- Title
- New and Changed Information
- Preface
- Overview
- Configuring FIPS
- Configuring Users and Common Roles
- Configuring Security Features on an External AAA Server
- Configuring IPv4 and IPv6 Access Control Lists
- Configuring Certificate Authorities and Digital Certificates
- Configuring IPSec Network Security
- Configuring FC-SP and DHCHAP
- Configuring Port Security
- Configuring Fibre Channel Common Transport Management Security
- Configuring Fabric Binding
- Configuring Cisco TrustSec Fibre Channel Link Encryption
Cisco MDS 9000 Family NX-OS Security Configuration Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- May 16, 2011
Chapter: Configuring FIPS
Configuring FIPS
The Federal Information Processing Standards (FIPS) Publication 140-2, Security Requirements for Cryptographic Modules, details the U.S. government requirements for cryptographic modules. FIPS 140-2 specifies that a cryptographic module should be a set of hardware, software, firmware, or some combination that implements cryptographic functions or processes, including cryptographic algorithms and, optionally, key generation, and is contained within a defined cryptographic boundary.
FIPS specifies certain crypto algorithms as secure, and it also identifies which algorithms should be used if a cryptographic module is to be called FIPS compliant.

Note![]() On Cisco MDS NX-OS Release 7.x and earlier, FIPS feature is supported, but it is not FIPS compliant (certification process is with the U.S. government). For current FIPS compliance, refer to the Table 1 Current FIPS Compliance Reviews section in the Cisco FIPS 140 document.
On Cisco MDS NX-OS Release 7.x and earlier, FIPS feature is supported, but it is not FIPS compliant (certification process is with the U.S. government). For current FIPS compliance, refer to the Table 1 Current FIPS Compliance Reviews section in the Cisco FIPS 140 document.

Note![]() On Cisco MDS NX-OS Release 6.2(19) and earlier, SSH keys must be 2048 bits when FIPS mode is enabled.
On Cisco MDS NX-OS Release 6.2(19) and earlier, SSH keys must be 2048 bits when FIPS mode is enabled.
Configuration Guidelines
Follow these guidelines before enabling FIPS mode:
- Make your passwords a minimum of eight characters in length.
- Disable Telnet. Users should log in using SSH only.
- Disable remote authentication through RADIUS/TACACS+. Only users local to the switch can be authenticated.
- Disable SNMP v1 and v2. Any existing user accounts on the switch that have been configured for SNMPv3 should be configured only with SHA for authentication and AES/3DES for privacy.
- Disable VRRP.
- Do not configure FIPS and IPsec together on a switch. With FIPS enabled, if you configure IKE, then FCIP links will not come up.
- Delete all SSH Server RSA1 keypairs.
Enabling FIPS Mode
To enable FIPS mode, follow these steps:
|
|
|
|
|---|---|---|
To enable FIPS mode using Fabric Manager, follow these steps:
Step 1![]() Expand Switches from the Physical Attributes pane. Expand Security and then select FIPS.
Expand Switches from the Physical Attributes pane. Expand Security and then select FIPS.
You see the FIPS activation details in the Information pane as shown in Figure 5-1.
Figure 5-1 FIPS Activation in Fabric Manager
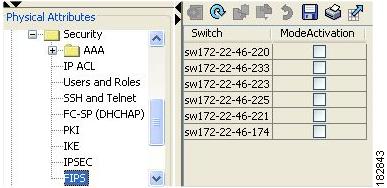
Step 2![]() Check the ModeActivation check box next to the switch for which you want to enable FIPS mode.
Check the ModeActivation check box next to the switch for which you want to enable FIPS mode.
Step 3![]() Click Apply Changes to commit and distribute these changes.
Click Apply Changes to commit and distribute these changes.
Step 4![]() Click Undo Changes to discard any unsaved changes.
Click Undo Changes to discard any unsaved changes.
To enable FIPS mode using Device Manager, follow these steps:
Step 1![]() Choose Physical > System or right-click and select Configure.
Choose Physical > System or right-click and select Configure.
You see the System dialog box as shown in Figure 5-2.
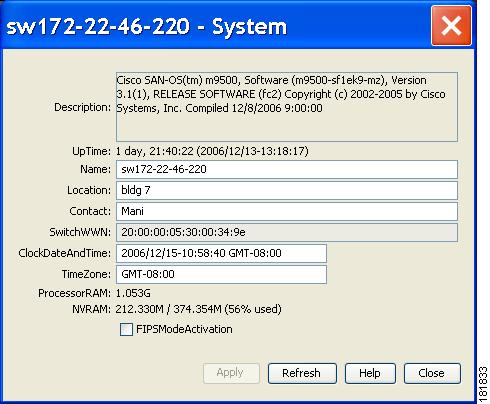
Step 2![]() Check the FIPSModeActivation check box to enable FIPS mode on the selected switch.
Check the FIPSModeActivation check box to enable FIPS mode on the selected switch.
Step 3![]() Click Apply to save the changes.
Click Apply to save the changes.
Step 4![]() Click Close to close the dialog box.
Click Close to close the dialog box.
Displaying FIPS Status
FIPS Self-Tests
A cryptographic module must perform power-up self-tests and conditional self-tests to ensure that it is functional.

Note![]() FIPS power-up self-tests automatically run when FIPS mode is enabled by entering the fips mode enable command. A switch is in FIPS mode only after all self-tests are successfully completed. If any of the self-tests fail, then the switch is rebooted.
FIPS power-up self-tests automatically run when FIPS mode is enabled by entering the fips mode enable command. A switch is in FIPS mode only after all self-tests are successfully completed. If any of the self-tests fail, then the switch is rebooted.
Power-up self-tests run immediately after FIPS mode is enabled. A cryptographic algorithm test using a known answer must be run for all cryptographic functions for each FIPS 140-2-approved cryptographic algorithm implemented on the Cisco MDS 9000 Family.
Using a known-answer test (KAT), a cryptographic algorithm is run on data for which the correct output is already known, and then the calculated output is compared to the previously generated output. If the calculated output does not equal the known answer, the known-answer test fails.
Conditional self-tests must be run when an applicable security function or operation is invoked. Unlike the power-up self-tests, conditional self-tests are executed each time their associated function is accessed.
Conditional self-tests include the following:
- Pair-wise consistency test—This test is run when a public-private keypair is generated.
- Continuous random number generator test—This test is run when a random number is generated.
Both of these tests automatically run when a switch is in FIPS mode.
 Feedback
Feedback