- Preface
- Configuration Overview
- Right to Use (RTU) Licenses
- Using the Command-Line Interface
- Configuring Interfaces
- Configuring Switch Alarms
- Performing Switch Setup Configuration
- Configuring Cisco IOS Configuration Engine
- Configuring Switch Clusters
- Performing Switch Administration
- Configuring PTP
- Configuring PROFINET
- Configuring CIP
- Configuring SDM Templates
- Configuring Switch-Based Authentication
- Configuring IEEE 802.1x Port-Based Authentication
- Configuring Web-Based Authentication
- Configuring Smartports Macros
- Configuring SGT Exchange Protocol over TCP (SXP) and Layer 3 Transport
- Configuring VLANs
- Configuring VTP
- Configuring Voice VLAN
- Configuring STP
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Resilient Ethernet Protocol
- Parallel Redundancy Protocol (PRP)
- Configuring FlexLinks and the MAC Address-Table Move Update
- Configuring DHCP
- Configuring Dynamic ARP Inspection
- Configuring IP Source Guard
- Configuring IGMP Snooping and MVR
- Configuring Port-Based Traffic Control
- Configuring SPAN and RSPAN
- Configuring LLDP, LLDP-MED, and Wired Location Service
- Configuring Layer 2 NAT
- Configuring CDP
- Configuring UDLD
- Configuring RMON
- Configuring System Message Logging
- Configuring SNMP
- Configuring Network Security with ACLs
- Configuring QoS
- Configuring Static IP Unicast Routing
- Configuring IPv6 Host Functions
- Configuring Link State Tracking
- Configuring IP Multicast Routing
- Configuring MSDP
- Configuring IPv6 ACLs
- Configuring HSRP and VRRP
- Configuring IPv6 ACLs
- Configuring Embedded Event Manager
- Configuring IP Unicast Routing
- Configuring IPv6 Unicast Routing
- Unicast Overview
- Configuring Cisco IOS IP SLAs Operations
- Dying Gasp
- Configuring Enhanced Object Tracking
- Configuring MODBUS TCP
- Ethernet CFM
- Working with the Cisco IOS File System, Configuration Files, and Software Images
- Configuring EtherChannels
- Troubleshooting
- Using an SD Card
Cisco Industrial Ethernet 5000 Hardened Aggregator Software Configuration Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 8, 2015
Chapter: Configuring Cisco IOS Configuration Engine
- Prerequisites for Configuring Cisco IOS Configuration Engine
- Information About Configuring Cisco IOS Configuration Engine
Configuring Cisco IOS Configuration Engine
Prerequisites for Configuring Cisco IOS Configuration Engine
■![]() When using the Cisco Configuration Engine user interface, you must first set the DeviceID field to the hostname value that the switch acquires after, not before, you use the cns config initial global configuration command at the switch. Otherwise, subsequent cns config partial global configuration command operations malfunction.
When using the Cisco Configuration Engine user interface, you must first set the DeviceID field to the hostname value that the switch acquires after, not before, you use the cns config initial global configuration command at the switch. Otherwise, subsequent cns config partial global configuration command operations malfunction.
Enable Automated CNS Configuration
■![]() To enable automated CNS configuration of the switch, you must first complete the prerequisites in Table 1. When you complete them, power on the switch. At the setup prompt, you do not need to enter a command. The switch begins the initial configuration as described in the Initial Configuration. When the full configuration file is loaded on your switch, you do not need to do anything else.
To enable automated CNS configuration of the switch, you must first complete the prerequisites in Table 1. When you complete them, power on the switch. At the setup prompt, you do not need to enter a command. The switch begins the initial configuration as described in the Initial Configuration. When the full configuration file is loaded on your switch, you do not need to do anything else.
Information About Configuring Cisco IOS Configuration Engine
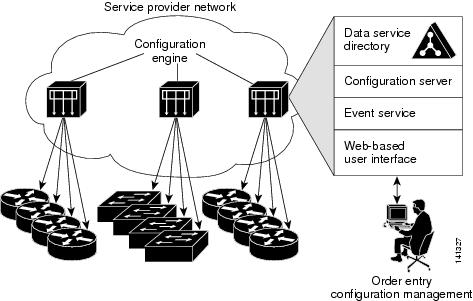
Cisco Configuration Engine is network management software that acts as a configuration service for automating the deployment and management of network devices and services (see Figure 5). Each Cisco Configuration Engine service manages a group of Cisco devices (switches and routers) and the services that they deliver, storing their configurations and delivering them as needed. Cisco Configuration Engine automates initial configurations and configuration updates by generating device-specific configuration changes, sending them to the device, executing the configuration change, and logging the results.
Cisco Configuration Engine supports standalone and server modes and has these CNS components:
■![]() Configuration service (web server, file manager, and namespace mapping server)
Configuration service (web server, file manager, and namespace mapping server)
■![]() Event service (event gateway)
Event service (event gateway)
■![]() Data service directory (data models and schema)
Data service directory (data models and schema)
In standalone mode, Cisco Configuration Engine supports an embedded directory service. In this mode, no external directory or other data store is required. In server mode, Cisco Configuration Engine supports a user-defined external directory.
Figure 5 Configuration Engine Architectural Overview
Configuration Service
Configuration Service is the core component of Cisco Configuration Engine. It consists of a configuration server that works with Cisco IOS CNS agents on the switch. Configuration Service delivers device and service configurations to the switch for initial configuration and mass reconfiguration by logical groups. Switches receive their initial configuration from the Configuration Service when they start up on the network for the first time.
Configuration Service uses CNS Event Service to send and receive configuration change events and to send success and failure notifications.
The configuration server is a web server that uses configuration templates and the device-specific configuration information stored in the embedded (standalone mode) or remote (server mode) directory.
Configuration templates are text files containing static configuration information in the form of CLI commands. In the templates, variables are specified using Lightweight Directory Access Protocol (LDAP) URLs that reference the device-specific configuration information stored in a directory.
The Cisco IOS agent can perform a syntax check on received configuration files and publish events to show the success or failure of the syntax check. The configuration agent can either apply configurations immediately or delay the application until receipt of a synchronization event from the configuration server.
Event Service
Cisco Configuration Engine uses Event Service for receipt and generation of configuration events. The event agent is on the switch and facilitates the communication between the switch and the event gateway on Configuration Engine.
Event Service is a highly capable publish-and-subscribe communication method. Event Service uses subject-based addressing to send messages to their destinations. Subject-based addressing conventions define a simple, uniform namespace for messages and their destinations.
NameSpace Mapper
Configuration Engine includes NameSpace Mapper (NSM), which provides a lookup service for managing logical groups of devices based on application, device or group ID, and event.
Cisco IOS devices recognize only event subject names that match those configured in Cisco IOS software; for example, cisco.cns.config.load. You can use the namespace mapping service to designate events by using any desired naming convention. When you have populated your data store with your subject names, NSM changes your event subject-name strings to those known by Cisco IOS.
For a subscriber, when given a unique device ID and event, the namespace mapping service returns a set of events to which to subscribe. Similarly, for a publisher, when given a unique group ID, device ID, and event, the mapping service returns a set of events on which to publish.
CNS IDs and Device Hostnames
Configuration Engine assumes that a unique identifier is associated with each configured switch. This unique identifier can take on multiple synonyms, where each synonym is unique within a particular namespace. The event service uses namespace content for subject-based addressing of messages.
Configuration Engine intersects two namespaces, one for the event bus and the other for the configuration server. Within the scope of the configuration server namespace, the term ConfigID is the unique identifier for a device. Within the scope of the event bus namespace, the term DeviceID is the CNS unique identifier for a device.
Because Configuration Engine uses both the event bus and the configuration server to provide configurations to devices, you must define both ConfigID and Device ID for each configured switch.
Within the scope of a single instance of the configuration server, no two configured switches can share the same value for ConfigID. Within the scope of a single instance of the event bus, no two configured switches can share the same value for DeviceID.
ConfigID
Each configured switch has a unique ConfigID, which serves as the key into the Configuration Engine directory for the corresponding set of switch CLI attributes. The ConfigID defined on the switch must match the ConfigID for the corresponding switch definition on Configuration Engine.
The ConfigID is fixed at startup time and cannot be changed until the device restarts, even if the switch hostname is reconfigured.
DeviceID
Each configured switch participating on the event bus has a unique DeviceID, which is analogous to the switch source address so that the switch can be targeted as a specific destination on the bus. All switches configured with the cns config partial global configuration command must access the event bus. Therefore, the DeviceID, as originated on the switch, must match the DeviceID of the corresponding switch definition in Configuration Engine.
The origin of the DeviceID is defined by the Cisco IOS hostname of the switch. However, the DeviceID variable and its usage reside within the event gateway adjacent to the switch.
The logical Cisco IOS termination point on the event bus is embedded in the event gateway, which in turn functions as a proxy on behalf of the switch. The event gateway represents the switch and its corresponding DeviceID to the event bus.
The switch declares its hostname to the event gateway immediately after the successful connection to the event gateway. The event gateway couples the DeviceID value to the Cisco IOS hostname each time this connection is established. The event gateway caches this DeviceID value for the duration of its connection to the switch.
Hostname and DeviceID Interaction
The DeviceID is fixed at the time of the connection to the event gateway and does not change even when the switch hostname is reconfigured.
When changing the switch hostname on the switch, the only way to refresh the DeviceID is to break the connection between the switch and the event gateway. Enter the no cns event global configuration command followed by the cns event global configuration command.
When the connection is reestablished, the switch sends its modified hostname to the event gateway. The event gateway redefines the DeviceID to the new value.
Using Hostname, DeviceID, and ConfigID
In standalone mode, when a hostname value is set for a switch, the configuration server uses the hostname as the DeviceID when an event is sent on hostname. If the hostname has not been set, the event is sent on the cn=< value > of the device.
In server mode, the hostname is not used. In this mode, the unique DeviceID attribute is always used for sending an event on the bus. If this attribute is not set, you cannot update the switch.
These and other associated attributes (tag value pairs) are set when you run Setup on Configuration Engine.
Cisco IOS Agents
The CNS event agent feature allows the switch to publish and subscribe to events on the event bus and works with the Cisco IOS agent.
Initial Configuration
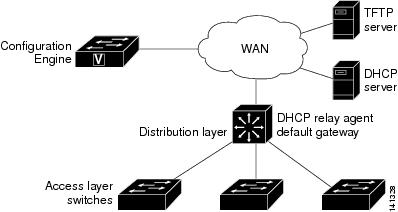
When the switch first comes up, it attempts to get an IP address by broadcasting a DHCP request on the network. Assuming there is no DHCP server on the subnet, the distribution switch acts as a DHCP relay agent and forwards the request to the DHCP server. Upon receiving the request, the DHCP server assigns an IP address to the new switch and includes the TFTP server IP address, the path to the bootstrap configuration file, and the default gateway IP address in a unicast reply to the DHCP relay agent. The DHCP relay agent forwards the reply to the switch.
The switch automatically configures the assigned IP address on interface VLAN 1 (the default) and downloads the bootstrap configuration file from the TFTP server. Upon successful download of the bootstrap configuration file, the switch loads the file in its running configuration.
The Cisco IOS agents initiate communication with Configuration Engine by using the appropriate ConfigID and EventID. Configuration Engine maps the ConfigID to a template and downloads the full configuration file to the switch.
Figure 6 shows a sample network configuration for retrieving the initial bootstrap configuration file by using DHCP-based autoconfiguration.
Figure 6 Initial Configuration Overview
Incremental (Partial) Configuration
After the network is running, new services can be added by using the Cisco IOS agent. Incremental (partial) configurations can be sent to the switch. The actual configuration can be sent as an event payload by way of the event gateway (push operation) or as a signal event that triggers the switch to initiate a pull operation.
The switch can check the syntax of the configuration before applying it. If the syntax is correct, the switch applies the incremental configuration and publishes an event that signals success to the configuration server. If the switch does not apply the incremental configuration, it publishes an event showing an error status. When the switch has applied the incremental configuration, it can write it to NVRAM or wait until signaled to do so.
Synchronized Configuration
When the switch receives a configuration, it can defer application of the configuration upon receipt of a write-signal event. The write-signal event tells the switch not to save the updated configuration into its NVRAM. The switch uses the updated configuration as its running configuration. This ensures that the switch configuration is synchronized with other network activities before saving the configuration in NVRAM for use at the next reboot.
How to Configure Cisco IOS Configuration Engine
Configuring Cisco IOS Agents
CNS Event Agent and Cisco IOS CNS Agent embedded in the Cisco IOS software on the switch allows the switch to be connected and automatically configured. Both agents must be enabled and the CNS configuration can be initial or partial. The partial configuration allows you to use Configuration Engine to remotely send incremental configuration to the switch.
Enabling CNS Event Agent
You must enable CNS Event Agent on the switch before you enable Cisco IOS CNS Agent.
Enabling Cisco IOS CNS Agent and an Initial Configuration
Enabling a Partial Configuration
Monitoring and Maintaining Cisco IOS Configuration Engine
Configuration Examples for Cisco IOS Configuration Engine
Enabling the CNS Event Agent: Example
This example shows how to enable the CNS event agent, set the IP address gateway to 10.180.1.27, set 120 seconds as the keepalive interval, and set 10 as the retry count.
Configuring an Initial CNS Configuration: Examples
This example shows how to configure an initial configuration on a remote switch when the switch configuration is unknown (the CNS Zero Touch feature).
This example shows how to configure an initial configuration on a remote switch when the switch IP address is known. The Configuration Engine IP address is 172.28.129.22.
Additional References
The following sections provide references related to switch administration:
Related Documents
|
|
|
|---|---|
Standards
|
|
|
|---|---|
No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature. |
MIBs
|
|
|
|---|---|
To locate and download MIBs using Cisco IOS XR software, use the Cisco MIB Locator found at the following URL and choose a platform under the Cisco Access Products menu: http://cisco.com/public/sw-center/netmgmt/cmtk/mibs.shtml |
RFCs
|
|
|
|---|---|
No new or modified RFCs are supported by this feature, and support for existing RFCs has not been modified by this feature. |
 Feedback
Feedback