About the ASA FirePOWER Module
The ASA FirePOWER module supplies next-generation firewall services, including Next-Generation Intrusion Prevention System (NGIPS), Application Visibility and Control (AVC), URL filtering, and Advanced Malware Protection (AMP).
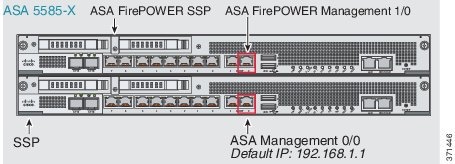
The ASA FirePOWER module runs a separate application from the ASA. The module can be a hardware module (on the ASA 5585-X only) or a software module (all other models).
How the ASA FirePOWER Module Works with the ASA
You can configure your ASA FirePOWER module using one of the following deployment models:
-
Inline mode—In an inline deployment, the actual traffic is sent to the ASA FirePOWER module, and the module’s policy affects what happens to the traffic. After dropping undesired traffic and taking any other actions applied by policy, the traffic is returned to the ASA for further processing and ultimate transmission.
-
Inline tap monitor-only mode (ASA inline)—In an inline tap monitor-only deployment, a copy of the traffic is sent to the ASA FirePOWER module, but it is not returned to the ASA. Inline tap mode lets you see what the ASA FirePOWER module would have done to traffic, and lets you evaluate the content of the traffic, without impacting the network. However, in this mode, the ASA does apply its policies to the traffic, so traffic can be dropped due to access rules, TCP normalization, and so forth.
-
Passive monitor-only (traffic forwarding) mode—If you want to prevent any possibility of the ASA with FirePOWER Services device impacting traffic, you can configure a traffic-forwarding interface and connect it to a SPAN port on a switch. In this mode, traffic is sent directly to the ASA FirePOWER module without ASA processing. The traffic is dropped, and nothing is returned from the module, nor does the ASA send the traffic out any interface. You must operate the ASA in single context transparent mode to configure traffic forwarding.
Be sure to configure consistent policies on the ASA and the ASA FirePOWER. Both policies should reflect the inline or monitor-only mode of the traffic.
The following sections explain these modes in more detail.
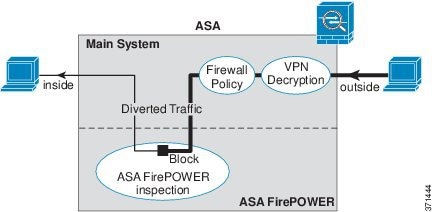
ASA FirePOWER Inline Mode
In inline mode, traffic goes through the firewall checks before being forwarded to the ASA FirePOWER module. When you identify traffic for ASA FirePOWER inspection on the ASA, traffic flows through the ASA and the module as follows:
-
Traffic enters the ASA.
-
Incoming VPN traffic is decrypted.
-
Firewall policies are applied.
-
Traffic is sent to the ASA FirePOWER module.
-
The ASA FirePOWER module applies its security policy to the traffic, and takes appropriate actions.
-
Valid traffic is sent back to the ASA; the ASA FirePOWER module might block some traffic according to its security policy, and that traffic is not passed on.
-
Outgoing VPN traffic is encrypted.
-
Traffic exits the ASA.
The following figure shows the traffic flow when using the ASA FirePOWER module in inline mode. In this example, the module blocks traffic that is not allowed for a certain application. All other traffic is forwarded through the ASA.
 Note |
If you have a connection between hosts on two ASA interfaces, and the ASA FirePOWER service policy is only configured for one of the interfaces, then all traffic between these hosts is sent to the ASA FirePOWER module, including traffic originating on the non-ASA FirePOWER interface (because the feature is bidirectional). |
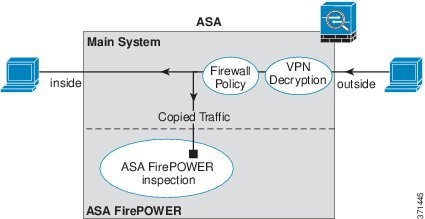
ASA FirePOWER Inline Tap Monitor-Only Mode
This mode sends a duplicate stream of traffic to the ASA FirePOWER module for monitoring purposes only. The module applies the security policy to the traffic and lets you know what it would have done if it were operating in inline mode; for example, traffic might be marked “would have dropped” in events. You can use this information for traffic analysis and to help you decide if inline mode is desirable.
 Note |
You cannot configure both inline tap monitor-only mode and normal inline mode at the same time on the ASA. Only one type of service policy rule is allowed. In multiple context mode, you cannot configure inline tap monitor-only mode for some contexts, and regular inline mode for others. |
The following figure shows the traffic flow when operating in inline tap mode.
ASA FirePOWER Passive Monitor-Only Traffic Forwarding Mode
If you want to operate the ASA FirePOWER module as a pure Intrusion Detection System (IDS), where there is no impact on the traffic at all, you can configure a traffic forwarding interface. A traffic forwarding interface sends all received traffic directly to the ASA FirePOWER module without any ASA processing.
The module applies the security policy to the traffic and lets you know what it would have done if it were operating in inline mode; for example, traffic might be marked “would have dropped” in events. You can use this information for traffic analysis and to help you decide if inline mode is desirable.
Traffic in this setup is never forwarded: neither the module nor the ASA sends the traffic on to its ultimate destination. You must operate the ASA in single context and transparent modes to use this configuration.
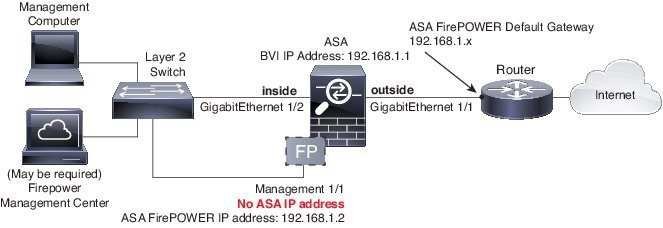
The following figure shows an interface configured for traffic-forwarding. That interface is connected to a switch SPAN port so the ASA FirePOWER module can inspect all of the network traffic. Another interface sends traffic normally through the firewall.

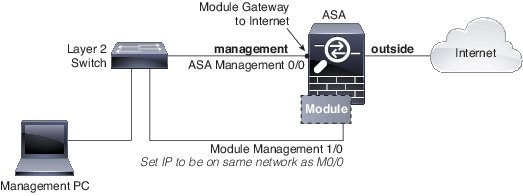
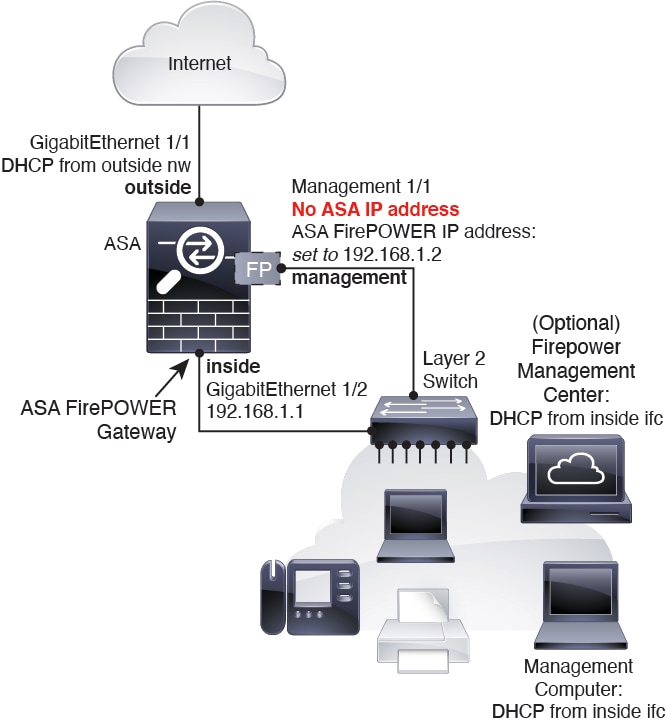
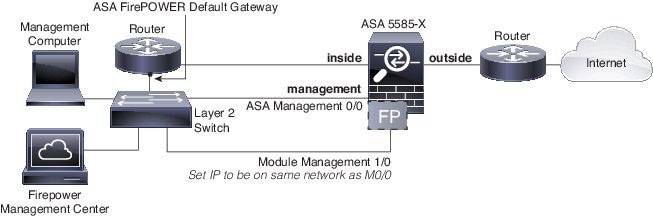
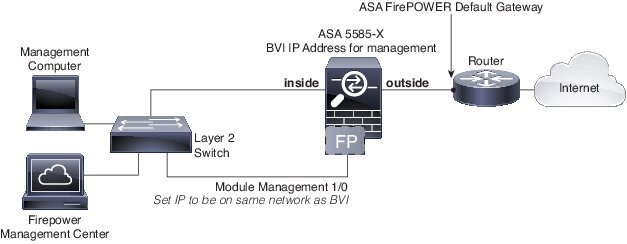
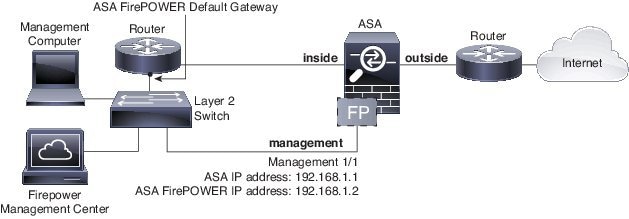
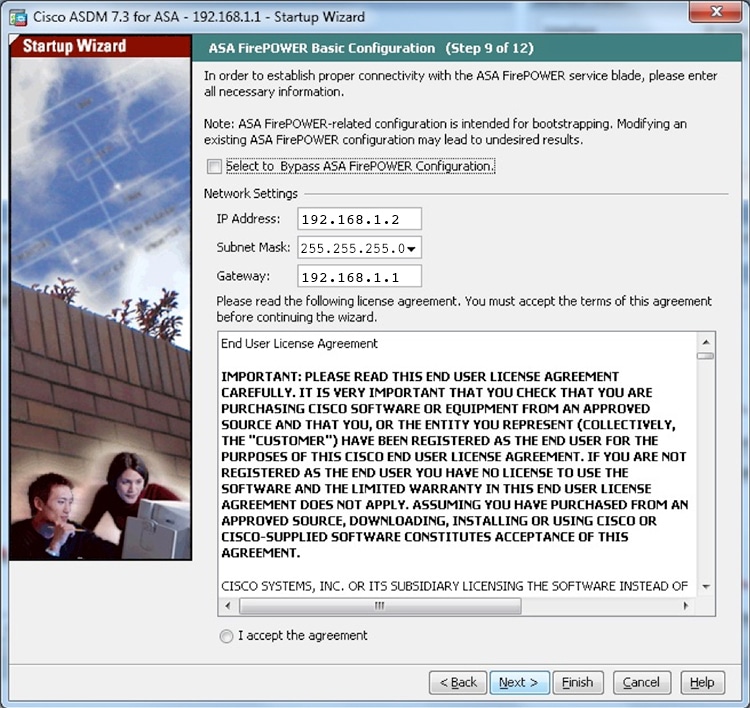
ASA FirePOWER Management
The module has a basic command line interface (CLI) for initial configuration and troubleshooting only. You configure the security policy on the ASA FirePOWER module using one of the following methods:
-
Firepower/FireSIGHT Management Center—Can be hosted on a separate Management Center appliance or as a virtual appliance. The Management Center application is called Firepower beginning in version 6.0. Previous versions are called FireSIGHT.
-
ASDM (check for compatibility with your model/version)—You can manage both the ASA and the module using the on-box ASDM.
Compatibility with ASA Features
The ASA includes many advanced application inspection features, including HTTP inspection. However, the ASA FirePOWER module provides more advanced HTTP inspection than the ASA provides, as well as additional features for other applications, including monitoring and controlling application usage.
You must follow these configuration restrictions on the ASA:
-
Do not configure ASA inspection on HTTP traffic that you send to the ASA FirePOWER module.
-
Do not enable the Mobile User Security (MUS) server; it is not compatible with the ASA FirePOWER module.
Other application inspections on the ASA are compatible with the ASA FirePOWER module, including the default inspections.
What to Do if the ASA FirePOWER Module Cannot Filter URLs
The ASA FirePOWER module obtains its URL filtering data from the managing Firepower Management Center, over HTTP. The module cannot perform URL filtering if it cannot download this database.
If there is a device between the ASA FirePOWER module and Firepower Management Center that is performing ASA HTTP inspection, the inspections can block the ASA FirePOWER module's HTTP GET requests to the Firepower Management Center. This problem also occurs if you configure HTTP inspection on the ASA that hosts the ASA FirePOWER module (which is a misconfiguration).
To resolve the issues, do any of the following that apply to your situation:
-
If you configured HTTP inspection on the ASA that hosts the ASA FirePOWER module, remove the HTTP inspection configuration. ASA FirePOWER inspection and ASA HTTP inspection are incompatible.
-
If there is an intervening device doing ASA HTTP inspection, remove the drop protocol violations action from the HTTP inspection policy map:
policy-map type inspect http http_inspection_policy parameters no protocol-violation action drop-connection
 Feedback
Feedback