Information About SPAN and ERSPAN
The Switched Port Analyzer (SPAN) feature (sometimes called port mirroring or port monitoring) allows network traffic to be analyzed by a network analyzer such as a Cisco SwitchProbe or other Remote Monitoring (RMON) probes.
SPAN allows you to monitor traffic on one or more ports, or one or more VLANs, and send the monitored traffic to one or more destination ports where the network analyzer is attached.
SPAN Sources
The interfaces from which traffic can be monitored are called SPAN sources. These sources include Ethernet, virtual Ethernet, port-channel, port profile, and VLAN. When a VLAN is specified as a SPAN source, all supported interfaces in the VLAN are SPAN sources. When a port profile is specified as a SPAN source, all ports that inherit the port profile are SPAN sources. Traffic can be monitored in the receive direction, the transmit direction, or both directions for Ethernet and virtual Ethernet source interfaces as described by the following:
-
Receive source (Rx)—Traffic that enters the switch through this source port is copied to the SPAN destination port.
-
Transmit source (Tx)—Traffic that exits the switch through this source port is copied to the SPAN destination port
Characteristics of SPAN Sources
A local SPAN source has these characteristics:
-
Can be port type Ethernet, virtual Ethernet, port profile, or VLAN.
-
Cannot be a destination port or port profile
-
Can be configured to monitor the direction of traffic — receive, transmit, or both.
-
Can be in the same or different VLANs.
-
For VLAN SPAN sources, all active ports in the source VLAN are included as source ports.
-
Must be on the same host Virtual Service Engine (VSE) as the destination port.
-
For port profile sources, all active interfaces attached to the port profile are included as source ports.
SPAN Destinations
SPAN destinations refer to the interfaces that monitor source ports.
Characteristics of Local SPAN Destinations
Each local SPAN session must have at least one destination port (also called a monitoring port) that receives a copy of traffic from the source ports or VLANs. A destination port has these characteristics:
-
Can be any physical, virtual Ethernet port, or a port profile.
-
Cannot be a source port or port profile.
-
Is excluded from the source list and is not monitored if it belongs to a source VLAN of any SPAN session or a source port profile.
-
Receives copies of transmitted and received traffic for all monitored source ports in the same VSE. If a destination port is oversubscribed, it can become congested. This congestion can affect traffic forwarding on one or more of the source ports.
-
Must not be private VLAN mode.
-
Can only monitor sources on the same host (VSE)
-
In access mode, can receive monitored traffic on all the VLANs.
-
In trunk mode, can receive monitored traffic only on the allowed VLANs in the trunk configuration.
Characteristics of ERSPAN Destinations
-
An ERSPAN destination is specified by an IP address.
-
In ERSPAN, the source SPAN interface and destination SPAN interface may be on different devices interconnected by an IP network. ERSPAN traffic is Generic Routing Encapsulation (GRE-encapsulated).
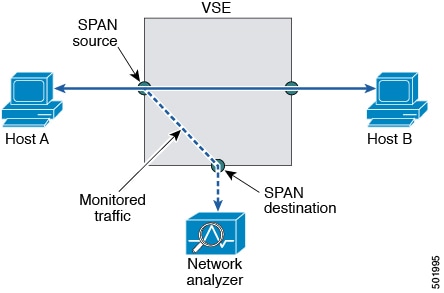
Local SPAN
In Local SPAN, the source interface and destination interface are on the same VSE. The network analyzer is attached directly to the SPAN destination port. The SPAN source can be a port, a VLAN interface, or a port profile.The destination can be a port or port profile.
The diagram shows that traffic transmitted by host A is received on the SPAN source interface. Traffic (ACLs, QoS, and so forth) is processed as usual. Traffic is then replicated. The original packet is forwarded on toward host B. The replicated packet is then sent to the destination SPAN interface where the monitor is attached.
Local SPAN can replicate to one or more destination ports. Traffic can be filtered so that only traffic of interest is sent out the destination SPAN interface.
Local SPAN can monitor all traffic received on the source interface including Bridge Protocol Data Unit (BPDU).
Encapsulated Remote SPAN
Encapsulated remote SPAN (ERSPAN) monitors traffic in multiple network devices across an IP network and sends that traffic in an encapsulated envelope to destination analyzers. In contrast, Local SPAN cannot forward traffic through the IP network. ERSPAN can be used to monitor traffic remotely. ERSPAN sources can be ports, VLANs, or port profiles.
In the following figure, the ingress and egress traffic for Host A are monitored using ERSPAN. Encapsulated ERSPAN packets are routed from Host A through the routed network to the destination device where they are decapsulated and forwarded to the attached network analyzer. The destination may also be on the same Layer 2 network as the source.
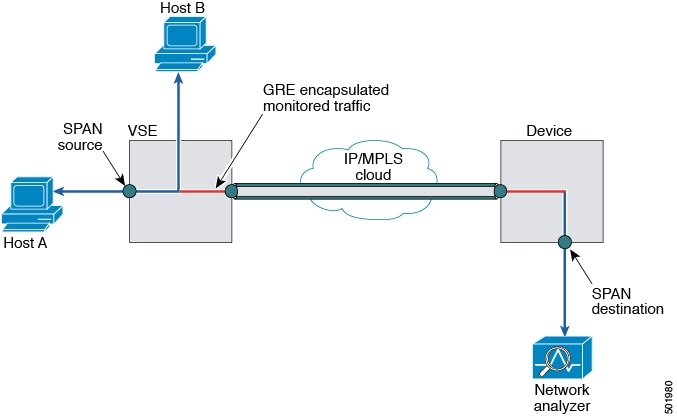
Network Analysis Module
You can also use the Cisco Network Analysis Module (NAM) to monitor ERSPAN data sources for application performance, traffic analysis, and packet header analysis.
SPAN Sessions
You can create up to 64 total SPAN sessions (Local SPAN plus ERSPAN) on the VSE.
You must configure an ERSPAN session ID that is added to the ERSPAN header of the encapsulated frame to differentiate between ERSPAN streams of traffic at the termination box. You can also configure the range of flow ID numbers.
When trunk ports are configured as SPAN sources and destinations, you can filter VLANs to send to the destination ports from among those allowed. Both sources and destinations must be configured to allow the VLANs.
The following figure shows one example of a VLAN-based SPAN configuration in which traffic is copied from three VLANs to three specified destination ports. You can choose which VLANs to allow on each destination port to limit the traffic transmitted. In the figure, the device transmits packets from one VLAN at each destination port. The destinations in this example are trunks on which allowed VLANs are configured.
 Note |
VLAN-based SPAN sessions cause all source packets to be copied to all destinations, whether the packets are required at the destination or not. VLAN traffic filtering occurs at transmit destination ports. |

This image extra/186284.jpg is not available in preview/cisco.com

 Feedback
Feedback