Cisco Jabber Guest Server 10.5 Installation and Configuration Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- December 5, 2014
Chapter: Install and Deploy
- Install Cisco Jabber Guest Server
- Deploy Cisco Jabber Guest
- Ports and Protocols
- Configure Cisco Expressway-E and Cisco Expressway-C
- Configure Cisco Jabber Guest
- Change MTU Size
Install and Deploy
Install Cisco Jabber Guest Server
Install Server to vCenter Server
What to Do Next
To turn on the virtual machine after it has been created, in the console window select Power On.
Configure the appropriate SIP trunk in Cisco Unified Communications Manager or zones in Cisco TelePresence Video Communication Server depending on the type of server deployed in your network.
 Note | If the virtual machine cannot acquire the IP address of your VLAN, it shows a bootup failure related to network eth0. |
Install Server to ESXi, UC Virtualization Foundation, or UC Virtualization Hypervisor
What to Do Next
To turn on the virtual machine after it has been created, in the console window, select Power On.
 Note | The virtual machine is set up with DHCP by default. If you want to configure the virtual machine with a static IP address, edit the following properties: IP address, network mask, hostname, gateway IP address, and at least one DNS server IP address. |
Configure the appropriate SIP trunk in Cisco Unified Communications Manager or zones in Cisco TelePresence Video Communication Server depending on the type of server deployed in your network.
 Note | If the virtual machine cannot acquire the IP address of your VLAN, it shows a boot up failure related to network eth0. |
Sign In to Cisco Jabber Guest Administration
The Cisco Jabber Guest server is set up with default credentials.
You can access Cisco Jabber Guest Administration on Windows with:
Google Chrome 18 or later
Microsoft Internet Explorer 8 or later (32-bit, or 64-bit running 32-bit tabs only)
Mozilla Firefox 10 or later
You can access Cisco Jabber Guest Administration on Mac with:
Your session times out after 30 minutes of inactivity.
Sign In to Cisco Jabber Guest Server CLI
The Cisco Jabber Guest server command-line interface (CLI) is set up with default credentials.
Install Certificate
When you install Cisco Jabber Guest, a self-signed certificate is installed by default. If you want, you can:
-
Install a certificate that is signed by a third party (a trusted certificate authority).
-
Install a certificate with additional distinguished name information.
-
Install a certificate that includes the intermediate certificate or the entire certificate trust chain.
Cisco Jabber Guest supports installing DER encoded certificates and PEM encoded certificates.
The certificate signing request must be generated on the server on which you install the certificate. For this reason, we recommend that you obtain a new CA-signed certificate for your new install of Cisco Jabber Guest or use a self-signed certificate.
If you choose to use the certificate that is installed by default, you must generate a new self-signed certificate if the hostname of the server changes.
- Install Certificate Signed by a Certificate Authority
- Install Certificate with Additional Distinguished Name Information
- Install Certificate That Includes the Intermediate Certificate or the Entire Certificate Trust Chain
- Generate New Self-Signed Certificate
Install Certificate Signed by a Certificate Authority
The following procedure creates a certificate signing request in which the Distinguished Name (DN) information is composed of Common Name=<ip address> only. If your organization requires you to include additional DN information in your request, follow the instructions in the procedure, Install Certificate with Additional Distinguished Name Information.
If you have deployed a Cisco Jabber Guest cluster, you must install a certificate on each server in the cluster.
When you create the new certificate signing request, the current certificate becomes invalid.
Install Certificate with Additional Distinguished Name Information
If you use Cisco Jabber Guest Administration to create a certificate signing request, the Distinguished Name (DN) information in the request is composed only of Common Name=<ip address>. If your organization requires you to include additional DN information, such as organization name and locality name, use the following procedure.
If you have deployed a Cisco Jabber Guest cluster, you must install a certificate on each server in the cluster.
When you create the new certificate signing request, the current certificate becomes invalid.
Install Certificate That Includes the Intermediate Certificate or the Entire Certificate Trust Chain
You can upload a combined certificate file that includes the Cisco Jabber Guest server certificate and your intermediate certificate or that includes the Cisco Jabber Guest server certificate, your intermediate certificate, and your root certificate.
If you have deployed a Cisco Jabber Guest cluster, you must install a certificate on each server in the cluster.
When you create the new certificate signing request, the current certificate becomes invalid.
Generate New Self-Signed Certificate
If you are using the self-signed certificate that is installed by default and the hostname of the server changes, you must generate a new self-signed certificate.
When you generate a new self-signed certificate, the current certificate becomes invalid.
Change Time Zone on Server
By default, the server time zone is set to Coordinated Universal Time (UTC). To change the time zone, use the following procedure.
The time zone change takes effect immediately.
| Step 1 | Sign in to the server as root. |
| Step 2 | Check the current time zone by executing the command: date. The date and time appear in the format: ddd mmm dd hh:mm:ss UTC yyyy. For example: Fri Dec 20 16:57:18 UTC 2013. |
| Step 3 | Change directory to /opt/cisco/webcommon/scripts: cd /opt/cisco/webcommon/scripts |
| Step 4 | Execute the timezone script: ./timezone |
| Step 5 | Follow the on-screen instructions. |
| Step 6 | At the confirmation message, type 1 for Yes. |
| Step 7 | Verify that the server is set to your time zone by executing the command: date. |
| Step 8 | Restart Tomcat: service tomcat-as-standalone.sh restart |
Deploy Cisco Jabber Guest
Cisco Jabber Guest must be configured to work with the other elements in your network after the server is deployed.
- Deployment Options
- Network Topology
- Ports and Protocols
- Configure Cisco Expressway-E and Cisco Expressway-C
- Configure Cisco Jabber Guest
- Change MTU Size
Deployment Options
Cisco Expressway-E with a single NIC—SIP traffic goes to the Cisco Expressway-C and media flows over a port range between the Cisco Expressway-E and the Cisco Expressway-C.
Cisco Expressway-E with dual NIC—SIP traffic goes to the Cisco Expressway-E and media flows through the traversal zone between the Cisco Expressway-E and the Cisco Expressway-C.
Only the Cisco Expressway-E with dual NIC deployment supports NAT/PAT between the Cisco Expressway-E and the Cisco Expressway-C.
Lab Deployment
Cisco Jabber Guest can be pointed directly to Cisco Unified Communications Manager for lab deployments only; configure a SIP trunk on Cisco Unified Communications Manager for this deployment. This option is best suited to a lab deployment in which the goal is to familiarize yourself with Cisco Jabber Guest without the additional overhead of configuring Expressway. However, without configuring Expressway, Cisco Jabber Guest is not supported in a production environment.
Network Topology
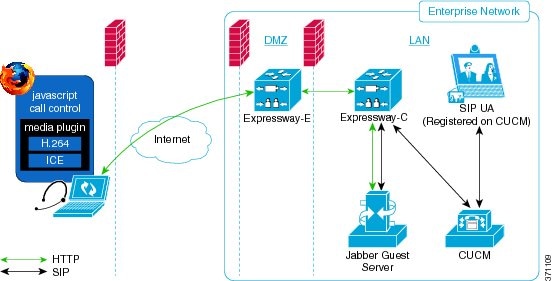
Overview of Cisco Expressway-E with Single NIC Deployment
SIP traffic is sent to the Cisco Expressway-C.
Cisco Expressway-E is single NIC only.
Cisco Expressway-E in static NAT mode is optional and requires additional configuration on the Cisco Jabber Guest server.
Cisco Expressway-E is used for TURN services and reverse proxy, not call control.
Media flows between the Cisco Expressway-E and the Cisco Expressway-C over port range, not a traversal zone.
Overview of Cisco Expressway-E with Dual NIC Deployment
SIP traffic is sent to the Cisco Expressway-E.
Cisco Expressway-E is dual NIC only.
Cisco Expressway-E in static NAT mode is optional and requires additional configuration on the Cisco Jabber Guest server.
Cisco Expressway-E is used for TURN services, reverse proxy, and call control.
Media flows between the Cisco Expressway-E and the Cisco Expressway-C through a traversal zone.
In a production environment, Cisco Jabber Guest requires that your Cisco Unified Communications Manager be configured to work with Cisco Expressway.
 Note | If Cisco Expressway-E is used for reverse proxy functionality, the Cisco Jabber Guest URL looks like https://expressway-e.example.com/call where expressway-e.example.com is the FQDN of Cisco Expressway-E. |
Call Control Flow
 Note | The mobile and web clients use the same interfaces when interacting with Cisco Expressway/Cisco VCS and Cisco Jabber Guest. To simplify the documentation, we reference only the web client throughout this guide. |
- Call Control Flow: Cisco Expressway-E with Single NIC Deployment
- Call Control Flow: Cisco Expressway-E with Dual NIC Deployment
Call Control Flow: Cisco Expressway-E with Single NIC Deployment
The following is an example of the call control flow for a Cisco Expressway-E with single NIC deployment of Cisco Jabber Guest Server.
Call Control Flow: Cisco Expressway-E with Dual NIC Deployment
The following is an example of the call control flow for a Cisco Expressway-E with dual NIC deployment of Cisco Jabber Guest Server.
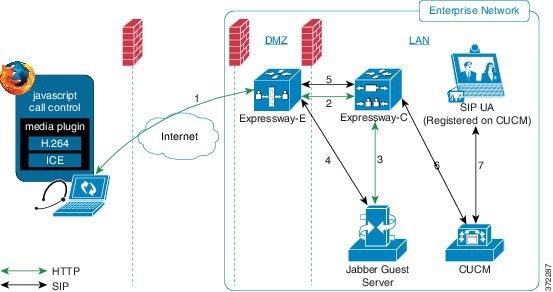
SIP flows between the Cisco Jabber Guest server and the Cisco Expressway-E. This requires bi-directional TCP traffic between the two servers over 5060 (SIP over TCP) or 5061 (SIP over TLS). The SIP traffic then goes over the traversal zone to the Cisco Expressway-C.
We recommend that you disable SIP and H.323 application-level gateways on routers/firewalls carrying network traffic to or from a Cisco Expressway-E.
Because media hairpins between the two Cisco Expressway-E NICs, the TURN traffic and SIP traffic must reside on the same Cisco Expressway-E server. You must configure the static NAT address, DMZ external address, and DMZ internal address of the Cisco Expressway-E on the Cisco Jabber Guest server.
Media Flow
The web client uses TURN relays allocated on the Cisco Expressway-E to tunnel media into the enterprise. Media is sent and received in STUN encapsulated packets to the TURN server through UDP port 3478.
The Cisco Jabber Guest client allocates a call resource through HTTP to the Cisco Jabber Guest server.
The Cisco Jabber Guest server requests short-term TURN credentials from the Cisco Expressway-C through a secure HTTP request. Administrator credentials are used for authentication. The configured domain must be on the Cisco Expressway-C with Jabber Guest service enabled.
The Cisco Expressway-C creates the TURN credential and passes it to the Cisco Jabber Guest server.
The Cisco Expressway-C propagates the TURN credential to the Cisco Expressway-E through the SSH tunnel (port 2222).
The Cisco Jabber Guest server responds to the Cisco Jabber Guest client with the TURN credential and TURN server (Cisco Expressway-E) address (DNS or IP).
The Cisco Jabber Guestclient uses the TURN credential to allocate the TURN relay on the TURN server.
- Media Flow: Cisco Expressway-E with Single NIC Deployment
- Media Flow: Cisco Expressway-E with Dual NIC Deployment
Media Flow: Cisco Expressway-E with Single NIC Deployment
The following diagram is an example of the media flow for a Cisco Expressway-E with single NIC deployment of Cisco Jabber Guest.
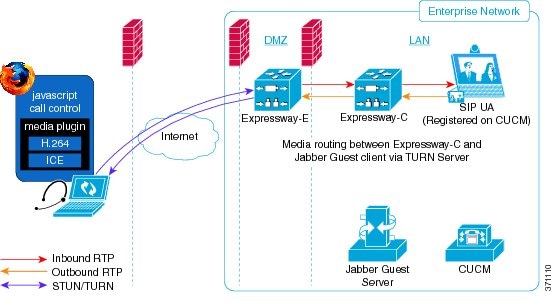
Cisco Jabber Guest media does not go through the traversal link between Cisco Expressway-E and Cisco Expressway-C.
If the Cisco Expressway-E is behind a NAT, additional configuration is required on the Cisco Jabber Guest server to avoid the media flowing to the static NAT address. Turn on Static NAT mode and configure the static NAT address and DMZ external address of the Cisco Expressway-E on the Cisco Jabber Guest server. This allows media to be sent to the DMZ external address of the Cisco Expressway-E, avoiding NAT reflection on the outside firewall.
Media Flow: Cisco Expressway-E with Dual NIC Deployment
The following diagram is an example of the media flow for a Cisco Expressway-E with dual NIC deployment of Cisco Jabber Guest.
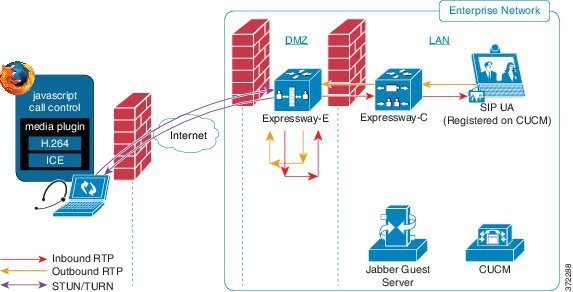
Media flows through the traversal zone between the Cisco Expressway-C and the internal NIC of the Cisco Expressway-E. It hairpins on the Cisco Expressway-E to the external NIC of the Cisco Expressway-E, and then is STUN/TURN wrapped before being sent to the client browser.
If the Cisco Expressway-E is behind a NAT, additional configuration is required on the Cisco Jabber Guest server to avoid the media flowing to the static NAT address. Turn on Static NAT mode and configure the static NAT address, DMZ external address, and DMZ internal address of the Cisco Expressway-E on the Cisco Jabber Guest server. This allows media to be sent to the DMZ external address of the Cisco Expressway-E, avoiding NAT reflection on the outside firewall.
Ports and Protocols
HTTP and HTTPS traffic from Cisco Jabber Guest clients in the Internet is sent to ports 80 and 443 TCP respectively. Therefore the firewall between the Cisco Expressway-E and the public Internet must translate destination port 80 to 9980 and destination port 443 to 9443 for all TCP traffic that targets the Cisco Expressway-E address.
The Cisco Expressway-E redirects HTTP requests on port 9980 to HTTPS on 9443.
80/443 TCP are the standard HTTP/S administration interfaces on the Expressway. If the Cisco Expressway-E is administered from systems located in the Internet, then the firewall translation must also distinguish by source address and must not translate the destination port of traffic arriving from those management systems.
You also need to ensure that appropriate DNS records exist so that the Cisco Jabber Guest client can reach the Cisco Expressway-E. The FQDN of the Cisco Expressway-E in DNS must include the Cisco Jabber Guest domain. The Cisco Jabber Guest domain is the domain that is configured on the Cisco Expressway-C.
- Ports and Protocols: Cisco Expressway-E with Single NIC Deployment
- Ports and Protocols: Cisco Expressway-E with Dual NIC Deployment
Ports and Protocols: Cisco Expressway-E with Single NIC Deployment
|
Purpose |
Protocol |
Internet Endpoint (Source) |
Cisco Expressway-E (Listening) |
|---|---|---|---|
|
HTTP |
TCP |
TCP source port |
9980 (read the following Important note) |
|
HTTPS proxy |
TLS |
TCP source port |
9443 (read the following Important note) |
|
TURN server control/media |
UDP |
UDP source port |
3478–3483 (control and media sent to this port) |
-
The Cisco Expressway-E administrator currently uses port 80 and therefore, incoming requests from the Cisco Jabber Guest client to Cisco Expressway-E on port 80 must be remapped to port 9980 using a firewall (or similar) in front of Cisco Expressway-E. For the mobile client, using 9980 in call links is not supported; you must use port remapping on your firewall to remap port 80 to port 9980.
-
The Cisco Expressway-E administrator currently uses port 443 and therefore, incoming requests from the Cisco Jabber Guest client to Cisco Expressway-E on port 443 must be remapped to port 9443 using a firewall (or similar) in front of Cisco Expressway-E. For the mobile client, using 9443 in call links is not supported; you must use port remapping on your firewall to remap port 443 to port 9443.
|
Purpose |
Protocol |
Cisco Expressway-C (Source) |
Cisco Expressway-E (Destination) |
|---|---|---|---|
|
SSH (HTTP/S tunnels) |
TCP |
Ephemeral port |
2222 (not configurable) |
|
Traversal zone SIP signaling |
TLS |
25000–29999 |
7001 |
|
Media1 |
UDP |
36000–59999 |
24000–299992 60000–617993 |
|
Purpose |
Protocol |
Cisco Expressway-E (Source) |
Cisco Expressway-C (Destination) |
|---|---|---|---|
|
Media |
UDP |
24000–299994 60000–617995 |
36000–59999 |
-
Inbound firewall rules are required to allow media to flow from the Cisco Expressway-E to Cisco Expressway-C.
-
You may find that two-way media can still be established even if the inbound from Cisco Expressway-E (DMZ) to Cisco Expressway-C (private) firewall rules are not applied. This is because the outbound media creates a pinhole in the firewall; however, these rules are required to support uni-directional media (that is, only from outside to inside).
|
Purpose |
Protocol |
Cisco Expressway-C (Source) |
Cisco Jabber Guest (Destination) |
|---|---|---|---|
|
HTTP |
TCP |
Ephemeral port |
80 |
|
HTTPS |
TLS |
Ephemeral port |
443 |
|
SIP |
TCP/TLS |
Ephemeral port |
5060 (SIP over TCP) 5061 (SIP over TLS) |
|
Purpose |
Protocol |
Cisco Jabber Guest (Source) |
Cisco Expressway-C (Destination) |
|---|---|---|---|
|
HTTPS |
TLS |
Ephemeral port |
443 |
|
SIP |
TCP/TLS |
Ephemeral port |
5060 (SIP over TCP) 5061 (SIP over TLS) |
Ports and Protocols: Cisco Expressway-E with Dual NIC Deployment
|
Purpose |
Protocol |
Internet Endpoint (Source) |
Cisco Expressway-E (Listening) |
|---|---|---|---|
|
HTTP |
TCP |
TCP source port |
9980 (read the following Important note) |
|
HTTPS proxy |
TLS |
TCP source port |
9443 (read the following Important note) |
|
TURN server control/media |
UDP |
UDP source port |
3478–3483 (control and media sent to this port) |
-
The Cisco Expressway-E administrator currently uses port 80 and therefore, incoming requests from the Cisco Jabber Guest client to Cisco Expressway-E on port 80 must be remapped to port 9980 using a firewall (or similar) in front of Cisco Expressway-E. For the mobile client, using 9980 in call links is not supported; you must use port remapping on your firewall to remap port 80 to port 9980.
-
The Cisco Expressway-E administrator currently uses port 443 and therefore, incoming requests from the Cisco Jabber Guest client to Cisco Expressway-E on port 443 must be remapped to port 9443 using a firewall (or similar) in front of Cisco Expressway-E. For the mobile client, using 9443 in call links is not supported; you must use port remapping on your firewall to remap port 443 to port 9443.
|
Purpose |
Protocol |
Cisco Expressway-C (Source) |
Cisco Expressway-E (Destination) |
||
|---|---|---|---|---|---|
|
SSH (HTTP/S tunnels) |
TCP |
Ephemeral port |
2222 (not configurable) |
||
|
Traversal zone SIP signaling |
TLS |
25000–29999 |
7001 |
||
|
Media
|
UDP |
36002–599996 36002–599997 50000–549998 |
36000–360019 36000–3601110 |
|
Purpose |
Protocol |
Cisco Jabber Guest (Source) |
Cisco Expressway-E (Destination) |
|---|---|---|---|
|
SIP |
TCP/TLS |
Ephemeral port |
5060 (SIP over TCP) 5061 (SIP over TLS) |
|
Purpose |
Protocol |
Cisco Expressway-E (Source) |
Cisco Jabber Guest (Destination) |
|---|---|---|---|
|
SIP |
TCP/TLS |
Ephemeral port |
5060 (SIP over TCP) 5061 (SIP over TLS) |
|
Purpose |
Protocol |
Cisco Expressway-C (Source) |
Cisco Jabber Guest (Destination) |
|---|---|---|---|
|
HTTP |
TCP |
Ephemeral port |
80 |
|
HTTPS |
TLS |
Ephemeral port |
443 |
|
Purpose |
Protocol |
Cisco Jabber Guest (Source) |
Cisco Expressway-C (Destination) |
|---|---|---|---|
|
HTTPS |
TLS |
Ephemeral port |
443 |
Configure Cisco Expressway-E and Cisco Expressway-C
Do one of the following:
- Configure Cisco Expressway-E and Cisco Expressway-C: Cisco Expressway-E with Single NIC Deployment
- Configure Cisco Expressway-E and Cisco Expressway-C: Cisco Expressway-E with Dual NIC Deployment
Configure Cisco Expressway-E and Cisco Expressway-C: Cisco Expressway-E with Single NIC Deployment
Follow the instructions in the Cisco Expressway documentation to set up Cisco Expressway security certificates and a Unified Communications traversal zone. Configure the traversal zone type between the Cisco Expressway-C and Cisco Expressway-E as Unified Communications traversal.
| Step 1 | On the Cisco Expressway-E, enable Cisco Jabber Guest support: |
| Step 2 | On the Cisco Expressway-E, enable TURN service: |
| Step 3 | On the Cisco Expressway-C, enable Cisco Jabber Guest support: |
| Step 4 | On the Cisco Expressway-C, configure the domain for which HTTP traffic will be routed to the Cisco Jabber Guest server: This domain is the outward-facing domain that is used to route the call on the Internet when users click a link. |
| Step 5 | Make sure that the domain has an associated DNS record that resolves to the Cisco Expressway-E. The domain information is propagated from the Cisco Expressway-C to the Cisco Expressway-E through the SSH tunnel (port 2222). It is used by the Cisco Expressway-E to validate incoming HTTP requests for the Cisco Jabber Guest service. |
| Step 6 | On the
Cisco Expressway-C,
associate the
Cisco Jabber Guest
servers with the domain:
This allows
the
Cisco Expressway-C
to route HTTP requests with this domain to the appropriate
Cisco Jabber Guest
server.
|
| Step 7 | Verify that the SSH tunnel is active: |
| Step 8 | On the
Cisco Expressway-C,
create a neighbor zone for each
Cisco Jabber Guest
server:
|
| Step 9 | Set up a connection between the Cisco Expressway-C and Cisco Unified
Communications Manager:
Follow the steps in the Cisco Unified Communications Manager with Cisco Expressway (SIP Trunk) Deployment Guide. |
| Step 10 | Create a search rule on Cisco Expressway-C to route calls to Cisco Unified Communications Manager. |
| Step 11 | Force the
protocol between the
Cisco Jabber Guest
server and the
Cisco Expressway-C
to be http:
|
HTTP request goes from the Cisco Expressway-E to the Cisco Expressway-C to the Cisco Jabber Guest server.
Configure Cisco Expressway-E and Cisco Expressway-C: Cisco Expressway-E with Dual NIC Deployment
Follow the instructions in the Cisco Expressway documentation to set up Cisco Expressway security certificates and a Unified Communications traversal zone. Configure the traversal zone type between the Cisco Expressway-C and Cisco Expressway-E as Unified Communications traversal.
| Step 1 | On the Cisco Expressway-E, enable Cisco Jabber Guest support: |
| Step 2 | On the Cisco Expressway-E, enable TURN service: |
| Step 3 | On the Cisco Expressway-C, enable Cisco Jabber Guest support: |
| Step 4 | On the Cisco Expressway-C, configure the domain for which HTTP traffic routes to the Cisco Jabber Guest server: This domain is the outward-facing domain that is used to route the call on the Internet when users click a link. |
| Step 5 | Make sure that the domain has an associated DNS record that resolves to the Cisco Expressway-E. The domain information is propagated from the Cisco Expressway-C to the Cisco Expressway-E through the SSH tunnel (port 2222). The information is used by the Cisco Expressway-E to validate incoming HTTP requests for the Cisco Jabber Guest service. |
| Step 6 | On the
Cisco Expressway-C,
associate the
Cisco Jabber Guest
servers with the domain:
This allows
the
Cisco Expressway-C
to route HTTP requests with this domain to the appropriate
Cisco Jabber Guest
server.
|
| Step 7 | Verify that the SSH tunnel is active: |
| Step 8 | On the
Cisco Expressway-E,
create a neighbor zone for each
Cisco Jabber Guest
server so that you can verify that the zone between the
Cisco Expressway-E
and the
Cisco Jabber Guest
server is active:
|
| Step 9 | Create a
search rule for the traversal zone between the
Cisco Expressway-E
and the
Cisco Expressway-C
servers.
For proper call routing, the SIP domain that you specify (click Settings, click Call Control and Media) and the domain that you optionally specify for Destination when you create a link (click Links, click New) must be configured on the Cisco Expressway-E search rule to point to the traversal zone. |
| Step 10 | Set up a connection between the Cisco Expressway-C and Cisco Unified
Communications Manager:
Follow the steps in the Cisco Unified Communications Manager with Cisco Expressway (SIP Trunk) Deployment Guide. |
| Step 11 | Create a search rule on Cisco Expressway-C to route calls to Cisco Unified Communications Manager. |
| Step 12 | Force the
protocol between the
Cisco Jabber Guest
server and the
Cisco Expressway-C
to be http:
|
HTTP request goes from the Cisco Expressway-E to the Cisco Expressway-C to the Cisco Jabber Guest server.
Configure Cisco Jabber Guest
Configure Signaling and Media
Do one of the following:
- Configure Signaling and Media: Cisco Expressway-E with Single NIC Deployment
- Configure Signaling and Media: Cisco Expressway-E with Dual NIC Deployment
Configure Signaling and Media: Cisco Expressway-E with Single NIC Deployment
We recommend enabling Session Initiation Protocol (SIP) over Transport Layer Security (TLS) for call control signaling and enabling Secure Real-Time Transfer Protocol (SRTP) for secure media. Secure media requires secure signaling.
On Cisco Expressway-C, make sure that you have created a neighbor zone for each Cisco Jabber Guest server. For more information, see Configure Cisco Expressway-E and Cisco Expressway-C: Cisco Expressway-E with Single NIC Deployment.
| Step 1 | To enable SIP
over TLS, obtain the
Cisco Expressway-C
server certificate or the
Cisco Expressway-C
certificate authority certificate:
|
| Step 2 | Upload the certificate to Cisco Jabber Guest Administration: |
| Step 3 | Configure
the
Call
Control and Media settings in
Cisco Jabber Guest
Administration:
|
| Step 4 | Click Update. The message Update successful appears. |
| Step 5 | Restart
Tomcat:
service tomcat-as-standalone.sh restart |
| Step 6 | On the Cisco Expressway-C, verify that the neighbor zones for each Cisco Jabber Guest server are active: |
Configure Signaling and Media: Cisco Expressway-E with Dual NIC Deployment
We recommend enabling Session Initiation Protocol (SIP) over Transport Layer Security (TLS) for call control signaling and enabling Secure Real-Time Transfer Protocol (SRTP) for secure media. Secure media requires secure signaling.
On Cisco Expressway-C, make sure that you have created a neighbor zone for each Cisco Jabber Guest server. For more information, see Configure Cisco Expressway-E and Cisco Expressway-C: Cisco Expressway-E with Dual NIC Deployment.
| Step 1 | To enable SIP
over TLS, obtain the
Cisco Expressway-E
server certificate or the
Cisco Expressway-E
certificate authority certificate:
|
| Step 2 | Upload the certificate to Cisco Jabber Guest Administration: |
| Step 3 | Configure the
Call
Control and Media settings in
Cisco Jabber Guest
Administration:
|
| Step 4 | Click Update. The message Update successful appears. |
| Step 5 | Restart
Tomcat:
service tomcat-as-standalone.sh restart |
| Step 6 | On the Cisco Expressway-E, verify that the neighbor zones for each Cisco Jabber Guest server are active: |
Configure Static NAT Mode on Cisco Expressway-E
| Step 1 | Sign in to Cisco Jabber Guest Administration. |
| Step 2 | Click Settings, and then click Call Control and Media. |
| Step 3 | Under Cisco Expressway-E Network Address Map, check Static NAT mode. This check box appears only when the option,Route calls using Cisco Expressway, is selected. |
| Step 4 | Under Public IP (Static NAT), enter the static NAT IP address of the Cisco Expressway-E server. |
| Step 5 | Under External IP (DMZ), enter the external IP address of the Cisco Expressway-E server. |
| Step 6 | Repeat Steps 4 and 5 for each of the Cisco Expressway-E servers in the cluster. |
| Step 7 | Click Update. |
Configure TURN Credential Provisioning
The Cisco Jabber Guest client needs TURN credentials to allocate TURN relays on the Cisco Expressway-E. The Cisco Jabber Guest server provisions these credentials on the Cisco Expressway-C when the Cisco Jabber Guest client connects.
The Cisco Jabber Guest server uses an HTTP-based XML API to communicate with Cisco Expressway-C.
| Step 1 | Sign in to Cisco Jabber Guest Administration as an administrator. |
| Step 2 | Click Settings, and then click Call Control and Media. |
| Step 3 | Under Cisco Expressway-C, for Expressway-C (IP address or DNS name), enter the Cisco Expressway-C IP address or DNS name. |
| Step 4 | Specify whether short-term TURN credentials are requested from the Cisco Expressway-C that proxied the HTTP request from the Cisco Jabber Guest client or from the server entered in Step 3. |
| Step 5 | For HTTPS port, specify the port. |
| Step 6 | For Domain, enter the domain on Cisco Expressway-C that has Jabber Guest services enabled. |
| Step 7 | For Username and Password, enter the username and password of the administrator account on Cisco Expressway-C that has read, write, and API access. |
| Step 8 | Click Update. |
Set Up TURN Server Information
The Cisco Jabber Guest client needs to know which Cisco Expressway-E to use for TURN relays.
| Step 1 | Sign in to Cisco Jabber Guest Administration as an administrator. |
| Step 2 | Click Settings, and then click Call Control and Media. |
| Step 3 | Under Cisco Expressway-E, for Expressway-E TURN server (IP address or DNS name), enter the Cisco Expressway-E TURN server outside IP address or DNS name. |
| Step 4 | For TURN port, enter the UDP port. The port is typically 3478 but you can enter a range of ports, such as 3478-3483. The range is necessary if the Cisco Expressway-E supports multiple TURN ports. The port must match the port specified on the Cisco Expressway-E (under ). |
| Step 5 | Click Update. |
Set FQDN of Cisco Jabber Guest Server
| Step 1 | Sign in to Cisco Jabber Guest Administration as an administrator. |
| Step 2 | Click Settings, and then click Call Control and Media (Local). |
| Step 3 | Enter the FQDN of the Cisco Jabber Guest server. The FQDN must match the value specified in the Cisco Jabber Guest Server hostname field on the Cisco Expressway-C. Cisco Expressway-C uses the FQDN to forward the per-session HTTP traffic to the appropriate Cisco Jabber Guest server in the cluster. |
| Step 4 | Click Update. |
What to Do Next
Make sure that you populate the Cisco Jabber Guest local FQDN field for each node in the Cisco Jabber Guest cluster.
Set Domain Used for Links
To create links on the Cisco Jabber Guest server, you must enter the domain that is configured on the Cisco Expressway.
| Step 1 | Sign in to Cisco Jabber Guest Administration as an administrator. |
| Step 2 | Click Settings, and then click Links. |
| Step 3 | For Domain used for links, enter the the public DNS name of the Cisco Expressway-E. You can add a subdomain for Cisco Jabber Guest service. Example:If yourcompany.com is configured as the domain on the Cisco Expressway and jg.yourcompany.com is configured on the Cisco Jabber Guest server, the format of the link is https://jg.yourcompany.com/call/<directory number>. |
| Step 4 | Click Update. |
Change MTU Size
In some call scenarios, such as when using VPN, the default Maximum Transmission Unit (MTU) on Cisco Expressway-E is too high and can cause packet loss. The default MTU is 1500 bytes. We recommend that you lower the MTU to 1400 bytes. If you do not, callers may experience problems, such as one-way video.
Configure Load Balancing
You can balance the load on your Cisco Expressway-C, Cisco Expressway-E, and Cisco Jabber Guest server clusters.
The following table describes the methods of load balancing that are available to distribute different types of traffic across the network.
Network Traffic |
Method of Load Balancing Available |
|
|---|---|---|
SIP for call control |
Send SIP to the Cisco Expressway-C server cluster |
|
Send SIP to the Cisco Expressway-E server cluster |
Send SIP to the Cisco Expressway-E server that provided TURN service For a clustered Cisco Expressway-E with dual NIC deployment. you must send SIP to the Cisco Expressway-E server that provided TURN service. |
|
TURN credential provisioning requests to the Cisco Expressway-C server cluster |
||
HTTPS from the Cisco Jabber Guest client to the Cisco Expressway-E server cluster |
Round-robin DNS |
|
TURN for media between the Cisco Jabber Guest client and the Cisco Expressway-E server cluster |
TURN port ranges are only supported when you use the large Cisco Expressway-E virtual machine. |
|
HTTP between the Cisco Expressway-E and Cisco Jabber Guest server clusters |
Configure Cisco Jabber Guest server priorities on the Cisco Expressway-C server. |
|
- Configure Round-Robin DNS Load Balancing
- Configure Round-Robin CSV Loading Balancing
- Configure HTTP Load Balancing
- Configure Round-Robin TURN Port Range Load Balancing
Configure Round-Robin DNS Load Balancing
With round-robin DNS load balancing, a DNS server returns an ordered list of IP addresses associated with a single host name. With each new query on that host name, the DNS server rotates through the list. Multiple servers at different IP addresses take turns handling new requests to provide the same service.
For TURN traffic, an advantage of round-robin DNS load balancing is that it also provides redundancy. If a TURN server is down or unreachable, the client tries another server.
 Note | The order of the IP address list returned for a DNS lookup is difficult to predict if the DNS server is under any kind of load directed at the host name. The important thing to expect is that calls to the host name go to different servers over time. |
| Step 1 | Make sure that the DNS server has round-robin enabled. |
| Step 2 | Make sure that the FQDNs for the Cisco Expressway-C and Cisco Expressway-E clusters are configured on the DNS server to round-robin through the IP addresses of the server cluster. |
| Step 3 | Sign in to Cisco Jabber Guest Administration as an administrator. |
| Step 4 | Click Settings, and then click Call Control and Media. |
| Step 5 | To set up round-robin DNS for the SIP server: |
| Step 6 | To set up round-robin DNS to request short-term TURN credentials from Cisco Expressway-C: |
| Step 7 | To set up round-robin DNS for the TURN server: For Expressway-E TURN server (IP address or DNS name), enter the FQDN of the Cisco Expressway-E cluster. Successive clients making TURN requests to that cluster FQDN are directed to different servers in the Cisco Expressway-E cluster; however, whether and how a particular client uses round-robin DNS for subsequent calls can be influenced by DNS caching. |
| Step 8 | Click Update. |
Round-robin DNS takes effect if the Cisco Jabber Guest call URL that is used by a client browser to make a Cisco Jabber Guest call uses the FQDN for the Cisco Expressway-E cluster.
What to Do NextTo ensure that the number of new call requests does not exceed the capacity of the Cisco Expressway-C, make sure that you change the SIP call throttle limit.
Change the SIP Call Throttle Limit
To ensure that the rate of new call requests (SIP INVITES) does not exceed the capacity of the Cisco Expressway-C, the Cisco Jabber Guest server implements a call throttling mechanism.
For a clustered Cisco Expressway-C deployment in which load balancing is achieved by round-robin DNS, we recommend that you change the SIP call throttle limit to 10 multiplied by the number of servers in the Cisco Expressway-C cluster to which Cisco Jabber Guest sends SIP. For example, if there are two servers in the Cisco Expressway-C cluster, set the SIP call throttle limit to 20.
If the rate of new calls exceeds the throttle limit, Cisco Jabber Guest delays a small amount of time before processing those calls that exceed the throttle limit. This throttling should not be noticed by users.
Configure Round-Robin CSV Loading Balancing
With round-robin CSV load balancing, a Cisco Jabber Guest server can be configured to make requests, in round-robin order, across individually specified servers by using a CSV list. After a server is used, the next server on the list is used, until the choice rotates to the beginning of the list and then repeats.
| Step 1 | Sign in to Cisco Jabber Guest Administration as an administrator. |
| Step 2 | Click Settings, and then click Call Control and Media. |
| Step 3 | To set up a CSV list for the SIP server: |
| Step 4 | To set up a CSV list to request short-term TURN credentials from Cisco Expressway-C: |
| Step 5 | To set up a CSV list for the TURN server: For Expressway-E TURN server (IP address or DNS name), enter a list of FQDNs for individual Cisco Expressway-E servers. The list of FQDNs must be separated by commas and must not contains spaces. Example:expressway-e-1.somedomain.com,expressway-e-2.somedomain.com,expressway-e-3.somedomain.com |
| Step 6 | Click Update. |
Configure HTTP Load Balancing
Cisco Jabber Guest server can take advantage of HTTP load balancing from the Cisco Expressway-C by sending SIP and TURN credential requests to the Cisco Expressway-C that sent the HTTP.
| Step 1 | Sign in to Cisco Jabber Guest Administration as an administrator. |
| Step 2 | Click Settings, and then click Call Control and Media. |
| Step 3 | To send SIP to the Cisco Expressway-C that sent the HTTP, next to Send SIP traffic to, click Expressway-C server that proxied the HTTP request from Jabber Guest client. |
| Step 4 | To send TURN credential requests to the Cisco Expressway-C that sent the HTTP, next to Request short-term TURN credentials from, click Expressway-C server that proxied the HTTP request from Jabber Guest client. |
| Step 5 | Click Update. |
Configure Round-Robin TURN Port Range Load Balancing
You can configure Cisco Jabber Guest to take advantage of the load-balancing potential for TURN requests by using different TURN ports for each successive TURN request.
On a large Cisco Expressway-E deployment, up to six TURN request ports can be specified as a range. When used in combination with round-robin DNS or round-robin CSV for TURN servers, this multiplies the number of TURN request ports in use.
| Step 1 | Sign in to Cisco Jabber Guest Administration as an administrator. |
| Step 2 | Click Settings, and then click Call Control and Media. |
| Step 3 | For TURN port, enter a hyphenated range of port numbers that matches the range of TURN request ports configured on Cisco Expressway-E (under ). Example: 3478-3483 |
| Step 4 | Click Update. |
 Feedback
Feedback