Cisco UCS Director Application Container Guide, Release 5.5
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- June 13, 2016
Chapter: Overview
Overview
This chapter contains the following sections:
- Application Containers
- Types of Application Containers
- Viewing Application Containers
- Securing a Container Using an ASA Gateway
- Securing a Container Using a Cisco Virtual Security Gateway
- Orchestration Tasks for Network Device Management
- Application Container Support for Cisco VXLANs
- ASAv Gateway
Application Containers
Application containers are a templatized approach to provision the applications for end users. Each application container is a collection of VMware virtual machines (VMs) and baremetal servers (BMs). The application container has an internal private network that is based on rules specified by the administrator. An application container can have one or more VMs and BMs, and can be secured by a fencing gateway (for example, a Virtual Secure Gateway) to the external or public cloud.
Cisco UCS Director supports the application containers and enables you to define container templates with one or more networks and VMs or BMs. When an application container is created from a template, Cisco UCS Director automatically deploys the VMs or BMs and configures the networks and any application services. Cisco UCS Director also automatically configures virtual and physical switches for Layer 2 changes.
When you want to configure Cisco UCS Directorto provision the applications, create one or more application container templates with the appropriate policies, workflows, and templates. The application container template determines how the application is provisioned for the end user. It can define some or all of the following:
-
Physical server or virtual machine
-
Amount of reserved storage
-
Maximum available CPU
-
Maximum available memory
-
Version of operating system
-
Range of VLANs
-
Gateway or firewall, if desired
-
Load balancer, if desired
-
Required approvals, if desired
-
Costs associated with the application container, if desired
Cisco UCS Director supports multiple types of application containers. The type of application container that you want to implement depends upon your deployment configuration. The steps required to configure the application container depend upon which type you plan to implement.
Types of Application Containers
There are several application container types for use in various deployment scenarios:
-
Fenced Virtual—The most common type of application container for use with VMs.
-
Virtual Secure Gateway (VSG)—This container type is used to provide for enhanced security in virtual environments.
-
Application Centric Infrastructure Controller (APIC) container—This container type is used in APIC deployments. For more information, see the Cisco UCS Director APIC Management Guide and Implementing Cisco Application Policy Infrastructure Controller Support in this guide.
-
Fabric—This container type is used in Dynamic Fabric Automation (DFA) network deployments. For more information on application containers in a DFA network, see the Cisco UCS Director Unified Fabric Automation Guide.
-
Virtual Application Container Services (VACS) container—This container type is used in deployments of Cisco Virtual Application Cloud Segmentation Services. 
Note
This container type is available in Cisco UCS Director only if the VACS modules are installed. For more information, see the Cisco Virtual Application Cloud Segmentation Services Configuration Guide.
Viewing Application Containers
To view application containers in Cisco UCS Director, do the following:
Securing a Container Using an ASA Gateway
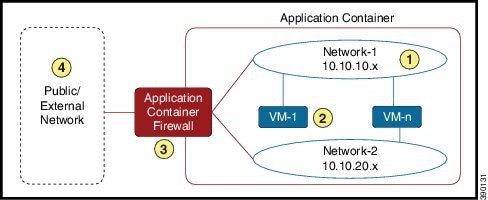
|
Region |
Description |
|
1 |
One or more internal networks using rules specified by an administrator. |
|
2 |
One or more VMs attached to one or more networks. |
|
3 |
A fencing gateway (firewall). In this example an Adaptive Security Appliance (ASA) is used. An ASA allows one-way (inside to outside) connections without an explicit configuration for each internal system and application. |
|
4 |
Public/external network. |
There are several steps required to create and manage an application container using a ASA gateway:
-
Define gateway policy—In the gateway policy, you must define the gateway type for the container and on which cloud account (vCenter) the gateway gets deployed.
-
Define an application container template—You must define the cloud account on which the container is created, as well as, performing several other tasks: 
Note
The steps are different for creation of an APIC container. See APIC Application Container Creation Process.
-
Create an application container from the defined container template—An application container is created from the template defined in step 2. You must choose a group for which the container is created.
-
Application container—After creating the application container, you can do various management actions, such as power management of the container, adding VMs to a container, cloning or deleting the container, and opening a console for VMs and viewing the reports.
Securing a Container Using a Cisco Virtual Security Gateway
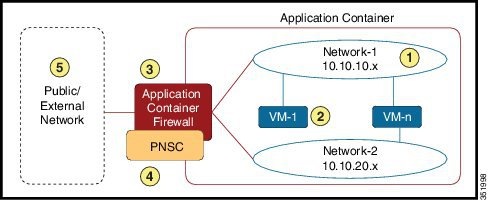
|
Region |
Description |
|
1 |
One or more internal networks using rules specified by an administrator. |
|
2 |
One or more VMs attached to one or more networks. |
|
3 |
A fencing gateway (firewall). In this example an Adaptive Security Appliance (ASA) is used. An ASA allows one-way (inside to outside) connections without an explicit configuration for each internal system and application. |
|
4 |
Cisco Prime Network Security Controller (PNSC) contributes to the deployment of an overlay network, facilitates network services insertion, and enables virtual machine mobility between private and public clouds |
|
5 |
Public/external network. |
There are several steps required to create and manage an application container secured with a Cisco VSG:
Orchestration Tasks for Network Device Management
Cisco UCS Director includes orchestration features that allow you to automate configuration and management of network domain devices in workflows.
A complete list of the network device orchestration tasks is available in the Workflow Designer and in the Task Library.
For more information about orchestration in Cisco UCS Director, see the Cisco UCS Director Orchestration Guide.
Application Container Support for Cisco VXLANs
 Note | APIC containers do not support VXLANs. |
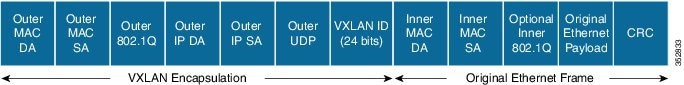
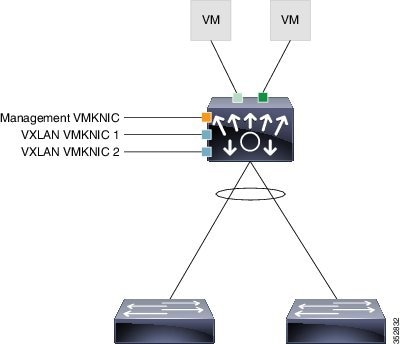
The connected VXLAN is specified within the port profile configuration of the vNIC and is applied when the VM connects. Each VXLAN uses an assigned IP multicast group to carry broadcast traffic within the VXLAN segment. When a VM attaches to a VEM, if it is the first to join the particular VXLAN segment on the VEM, an Internet Group Management Protocol (IGMP) join is issued for the VXLAN's assigned multicast group.
 Note | The VXLAN format is supported only by the Cisco Nexus 1000V Series Switch. |
ASAv Gateway
Cisco UCS Director provides the ability to create an application container that makes use of an Adaptive Security Virtual Appliance (ASAv) gateway. The Cisco ASAv supports both traditional tiered data center deployments and the fabric-based deployments of Cisco Application Centric Infrastructure (ACI) environments. The ASAv provides consistent, transparent security across physical, virtual, application-centric, SDN, and cloud environments.
The ASAv brings firewall capabilities to virtualized environments to secure data center traffic within multi-tenant architectures. Because it is optimized for data center environments, the ASAv supports vSwitches. The ASAv can therefore be deployed in Cisco, hybrid, and even non-Cisco data centers, significantly reducing administrative overhead and improving flexibility and operational efficiency.
For ACI deployments, the Cisco Application Policy Infrastructure Controller (APIC) provides a single point of control for both network and security management. APIC can provision ASAv security as a service, manage policy, and monitor the entire environment for a unified view of the entire distributed infrastructure. Many APIC functions can be controlled through UCS Director, including creation and deletion of ASAv gateways.
 Feedback
Feedback