| Step 1 |
Locate the IP address for your Cloud APIC.
|
| Step 2 |
Open a browser window and, using the secure version of HTTP (https://), paste the IP address into the URL field, then press Return to access this Cloud APIC.
For example, https://192.168.0.0.
If you see a message asking you to Ignore Risk and Accept Certificate, accept the certificate to continue.
|
| Step 3 |
Enter the following information in the login page for the Cloud APIC:
-
Username: Enter admin for this field.
-
Password: Enter the password that you provided to log into the Cloud APIC.
-
Domain: If you see the Domain field, leave the default Domain entry as-is.
|
| Step 4 |
Click Login at the bottom of the page.
| Note
|
If you see an error message when you try to log in, such as REST Endpoint user authentication datastore is not initialized - Check Fabric Membership Status of this fabric node, wait for several minutes, then try again after a few minutes. You might also have to refresh the page in order to log in.
|
The Welcome to Cloud APIC setup wizard page appears.
|
| Step 5 |
Click Begin Set Up.
The Let's Configure the Basics page appears, with these areas to be configured:
-
DNS and NTP Servers
-
Region Management
-
Smart Licensing
|
| Step 6 |
In the DNS and NTP Servers row, click Edit Configuration.
The DNS and NTP page appears.
|
| Step 7 |
In the DNS and NTP page, add the DNS, if necessary, and NTP servers.
-
A DNS server is already configured by default. Add a DNS server if you want to use a specific DNS server.
-
An NTP server is not configured by default, however, so we recommend that you configure an NTP server. Skip to 7.d if you want to configure an NTP server and you do not want to configure a DNS server.
-
If you want to use a specific DNS server, under the DNS Servers area, click +Add DNS Provider.
-
Enter the IP address for the DNS servers and, if necessary, check the box next to Preferred DNS Provider.
-
Click the check mark next to the DNS server, and repeat for any additional DNS servers that you want to add.
-
Under the NTP Servers area, click +Add Providers.
-
Enter the IP address for the NTP servers and, if necessary, check the box next to Preferred NTP Provider.
-
Click the check mark next to the NTP server, and repeat for any additional NTP servers that you want to add.
|
| Step 8 |
When you have finished adding the DNS and NTP servers, click Save and Continue.
The Let's Configure the Basics page appears again.
|
| Step 9 |
In the Region Management row, click Begin.
The Region Management page appears.
|
| Step 10 |
Verify that the Cloud APIC home region is selected.
The region that you selected when you were configuring your cloud site is the home region and should be selected already in
this page. This is the region where the Cloud APIC is deployed (the region that will be managed by Cloud APIC), and will be indicated with the text cAPIC deployed in the Region column.
|
| Step 11 |
Determine the type of connectivity that you want for the internal network and
make the appropriate selection in the Connectivity for Internal
Network area.
-
To enable Azure VNet peering, click Virtual Network
Peering.
This enables VNet peering at the Cloud APIC level, deploying NLBs in
all the regions with a CSR. For more information on the VNet peering
feature, see the Configuring VNet Peering for Cloud APIC for
Azure document in the Cisco Cloud APIC documentation page.
-
To enable the traditional VPN connectivity through the CSRs instead
of through VNet peering, click VPN Connectivity via
CSR.
|
| Step 12 |
If you want connectivity to the on-premises site or another cloud site—in
addition to connectivity within a region—check the Inter-Site
Connectivity check box.
|
| Step 13 |
Select additional regions if you want the Cloud APIC to manage additional regions, and to possibly deploy CSRs to have inter-VNET communication and Hybrid-Cloud, Hybrid Multi-Cloud,
or Multi-Cloud connectivity on those other regions.
The CSR can manage up to four regions, including the home region where Cloud APIC is deployed.
A Cloud APIC can manage multiple cloud regions as a single site. In a typical Cisco ACI configuration, a site represents anything that can be managed by an APIC cluster. If a Cloud APIC manages two regions, those two regions are considered a single site by Cisco ACI.
The following options are available on the row for any region that you select:
-
Cloud Routers: Select this option if you want to deploy CSRs in this region. You must have at least one region with CSRs deployed to have
inter-VNET or inter-VPC communications. However, if you choose multiple regions in this page, you do not have to have CSRs
in every region that you choose. See Understanding Limitations for Number of Sites, Regions and CSRs for more information.
-
Inter-Site Connectivity: Select this option if you want this region to connect to other sites (for example, if you want this region to connect to
an on-premises site, or to connect cloud site-to-cloud site, through Cisco ACI Multi-Site). Infra VNETs or VPCs are deployed
on all regions selected for inter-site connectivity. Note that when you select inter-site connectivity for a region, the cloud
routers option is also selected automatically for this region because you must have two cloud routers deployed for inter-site
connectivity hubs.
|
| Step 14 |
When you have selected all the appropriate regions, click Next at the bottom of the page.
The General Connectivity page appears.
|
| Step 15 |
Enter the following information on the General Connectivity page.
-
In the Fabric Autonomous System Number field, enter the BGP autonomous system number (ASN) that is unique to this site.
Note the following Microsoft Azure ASN restrictions:
-
Do not use 64518 as the autonomous system number in this
field.
-
Do not use 32-bit ASNs. Azure VPN Gateways support 16-Bit ASNs at this time.
-
The following ASNs are reserved by Azure for both internal and external peerings:
-
Public ASNs: 8074, 8075, 12076
-
Private ASNs: 65515, 65517, 65518, 65519, 65520
You cannot specify these ASNs for your on-premises VPN devices when connecting to Azure VPN gateways.
-
The following ASNs are reserved by IANA and cannot be configured on your Azure VPN Gateway: 23456, 64496-64511, 65535-65551 and 429496729
-
In the Subnet for Cloud Router field, enter the subnet for the cloud router.
The first subnet pool for the first two regions is automatically populated. If you selected more than two regions, you will
need to add a subnet for the cloud router to the list for the additional two regions. Addresses from this subnet pool will
be used for inter-region connectivity for any additional regions that are added that need to be managed by the Cloud APIC
after the first two regions. This must be a valid IPv4 subnet with mask /24.
-
Under the Cloud Router Template area, in the Number of Routers Per Region field, choose the number of Cisco Cloud Services Routers (CSRs) that will be used in each region.
-
In the Username, enter the username for the Cisco Cloud Services Router.
| Note
|
Do not use admin as a username for the Cisco Cloud Services Router when connecting to an Azure cloud site.
|
-
In the Password field, enter the password for the Cisco Cloud Services Router.
-
In the Throughput of the routers field, choose the throughput of the Cisco Cloud Services Router.
Changing the value in this field changes the size of the CSR instance that is deployed. Choosing a higher value for the throughput
results in a larger VM being deployed.
| Note
|
If you wish to change this value at some point in the future, you must delete the CSR, then repeat the processes in this chapter
again and select the new value that you would like in the same Throughput of the routers field.
|
In addition, the licensing of the CSR is based on this setting. You will need the equivalent or higher license in your Smart
account for it to be compliant. See Requirements for the Azure Public Cloud for more information.
| Note
|
Cloud routers should be undeployed from all regions before changing the router throughput or login credentials.
|
-
In the License Token field, enter the license token for the Cisco Cloud Services Router.
This is the Product Instance Registration token from your Cisco Smart Software Licensing account. To get this license token,
go to http://software.cisco.com, then navigate to to find the Product Instance Registration token.
|
| Step 16 |
Click the appropriate button, depending on whether you are configuring inter-site connectivity or not.
-
If you are not configuring inter-site connectivity (if you did not select Inter-Site Connectivity when you were selecting regions to manage in the Region Management page), click Save and Continue. The Let's Configure the Basics page appears again. Skip to Step 22.
-
If you are configuring inter-site connectivity (if you selected Inter-Site Connectivity when you were selecting regions to manage in the Region Management page), click Next at the bottom of the page. The Inter-Site Connectivity page appears.
|
| Step 17 |
Enter the following information in the Inter-Site Connectivity page:
-
IPSec Tunnels to Inter-Site Routers: This field is necessary only for on-premises connectivity to cloud sites. There is no need to enter information in this
field if you don't have an on-premises site.
In this area, click the + button next to the Add Public IP of IPsec Tunnel Peer field.
-
OSPF Area for Inter-Site Connectivity: Enter the underlay OSPF area ID that will be used with on-premises ISN peering (for example, 0.0.0.1)
-
Under the External Subnets for Inter-Site Connectivity heading, click the + button next to the +Add External Subnet field.
-
Enter the subnet tunnel endpoint pool (the cloud TEP) that will be used in Azure. It must be a valid IPv4 subnet with a mask
between /16 and /22 (for example, 30.29.0.0/16). This subnet will be used to address the IPsec tunnel interfaces and loopbacks of the Cloud Routers used for on-premises
connectivity, and cannot overlap with other on-premises TEP pools.
-
Click the check mark after you have entered in the appropriate subnet pools.
|
| Step 18 |
When you have configured all the connectivity options, click Next at the bottom of the page.
The Cloud Resource Naming Rules page appears.
|
| Step 19 |
Choose Cloud Resource Naming mode.
Starting with Release 5.0(2), you can create a global naming policy on the Cloud APIC, which allows you to define a custom
cloud resources naming convention for all objects deployed from the Cloud APIC into the Azure cloud. Additional details about
naming rules, available object name variables, guidelines, and limitations are available in the earlier Cloud Resources Naming section of this chapter.
You can choose one of the following:
-
Default, in which case the cloud resources created by the Cloud APIC in Azure will be assigned names that are derived from the names
of the ACI objects. For example, resource groups' names will be based on the Tenant, VRF, and region: CAPIC_<tenant>_<vrf>_<region> .
-
Custom, in which case you can define your own rules for how each of the cloud resources is named.
When you select the custom naming, an Edit icon appears next to each cloud resource. You can click the edit icon to define the naming convention for one or more of
the displayed resources.
The variables that are available for this type of resource are listed under the naming rule text box. The variables are divided
into the Required Keyword and Optional Keywords, you must include all the required keywords for the rule you are updating. For example, when defining the naming rule for
Azure's Resource Groups, you must include the Tenant name, VRF name, and the Region keywords.
|
| Step 20 |
Confirm you have reviewed and accept the global resource naming policy.
Once a cloud resource is created, its name cannot be changed. As such, you must review and accept the global naming policy
you have defined in the previous step before any cloud resources can be deployed. When ready, enable the Deploy cloud resources based on these naming rules checkbox.
Note that you can leave the checkbox unchecked and choose to proceed, in which case any changes you have made will be saved
but no configuration will be deployed. You would need to come back to this screen to accept the naming policy to deploy.
|
| Step 21 |
When you have entered all the necessary information on this page, click Save and Continue at the bottom of the page.
The Let's Configure the Basics page appears again.
|
| Step 22 |
In the Smart Licensing row, click Register.
The Smart Licensing page appears.
|
| Step 23 |
Enter the necessary information in the Smart Licensing page.
Cisco Smart Licensing is a unified license management system that manages software licenses across Cisco products. To register
your Cloud APIC with Cisco Smart Software Licensing, do the following
-
Ensure that this product has access to the internet or a Smart Software Manager satellite installed on your network.
-
Log in to Smart Account:
-
Navigate to the Virtual Account containing the licenses to be used by this Product Instance.
-
Generate a Product Instance Registration Token (this identifies your Smart Account) and copy or save it.
To learn more about Smart Software Licensing, visit https://www.cisco.com/go/smartlicensing.
|
| Step 24 |
Click Register at the bottom of the page if you entered the necessary licensing information on this page, or click Continue in Evaluation Mode if you want to continue in evaluation mode instead.
The Summary page appears.
|
| Step 25 |
Verify the information on the Summary page, then click Finish.
At this point, you are finished with the internal network connectivity configuration for your Cloud APIC.
If this is the first time that you are deploying your Cloud APIC, this process might take quite a bit of time, possibly 30 minutes or so before the process is successfully completed.
|
| Step 26 |
Verify that the CSRs were successfully deployed.
-
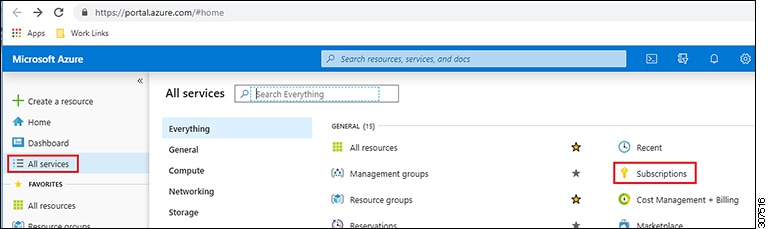
From the main Azure management portal page, click the All services link in the left nav bar, then click the Subscriptions link.
-
In the Subscriptions page in the Azure management portal, click the subscription account that you created.
The overview information for that subscription is displayed.
-
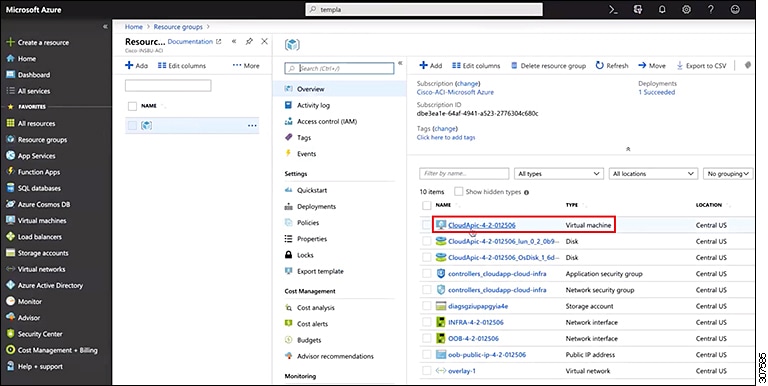
From the overview page for that subscription, locate the Resource groups link in the left nav bar and click that link.
The resource groups for that subscription is displayed.
-
Choose the resource group that you chose or created in the Custom deployment page in Deploying the Cloud APIC in Azure.
The overview information for that resource group is displayed.
-
In the overview page for the resource group, locate your CSR VM instance (shown as Virtual machine under the TYPE column), and click the link for that VM instance.
The CSR VM instance will have a name with a ct_routerp_region_x_0 format, where:
-
region is the managed region (for example, westus, westus2, centralus, or eastus)
-
x is the CSR count, starting from zero
For example: ct_routerp_centralus_0_0 or ct_routerp_centralus_1_0
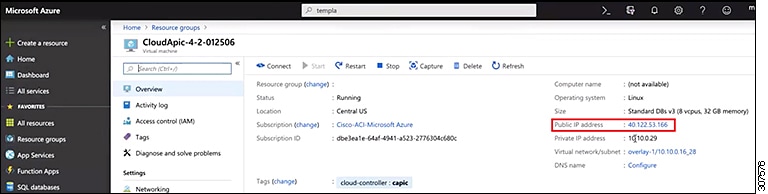
The overview information for the CSR VM instance is displayed.
-
Locate the Status field at the top left area in the page.
-
If you see the text Creating in the Status field, then the CSRs are not fully deployed yet.
-
If you see the text Running in the Status field, then the CSRs are fully deployed.
|

 Feedback
Feedback