the Cisco WLC. The wIPS service stores and processes the alarms and generates SNMP traps. Cisco Prime Infrastructure configures its IP address as a trap destination to receive SNMP traps from the Cisco MSE.
This table lists all the SNMP trap controls and their respective traps. When a trap control is enabled, all the traps of that trap control are also enabled.
 Note | The Cisco WLC uses only SNMPv2 for SNMP trap transmission. |
|
newRoot, topologyChange, stpInstanceNewRootTrap, stpInstanceTopologyChangeTrap |
||
|
bsnDot11EssCreated, bsnDot11EssDeleted, bsnConfigSaved, ciscoLwappScheduledResetNotif, ciscoLwappClearResetNotif, ciscoLwappResetFailedNotif, ciscoLwappSysInvalidXmlConfig |
||
|
NAC Alert |
cldcClientWlanProfileName, cldcClientIPAddress, cldcApMacAddress, cldcClientQuarantineVLAN, cldcClientAccessVLAN |
|
|
bsnTooManyUnsuccessLoginAttempts, cLWAGuestUserLoggedIn, cLWAGuestUserLoggedOut |
||
|
bsnRADIUSServerNotResponding, ciscoLwappAAARadiusReqTimedOut |
||
|
bsnAdhocRogueAutoContained, bsnRogueApAutoContained, bsnTrustedApHasInvalidEncryption, bsnMaxRogueCountExceeded, bsnMaxRogueCountClear, bsnApMaxRogueCountExceeded, bsnApMaxRogueCountClear, bsnTrustedApHasInvalidRadioPolicy, bsnTrustedApHasInvalidSsid, bsnTrustedApIsMissing |
||
The following are the trap descriptions for the traps mentioned in the SNMP Trap Controls and Their Respective Traps table:
- General Traps
- SNMP Authentication—The
SNMPv2 entity has received a protocol message that is not properly
authenticated.

Note
When a user who is configured in SNMP V3 mode tries to access the Cisco WLC with an incorrect password, the authentication fails and a failure message is displayed. However, no trap logs are generated for the authentication failure. - Link (Port) Up/Down—Link changes status from up or down.
- Link (Port) Up/Down—Link changes status from up or down.
- Multiple Users—Two users log in with the same ID.
- Rogue AP—Whenever a rogue access point is detected, this trap is sent with its MAC address; when a rogue access point that was detected earlier no longer exists, this trap is sent.
- Config Save—Notification that is sent when the Cisco WLC configuration is modified.
- SNMP Authentication—The
SNMPv2 entity has received a protocol message that is not properly
authenticated.
- Cisco AP Traps
- Client-Related Traps
- 802.11 Association—Associate notification that is sent when a client sends an association frame.
- 802.11 Disassociation—Disassociate notification that is sent when a client sends a disassociation frame.
- 802.11 Deauthentication—Deauthenticate notification that is sent when a client sends a deauthentication frame.
- 802.11 Failed Authentication—Authenticate failure notification that is sent when a client sends an authentication frame with a status code other than successful.
- 802.11 Failed Association—Associate failure notification that is sent when the client sends an association frame with a status code other than successful.
- Exclusion—Associate failure notification that is sent when a client is exclusion listed (blacklisted).
-
Authentication—Authentication notification that is sent when a client is successfully authenticated.
-
Max Clients Limit Reached—Notification that is sent when the maximum number of clients, defined in the Threshold field, are associated with the Cisco WLC.
-
NAC Alert—Alert that is sent when a client joins an SNMP NAC-enabled WLAN.
This notification is generated when a client on NAC-enabled SSIDs completes Layer2 authentication to inform the NAC appliance about the client's presence. cldcClientWlanProfileName represents the profile name of the WLAN that the 802.11 wireless client is connected to, cldcClientIPAddress represents the unique IP address of the client. cldcApMacAddress represents the MAC address of the AP to which the client is associated. cldcClientQuarantineVLAN represents the quarantine VLAN for the client. cldcClientAccessVLAN represents the access VLAN for the client.
-
Association with Stats—Associate notification that is sent with data statistics when a client is associated with the Cisco WLC, or roams. Data statistics include transmitted and received bytes and packets.
-
Disassociation with Stats—Disassociate notification that is sent with data statistics when a client disassociates from the Cisco WLC. Data statistics include transmitted and received bytes and packets, SSID, and session ID.
- Security Traps
- User Auth Failure—This trap informs that a client RADIUS Authentication failure has occurred.
- RADIUS Server No Response—This trap is to indicate that no RADIUS servers are responding to authentication requests sent by the RADIUS client.
- WEP Decrypt Error—Notification sent when the Cisco WLC detects a WEP decrypting error.
- Rouge AP—Whenever a rogue access point is detected, this trap is sent with its MAC address; when a rogue access point that was detected earlier no longer exists, this trap is sent.
- SNMP Authentication—The
SNMPv2 entity has received a protocol message that is not properly
authenticated.

Note
When a user who is configured in SNMP V3 mode tries to access the Cisco WLC with an incorrect password, authentication fails and a failure message is displayed. However, no trap logs are generated for the authentication failure. - Multiple Users—Two users log in with the same ID.
- SNMP Authentication
- Load Profile—Notification sent when the Load Profile state changes between PASS and FAIL.
- Noise Profile—Notification sent when the Noise Profile state changes between PASS and FAIL.
- Interference Profile—Notification sent when the Interference Profile state changes between PASS and FAIL.
- Coverage Profile—Notification sent when the Coverage Profile state changes between PASS and FAIL.
- Auto RF Profile Traps
- Load Profile—Notification sent when the Load Profile state changes between PASS and FAIL.
- Noise Profile—Notification sent when the Noise Profile state changes between PASS and FAIL.
- Interference Profile—Notification sent when the Interference Profile state changes between PASS and FAIL.
- Coverage Profile—Notification sent when the Coverage Profile state changes between PASS and FAIL.
- Auto RF Update Traps
- Mesh Traps
- Child Excluded Parent—Notification that is sent when a defined number of failed association to the Cisco WLC occurs through a parent mesh node.
- Notification sent when a child mesh node exceeds the threshold limit of the number of discovery response timeouts. The child mesh node does not try to associate an excluded parent mesh node for the interval defined. The child mesh node remembers the excluded parent MAC address when it joins the network, and informs the Cisco WLC.
- Parent Change—Notification is sent by the agent when a child mesh node changes its parent. The child mesh node remembers previous parent and informs the Cisco WLC about the change of parent when it rejoins the network.
- Child Moved—Notification sent when a parent mesh node loses connection with its child mesh node.
- Excessive Parent Change—Notification sent when the child mesh node changes its parent frequently. Each mesh node keeps a count of the number of parent changes in a fixed time. If it exceeds the defined threshold, the child mesh node informs the Cisco WLC.
- Excessive Children—Notification sent when the child count exceeds for a RAP and a MAP.
- Poor SNR—Notification sent when the child mesh node detects a lower SNR on a backhaul link. For the other trap, a notification is sent to clear a notification when the child mesh node detects an SNR on a backhaul link that is higher then the object defined by 'clMeshSNRThresholdAbate'.
- Console Login—Notification is sent by the agent when a login on a MAP console is either successful or fail after three attempts.
- Default Bridge Group Name—Notification sent when the MAP mesh node joins its parent using the default bridge group name.
 Note | The remaining traps do not have trap controls. These traps are not generated too frequently and do not require any trap control. Any other trap that is generated by the Cisco WLC cannot be turned off. |
 Note | In all of the above cases, the Cisco WLC functions solely as a forwarding device. |
Restrictions for wIPS
Configuring wIPS on an Access Point (GUI)
| Step 1 | Choose Wireless > Access Points > All APs > access point name. |
| Step 2 | Set the AP Mode parameter. To configure an access point for wIPS, you must choose one of the following modes from the AP Mode drop-down list: |
| Step 3 | Choose wIPS from the AP Sub Mode drop-down list. |
| Step 4 | Click Apply. |
| Step 5 | Click Save Configuration. |
Configuring wIPS on an Access Point (CLI)
| Step 1 | Configure an access point for
the monitor mode by entering this command:
config ap mode
{monitor | local | flexconnect}
Cisco_AP
| ||
| Step 2 | Enter Y when you see the message that the access point will be rebooted if you want to continue. | ||
| Step 3 | Save your
changes by entering this command:
save config | ||
| Step 4 | Disable the access point radio by entering this command: config {802.11a | 802.11b} disable Cisco_AP | ||
| Step 5 | Configure the
wIPS submode on the access point by entering this command:
config ap mode
ap_mode submode wips
Cisco_AP
| ||
| Step 6 | Enable
wIPS-optimized channel scanning for the access point by entering this command:
config ap monitor-mode wips-optimized Cisco_AP The access point scans each channel for 250 milliseconds. It derives the list of channels to be scanned from the monitor configuration. You can choose one of these options:
The 802.11a or 802.11b Monitor Channels information in the output of the show advanced {802.11a | 802.11b} monitor command shows the monitor configuration channel set: Default 802.11b AP monitoring 802.11b Monitor Mode........................... enable 802.11b Monitor Channels....................... Country channels 802.11b AP Coverage Interval................... 180 seconds 802.11b AP Load Interval....................... 60 seconds 802.11b AP Noise Interval...................... 180 seconds 802.11b AP Signal Strength Interval............ 60 seconds | ||
| Step 7 | Reenable the access point radio by entering this command: config { 802.11a | 802.11b} enable Cisco_AP | ||
| Step 8 | Save your changes by entering this command: save config |
Viewing wIPS Information (CLI)
 Note | You can also view the access point submode from the controller GUI. To do so, choose Wireless > Access Points > All APs > access point name > the Advanced tab. The AP Sub Mode field shows wIPS if the access point is in the monitor mode and the wIPS submode is configured on the access point, or None if the access point is not in the monitor mode or the access point is in the monitor mode, but the wIPS submode is not configured. |
See the wIPS submode in the access point by entering this command: show ap config general Cisco_AP
See the wIPS-optimized channel-scanning configuration in the access point by entering this command:
See the wIPS configuration forwarded by Cisco Prime Infrastructure to the controller by entering this command: show wps wips summary
See the current state of the wIPS operation in the controller by entering this command: show wps wips statistics
Clear the wIPS statistics in the controller by entering this command: clear stats wps wips
Configuring Wi-Fi Direct Client Policy
Information About the Wi-Fi Direct Client Policy
Devices that are Wi-Fi Direct capable can connect directly to each other quickly and conveniently to do tasks such as printing, synchronization, and sharing of data. Wi-Fi Direct devices may associate with multiple peer-to-peer (P2P) devices and with infrastructure wireless LANs (WLANs) concurrently. You can use the controller to configure the Wi-Fi Direct Client Policy, on a per WLAN basis, where you can allow or disallow association of Wi-Fi devices with infrastructure WLANs, or disable Wi-Fi Direct Client Policy altogether for WLANs.
Restrictions for the Wi-Fi Direct Client Policy
Configuring the Wi-Fi Direct Client Policy (GUI)
| Step 1 | Choose WLANs to open the WLANs page. |
| Step 2 | Click the WLAN ID of the WLAN for which you want to configure the Wi-Fi Direct Client Policy. The WLANs > Edit page appears. |
| Step 3 | Click the Advanced tab. |
| Step 4 | From the Wi-Fi Direct Clients Policy drop-down list, choose one of the following options: |
| Step 5 | Click Apply. |
Configuring the Wi-Fi Direct Client Policy (CLI)
Monitoring and Troubleshooting the Wi-Fi Direct Client Policy (CLI)
Monitor and troubleshoot the Wi-Fi Direct Client Policy by entering theses commands:
Configuring Web Auth Proxy
Information About the Web Authentication Proxy
This feature enables clients that have manual web proxy enabled in the browser to facilitate authentication with the controller. If the user's browser is configured with manual proxy settings with a configured port number as 8080 or 3128 and if the client requests any URL, the controller responds with a web page prompting the user to change the Internet proxy settings to automatically detect the proxy settings so that the browser’s manual proxy settings information does not get lost. After enabling this settings, the user can get access to the network through the web authentication policy. This functionality is given for port 8080 and 3128 because these are the most commonly used ports for the web proxy server.
 Note | The web authentication proxy redirect ports are not blocked through CPU ACL. If a CPU ACL is configured to block the port 8080, 3128, and one random port as part of web authentication proxy configuration, those ports are not blocked because the webauth rules take higher precedence than the CPU ACL rules unless the client is in the webauth_req state. |
A web browser has the following three types of Internet settings that you can configure:
In a manual proxy server configuration, the browser uses the IP address of a proxy server and a port. If this configuration is enabled on the browser, the wireless client communicates with the IP address of the destination proxy server on the configured port. In a web authentication scenario, the controller does not listen to such proxy ports and the client is not able to establish a TCP connection with the controller. The user is unable to get any login page to authentication and get access to the network.
When a wireless client enters a web-authenticated WLAN, the client tries to access a URL. If a manual proxy configuration is configured on the client's browser, all the web traffic going out from the client will be destined to the proxy IP and port configured on the browser.
-
A TCP connection is established between the client and the proxy server IP address that the controller proxies for.
-
The client processes the DHCP response and obtains a JavaScript file from the controller. The script disables all proxy configurations on the client for that session. 
Note
For external clients, the controller sends the login page as is (with or without JavaScipt).
-
Any requests that bypass the proxy configuration. The controller can then perform web-redirection, login, and authentication.
-
When the client goes out of the network, and then back into its own network, a DHCP refresh occurs and the client continues to use the old proxy configuration configured on the browser.
-
If the external DHCP server is used with webauth proxy, then DHCP option 252 must be configured on the DHCP server for that scope. The value of option 252 will have the format http://<virtual ip>/proxy.js. No extra configuration is needed for internal DHCP servers.

Note
When you configure FIPS mode with secure web authentication, we recommend that you use Mozilla Firefox as your browser.
Configuring the Web Authentication Proxy (GUI)
| Step 1 | Choose Controller > General |
| Step 2 | From the WebAuth Proxy Redirection Mode drop-down list, choose Enabled or Disabled. |
| Step 3 | In the WebAuth Proxy Redirection Port text box, enter the port number of the web auth proxy. This text box consists of the port numbers on which the controller listens to for web authentication proxy redirection. By default, the three ports 80, 8080, and 3128 are assumed. If you configured the web authentication redirection port to any port other than these values, you must specify that value. |
| Step 4 | Click Apply. |
Configuring the Web Authentication Proxy (CLI)
Enable web authentication proxy redirection by entering this command: config network web-auth proxy-redirect {enable | disable}
Configure the secure web (HTTPS) authentication for clients by entering this command: config network web-auth secureweb {enable | disable}
The default secure web (HTTPS) authentication for clients is enabled. 
Note
If you configure to disallow secure web (HTTPS) authentication for clients using the config network web-auth secureweb disable command, then you must reboot the Cisco WLC to implement the change.Set the web authentication port number by entering this command: config network web-auth port port-number
This parameter specifies the port numbers on which the controller listens to for web authentication proxy redirection. By default, the three ports 80, 8080, and 3128 are assumed. If you configured the web authentication redirection port to any port other than these values, you must specify that value.
Configure secure redirection (HTTPS) for web authentication clients by entering this command: config network web-auth https-redirect {enable | disable}
See the current status of the web authentication proxy configuration by entering one of the following commands:
Detecting Active Exploits
The controller supports three active exploit alarms that serve as notifications of potential threats. They are enabled by default and therefore require no configuration on the controller.
ASLEAP detection—The controller raises a trap event if an attacker launches a LEAP crack tool. The trap message is visible in the controller’s trap log.
Fake access point detection—The controller tweaks the fake access point detection logic to avoid false access point alarms in high-density access point environments.
Honeypot access point detection—The controller raises a trap event if a rogue access point is using managed SSIDs (WLANs configured on the controller). The trap message is visible in the controller’s trap log.
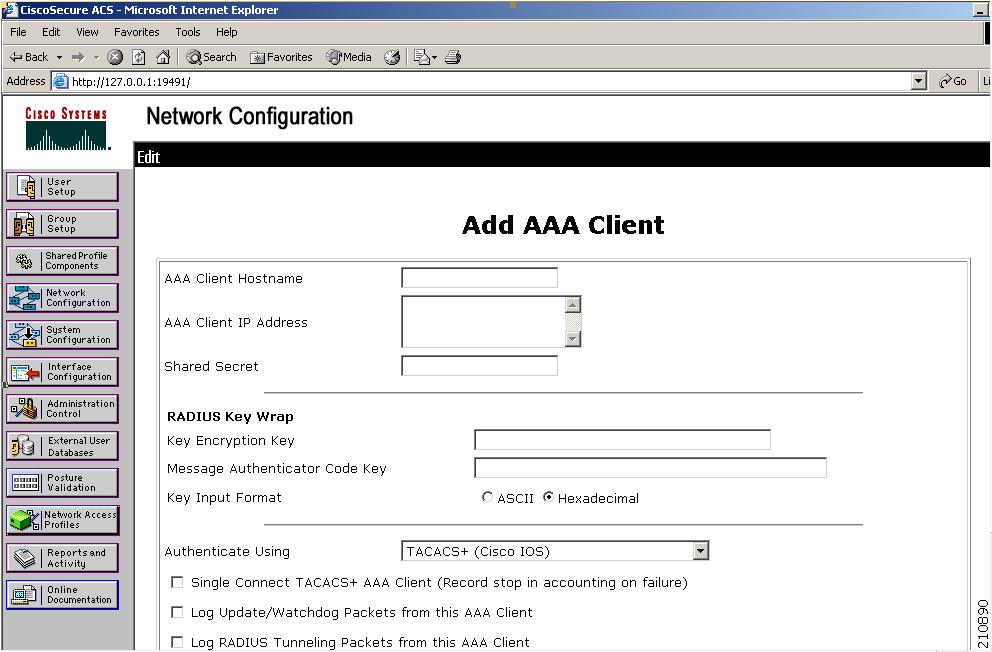
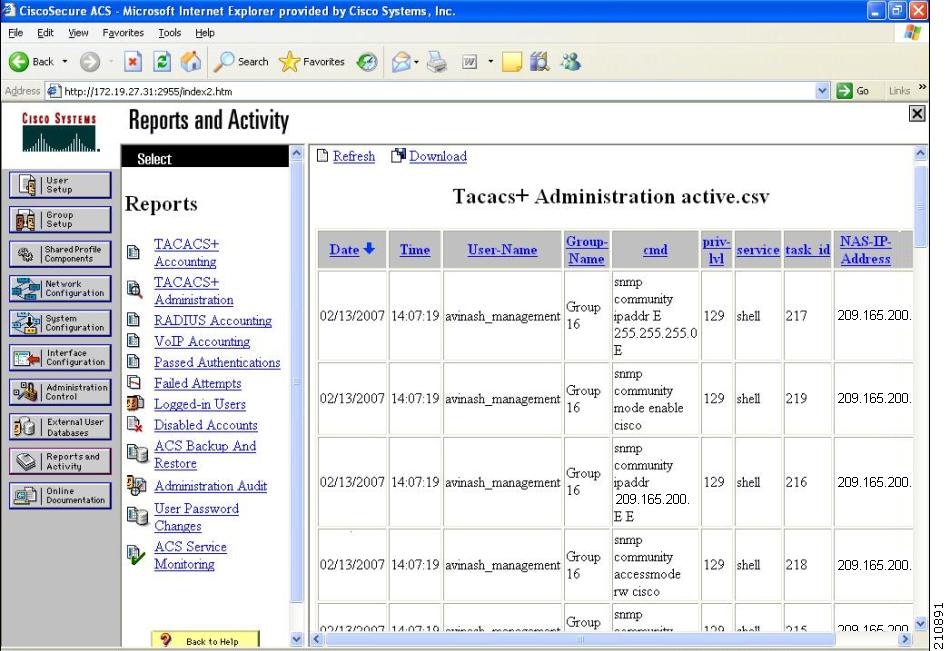
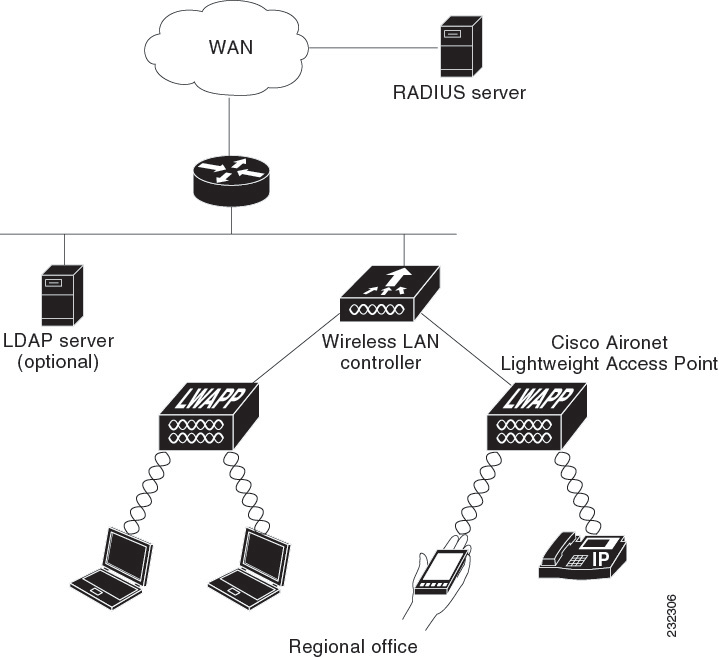
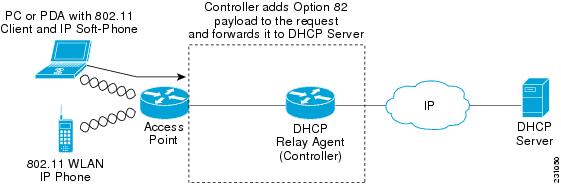
 Feedback
Feedback