Network Security within a Converged Plantwide Ethernet Architecture
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- December 21, 2018
Chapter: Troubleshooting
- TrustSec Troubleshooting Tips on Cisco IE and Allen-Bradley Stratix IES and Cisco Catalyst 3850 Switches
- IES is Unable to Register with Cisco ISE and Download the SGT Table Information
- Verify whether the IES and Cisco ISE have the Right TrustSec Credentials Matched
- Verify Whether the PAC Key Between the IES and the Cisco ISE is Configured Correctly
- Verify that RADIUS is Operational from the IES
- Verify that the CTS server-list is Pointing to the Right Policy Server Node
- Verify that the IES has Downloaded the Right SGT Table Information
- IACS Asset is Unable to Authenticate to Cisco ISE
- Verify the Authentication and Authorization State of IACS Assets Attached to an IES
- Verify that NMT has Discovered the IACS Asset 10.17.10.65
- Verify that the pxGrid Service is Enabled at Cisco ISE
- Verify that Profiling Policies are Configured Correctly
- Verify that Authentication and Authorization Policies are Configured Correctly in Cisco ISE
- Verify that pxGrid probe is enabled at PSN
- Verify Live Logs at ISE to Understand the Authentication/Authorization Flow
- 3850 Distribution Switch is not Enforcing the Policy Correctly
- Verify that SGT is Assigned to the Port on the IES
- Verify that SXP tunnel is up Between the Cisco ISE and the IES Device
- Verify that SXP Tunnel is Up at Cisco ISE to the IES (IE4K-25)
- Verify that Cisco ISE has Received the SGT-IP Mapping Information through the SXP Tunnel
- Verify that 3850 is Receiving the SGT-IP Information through SXP Tunnel
- Verify that Policy Matrix is Downloaded to the 3850 Distribution Switch
- IES is Unable to Register with Cisco ISE and Download the SGT Table Information
- Show Commands at the IES/3850 Distribution Switch
- Verify that the NetFlow Record is Collecting the Right Parameters
- Verify that the Exporter is Configured with the Right IP Address
- Verify that the Flow Monitor is Configured Correctly
- Verify that the Flow Monitor is Applied to an Appropriate Interface
- Verify that the Flow Information is Cached on the IES/3850 Switch
Troubleshooting the Infrastructure
TrustSec Troubleshooting Tips on Cisco IE and Allen-Bradley Stratix IES and Cisco Catalyst 3850 Switches
The following section describes certain show commands that can be executed to view potential sources of problems related to Cisco TrustSec.

Note![]() An IT engineer should have some expertise in TrustSec in order to troubleshoot any problems that are discovered. For complete information on Cisco TrustSec troubleshooting tips, refer to the following URL: https://community.cisco.com/t5/security-documents/trustsec-troubleshooting-guide/ta-p/3647576
An IT engineer should have some expertise in TrustSec in order to troubleshoot any problems that are discovered. For complete information on Cisco TrustSec troubleshooting tips, refer to the following URL: https://community.cisco.com/t5/security-documents/trustsec-troubleshooting-guide/ta-p/3647576
IES is Unable to Register with Cisco ISE and Download the SGT Table Information
Verify whether the IES and Cisco ISE have the Right TrustSec Credentials Matched
This is the first step and it is possible that the IT security administrator might have a typo in the password or the ID information in the IES or the Cisco ISE. Refer to the following sections in Chapter 4, “Configuring the Infrastructure”:
The credentials may be missing on the IES. Issue the following command:
Verify Whether the PAC Key Between the IES and the Cisco ISE is Configured Correctly
The PAC key must match between the Cisco ISE and the IES. If there is a mismatch in the IES, then re-configure the key, which will force a new PAC provisioning in the IES. Refer to Configuring RADIUS AAA in Chapter4, “Configuring the Infrastructure” To verify that the PAC is installed:
Verify that RADIUS is Operational from the IES
Verify that the CTS server-list is Pointing to the Right Policy Server Node
The command to verify the cts server-list is shown below:
Verify that the IES has Downloaded the Right SGT Table Information
IACS Asset is Unable to Authenticate to Cisco ISE
This section describes how to troubleshoot when an IACS device is unable to authenticate to Cisco ISE. To demonstrate the flow the IACS asset 10.17.10.65 is used to show the process.
Verify the Authentication and Authorization State of IACS Assets Attached to an IES
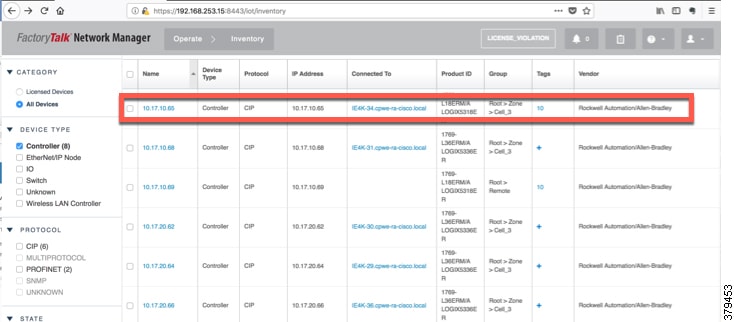
Verify that NMT has Discovered the IACS Asset 10.17.10.65
The first step would be to verify if NMT has discovered the IACS device 10.17.10.65.
Figure 6-1 NMT Discovering IACS Asset 10.17.10.65
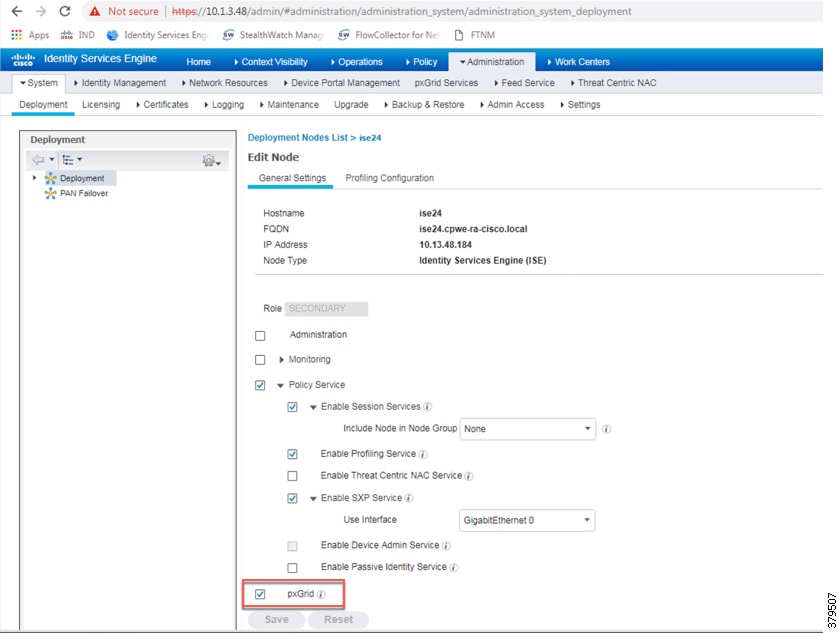
Verify that the pxGrid Service is Enabled at Cisco ISE
To verify that go to (ISE admin web) —> Administration —> Deployment and select the PSN (ise24 in this CPwE Network Security CVD):
Figure 6-2 Verifying that the pxGrid Service is Enabled at Cisco ISE
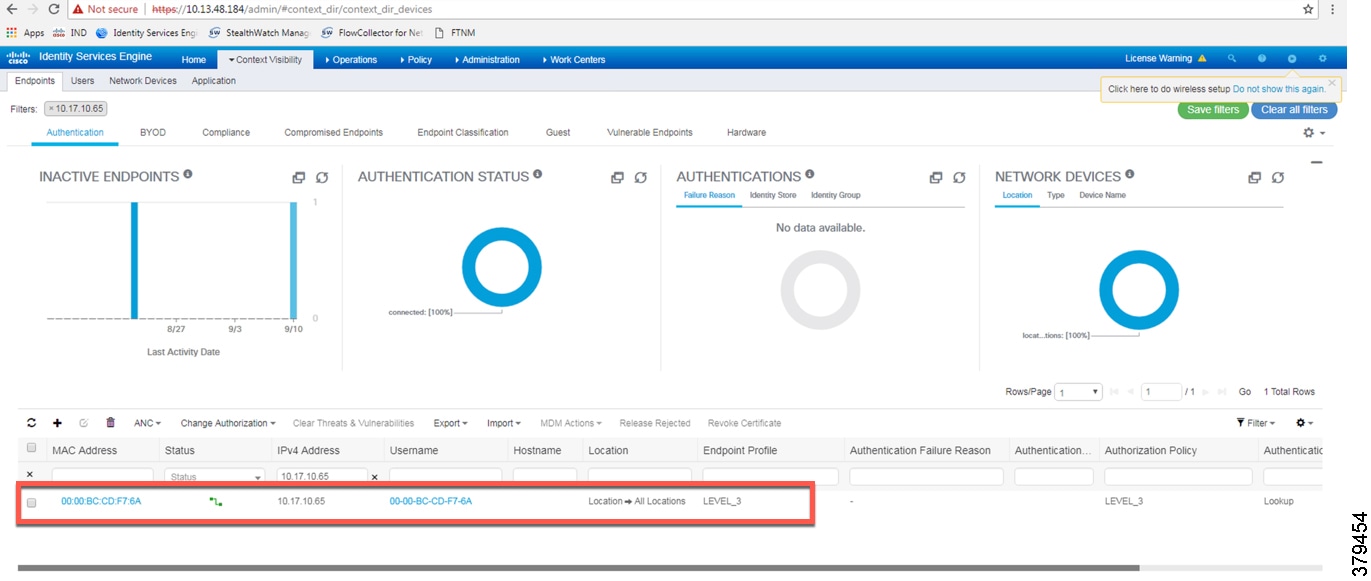
The next step is to verify if Cisco ISE has learned the IACS asset. Figure 6-3 shows that Cisco ISE has learned about the IACS asset.
Figure 6-3 Cisco ISE has Learned the IACS Asset 10.17.10.65
Verify that Profiling Policies are Configured Correctly
ISE profiles the IACS assets based on the profiling policy. If conditions in the profiling policy are not configured correctly, then ISE will not be able to profile the IACS asset. Refer to Profiling in Cisco ISE in Chapter 4, “Configuring the Infrastructure” for information on configuring the profiling policies
Verify that Authentication and Authorization Policies are Configured Correctly in Cisco ISE
To assign a SGT to an IACS asset, the authentication and authorization policy conditions must match to the IACS device attributes. Refer to Authorization Policies in Chapter4, “Configuring the Infrastructure”
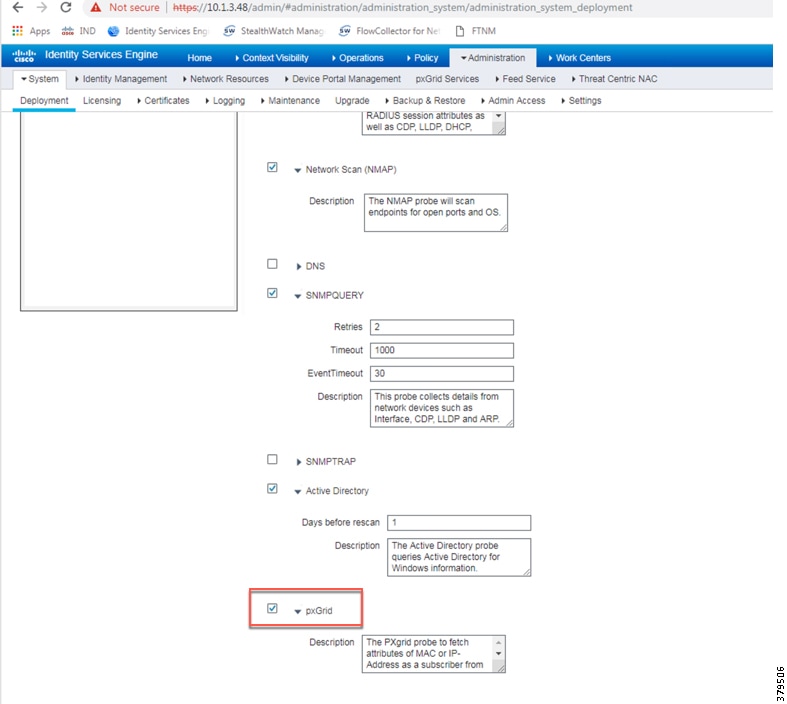
Verify that pxGrid probe is enabled at PSN
To verify that, go to (ISE admin web) —> Administration —> Deployment —> Select the psn (ise24 in this CVD) and select the tab profiling configuration.
Figure 6-4 Verifying that pxGrid Probe is Enabled on the PSN
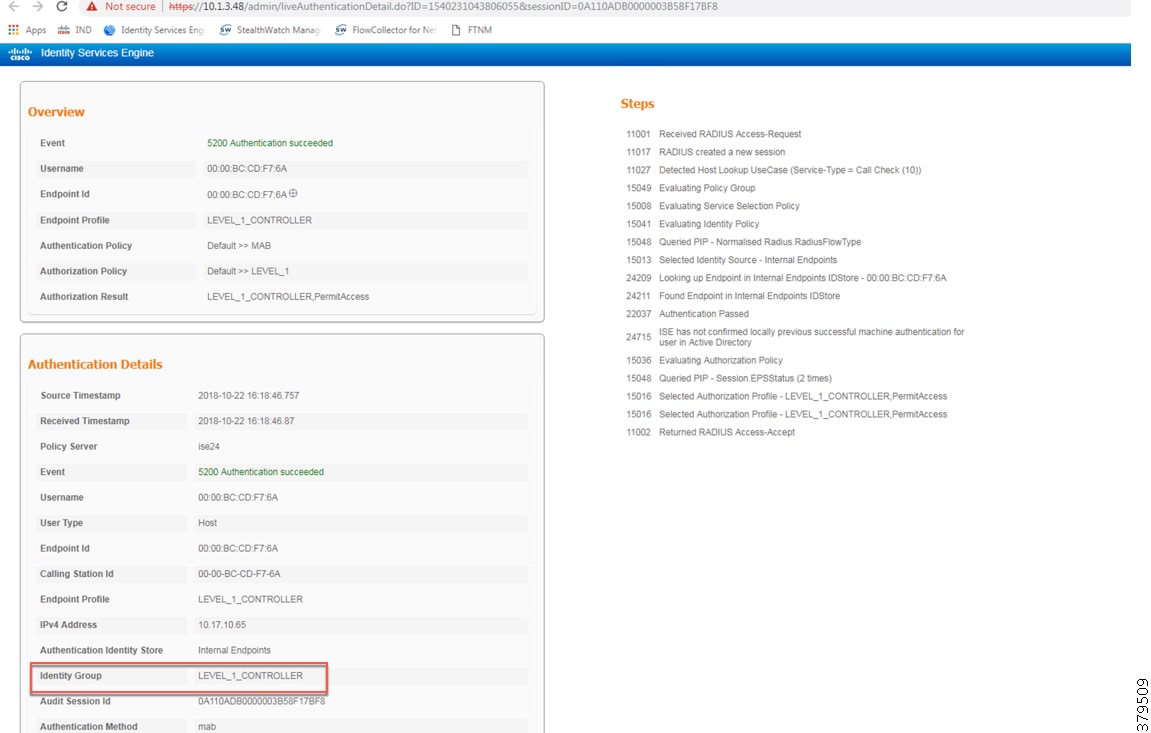
Verify Live Logs at ISE to Understand the Authentication/Authorization Flow
To see live logs, go to (ISE admin web) —> Operation —> Live Logs to get a list of devices that went through the authentication/authorization process.
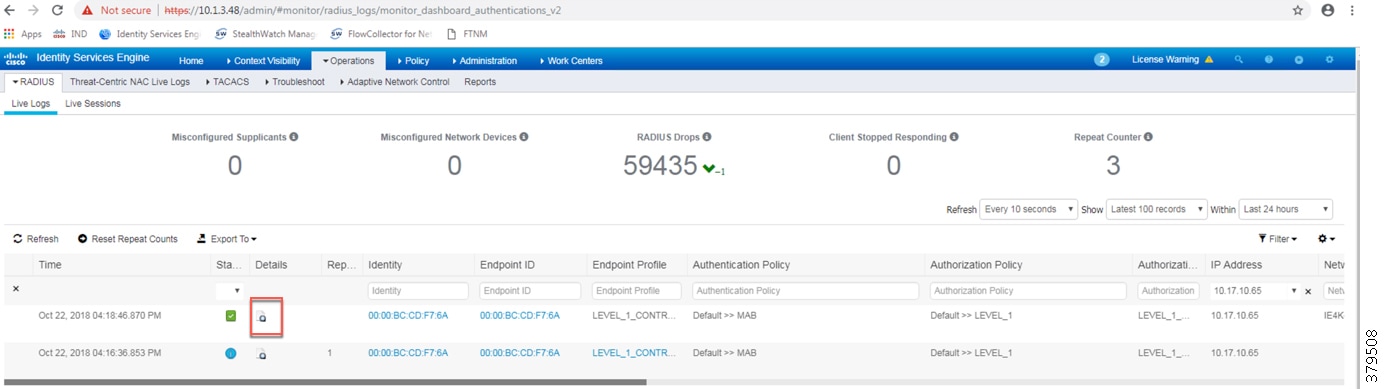
Selecting the Details option will provide details about the complete exchange.
Figure 6-6 Authentication and Authorization Results of an IACS Asset
3850 Distribution Switch is not Enforcing the Policy Correctly
Different reasons for this problem to happen exist; it can be troubleshooted by going through the following steps:
Verify that SGT is Assigned to the Port on the IES
Verify that SXP tunnel is up Between the Cisco ISE and the IES Device
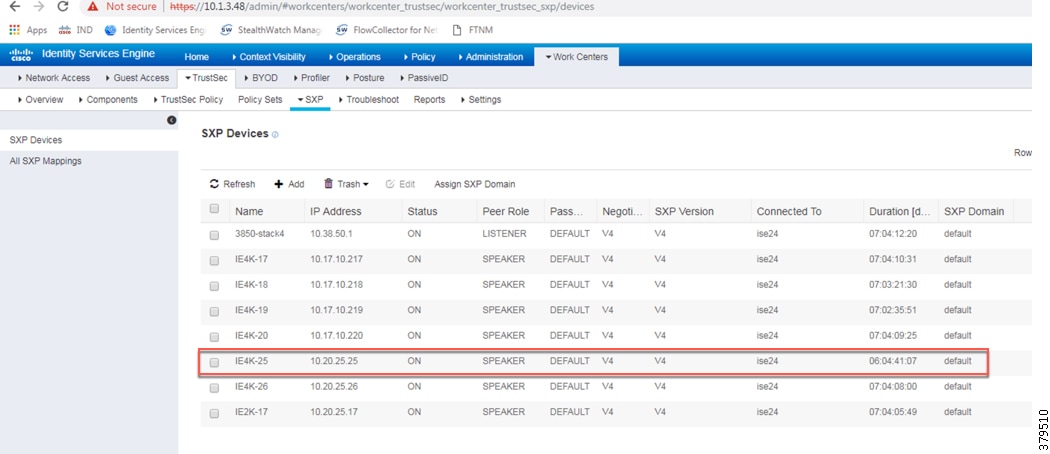
Verify that SXP Tunnel is Up at Cisco ISE to the IES (IE4K-25)
Navigate to (ISE admin web) —> Work Centers —> TrustSec —> SXP Devices and verify the SXP status.
Figure 6-7 Verifying the SXP Status of an IES Switch at ISE
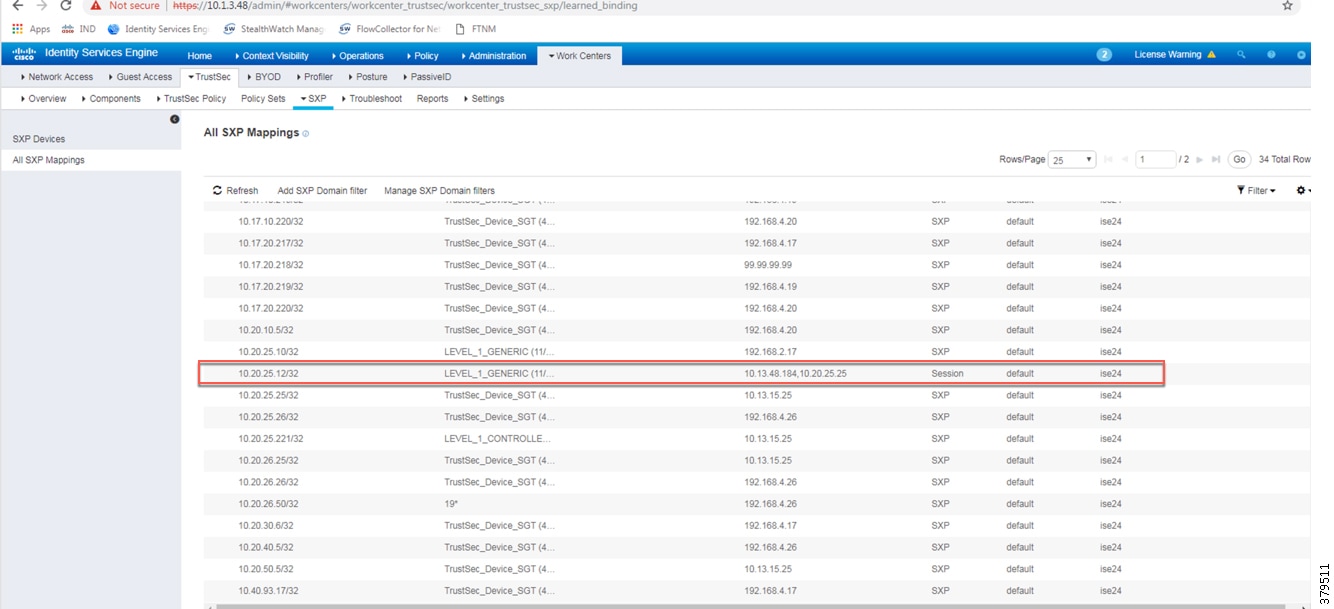
Verify that Cisco ISE has Received the SGT-IP Mapping Information through the SXP Tunnel
Figure 6-8 Verifying the SXP Status of an IES Switch at ISE
Verify that 3850 is Receiving the SGT-IP Information through SXP Tunnel
Verify that Policy Matrix is Downloaded to the 3850 Distribution Switch
Cisco NetFlow Troubleshooting Tips
This section discusses some useful show commands for troubleshooting if NetFlow records are not showing up at the Stealthwatch management console.
Show Commands at the IES/3850 Distribution Switch
This section describes the various show commands that can be issued to troubleshoot the problem in a methodical fashion.
Verify that the NetFlow Record is Collecting the Right Parameters
Verify that the Exporter is Configured with the Right IP Address
Verify that the Flow Monitor is Configured Correctly
Verify that the Flow Monitor is Applied to an Appropriate Interface
Verify that the Flow Information is Cached on the IES/3850 Switch
NMT Troubleshooting Tips
The configuration details for NMT can be found at:
- https://compatibility.rockwellautomation.com/Pages/MultiProductFindDownloads.aspx?crumb=112&refSoft=1&toggleState=&versions=57256
- https://www.cisco.com/c/en/us/td/docs/switches/ind/install/IND_1-5_install.html
A troubleshooting feature of NMT is to collect log information, which can help an IT security architect isolate a problem. Figure 6-9 shows how to collect logs for pxGrid in NMT.
Figure 6-9 Creating a Log File in NMT
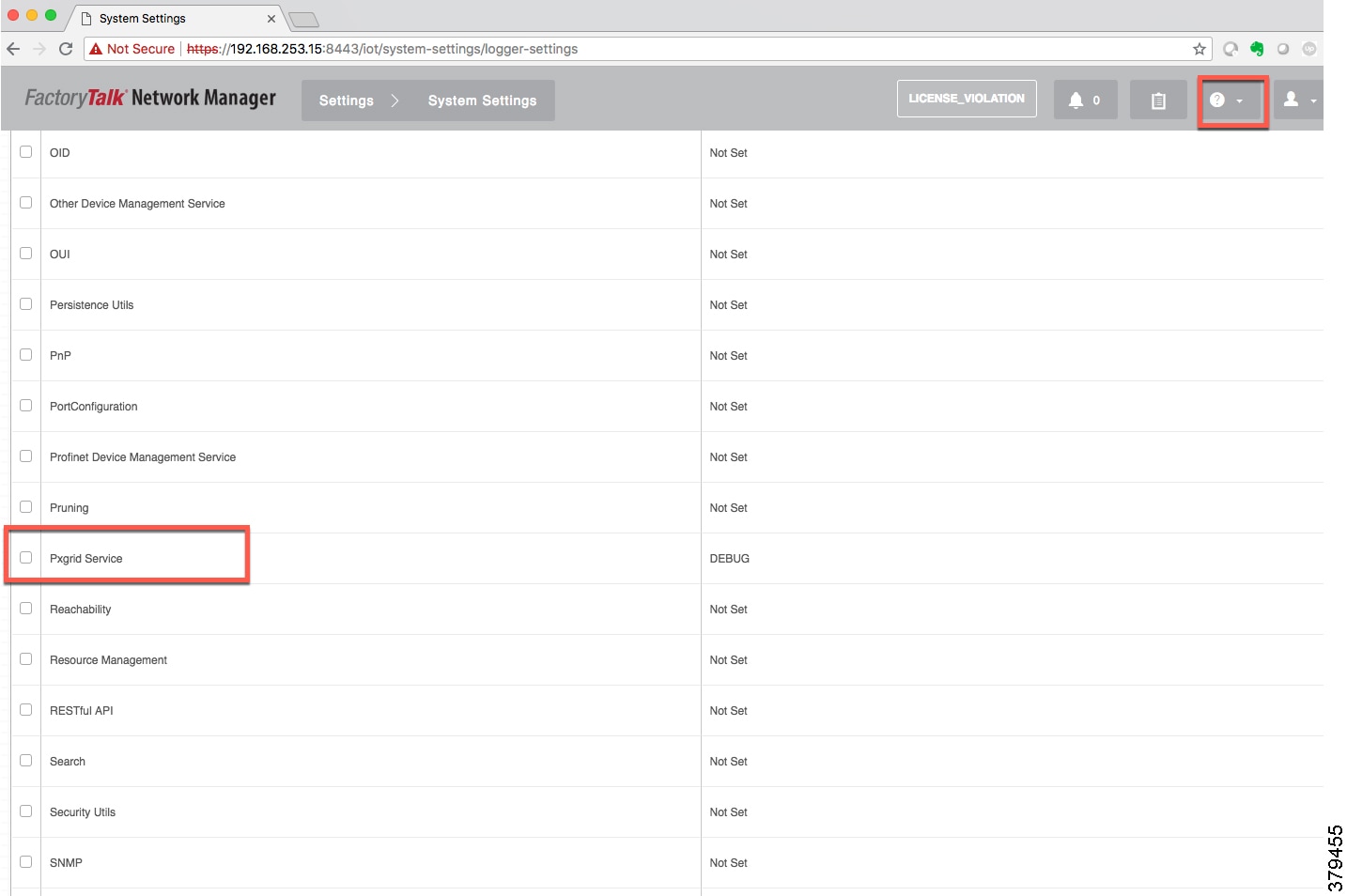
After enabling the log files, to download logs select the “?” option in the top right corner as shown in Figure 6-9.
Cisco ISE Troubleshooting Tips
The following section provides high level troubleshooting information to assist in identifying and resolving problems you may encounter when you use the Cisco Identity Services Engine (ISE).

Note For complete information on Cisco ISE monitoring and troubleshooting tips, refer to the following URL:
- https://www.cisco.com/c/en/us/td/docs/security/ise/2-4/admin_guide/b_ise_admin_guide_24/b_ise_admin_guide_24_new_chapter_011001.html
Checking the Status of pxGrid
On the PSN, execute the following command to check the status of the pxGrid:
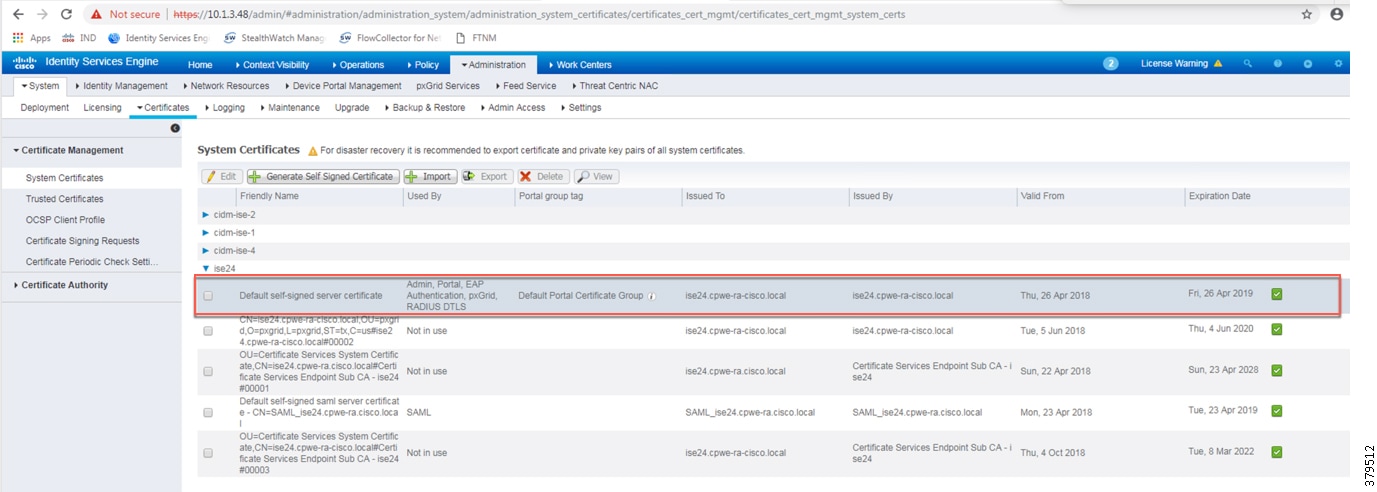
Verify pxGrid Certificate in ISE PSN
From (ISE admin Web), navigate to Administration —> System —> Certificates —> System Certificates and expand on PSN (ise24 in this CPwE Network Security CVD) to verify that system certificate is used for pxGrid.
Figure 6-10 Verifying pxGrid Certificate in ISE PSN
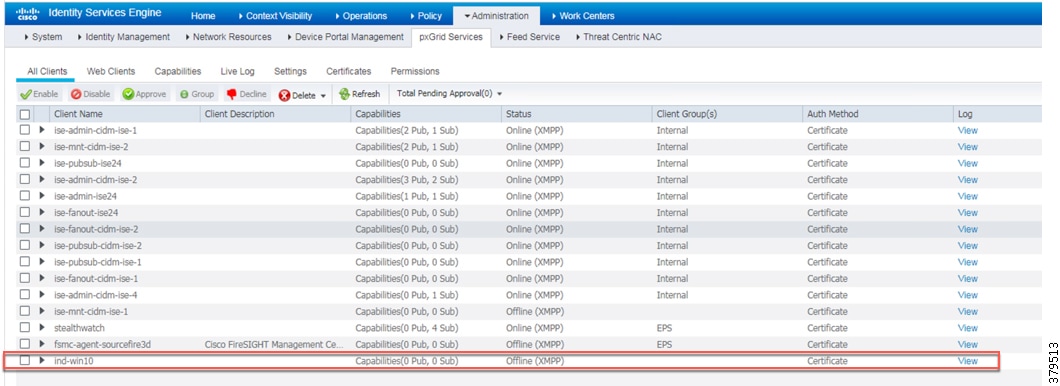
Verify the NMT pxGrid Status in ISE
From (ISE admin Web), navigate to Administration —> pxGrid Services and verify that NMT is registered as client.
Figure 6-11 Verifying the NMT pxGrid Status in ISE
Enable DEBUG on Profiler and pxGrid
In certain situations, it may be desired to enable debug on ISE and verify the exchange of information between the NMT and ISE via pxGrid. This section describes how to enable the debug.
Step 1![]() From (ISE admin web), navigate to Administration —> System —> Logging —> Debug Log Configuration.
From (ISE admin web), navigate to Administration —> System —> Logging —> Debug Log Configuration.
Step 2![]() Select the PSN on the right panel (ise24 in this CPwE Network Security CVD DIG).
Select the PSN on the right panel (ise24 in this CPwE Network Security CVD DIG).
Step 3![]() Select profiler and change the logging levels to DEBUG and click Save.
Select profiler and change the logging levels to DEBUG and click Save.
Step 4![]() Select pxgrid and change the logging levels to TRACE and click Save.
Select pxgrid and change the logging levels to TRACE and click Save.
To verify the log information, navigate to PSN (ise24) and issue the following command:
 Feedback
Feedback