Cisco Security Modules for Security Appliances
| Overview | Product Overview |
|---|---|
| Status | Available Order |
| Series Release Date | 15-APR-2008 |
- US/Canada 800-553-2447
- Worldwide Support Phone Numbers
- All Tools
 Feedback
Feedback
-
Key Information
Customers Also Viewed
Saved Content
-
You can now save documents for easier access and future use. Saved documents for this product will be listed here, or visit the My Saved Content page to view and manage all saved content from across Cisco.com.
Log in to see your Saved Content.
Document Categories
-
Data Sheets and Product Information
- Saipem Customer Video Case Study (PDF - 757 KB)
- Cisco ASA 5500 Series Advanced Inspection and Prevention Security Services Module and Card
- Cisco ASA 5500 Series Content Security and Control Security Services Module
Data Sheets
- EOL/EOS for the Cisco ASA Content Security and Control (CSC) Security Services Module Software Version 6.0
End-of-Life and End-of-Sale Notices
-
Security Notices
-
Applicable to Multiple Models
- Field Notice: FN - 63584 - IPS Sensors: Change in Server IP Address for IPS Signature Updates - Configuration Change Recommended
- Field Notice: FN - 64080 - IPS Sensors - Software Upgrade Required in Order to Enable SHA-2 Support For IPS Signature Updates - Software Upgrade Recommended
- Field Notice: FN - 63705 - ASA 5500-X Appliances - Default IPS Software Might Not Be Installed - Software Upgrade Recommended
- Field Notice: FN - 63521 - ASA5500-X Appliance - Units shipped without default configuration - Configuration Change Recommended
- Field Notice: FN - 64099 - IPS Sensors - Software Upgrade Required in Order to Enable SHA-2 Support for IPS Global Correlation - Software Upgrade Recommended
- Field Notice: FN - 63742 - ASA 5505 Series Appliances - Some Appliances Might Fail to Boot Up After a Power Cycle - Replace on Failure
- Field Notice: FN - 63741 - ASA 5500 Series Appliances - Some Appliances Might Fail to Boot Up after a Power Cycle - Replace on Failure
Field Notices
- Cisco ASA Content Security and Control Security Services Module Denial of Service Vulnerability
Security Advisories, Responses and Notices
-
-
Configuration
-
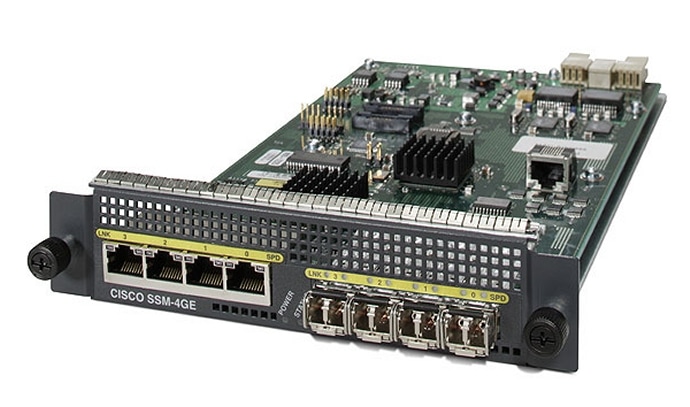
Cisco ASA 5500 Series 4-Port Gigabit Ethernet Security Services Module
-
Cisco ASA Advanced Inspection and Prevention Security Services Module
Configuration Examples and TechNotes
-
-
Troubleshooting
-
Applicable to Multiple Models
Password Recovery
-
Applicable to Multiple Models
-
Cisco ASA Content Security and Control (CSC) Security Services Module
Support FAQ
-
Cisco ASA 5500 Series 4-Port Gigabit Ethernet Security Services Module
-
Cisco ASA Content Security and Control (CSC) Security Services Module
Troubleshooting TechNotes
-
-
Log in to see available downloads.
-
-
Unless specified, documentation for the Cisco Security Modules for Security Appliances is applicable to all models.
Below are the supported models within this series:
- ASA 5500 Series 4-Port Gigabit Ethernet Security Services Module
- ASA 5512-X IPS Security Services Processor
- ASA 5512-X No Payload Encryption IPS Security Services Processor
- ASA 5515-X IPS Security Services Processor
- ASA 5515-X No Payload Encryption IPS Security Services Processor
- ASA 5525-X IPS Security Services Processor
- ASA 5525-X No Payload Encryption IPS Security Services Processor
- ASA 5545-X IPS Security Services Processor
- ASA 5545-X No Payload Encryption IPS Security Services Processor
- ASA 5555-X IPS Security Services Processor
- ASA 5555-X No Payload Encryption IPS Security Services Processor
- ASA 5585-X CX Security Services Processor
- ASA 5585-X IPS Security Services Processor
- ASA 5585-X No Payload Encryption IPS Security Services Processor
- ASA 5585-X No Payload Encryption Security Services Processor
- ASA 5585-X Security Services Processor
- ASA Advanced Inspection and Prevention (AIP) Security Services Module
- ASA Advanced Inspection and Prevention Security Services Card
- ASA Content Security and Control (CSC) Security Services Module
 Feedback
Feedback