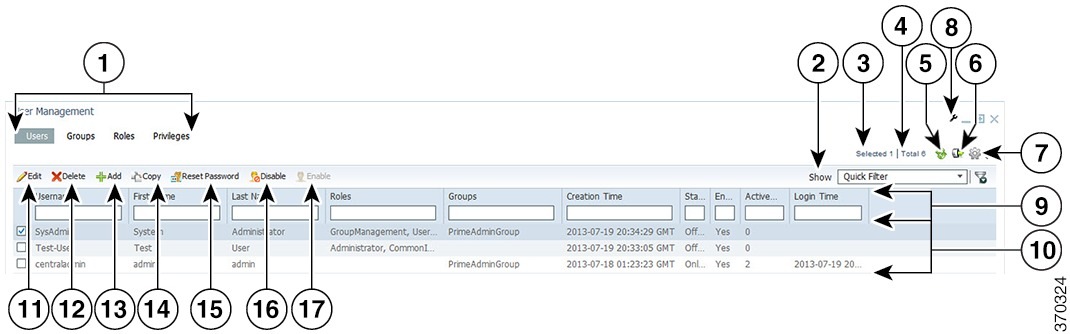
User Management Portlet
The following figure shows the User Management portlet, where users with administrator-level privileges can perform all user management tasks.
|
1 |
User management tabs: Users, Groups, Roles, Privileges |
10 |
Properties pane |
|
2 |
Show drop-down list and Filter icon |
11 |
Edit icon |
|
3 |
Number of selected table rows |
12 |
Delete icon |
|
4 |
Total table rows |
13 |
Add icon |
|
5 |
Refresh icon |
14 |
Copy icon |
|
6 |
Export icon |
15 |
Reset Password icon |
|
7 |
Settings icon |
16 |
Disable icon |
|
8 |
Options icon |
17 |
Enable icon |
|
9 |
Filter parameters area |
— |
— |
Managing Users
You can add, edit, copy, and delete users; reset user passwords; disable and enable user accounts; and configure user security settings.
Each user can be assigned any number of roles, and each role can aggregate any number of privileges.
Prime Central includes a default user named centraladmin whose account cannot be deleted or disabled. The centraladmin user has local authentication, user management, and administrator privileges, but initially does not have any privileges on the various applications.
Adding a User
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click Add. |
| Step 3 |
In the Add User window: |
| Step 4 |
In the Application Access Privilege area, grant user access to the appropriate applications and assign individual roles: Note the following:
|
| Step 5 |
Add the new user as a member of one or more groups:
All users that belong to the group share the same role. |
| Step 6 |
Click Add. The new user is displayed in the User Management portlet. |
| Step 7 |
Assign device scopes (in Prime Network and Agora-NG) or NEs (in Prime Optical) to the new user: |
Name, Password, Phone, and Note Constraints
When adding, editing, or copying a user, the variables that you define must adhere to the constraints listed in the following table.
|
Variable |
Constraints |
||||
|---|---|---|---|---|---|
|
Username |
The username must:
|
||||
|
Group name, role name, or privilege name |
The name must:
|
||||
|
Password |
The password must:
|
||||
|
Phone |
The phone number can contain up to 64 characters. All characters are allowed. |
||||
|
Note |
The note can contain up to 1000 characters. All characters are allowed. |
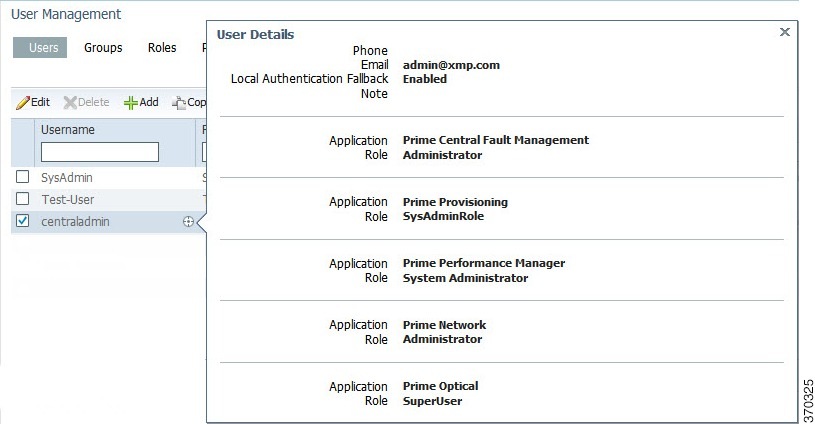
User Information in the Quick View
In the User Management portlet, the quick view displays additional user information when the cursor rests over the icon shown in the following figure.
Editing a User
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, select the user that you want to edit and click Edit. |
| Step 3 |
In the Edit User window: |
| Step 4 |
In the Application Access Privilege area, click the Roles tab and update the user's application access and roles, as required. If an application is not installed, it is not listed here. Note the following:
|
| Step 5 |
In the Application Access Privilege area, click the Groups tab and update the user's assigned groups and group roles, as required. |
| Step 6 |
Click Update. The updated user is displayed in the User Management portlet.. If you changed a user's assigned roles or access privileges, that user must log out of Prime Central and log back in to see the changes. The changes do not take effect until the user logs in next. You can also use Update to deactivate an user. |
| Step 7 |
(Optional) Reassign device scopes to the user you edited: |
Copying a User
You can easily create a new user by copying an existing user’s assigned privileges, groups, and roles.
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, select the user that you want to copy and click Copy. |
| Step 3 |
In the Add User window, make the following entries (this information is unique to each user and is therefore not copied from the existing user): |
| Step 4 |
For each of the following items, make any changes needed for the new user (the current information is copied from the existing user):
|
| Step 5 |
Click Add. The new user is displayed in the User Management portlet. |
| Step 6 |
Assign device scopes (in Prime Network and Agora-NG) or NEs (in Prime Optical) to the new user: |
Deleting a User
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, select the user that you want to delete and click Delete. |
| Step 3 |
At the confirmation prompt, click Yes. If the user exists on an application that is down when you delete the user from Prime Central, that user will persist on that particular application as a local user. |
Resetting Another User’s Password
Users with administrator-level privileges can reset another user’s password.
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, select the user whose password you want to reset and click Reset Password. |
| Step 3 |
In the Reset Password dialog box, enter a new password that adheres to the constraints described in Name, Password, Phone, and Note Constraints. |
| Step 4 |
Enter the new password again to confirm the entry. |
| Step 5 |
Click Save. |
Resetting Your User Password
Users of any privilege level can use the My Account portlet to reset their own Prime Central password. The password reset applies to the Prime Central user who is currently logged in.
Procedure
| Step 1 |
On the portal home page, place your cursor over your login name (to the left of the Log Out link) and click My Account. In the example shown in the following figure, the name is Test User. |
| Step 2 |
In the My Account portlet, enter your current password in the Current Password field. |
| Step 3 |
In the New Password field, enter a new password that adheres to the constraints described in Name, Password, Phone, and Note Constraints. |
| Step 4 |
Enter the new password again to confirm the entry. |
| Step 5 |
(Optional) In the Email field, edit the email address that will be displayed in the User Management portlet. This field is dimmed for the centraladmin user. |
| Step 6 |
(Optional) In the Phone field, edit the phone number that will be displayed in the User Management portlet. This field is dimmed for the centraladmin user. |
| Step 7 |
Click Save. 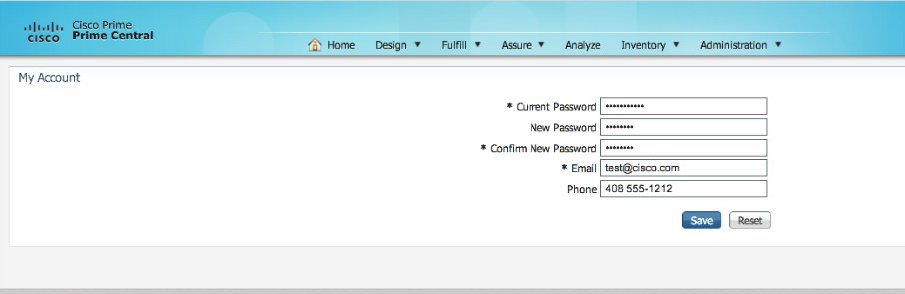 |
Resetting a Lost Password
From the UNIX command line, the Linux root user on the Prime Central portal can reset any Prime Central portal user’s password, including an administrator password.
Complete this procedure only after trying Resetting Another User’s Password and Resetting Your User Password.
Procedure
| Step 1 |
As the primeusr user, log in to the Prime Central portal with the primeusr password that you specified during installation. |
| Step 2 |
Enter the following command: |
| Step 3 |
When prompted, enter the root user password. |
| Step 4 |
Change directories to the $XMP_HOME/bin folder. |
| Step 5 |
Enter the following command: |
| Step 6 |
When prompted, enter the Prime Central username and the new password. In the following example, the Prime Central username is User_XYZ When the script finishes, output similar to the following is displayed: |
Enabling or Disabling a User Account
Users with administrator-level privileges can enable or disable another user’s account. However, you cannot disable the centraladmin user account.
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, select the desired user and click Enable or Disable. The User Management portlet > Enabled column displays the following value:
|
Configuring User Security Settings
Users with the appropriate privileges can configure security settings that apply to all other users.
The following security settings do not apply to the centraladmin user, who has administrator-level privileges:
 Note |
|
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the top-right corner of the User Management portlet, click the Options icon. |
| Step 3 |
Click the Configuration link. The User Management - Configuration dialog box (see the following figure) opens. |
| Step 4 |
Configure the security settings that will apply to all users. See the User Security Setting Descriptions table for more information. |
| Step 5 |
Click Save. 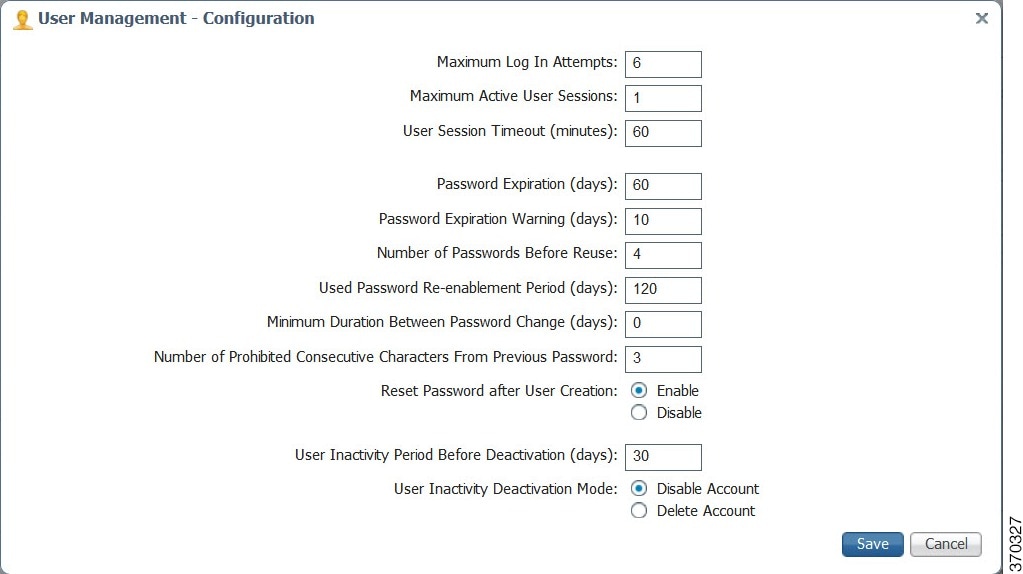 |
User Security Setting Descriptions
The following table describes the security settings you can configure for the users in your network.
|
Setting |
Description |
|---|---|
|
Maximum Log In Attempts |
The maximum number of failed login attempts allowed before the user account is denied access to Prime Central. The default is 6 retries. |
|
Maximum Active User Sessions |
The number of concurrent sessions allowed. The default is 1 session. |
|
User Session Timeout (minutes) |
The number of minutes a user’s session is inactive before Prime Central automatically locks the user out. By default, the session times out after 60 minutes of inactivity. You are prompted to extend the session 10 minutes before it times out. If you do not extend the session before the timeout, you are logged out automatically from Prime Central and from any applications. |
|
Password Expiration (days) |
The number of days before the password expires. The default is 60 days. |
|
Password Expiration Warning (days) |
The early warning period for password expiration. The default is 10 days. The value in this field must be less than the value in the Password Expiration field. |
|
Number of Passwords Before Reuse |
The number of different passwords a user must use before being allowed to reuse the first password. The default is 4 passwords. This field takes priority over the Used Password Re-enablement Period field. For example, assume that:
If the user password is test, you can change it to sample the next day, and then to basic on the second day. You can then change it back to test before 5 days elapses, because the Number of Passwords Before Reuse field takes priority. |
|
Used Password Re-enablement Period (days) |
The number of days before an old password can be reused. The default is 120 days. |
|
Minimum Duration Between Password Change (days) |
The number of days a user must wait between password changes. The default is 0 days. |
|
Number of Prohibited Consecutive Characters From Previous Password |
The number of consecutive characters by which the new password must differ from the previous one. The default is 3 characters. |
|
Reset Password after User Creation |
Specify whether newly added users will be prompted to reset their password before their first login. |
|
User Inactivity Period Before Deactivation (days) |
The number of days a user’s session is inactive before Prime Central automatically deactivates the user. The default is 30 days. |
|
User Inactivity Deactivation Mode |
Specify whether to disable or delete an inactive user account. The default is Disable Account. |
Managing Groups
All users that belong to a particular group share the same role and have access to a specific set of functions. User groups can be tied to one or more roles. The idea is to easily create groups of users who all share the same access privileges. A user can be assigned to more than one group, but this is not typical, as a single group should define an overall operational role within the suite.
Prime Central includes a default group named PrimeAdminGroup that cannot be edited or deleted.
Adding a Group
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click the Groups tab. |
| Step 3 |
Click Add. |
| Step 4 |
In the Add Group dialog box: |
Editing a Group
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click the Groups tab. |
| Step 3 |
Select the group that you want to edit and click Edit. |
| Step 4 |
Edit the group description or assigned roles, as required. The group description can contain from 1 to 50 alphanumeric or special characters. The group name is display only and cannot be changed. |
| Step 5 |
Click Update. |
Deleting a Group
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click the Groups tab. |
| Step 3 |
Select the group that you want to delete and click Delete. |
| Step 4 |
At the confirmation prompt, click Yes. |
Managing Roles
Users have access to functions based on the role to which they are assigned. Roles define the functions or tasks a user can perform. A user can be assigned more than one role.
Prime Central includes a set of default roles for security and access control that allow different system functions. The following table lists the default roles, the privileges that each role inherits, and the portlets that each role can access. (The default privileges are explained in Managing Privileges.) The default roles cannot be edited or deleted.
User roles inherit privileges as a union of role types. For example, the Fault Management role (which has no Common Inventory access) paired with the User role (which has Common Inventory access) results in Common Inventory access.
|
Default Role Name |
Privileges |
Ability to Access These Portlets: |
||||||||
|---|---|---|---|---|---|---|---|---|---|---|
|
My Account |
User Preferences |
User Management |
Suite Monitoring |
Group Management |
Common Inventory |
Alarm Browser |
Alarm Report |
Audit Log |
||
|
Administrator |
Admin Privilege |
Yes |
Yes |
Yes |
Yes |
Yes |
Yes |
Yes |
Yes |
Yes |
|
All Access Privilege |
||||||||||
|
InTracer Launch Privilege |
||||||||||
|
Common Inventory Admin |
Common Inventory Admin Privilege |
Yes |
Yes |
No |
Yes |
No |
Yes |
No |
No |
No |
|
Cross Launch Privilege |
||||||||||
|
Subsystem Inventory User Privilege |
||||||||||
|
User Privilege |
||||||||||
|
Common Inventory User |
Common Inventory User Privilege |
Yes |
Yes |
No |
Yes |
No |
Yes |
No |
No |
No |
|
Cross Launch Privilege |
||||||||||
|
Subsystem Inventory User Privilege |
||||||||||
|
User Privilege |
||||||||||
|
Fault Management |
Cross Launch Privilege |
Yes |
Yes |
No |
Yes |
No |
No |
Yes |
Yes |
No |
|
Fault Management Privilege |
||||||||||
|
Subsystem Inventory User Privilege |
||||||||||
|
User Privilege |
||||||||||
|
Group Management |
Group Management Privilege |
Yes |
Yes |
No |
No |
Yes |
No |
No |
No |
No |
|
User Privilege |
||||||||||
|
User |
Common Inventory User Privilege |
Yes |
Yes |
No |
Yes |
No |
Yes |
Yes |
Yes |
No |
|
Cross Launch Privilege |
||||||||||
|
Fault Management Privilege |
||||||||||
|
Subsystem Inventory User Privilege |
||||||||||
|
User Privilege |
||||||||||
|
User Management Admin |
Cross Launch Privilege |
Yes |
Yes |
Yes |
Yes |
No |
No |
No |
No |
No |
|
Subsystem Inventory Admin Privilege |
||||||||||
|
User Privilege |
||||||||||
|
User Management Admin Privilege |
||||||||||
 Note |
In the GUI, there are no spaces in the role or privilege names. |
Adding a Role
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click the Roles tab. |
| Step 3 |
Click Add. |
| Step 4 |
In the Add Role dialog box: |
Editing a Role
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click the Roles tab. |
| Step 3 |
Select the role that you want to edit and click Edit. |
| Step 4 |
Edit the role description or assigned privileges, as required. The role description can contain from 1 to 50 alphanumeric or special characters. The role name is display only and cannot be changed. |
| Step 5 |
Click Update. |
Deleting a Role
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click the Roles tab. |
| Step 3 |
Select the role that you want to delete and click Delete. |
| Step 4 |
At the confirmation prompt, click Yes. |
Managing Privileges
Privileges control the portlets, menu options, and back-end URLs that a role is authorized to access in Prime Central.
Prime Central provides the default privileges shown in the following table. The default privileges cannot be edited or deleted.
|
Default Privilege Name |
Can... |
|---|---|
|
Admin Privilege |
|
|
All Access Privilege |
|
|
Common Inventory Admin Privilege |
|
|
Common Inventory User Privilege |
|
|
Cross Launch Privilege |
|
|
Fault Management Privilege |
|
|
Group Management Privilege |
|
|
InTracer Launch Privilege |
|
|
Subsystem Inventory Admin Privilege |
|
|
Subsystem Inventory User Privilege |
|
|
User Management Admin Privilege |
|
|
User Privilege |
|
 Note |
In the GUI, there are no spaces in the privilege names. |
Adding a Privilege
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click the Privileges tab. |
| Step 3 |
Click Add. |
| Step 4 |
In the Add Privilege window:
|
| Step 5 |
Click Add. |
| Step 6 |
Create a new role and assign it the newly created privilege in the Privileges tab. See Adding a Role. |
Editing a Privilege
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click the Privileges tab. |
| Step 3 |
Select the privilege that you want to edit and click Edit. |
| Step 4 |
In the Edit Privilege window, update the privilege description, URL filter expressions, assigned portlets, and menu options, as required. The description can contain from 1 to 50 alphanumeric or special characters. The privilege name is display only and cannot be changed. |
| Step 5 |
Click Update. |
Deleting a Privilege
Procedure
| Step 1 |
From the Prime Central menu, choose . |
| Step 2 |
In the User Management portlet, click the Privileges tab. |
| Step 3 |
Select the privilege that you want to delete and click Delete. |
| Step 4 |
At the confirmation prompt, click Yes. |
Creating a Bulk User
From the Unix command line, you can create a new user named 'bulkuser' that can be used for Bulk User management operations.
Procedure
| Step 1 |
Log in to the Prime Central as a root user. |
| Step 2 |
In the directory installation-directory/utils/prime_tools/UtilityUsersDir folder, run the ./createBulkUser script. A user with name 'bulkuser' is created, which can be used for BulkUser Management operations. |
Importing Users in Bulk
From the UNIX command line, you can perform a bulk import of users from an Excel file that you create.
Procedure
| Step 1 |
As the bulkuser user, log in to the Prime Central server with the bulkuser password that you specified during creation. |
||
| Step 2 |
Change directories to the installation-directory/utils/prime_tools/UtilityUsersDir folder. |
||
| Step 3 |
Create your own Excel file that contains all the users you want to import; then, add that spreadsheet to the UtilityUsersDir folder. By default, the UtilityUsersDir folder contains a sample spreadsheet named customers.xlsx. You can structure your Excel file similarly. The sample customers.xls file contains four sheets, each of which corresponds to a step in the User Management portlet > Add wizard. Each sheet contains a GLOBAL SETTING row with information that will apply to all users, unless you overwrite the global setting with your specified value. If you leave a cell blank, Prime Central uses the global setting.
|
||
| Step 4 |
Enter the following command to import the users defined in your Excel file into the Prime Central database: sh importUsers FILE -c Excel-filename For example, to import a file named users_xyz.xlsx, enter: sh importUsers FILE -c users_xyz.xlsx |
||
| Step 5 |
At the following prompt, enter your Prime Central administrative username and password: |
||
| Step 6 |
At the following prompt: Do you want the system to
generate a random password for each imported user? [Y|N]:
Enter one of the following:
Enter
a default password for all imported users:
The import begins. After Import, output similar to the following is displayed:
|
||
| Step 7 |
Log in to Prime Central and choose to open the User Management portlet. Verify that the users you imported are visible in the Users tab. For the imported users, roles associated to bulk users, their associated groups and relevant domain managers from an Excel file that you create will be assigned automatically. |
Updating Users in Bulk
From the UNIX command line, you can perform a bulk update of users from an Excel file that you create.
Procedure
| Step 1 |
As the bulkuser user, log in to the Prime Central server with the bulkuser password that you specified during creation. |
| Step 2 |
Change directories to the installation-directory/utils/prime_tools/UtilityUsersDir folder. |
| Step 3 |
Create your own Excel file that contains all the users you want to update; then, add that spreadsheet to the UtilityUsersDir folder. By default, the UtilityUsersDir folder contains a sample spreadsheet named customers.xlsx. You can structure your Excel file similarly. The sample customers.xls file contains four sheets, each of which corresponds to a step in the User Management portlet > Add wizard. Each sheet contains a GLOBAL SETTING row with information that will apply to all users, unless you overwrite the global setting with your specified value. If you leave a cell blank, Prime Central uses the global setting. |
| Step 4 |
Enter the following command to update the users defined in your Excel file into the Prime Central database: sh importUsers-u FILE Excel-filename For example, to update a file named users_xyz.xlsx, enter: sh importUsers-u FILE users_xyz.xlsx |
| Step 5 |
At the following prompt, enter your Prime Central administrative username and password: |
| Step 6 |
Log in to Prime Central and choose to open the User Management portlet. Verify that the users you updated are visible in the Users tab. For the updated users, roles associated to bulk users, their associated groups and relevant domain managers from an Excel file that you create will be updated automatically. |
Retrieving Users in Bulk
From the UNIX command line, you can perform a bulk retrieve of users into an Excel file.
Procedure
| Step 1 |
As the bulkuser user, log in to the Prime Central server with the bulkuser password that you specified during creation. |
||
| Step 2 |
Change directories to the installation-directory/utils/prime_tools/UtilityUsersDir folder. |
||
| Step 3 |
Enter the following command to retrieve the users defined in the Prime Central database into the Excel file: sh importUsers -r FILE Excel-filename For example, to update a file named users_xyz.xlsx, enter: sh importUsers-r FILE users_xyz.xlsx
|
||
| Step 4 |
At the following prompt, enter your Prime Central administrative username and password: |
||
| Step 5 |
Log in to Prime Central and choose to open the User Management portlet. Verify that the users, which are visible in the Users tab are retrieved in the Excel file. |
Deleting Users in Bulk
From the UNIX command line, you can perform a bulk delete of users from an Excel file that you create.
Procedure
| Step 1 |
As the bulkuser user, log in to the Prime Central server with the bulkuser password that you specified during creation. |
| Step 2 |
Change directories to the installation-directory/utils/prime_tools/UtilityUsersDir folder. |
| Step 3 |
Create your own Excel file that contains all the users you want to delete; then, add that spreadsheet to the UtilityUsersDir folder. By default, the UtilityUsersDir folder contains a sample spreadsheet named customers.xlsx. You can structure your Excel file similarly. The sample customers.xls file contains four sheets, each of which corresponds to a step in the User Management portlet > Add wizard. Each sheet contains a GLOBAL SETTING row with information that will apply to all users, unless you overwrite the global setting with your specified value. If you leave a cell blank, Prime Central uses the global setting. |
| Step 4 |
Enter the following command to delete the users defined in your Excel file into the Prime Central database: sh importUsers-d FILE Excel-filename For example, to delete a file named users_xyz.xlsx, enter: sh importUsers-d FILE users_xyz.xlsx |
| Step 5 |
At the following prompt, enter your Prime Central administrative username and password: |
| Step 6 |
Log in to Prime Central and choose to open the User Management portlet. Verify that the users you deleted are not visible in the Users tab. |
Reporting User Logins in Bulk
From the UNIX command line, you can run a script to report users who logged in to (or did not log in to) Prime Central within a specific number of days.
Procedure
| Step 1 |
As the bulkuser , log in to the Prime Central portal with the bulkuser password that you specified during creation. |
| Step 2 |
Change directories to the installation-directory/utils/prime_tools/UtilityUsersDir folder. |
| Step 3 |
Enter the following command: sh reportUsers number-of-days {login | notlogin} output-filename For example, to report all users who logged in within the last 10 days and save the data to a text file named output_abc.txt, enter: sh reportUsers 10 login output_abc.txt To report all users who did not log in within the last 30 days and save the data to a text file named output_xyz.txt, enter: sh reportUsers 30 notlogin output_xyz.txt |
| Step 4 |
At the following prompt, enter your Prime Central administrative username and password: The script begins to run. When it finishes, the following output is displayed: The output file is saved in the runtime location that you specified; either absolute-path /filename or relative-path /filename . The output file contains four tab-separated columns that report the username, first name, last name, and last login date and time. |
Exporting User Data
Prime Central allows you to export user data to Microsoft Excel. Opening the exported file with any program other than Excel is not recommended.
If you sort or filter the data before exporting it, the exported data is likewise sorted or filtered. If you check the left-most check box for a row, the exported data contains a check box for each checked row.
Procedure
| Step 1 |
From the Prime Central menu, choose. |
||
| Step 2 |
In the User Management portlet, click the tab that contains the data you want to export. |
||
| Step 3 |
Click the Export to Excel icon. |
||
| Step 4 |
At the prompt to open or save the Excel file, click Open. The default filename depends on the tab you selected in Step 2.:
|
||
| Step 5 |
Click Yes at the following prompt: |
Auditing User Activity
Prime Central collects and stores security audit information, which you can use to track user activity such as logins or logouts, updates of user information, and application cross launches.
Procedure
| Step 1 |
From the Prime Central menu, choose . The Audit Log portlet opens, displaying user activity for the past 90 days (by default). |
| Step 2 |
To change the default value, do the following: |
Using an External Authentication Provider (LDAP or AAA Server) for User Authentication
By default, Prime Central uses internal authentication, which means passwords are stored in and verified against the data that is stored in the Prime Central database. You can also use a Lightweight Directory Access Protocol (LDAP) server or AAA server to manage user authentication externally. If you use external authentication, user information is checked against what is stored in the external LDAP or AAA server (instead of the Prime Central database). The external authentication server only stores login and password information; information pertaining to user roles is stored in the Prime Central database. The same user must exist in both the Prime Central database and the external authentication server.
Configuring Prime Central to Communicate with an External LDAP Server
When you configure Prime Central for external user authentication via an Lightweight Directory Access Protocol (LDAP) server, you can choose to add another layer of security by enabling the use of SSL encryption. Complete one of the following procedures to configure an LDAP server connection.
Configuring a Standard LDAP Server Connection
This procedure uses LDAP terminology, such as distinguished name (DN), common name (CN), and domain component (DC). An LDAP distinguished name uniquely identifies a user in the LDAP database, similar to a full filename but in reverse order. CNs and DCs are attributes of the domain name.
Procedure
| Step 1 |
In the User Management portlet, create a new user as described in Adding a User. For example, create a Prime Central user named test-admin . |
| Step 2 |
If the test-admin user does not already exist on the LDAP server, use an LDAP application to create the test-admin user. |
| Step 3 |
Reset the test-admin user's LDAP password, ensuring that you enter this same password in Step 4d. |
| Step 4 |
Do the following to enable LDAP authentication on the Prime Central portal: |
| Step 5 |
As the primeusr user, enter the following commands to restart the Prime Central portal: portalctl stop portalctl start You can now use the external authentication server for Prime Central authentication. In this example, the credentials to log in to the Prime Central portal are:
|
Sample LDAP Server Settings
The following table provides samples of the settings you would specify when configuring an LDAP server for Prime Central authentication.
|
Setting |
Sample Value |
Description |
||
|---|---|---|---|---|
|
ldapServerName |
ldap://209.165.200.254:56425 |
LDAP server IP address or hostname and directory server port number. |
||
|
ldapUserDn |
CN=test-admin,CN=Users,DC=t4,DC=local |
LDAP server user ID to log in to the LDAP server. To obtain the value you need to specify for this setting, run the following command: dsquery user -name test-admin
|
||
|
ldapPassword |
(Encrypted) zhEaxSqhTpJY0R2vStJJBQ== |
LDAP server user password to log in to the LDAP server. |
||
|
ldapBase |
CN=Users,DC=t4,DC=local |
LDAP base of LDAP users for authentication. |
Configuring an SSL-Encrypted LDAP Server Connection
Procedure
| Step 1 |
In the User Management portlet, create a new user as described in Adding a User. For example, create a Prime Central user named test-admin . |
| Step 2 |
If the test-admin user does not already exist on the LDAP server, use an LDAP application to create the test-admin user. |
| Step 3 |
Enable SSL encryption on your LDAP server, following the instructions provided in the documentation for your server. |
| Step 4 |
In the first line of the extprovider.properties file, which can be found in the installation-directory /XMP_Platform/conf/prime/conf folder:
For example, if port number 10636 is designated for SSL use on your server, the first line of the extprovider.properties file should look like this:
|
| Step 5 |
Export the LDAP SSL keystore certification by entering the following command: keytool -export -keystore Your_LDAP.ks -alias Your_Domain -file Your_LDAP.cer This command will create the keystore certificate (in this example, Your_LDAP .cer). Make sure to specify the same .ks file you set up when you enabled SSL encryption on your LDAP server. |
| Step 6 |
Import the keystore certificate into the Prime Central keystore by entering the following command: keytool -import -alias Your_Domain -file Your_LDAP.cer -keystore $ XMP_Home/jre/lib/security/cacerts where XMP_Home is the Prime Central installation directory. |
| Step 7 |
As the root user, enter the keystore password. |
| Step 8 |
Restart the Prime Central portal. |
| Step 9 |
(Optional) To verify that you have set up the LDAP server connection correctly using an LDAP client, such as jexplorer, import the keystone certificate to your local client machine by entering the following command: keytool -import -alias Your_Domain -file Your_LDAP.cer –keystore $ JAVA_Home/jre/lib/security/cacerts where JAVA_Home is the JDK installation directory. |
Configuring Prime Central to Communicate with an External AAA Server
Use this procedure to configure the Prime Central portal to communicate with the AAA (RADIUS or TACACS+) server, and to test the connection after it is configured. This procedure uses AAA terminology. User can configure upto three TACACS+ servers.
Procedure
| Step 1 |
In the User Management portlet, create a new user as described in Adding a User. For example, create a Prime Central user named test-admin . |
| Step 2 |
If the test-admin user does not already exist on the AAA server, use an AAA application to create the test-admin user. |
| Step 3 |
Do the following to enable AAA authentication on the Prime Central portal: |
| Step 4 |
As the primeusr user, enter the following commands to restart the Prime Central portal: portalctl stop portalctl start |
| Step 5 |
You can now use the external authentication server for Prime Central authentication. In this example, the credentials to log in to the Prime Central portal are:
|
Sample AAA Server Settings
The following table provides samples of the settings you would specify when configuring a AAA server for Prime Central authentication.
|
Setting |
Sample Value |
Description |
||
|---|---|---|---|---|
|
TACACS+ |
||||
|
server |
209.165.200.254 |
TACACS+ server IP address or hostname |
||
|
port |
49 |
TACACS+ server port number |
||
|
secondaryServer |
209.165.200.253 |
TACACS+ server IP address or hostname |
||
|
secondaryPort |
49 |
TACACS+ server port number |
||
|
tertiaryServer |
209.165.200.254 |
TACACS+ server IP address or hostname |
||
|
tertiaryPort |
49 |
TACACS+ server port number |
||
|
JaasSecretKey |
(Encrypted)TACACS+ server secret
key
zhEaxSqhTpJY0R2vStJJBQ== |
TACACS+ server secret key |
||
|
RADIUS |
||||
|
server |
209.165.200.254 |
RADIUS server IP address or hostname |
||
|
port |
1812 |
RADIUS server port number |
||
|
JaasSecretKey |
(Encrypted) zhEaxSqhTpJY0R2vStJJBQ== |
RADIUS server secret key |
||
|
authenticationType |
PAP |
RADIUS server authentication type
|
||
TACACS {
com.cisco.xmp.jaas.tacacs.TacacsLoginModule required
debug=true
JaasSecretKey="tIm+wkEvOaUqdbhWSLf+gA=="
server="172.168.203.200"
port="49"
secondaryServer="172.168.203.197"
secondaryPort="49";
}; Feedback
Feedback