- Preface
- ACS 5.8.1 Deployment Overview
- Understanding ACS 5.8.1 Configuration
- Configuring Migration Methods in ACS 5.8.1
- ACS 5.8.1 Migration Utility Support
- Migration Utility Setup and Installation
- Using the Migration Utility to Migrate Data from ACS 4.x to ACS 5.8.1
- ACS 5.8 Attribute Support in the Migration Utility
- Configuration Mapping from ACS 3.x to 5.8.1
- Feature Comparison of ACS 3.x and 4.x with ACS 5.8.1
- Troubleshooting the Migration Utility
Migration Guide for Cisco Secure Access Control System 5.8.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- March 21, 2016
Chapter: Using the Migration Utility to Migrate Data from ACS 4.x to ACS 5.8.1
- Introduction
- Running the Migration Utility
- Migration Script Sections
- Migration of ACS 4.x Objects
Using the Migration Utility to Migrate Data from ACS 4.x to ACS 5.8.1
This chapter describes how to migrate data from ACS 4.x to ACS 5.8.1 and contains:
■![]() Running the Migration Utility
Running the Migration Utility
■![]() Analysis and Export of ACS 4.x Data
Analysis and Export of ACS 4.x Data
■![]() Importing the ACS 4.x Data to ACS 5.8.1
Importing the ACS 4.x Data to ACS 5.8.1
■![]() Migration Impact on Memory and Performance
Migration Impact on Memory and Performance
■![]() Printing Reports and Report Types
Printing Reports and Report Types
■![]() Errors and Exception Handling
Errors and Exception Handling
Introduction
This chapter contains information to migrate data from ACS 4.x to ACS 5.8.1. Before you begin, you must follow the setup, backup, and installation instructions in Migration Utility Setup and Installation
Before you begin migration, ensure that you have enabled the migration interface on the ACS 5.8.1 server.
From the command line interface, enter:
acs config-web-interface migration enable
To verify that the migration interface is enabled on the ACS 5.8.1 server, from the command line interface, enter:
See the Command Line Interface Reference Guide for Cisco Secure Access Control System 5.8.1 for more information.
Running the Migration Utility
1.![]() Open a command prompt and change directory to C:\Migration Utility\migration\bin.
Open a command prompt and change directory to C:\Migration Utility\migration\bin.
You can specify any directory in which to install the Migration Utility. This example uses the Migration Utility as the root directory.
2.![]() At the command prompt, type migration.bat.
At the command prompt, type migration.bat.
Example 1: Migration Script (User Input) shows the prompts that appear when you run the Migration Utility.
Migration Script Sections
■![]() Migration environment information. See Migration Script Environment Information.
Migration environment information. See Migration Script Environment Information.
■![]() Migration user preferences. See Migration Script User Preferences.
Migration user preferences. See Migration Script User Preferences.
■![]() Migration groups. See Migration Script Object Groups.
Migration groups. See Migration Script Object Groups.
■![]() Migration phases. See Migration Script Phases.
Migration phases. See Migration Script Phases.
|
|
|
|---|---|
|
|
■ If data passes the Analysis phase, it can be exported and imported to ACS 5.8.1. See Migration of ACS 4.x Objects. Ensure that you back up your ACS 5.8.1 database. ■ ■ The config folder in the migration directory contains the full and summary reports. See Printing Reports and Report Types. ■ |
|
|
The default value is no. Enter yes to migrate another ACS 4.x instance. |
Migration of ACS 4.x Objects
The following sections describe in detail the various phases in the migration procedure and the impact and considerations for each object type.
■![]() NDG
NDG
■![]() EAP-Fast Master Keys and the Authority ID
EAP-Fast Master Keys and the Authority ID
AAA Client/Network Device
In ACS 4.x, the Network Configuration option contains NDGs, which in turn can contain AAA servers or AAA clients. The AAA client definitions are migrated and stored within the Network Devices and AAA Clients option in ACS 5.8.1.
Data Mapping
Table 5 shows the data mapping between ACS 4.x and ACS 5.8.1, for the AAA client or Network Devices.
Note: The group’s Single Connect flag overwrites the device’s Single Connect flag.
Analysis and Export
There are three major differences between the AAA Client (ACS 4.x) and Network Device (ACS 5.8.1) definitions:
■![]() In ACS 5.8.1, it is possible to define one network device that handles both RADIUS and TACACS+, while in ACS 4.x, two different AAA clients are required.
In ACS 5.8.1, it is possible to define one network device that handles both RADIUS and TACACS+, while in ACS 4.x, two different AAA clients are required.
■![]() In ACS 5.8.1, IP address is defined as a pair consisting of an IP address and a mask, while in ACS 4.1, IP address is defined using regular expressions.
In ACS 5.8.1, IP address is defined as a pair consisting of an IP address and a mask, while in ACS 4.1, IP address is defined using regular expressions.
■![]() In ACS 5.8.1, each network device definition is limited to storing 40 IP addresses. In ACS 4.x, it is possible to define more than 40 IP addresses.
In ACS 5.8.1, each network device definition is limited to storing 40 IP addresses. In ACS 4.x, it is possible to define more than 40 IP addresses.
■![]() Unsupported Characters in a Device Name
Unsupported Characters in a Device Name
Unsupported Characters in a Device Name
Some special characters are not allowed in the device name during export. You will get an error message during the analysis and the export will not proceed if the following characters are used in the device name:
In ACS 4.x, you can create definitions with overlapping IP addresses as part of a network device, where the first IP address utilizes TACACS+ and the second IP address utilizes RADIUS.
In ACS 5.8.1, TACACS+ and RADIUS are unified within a single network device definition. However, the unification is not possible if TACACS+ and RADIUS are part of different NDGs in ACS 4.x.
In the migration analysis phase, the network group and overlapping IP addresses are identified and reported to the administrator so that these definitions can be modified to conform to the ACS 5.8.1 requirements.
Network device AA: IP address = 23.8.23.*, 45.87.*.8, protocol = RADIUS, group = HR
Network device BB: IP address = 45.*.6.8, 1.2.3.4, protocol = TACACS, group = Admin
In this example, the second IP address in the AA network device list overlaps the first IP address in the BB network device list, and each of the network devices is part of a different NDG.
Consolidation between separate entries for RADIUS and TACACS+ network devices is possible only if the IP addresses are identical and both of the network devices are part of the same NDG. All consolidation is reported in the Analysis report.
ACS 5.8.1 supports wildcards and ranges. If you specify the IP address as in ACS 4.x, all existing IP addresses in ACS 4.x are migrated to ACS 5.8.1.
For example, the following IP address patterns can be translated:
The migration analysis process identifies the network devices with more than 40 IP subnets and reports that these devices cannot be migrated. To allow migration, you can change them to subnet masks or split them into multiple network device definitions to conform to the ACS 5.8.1 format. Table 6 describes the ACS 4.x attributes that can be modified to conform to ACS 5.8.1 limitations.
The keys that contain the following characters are identified during the analysis phase:
An error message appears during the analysis phase and the export will not proceed, if any of the following characters are found in the network device's Key Encryption Key or in the Message Authenticator Code Key:
Table 6 describes the ACS 4.x attributes that can be modified to conform to ACS 5.8.1 limitations.
Import
The Unified Device Name setting is used during import of network devices. In ACS 5.8.1, configuration options are available to determine the name of the new device in ACS 5.8.1, if there are separate RADIUS and TACACS+ devices in ACS 4.x that can be unified into a single network device definition. The following options are available in ACS 5.8.1:
ACS 4.x contains a single-level hierarchy between a network device and an NDG. Each defined network device (AAA client) must be included in one of the NDGs. To keep this association between the network device and the NDG, ACS 5.8.1 first exports and imports the NDGs, and then the network devices with an association to the NDGs. NDGs and network devices are processed as a single object group.
When a new record is imported into ACS 5.8.1, a default description field called Migrated is created.
Multiple-Instance Support
In ACS 5.8.1, you cannot define different network devices with an overlapping IP address. You may define a specific (or global) prefix for the network device name to avoid duplicates. However, devices that have overlapping IP addresses are reported as duplicates and are not migrated, even though their names are unique. Also, merge between two such instances is not supported.
Instance = X, network device = AA, IP address = 23.8.23.12, protocol = RADIUS, group = HR
Instance = Y, network device = BB, IP address = 23.8.23.12, protocol = TACACS+, group = HR
In this example, you cannot create a unified device, since the network device AA is from instance X and the network device BB is from instance Y. If the TACACS+ and RADIUS devices are from the same instance, unified device creation is supported.
Devices that are associated to an NDG that was imported in a previous migration instance are associated to the NDG that already exists in ACS 5.8.1.
NDG
To facilitate migration of the ACS 4.x NDG definitions, an additional NDG hierarchy has been created in ACS 5.8.1.
During the migration process, you are prompted to enter the name of the hierarchy root that stores the ACS 4.x NDG definitions. The prompt offers a default name of the migrated NDG; you can modify this name as desired.
ACS 4.x contains an unsaved group known as Not Assigned NDG for all the devices that do not belong to any group. The Not Assigned NDG group is created after export to ACS 5.8.1.
In ACS 4.x, the NDGs contain attributes such as shared secret and Legacy TACACS+ Single Connect support for the AAA client. However, in ACS 5.8.1, the NDGs are labels that can be attached to the network device definitions and do not contain data. If a value is set for the shared secret in an ACS 4.x NDG, this value is extracted to set the value for each network device that is associated with the group.
Data Mapping
Table 7 shows the data mapping between ACS 4.x and ACS 5.8.1 for the NDGs.
Analysis and Export
The following items are reported during the analysis phase:
■![]() Special characters in the NDG name—Some special characters are not allowed in the NDG name during export. An error message appears during the analysis and the export will not proceed if the following characters are used in the NDG name:
Special characters in the NDG name—Some special characters are not allowed in the NDG name during export. An error message appears during the analysis and the export will not proceed if the following characters are used in the NDG name:
■![]() NDGs that contains a shared secret definition—A message indicates that the shared secret definition will override the values defined at the device level.
NDGs that contains a shared secret definition—A message indicates that the shared secret definition will override the values defined at the device level.
■![]() NDGs that contain either Key Encryption Key or Message Authenticator Code Key definition—A message indicates that Key Encryption Key or Message Authenticator Code Key definition will override the values defined at the device level.
NDGs that contain either Key Encryption Key or Message Authenticator Code Key definition—A message indicates that Key Encryption Key or Message Authenticator Code Key definition will override the values defined at the device level.
■![]() Special characters in the network device's Key Encryption Key or in the Message Authenticator Code Key—An error message appears during the analysis phase and the export will not proceed, if any of the following characters are found in the network device's Key Encryption Key or in the Message Authenticator Code Key:
Special characters in the network device's Key Encryption Key or in the Message Authenticator Code Key—An error message appears during the analysis phase and the export will not proceed, if any of the following characters are found in the network device's Key Encryption Key or in the Message Authenticator Code Key:
No similar information is displayed during the export phase.
Import
During the import phase, a new NDG hierarchy is created, with the name as defined in the User Preferences. A root node with name as per the User Preferences, prefixed by All, is also created. All the migrated NDGs are created under this root node.
Multiple-Instance Support
In ACS 5.8.1, you cannot define two NDGs (hierarchy node) with the same name on one hierarchy root; however, it is possible to define them on different hierarchies. For example, you can define two groups named Engineers, one on the root SJ and the other on the root NY. Multiple-instance support allows you to do one of the following to migrate the NDGs:
■![]() Define a different root for each instance and import all the NDGs of the instance under the instance root.
Define a different root for each instance and import all the NDGs of the instance under the instance root.
■![]() Define one root for all the migrated NDGs; the Migration Utility adds only the unique NDGs to the root. NDGs that already exist are reported as duplicates and are not imported. However, in this case the ID of the already existing NDG is retrieved for association purposes.
Define one root for all the migrated NDGs; the Migration Utility adds only the unique NDGs to the root. NDGs that already exist are reported as duplicates and are not imported. However, in this case the ID of the already existing NDG is retrieved for association purposes.
To choose either of these options, go to Preferences > User Interface. For each selection, the association between the NDG and the network devices is maintained according to the logic of that selection.
For example, Device ABC (with a unique name and IP address) associated to an NDG SJ is migrated from the first ACS 4.x instance. When you select any of the above two options, ABC is associated to NDG SJ, but SJ can be defined either in the root All or in the specific root Engineers.
Internal User
In ACS 5.8.1, policy components are reusable objects that can be selected as policy results.
Migration activities that are related to internal users consist of the following aspects:
■![]() User Data Configuration and User Mapping
User Data Configuration and User Mapping
■![]() User Shell Command Authorization
User Shell Command Authorization
ACS 4.x can contain dynamic users. External databases, such as LDAP, can manage dynamic users, their identities, and other related properties.
Dynamic users are created in the ACS internal database after they are successfully authenticated against external sources. Dynamic users are created for optimization, and removing them does not affect ACS functionality. Dynamic users are ignored by the Migration Utility and are not processed.
Basic User Definition
For each user, the basic definition includes username, password, disable or enable status, and identity group.
Table 8 shows the user interface data mapping of ACS 4.x with ACS 5.8.1 for internal users.
Some special characters and <space> are not allowed in the username during export. It is reported in the Analysis report if the following characters are used in the username:
By default, internal users who are authenticated to use an external password type are migrated as internal users with an internal password type. with external password type are migrated with the password type, as internal users. Users with an internal password type are reported in the Analysis report.
Users with a password of fewer than four characters are not exported. The option “Disable Account if Date Exceeds” is also migrated in ACS 5.8.1.
Note: User Command Sets are not migrated for users whose username contains an apostrophe (’).
The following options are available in the password definitions for internal users:
■![]() Internal—Password is stored internally in ACS.
Internal—Password is stored internally in ACS.
■![]() External Database—Password is stored in an external database, and authentication is performed against this database.
External Database—Password is stored in an external database, and authentication is performed against this database.
■![]() Empty Password—VoIP users can be defined by associating them with a group that has the following settings selected “ T his is a Voice-over-IP (VoIP) group and all users of this group are VoIP users”. In this case, no password is defined for the user.
Empty Password—VoIP users can be defined by associating them with a group that has the following settings selected “ T his is a Voice-over-IP (VoIP) group and all users of this group are VoIP users”. In this case, no password is defined for the user.
Externally authenticated users are not supported in ACS 5.8.1. The following configuration options are available to define the import of such users:
■![]() Default authentication password—All externally authenticated users are assigned with this password.
Default authentication password—All externally authenticated users are assigned with this password.
■![]() Disabled or Change password—You can select whether such users are defined in ACS 5.8.1 as disabled or are required to change their password on the next login.
Disabled or Change password—You can select whether such users are defined in ACS 5.8.1 as disabled or are required to change their password on the next login.
No analysis warnings are displayed for such users, because there could be a large number of users.
Note: VoIP is not supported in ACS 5.8.1. Users that are associated with a VoIP-enabled user group are reported as part of the analysis and are not exported.
Multiple-Instance Support
Duplicate identification of users from different ACS 4.x instances is based on the username and is reported in the Import report. Only unique users are migrated. There is no support for a name prefix or merge between users' data from multiple ACS 4.x instances.
For example, it is not possible to add an enable password to the user Jeff, if Jeff exists in multiple ACS 4.x instances and the enable password exists only on the instance that was not migrated first.
Users who have a unique username and are associated to a user group are migrated and the association preserved, even if the user group itself was migrated in the same instance as the user or in a previous instance.
Note: If the user does not pass migration, user attribute values and policy components such as TACACS+ and Shell attribute values and the Command Set that originated from the user, are also not migrated, even if they are valid.
User Data Configuration and User Mapping
ACS 4.x contains up to five user-defined fields that can be selected for inclusion in the user record. For each such field, a corresponding field name can be defined. In ACS 5.8.1, these fields are migrated so that equivalent user attributes can be created and then populated for each user.
To configure these fields, select Interface Configuration > User Data Configuration. You must repeat the configuration for each of the five fields.
Table 9 shows the user interface data mapping between ACS 4.x and ACS 5.8.1 for User Data Configuration and User Mapping.
Analysis is performed on the field name to check:
■![]() The field length does not exceed 32 characters.
The field length does not exceed 32 characters.
■![]() The field does not contain the following special characters
The field does not contain the following special characters
In ACS 4.x, you can define multiple field names with the same name. However, in ACS 5.8.1, user-defined attributes must have unique names. If multiple attributes have the same name, the original name is retained only for the first attribute found. For subsequent attribute, the suffix _1 is added.
For example, if three attributes in ACS 4.x have the name ACS, after import to ACS 5.8.1, the attribute names are as follows:
In ACS 5.8.1, you cannot define two user attributes with the same name on the identity dictionary. However, you can create a name prefix for each ACS 4.x instance and add the attribute for each instance.
You can select one of the following options to migrate the user attributes:
■![]() Define a different name prefix for each instance and import all the user attributes with different names.
Define a different name prefix for each instance and import all the user attributes with different names.
■![]() Do not define a prefix. This results in unique attributes migration only. Attributes that already exist are reported as duplicates. In this case, the ID of the existing user attribute is preserved for association purposes.
Do not define a prefix. This results in unique attributes migration only. Attributes that already exist are reported as duplicates. In this case, the ID of the existing user attribute is preserved for association purposes.
User data for any user is taken only from a single ACS 4.x instance. If the same user exists in another ACS 4.x instance, the user is not imported but the user attributes are migrated with null values. There is a single set of internal user attributes that applies to all users.
For example, you migrate the user, user1 with user attribute A with value x and user attribute B with value y, from first ACS 4.x instance. Then, you migrate the same user, user1 with user attributes C with value z and user attribute D with value w, from the second ACS 4.x instance.
Here, the user user1 from the second instance is not migrated, but the user attributes C and D are migrated with null values. The user user1 in ACS 5.8.1 contains the following attributes:
■![]() C with null value from the second instance.
C with null value from the second instance.
■![]() D with null value from the second instance.
D with null value from the second instance.
The same user can contain attributes from second instance but not the attribute values. You cannot merge user attributes from multiple ACS 4.x instances.
For example, it is not possible to add only the attribute Real Name: Jeffrey to user jeff, if the user already exists in ACS 5.8.1 (migrated from another ACS 4.x instance) and the attribute Real Name: Jeffrey exists only on the current ACS 4.x instance.
The association between the user and the user attribute is preserved regardless of the migration run (current or previous migration) when the user attribute definition is migrated. A user with a unique username (that can be added in the current run) that is associated with a user attribute that already exists in ACS 5.8.1 (and was migrated in a previous run of the migration) is associated to the existing user attribute.
In ACS 5.8.1, every identity attribute that gets added to the dictionary also gets added to all the users, even if the value is blank.
For example, you create user, User1 in ACS 4.x first instance and start the Migration Utility. Enter the first instance server ID and add server specific migration prefix global1. Migrate the user, User1 with user attributes city, real name and description.
Create user, User2 in ACS 4.x second instance and start the Migration Utility. Enter the second instance server ID and add server specific migration prefix global2. Migrate the user, User2 with user attributes city, country and state.
After migration to ACS 5.8.1, user1 will contain the attributes, global1_city, global1_Description, global1_Real Name, global2_city, global2_country and global2_state.
User2 will contain the attributes, global1_city, global1_Description, global1_Real Name, global2_city, global2_country and global2_state.
Here, attributes with prefix global1 should be used for User1 and attributes with prefix global2 should be used for User2.
User Shell Command Authorization
In ACS 4.x, a shell command set can be embedded in the user record. As part of the migration functionality, this command set is extracted and defined as a shared object. A user attribute contains the name of a command associated with a user that was retrieved from the user record.
User command sets are migrated to shared command sets only if the user is migrated. The name is generated from the username.
Shared command sets are extracted only if the corresponding user was migrated.
Table 10 shows the user interface data mapping between ACS 4.x and ACS 5.8.1 for the user shell command authorization.
In ACS 4.x, you can assign a shell command authorization set on a per-NDG basis, where the user record contains pairs of device group names and command set names. This equivalent functionality is not supported in ACS 5.8.1, and a message is displayed during analysis.
The following user settings are used during import of each user command set:
■![]() Command set name format options—Add Prefix | User Name only.
Command set name format options—Add Prefix | User Name only.
■![]() Prefix to be added for consolidated objects in addition to the previous prefix—Default is an empty string
Prefix to be added for consolidated objects in addition to the previous prefix—Default is an empty string
The user attribute cmd-set is used to store the name of the ACS 5.8.1 command set that is migrated from a user definition.
1.![]() Create the cmd-set user attribute.
Create the cmd-set user attribute.
2.![]() For users who have a per-user definition of a command set:
For users who have a per-user definition of a command set:
- If the command set has been consolidated into another record, then proceed to process the next user.
a.![]() Determine the name of the command set as a combination of the username and any defined prefixes.
Determine the name of the command set as a combination of the username and any defined prefixes.
b.![]() Create the migrated command set.
Create the migrated command set.
3.![]() Set the name of the migrated command set in the cmd-set user attribute for the user.
Set the name of the migrated command set in the cmd-set user attribute for the user.
In ACS 5.8.1, you cannot define two command sets with the same name. However, you can create a command set with a name prefix per ACS 4.x instance and migrate the command sets for each ACS 4.x instance.
Thus, you can choose one of the following options to migrate command sets:
■![]() Define a different name prefix for each instance and import all the command sets with different names.
Define a different name prefix for each instance and import all the command sets with different names.
■![]() Do not define a prefix. Only unique command sets are migrated. The command sets that already exist (migrated in the previous instance), are reported as duplicates.
Do not define a prefix. Only unique command sets are migrated. The command sets that already exist (migrated in the previous instance), are reported as duplicates.
Shell Exec Parameters
In ACS 4.x, the user record contains shell (exec) TACACS+ settings. These settings are migrated to
ACS 5.8.1 as attributes of the user record. If one of these attributes is in use for any of the migrated user records, it is created as a user attribute. The value is set in the corresponding attribute in the migrated user definition.
The user shell attribute values are migrated only if the user is migrated.
Table 11 shows the data mapping between ACS 4.x and ACS 5.8.1 for the user shell attribute. All attributes, except the Max Privilege attribute, are taken from the TACACS+ shell (exec) settings.
|
|
|
|
|---|---|---|
ACS 5.8.1 supports the privilege level as a numeric value (0-9999). In ACS 4.x, privilege level is a string field with no validity checks. If the privilege level is not within the valid range, it is reported to the administrator.
This check is not applicable to the enable password, where the privilege level is selected from a valid list. However, an additional analysis verifies that the privilege level in the shell exec settings does not exceed the maximum enable privilege. Custom parameters defined in the shell exec are not supported in ACS 5.8.1. Invalid idle time and timeout values are reported in the Analysis report.
The shell exec parameters for all the users are collected. If a parameter exists for at least one of the users being migrated, it is migrated as a user attribute. In ACS 4.x, if the shell exec value is defined for each user being migrated, in ACS 5.8.1, this value is set in a user attribute associated with the user in ACS 5.8.1. If the attribute is not defined in ACS 4.x, it is left blank in ACS 5.8.1.
The Shell attribute has a fixed name. You cannot create Shell attributes with a name prefix per ACS 4.x instance. Also, you cannot merge the Shell attributes data (values) from multiple ACS 4.x instances.
For example, you cannot add only the attribute Timeout:123 to user jeff, if the user already exists in ACS 5.8.1 and that shell attribute is not defined on the user.
The association between a user and the shell attribute is preserved regardless of the run (current or previous migration) when the shell attribute definition is migrated.
A user with a unique username (that is added in the current run) is associated with a shell attribute that already exists in the ACS 5.8.1 identity dictionary (that was migrated in the previous run of the migration).
If the same user exists in another ACS 4.x instance, the user is not imported, but the user shell attributes are migrated with null values. There is a single set of internal user shell attributes that applies to all users. In ACS 5.8.1, every user shell attribute that gets added to the dictionary also gets added to all the users.
User Group
In ACS 5.8.1, the identity group is equivalent to the user groups. However, each identity group is purely a logical container to group sets of users for the purposes of policy processing and selection in rules conditions.
The user group names are migrated and merged into the identity group hierarchy. A new node is created beneath the root node of the identity hierarchy and under this node, all the migrated user groups are placed in a flat structure. You are prompted to define the name of this node. A default name is also presented.
In ACS 4.x, 500 user groups are created by default, and these groups can be edited by the administrator. In ACS 5.8.1, only the user groups that are being utilized and referenced from user or MAC definitions are migrated.
To keep the association between the users and user groups (the identity groups), you must first export (and import) the user groups, followed by the internal users with associations to those user groups.
Analysis and Export
A user group that does not contain any internal users or MAC definitions is not exported. It is reported to the administrator that such user groups have not been migrated. In addition, some special characters are not allowed in the group name during export. This will be reported in the Analysis report and the export will not proceed if the following characters are used in the group name:
Import
During import, a new identity group node, with a name defined in the User Preferences, is created under the root node of the identity group hierarchy. The default name is Migrated Group. All migrated user groups are created in a flat hierarchy under this newly created node.
In ACS 4.x, each user was associated to a single group. To keep the association between the users and user groups (the identity group) the user groups are imported first, followed by the internal users with associations to the user group.
Multiple-Instance Support
In ACS 5.8.1, you cannot define two identity groups with the same name on one hierarchy root. However, you can define them on different hierarchies.
For example, you can define two groups named Engineers, one on the root NY and the other on the root SJ. The multiple-instance support allows you to select one of the following options to migrate the groups:
■![]() Define a different root for each instance and import all the user groups of the instance under the instance root.
Define a different root for each instance and import all the user groups of the instance under the instance root.
■![]() Define one root for all the migrated groups. The Migration Utility adds only unique groups to the root. Groups that already exist are reported as duplicates and are not imported. However, the ID of the already exiting user group is retrieved for association purposes.
Define one root for all the migrated groups. The Migration Utility adds only unique groups to the root. Groups that already exist are reported as duplicates and are not imported. However, the ID of the already exiting user group is retrieved for association purposes.
To select either of the options, go to User Preferences. The association between user group and users is maintained according to the logic of that selection.
For example, the user john (unique username) is associated to the group Management, which was migrated from a previous run of an ACS 4.x instance. On any option selected, john is associated to the group Management, but Management is defined in the root All or in the specific root Engineers.
User Group Policy Components
In ACS 4.x, most of the policy-related authorization data is embedded within the user group definitions, whereas in ACS 5.8.1, this data is defined as shared objects.
Data is migrated only from the groups that are in use. The following data is extracted from the group data:
■![]() TACACS+ shell command authorization set is migrated to a command set.
TACACS+ shell command authorization set is migrated to a command set.
■![]() TACACS+ shell exec (+max privilege level) is migrated to a shell profile.
TACACS+ shell exec (+max privilege level) is migrated to a shell profile.
Group Command Set
The names of the command sets extracted from the users are stored in a user attribute. No similar action is performed when the data is extracted from the user groups. The multiple-instance support for the groups’ command sets is similar to the users’ command sets.
Note: Group command sets are migrated only when the groups are migrated.
Group Shell Exec
Table 12 shows the mapping of attributes from the group data to attributes in the shell profile. Each field in a shell profile has a flag to indicate whether the field is present in the profile. If a field is not enabled in the group record, it is marked as not present in the shell profile.
|
|
|
|
|---|---|---|
Analysis is performed on all groups that are determined to be in use and that are associated either with users or MAC addresses. The analysis verifies that the following values entered in ACS 4.x are in a valid range for the corresponding ACS 5.8.1 object:
In ACS 5.8.1, you can include wildcards in the MAC address, but wildcards can be used only with a specific ObjectID for example, "00-00-00-*. The following wildcard format is not supported: 11-11-11-11-11-*
The analysis also verifies that the new default privilege level value is not higher than the maximum value. If a group to be migrated has custom attributes defined, it is not migrated to ACS 5.8.1, and a warning is displayed.
The following user settings are used during import of the group shell exec:
■![]() Shell profile name format. Options available are:
Shell profile name format. Options available are:
■![]() Prefix to be added for consolidated objects in addition to the prefix above. The default is an empty string.
Prefix to be added for consolidated objects in addition to the prefix above. The default is an empty string.
The import process is performed for each shell exec that is not consolidated into another object. The name of the ACS 5.8.1 object is determined based on the user settings and the created shell profile.
Note: Group shell attributes are migrated only when the group is migrated.
Group Shell attributes are migrated to shared shell profiles and the name is generated from the group name.
In ACS 5.8.1, you cannot define two shell profiles with the same name. However, you can create shell profiles with a name prefix per ACS 4.x instance, and thus you can add a shell profile for each instance. With multiple-instance support, you can select one of the following options to migrate the shell profiles:
■![]() Define a different name prefix for each instance and import all the shell profiles with different names.
Define a different name prefix for each instance and import all the shell profiles with different names.
■![]() Do not define a prefix. This results in a uniquely named shell profile migration. Shell profiles that already exist are reported as duplicates.
Do not define a prefix. This results in a uniquely named shell profile migration. Shell profiles that already exist are reported as duplicates.
MAC Addresses and Internal Hosts
In ACS 4.x, support for authentication based on MAC address is as follows:
■![]() Define the MAC address as an internal username with a Password Authentication Protocol (PAP) password that is identical to the username. The user is migrated into the internal user database and there is no need for additional support for MAC addresses.
Define the MAC address as an internal username with a Password Authentication Protocol (PAP) password that is identical to the username. The user is migrated into the internal user database and there is no need for additional support for MAC addresses.
■![]() Define the MAC address in the NAP table as part of the authentication policy. Within the authentication policy, you can configure to authenticate the MAC address with the ACS internal database. You can then provide a list of MAC addresses and a corresponding identity. The MAC addresses are migrated to the corresponding records in the internal host’s database.
Define the MAC address in the NAP table as part of the authentication policy. Within the authentication policy, you can configure to authenticate the MAC address with the ACS internal database. You can then provide a list of MAC addresses and a corresponding identity. The MAC addresses are migrated to the corresponding records in the internal host’s database.
In ACS 5.8.1, you can define additional attributes to be associated with the hosts, as is done for the users. However, in ACS 4.x, there is no additional data associated with the MAC definitions, and hence no additional attributes are required for migration. However, the association with the identity group is retained.
Table 13 shows the data mapping between ACS 4.x and ACS 5.8.1 for MAC addresses and internal hosts.
You can enter MAC addresses in multiple formats, but they are always stored in 12-34-56-78-90-AB format. However, in ACS 4.x it is possible to include a wildcard in the address; for example, 12-34-56-78*.
In ACS 5.8.1, you can include a wildcard in the MAC address. You can migrate hosts with wildcards that are specified only after the first three octets of the MAC address, along with its associated user group. Hosts without wildcards can also be migrated.
NAP A has the following MAC addresses: 1-2-3-4-5-6 Group 10.
NAP B has the following MAC address: 1-2-4-* Group 24.
Here, the NAP A MAC address 1-2-3-4-5-6 is migrated along with its associated to group 10. Also, NAP B MAC address 1-2-4-* is migrated along with its associated group 24.
In ACS 4.x, duplicate MACs are identified based on the MAC address and are reported in the Import report. Only unique MAC addresses are migrated. There is no support for the name prefix. Unique MAC addresses that are associated to a user group are migrated.
The association is preserved, regardless of whether or not the user group itself was migrated in the same instance as the MAC address or in a previous instance.
Shared Shell Command Authorization Sets
In ACS 4.x, the shell command authorization set can be defined as shared objects, as part of the device administration. Such objects are migrated to the command sets. The name and the description of each object is the same as in ACS 4.x.
Table 14 shows the data mapping between ACS 4.x and ACS 5.8.1 for shared shell command authorization sets.
Some special characters are not allowed in the shell command authorization set during export. It will be reported in the Analysis report if the following characters are used in the device name:
In ACS 5.8.1, you cannot define two command sets with the same name. However, you can create them with a name prefix per ACS 4.x instance, and thus you can add a command set for each instance. Thus, with the multiple-instance support, you can select one of the following options to migrate the shared command sets:
■![]() Define a different name prefix for each ACS 4.x instance and import all the command sets with different names.
Define a different name prefix for each ACS 4.x instance and import all the command sets with different names.
■![]() Do not define a prefix, resulting in a uniquely named command set migration. Command sets that already exist are reported as duplicates.
Do not define a prefix, resulting in a uniquely named command set migration. Command sets that already exist are reported as duplicates.
Shared DACL Objects
In ACS 4.x, a shared downloadable access control list (DACL) can be defined as a shared object to be referenced from the application. A shared DACL consists of a set of ACL contents, where each ACL is associated with a specific Network Access Filtering (NAF) selection. When the object is referenced, the actual ACL that is utilized depends on the NAF condition that matches first.
ACS 5.8.1 contains the authorization policy that results in the selection of a DACL from an authorization profile. Therefore, each ACL that is contained within an ACS 4.x shared DACL is mapped to a separate DACL in ACS 5.8.1.
Data Mapping
Table 15 shows the data mapping between ACS 4.x and ACS 5.8.1 for shared DACL objects.
Analysis and Export
The following configuration options are available and affect the analysis and the import behavior:
■![]() The name of the object created for each ACL can be either a combination of the DACL name and the ACL name or just the ACL name.
The name of the object created for each ACL can be either a combination of the DACL name and the ACL name or just the ACL name.
■![]() In addition to the previously mentioned name, you can also add a prefix.
In addition to the previously mentioned name, you can also add a prefix.
The created object name is analyzed and the following analysis issues, if present, are reported:
■![]() If the object name exceeds 32 characters, the report shows that the final object name is truncated to 32 characters.
If the object name exceeds 32 characters, the report shows that the final object name is truncated to 32 characters.
■![]() All the object names that contain the following invalid characters:
All the object names that contain the following invalid characters:
The invalid characters may come from the shared DACL part or the ACL part of the name. If the DACL name contains invalid characters, the report shows all the combinations of the ACL.
Note: If the ACL name is used, multiple ACL records could be created on ACS 5.8.1 with the same name. You should utilize this option only if you are sure that the ACL name is unique, or there are duplicate ACLs and you want to import only one.
Import
You cannot create multiple DACLs with the same name. If you do so, it is reported in the Import report. This occurs when you use the ACL option for the DACL name to migrate multiple shared ACLs that contain the same ACL.
Multiple-Instance Support
In ACS 5.8.1, you cannot define two DACLs with the same name. However, you can create DACLs with a name prefix per ACS 4.x instance and thus add DACLs for each instance. With the multiple-instance support, you can select one of the following options to migrate the DACLs:
■![]() Define a different name prefix for each instance and import all the DACLs with different names.
Define a different name prefix for each instance and import all the DACLs with different names.
■![]() Do not define a prefix. Only uniquely named DACLs are migrated. DACLs that already exist are reported as duplicates.
Do not define a prefix. Only uniquely named DACLs are migrated. DACLs that already exist are reported as duplicates.
Shared RACs
In ACS 4.x, you can define a shared profile component that contains RADIUS Authorization Components (RACs) and defines a set of RADIUS attributes and values that are to be returned in an authorization response. These shared objects map the direction to the authorization profiles that are defined in ACS 5.8.1.
In ACS 4.x, an attribute is identified in the GUI as a combination of the vendor name and the attribute name. In ACS 5.8.1, it is defined as a combination of the dictionary and attribute name. Internally, the vendor or dictionary and attribute are identified by IDs that are, in turn, the values that are used while forming the RADIUS response.
Data Mapping
Table 16 shows the data mapping between ACS 4.x and ACS 5.8.1 for the shared RACs.
Analysis and Export
Some special characters are not allowed in the shared RAC during export. It will be reported in the Analysis report if the following characters are used in the shared RAC:
In ACS 4.x, the Microsoft vendor attributes can be included in a RAC, but values cannot be set, and a fixed string of <Value set by ACS> is displayed. The following Microsoft vendor attributes can be selected:
In ACS 5.8.1, you cannot configure these attributes, but they are added to the profile as required, depending on the type of authentication being performed and the corresponding required response. If these attributes are defined in ACS 4.x, the Analysis report states that they have not been migrated, although the RAC that contains them was migrated.
Import
You can optionally configure a prefix to be added to the name of all the migrated RACs. In ACS 5.8.1, attributes are included in an authorization profile if they meet the following conditions for the relevant properties:
The import process verifies that these conditions are met for all the attributes to be included in a profile, and any discrepancy is reported in the Import report.
Multiple-Instance Support
In ACS 5.8.1, you cannot define two RACs with the same name. However, you can create RACs with a name prefix per ACS 4.x instance and add RACs for each instance. With multiple-instance support, you can select one of the following options to migrate the RACs:
■![]() Define a different name prefix for each instance, and import all the RACs with different names.
Define a different name prefix for each instance, and import all the RACs with different names.
■![]() Do not define a prefix. Only uniquely named RACs are migrated. RACs that already exist are reported as duplicates.
Do not define a prefix. Only uniquely named RACs are migrated. RACs that already exist are reported as duplicates.
RADIUS VSAs
The dictionary and its content (the attribute definitions) are an important and core part of ACS 4.x. The dictionary defines the attributes specified by the IETF for the RADIUS protocol, and it is augmented by the vendor-specific attributes (VSAs) defined by different device vendors. VSAs are allocated a structured name space within the value of one of the IETF attributes (Attribute 26).
The majority of the used attributes are predefined in the dictionaries shipped with ACS. However, as vendors expand the capabilities of their devices, new VSAs are added.
If you do not wish to wait for the next release of ACS to get the updated dictionaries, you can use the Command Line Utility to define new dictionary slots for the new vendors, to augment the attributes of an already existing vendor in the dictionary, or to update already defined VSAs (for example, with additional enumeration values).
During migration, the dictionary is iterated to identify the missing attributes in ACS 5.8.1 for each vendor. There are two possible cases during this identification process:
■![]() If the vendor does not exist in the ACS 5.8.1 dictionary, all the vendor attributes are migrated.
If the vendor does not exist in the ACS 5.8.1 dictionary, all the vendor attributes are migrated.
■![]() If the vendor exists in the ACS 5.8.1 dictionary, only attributes that are not defined in ACS 5.8.1 are migrated.
If the vendor exists in the ACS 5.8.1 dictionary, only attributes that are not defined in ACS 5.8.1 are migrated.
For the Cisco Airespace attribute Aire-QoS-Level(2), the description of the enumerated values is different between ACS 4.1.x and ACS 5. Since the numeric value gets migrated, there is no difference in the response sent when using RACs that include this attribute and the same numeric value will be sent in the response. However, the string presented in the ACS GUI for this value is different.
For example, in ACS 4.1.x the value of 1 is displayed as Silver, whereas in ACS 5.8.1 this is displayed as Gold.
Table 17 shows the mapping of Aire-QoS-Level (2) values between ACS 4.1.x and ACS 5.8.1.
|
|
|
|---|---|
Description of the enumerated values of Cisco Airespace attribute Aire-QoS-Level(2), between ACS 4.2 and ACS 5.8.1 is the same.
Data Mapping
Table 18 shows the data field mapping between ACS 4.x and ACS 5.8.1 for RADIUS vendors.
Table 19 shows the data field mapping between ACS 4.x and ACS 5.8.1 for RADIUS VSAs.
Analysis and Export
The analysis phase for the RADIUS VSAs focuses on merging the dictionary content of ACS 4.x with the dictionary content of ACS 5.8.1. There are two cases for analysis:
■![]() Generally, for ACS 4.x supported vendors, the dictionary in ACS 5.8.1 is more up-to-date. However, you may have modified some ACS 4.x vendor dictionaries to include new VSAs, or to modify the existing VSAs (for example, new enumeration values). The migration behavior is as follows:
Generally, for ACS 4.x supported vendors, the dictionary in ACS 5.8.1 is more up-to-date. However, you may have modified some ACS 4.x vendor dictionaries to include new VSAs, or to modify the existing VSAs (for example, new enumeration values). The migration behavior is as follows:
–![]() An attribute defined in ACS 5.8.1 is not altered during migration. A warning is displayed for such attributes.
An attribute defined in ACS 5.8.1 is not altered during migration. A warning is displayed for such attributes.
–![]() An attribute not defined in ACS 5.8.1, but present in ACS 4.x, is migrated.
An attribute not defined in ACS 5.8.1, but present in ACS 4.x, is migrated.
■![]() The vendors that are imported by you into ACS 4.x, and are not present in ACS 5.8.1, are migrated without any analysis warning.
The vendors that are imported by you into ACS 4.x, and are not present in ACS 5.8.1, are migrated without any analysis warning.
Note: Difference between ACS 4.x and ACS 5.8.1 VSA attributes (profile, name, type) are reported in the Analysis report.
Import
EAP-Fast Master Keys and the Authority ID
In ACS 5.8.1, you can preserve support for all objects (users or devices) that authenticated on ACS 4.x. Therefore, all the master keys and the authority ID from ACS 4.x are migrated.
The master keys in ACS 4.x have a schema that is different from that of ACS 5.8.1, and they are migrated to different IM objects. ACS 4.x stores the authority ID per node, whereas ACS 5.8.1 stores the authority ID only in the primary database and then applies it to the entire deployment.
Data Mapping
Table 20 shows the data mapping between ACS 4.x and ACS 5.8.1 for EAP-FAST master keys and the authority ID.
The expiration time is calculated as follows:
1.![]() From the list of keys in the database, the tail key is checked to determine whether or not it has expired.
From the list of keys in the database, the tail key is checked to determine whether or not it has expired.
2.![]() Key creation time is saved as KeyCtime for the current key.
Key creation time is saved as KeyCtime for the current key.
3.![]() Current time is calculated by Calling Time(NULL).
Current time is calculated by Calling Time(NULL).
4.![]() TTL is taken for the key stored in AuthenConfig > EAP-FAST.
TTL is taken for the key stored in AuthenConfig > EAP-FAST.
5.![]() The Expiration time is calculated by adding the Current time and the Retired master key TTL.
The Expiration time is calculated by adding the Current time and the Retired master key TTL.
The master key TTL unit is represented as follows:
Minutes: 1, Hours: 2, Days: 3, Weeks: 4, Months: 5, Years: 6
For example, if the active master key TTL is selected as 1 month, it equates to 1 * 30 * 24 * 3600.
Analysis and Export
Import
In ACS 5.8.1, the objects are added to the Master Key table and are not available through the GUI. The authority ID is migrated to the EAP-FAST global settings.
Multiple-Instance Support
In ACS 5.8.1, you cannot define two master keys with the same ID; therefore, only unique master keys are migrated from multiple instances of ACS 4.x.
In ACS 5.8.1, the authority ID is stored as a global EAP setting and not stored per node or instance. Hence, it can be migrated only from one instance.
Analysis and Export of ACS 4.x Data
Choose option 1 in the Migration Utility to run AnalyzeAndExport. See This utility migrates data from ACS 4.x to ACS 5. You can migrate directly from the following ACS versions:. The Analyze and Export phase runs on the ACS 4.x migration machine by using data restored from the backup of the ACS 4.x source machine. The AnalyzeAndExport Summary Report lists the total:
■![]() Issues reported for each object.
Issues reported for each object.
■![]() Objects that can be migrated.
Objects that can be migrated.
■![]() Information on issues for each object.
Information on issues for each object.
■![]() Data to be consolidated. See Consolidating Data.
Data to be consolidated. See Consolidating Data.
The Analyze and Export phase can be run multiple times to make configuration changes between analysis cycles. For example, you might have overlapping IP addresses for network devices. You can use the ACS 4.x application to correct this problem. After you correct the problem, you can rerun the Analyze and Export phase and proceed to the Import phase. See Overlapping IP Addresses.
■![]() Issues Resulting from the Analysis and Export Phase
Issues Resulting from the Analysis and Export Phase
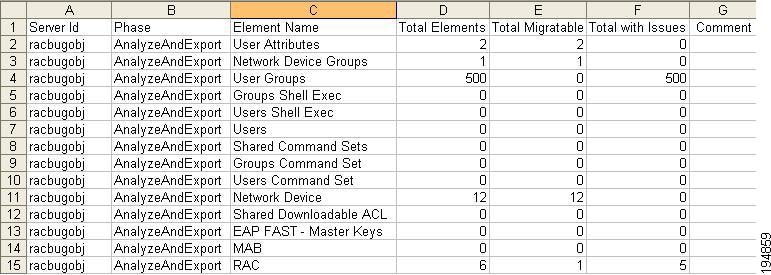
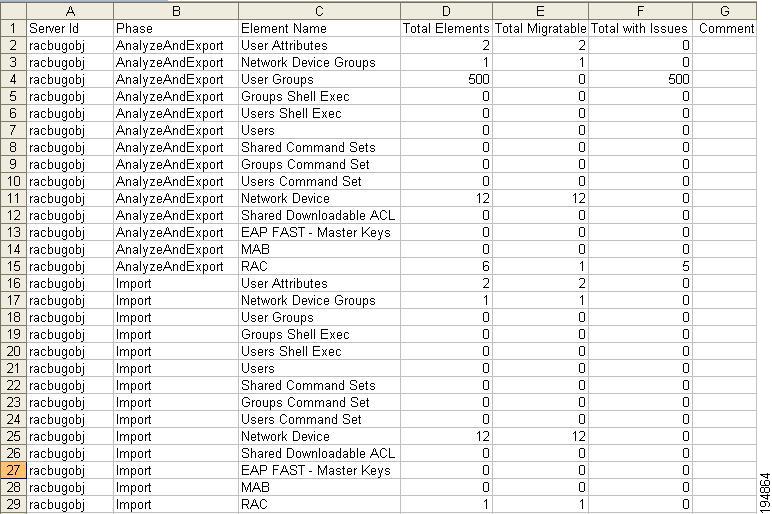
ExampleAnalyzeAndExport Summary Report shows a sample summary report for the Analyze and Export phase. This example shows the report generated if you select option 3- AllDevicesObjects, in the Migration Utility.
See ACS 5.8.1 Attribute Support in the Migration Utility for a list of the attributes that are migrated.
Consolidating Data
The consolidation process occurs in the Analysis and Export phase and:
■![]() Analyzes the created shared objects.
Analyzes the created shared objects.
■![]() Identifies the objects that are identical.
Identifies the objects that are identical.
■![]() Ensures that duplicate ACS 4.x objects are collapsed to a single object, which is migrated to ACS 5.8.1. This object can then be referenced by ACS 5.8.1 policies.
Ensures that duplicate ACS 4.x objects are collapsed to a single object, which is migrated to ACS 5.8.1. This object can then be referenced by ACS 5.8.1 policies.
For example, the Analysis report might show multiple command sets that appear to be different, but are actually the same command set. This might be because of the command set shortcuts, such as show or sho. In ACS 5.8.1, you can define polices such that they incorporate the migrated command set information. See the User Guide for Cisco Secure Access Control System 5.8.1 for more details on ACS 5.8.1 policies.
–![]() User and user group command set into a command set profile.
User and user group command set into a command set profile.
Issues Resulting from the Analysis and Export Phase
Not all data entities can migrate from ACS 4.x to ACS 5.8.1. The Analysis and Export phase might reveal issues such as overlapping IP addresses for the network devices.
Another issue is that the ACS 4.x IP address network device definitions could include wildcards and ranges. ACS 5.8.1 uses a standard subnet mask representation. Therefore, the network device definitions might not be compatible.
The Analysis and Export reports detail these issues. You can address these issues in the ACS 4.x application and subsequently rerun AnalyzeAndExport. You can rerun this process as many times as required. After you fix the issues, you can import the exported data to the ACS 5.8.1 machine.
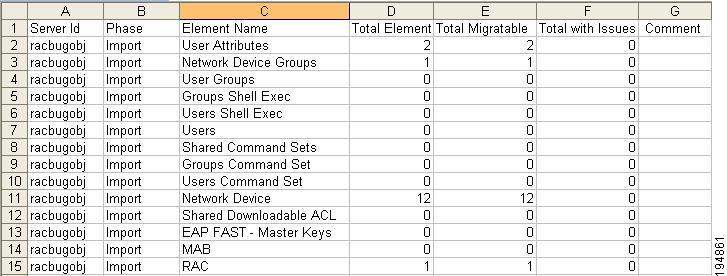
Importing the ACS 4.x Data to ACS 5.8.1
Choose option 2 in the Migration Utility to run Import. See This utility migrates data from ACS 4.x to ACS 5. You can migrate directly from the following ACS versions:. This phase imports the ACS 4.x data export file created in the Export phase.
The import process can take a long time if you migrate data from a large database.
Note: If the ACS 5.8.1 import fails, restore your ACS 5.8.1 database.
ExampleSample Progress Report for the Import Phase shows a sample progress report from the Import phase. This phase generates two reports:
■![]() ExampleImport Summary Report shows the Import Summary Report.
ExampleImport Summary Report shows the Import Summary Report.
■![]() ExampleImport Report shows the Import Report.
ExampleImport Report shows the Import Report.
Migrating Multiple Instances
Choose option 4 in the Migration Utility to import another ACS 4.x instance. See This utility migrates data from ACS 4.x to ACS 5. You can migrate directly from the following ACS versions:. You can import multiple ACS 4.x instances to ACS 5.8.1. ExampleImporting Multiple Instances shows the prompts that appear if you decide to migrate multiple instances.
After you enter the server ID or hostname of another ACS 4.x instance, the whole migration process starts again. In this way, you can migrate several ACS 4.x instances to ACS 5.8.1.
Migration Impact on Memory and Performance
Data export is performed from the ACS 4.x migration server and not directly from the ACS 4.x production server or source server. Therefore, the migration has no impact on the performance of the ACS 4.x production server. The Migration Utility can be run on a standard PC environment.
During the import of the migrated data, the ACS 5.8.1 server should be idle and should not be processing any AAA requests.
Printing Reports and Report Types
Choose option 3 in the Migration Utility to print full reports and summary reports to a CSV file. See This utility migrates data from ACS 4.x to ACS 5. You can migrate directly from the following ACS versions:. The config folder in the migration directory contains the Migration Utility reports. In the config folder, a new folder with the same name as the server ID is created for each
ACS 4.x server that you migrate.
For example, if the server ID is test1, a folder test1 is created under the config folder and it contains the Migration Utility reports. The report name has the server ID attached. This section contains:
■![]() Analyze and Export Summary Report
Analyze and Export Summary Report
■![]() Analyze and Export Full Report
Analyze and Export Full Report
Table 21 lists the migration phases and the reports that are generated in each phase.
|
|
|
|---|---|
Table 22 describes the Migration Utility reports.
Analyze and Export Summary Report
Analyze and Export Summary Report shows the Analyze and Export Summary Report. Table 23 contains the Analyze and Export Summary Report column definitions.
Figure 1 Analyze and Export Summary Report
|
|
|
|---|---|
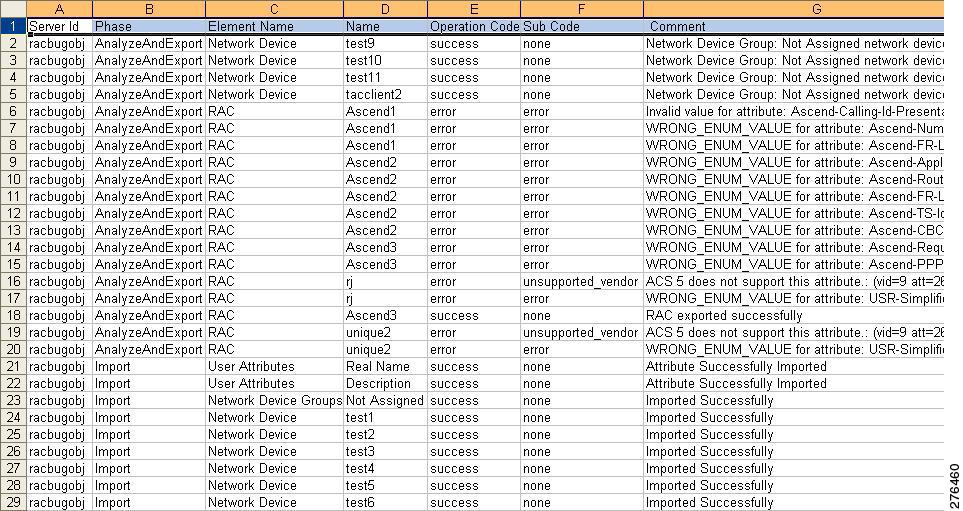
Analyze and Export Full Report
Analyze and Export Full Report shows the Analyze and Export Full Report. Table 24 contains the Analyze and Export Full Report column definitions.
Figure 2 Analyze and Export Full Report
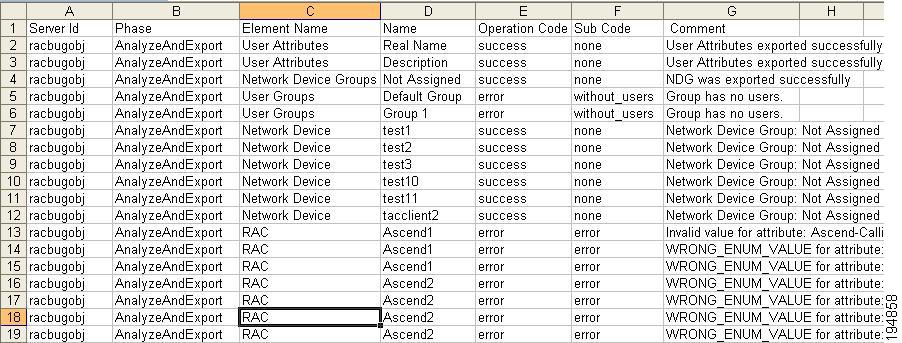
|
|
|
|---|---|
Status of the Analyze and Export phase. Valid values are success, error, and info (informational message). |
|
Import Summary Report
Import Summary Report shows the Import Summary Report. Table 25 contains the Import Summary Report column definitions.
Figure 3 Import Summary Report
|
|
|
|---|---|
Import Full Report
Import Full Report shows the Import Full Report. Table 26 contains the Import Full Report column definitions.
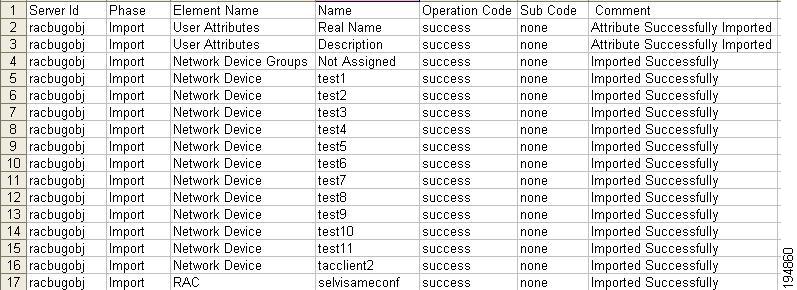
|
|
|
|---|---|
Indicates if the operation was a success or if an error occurred. |
|
Validating Import
After the import phase is complete, you must manually analyze the Import Summary Report. This lists:
■![]() The total number of objects to be migrated.
The total number of objects to be migrated.
■![]() The number of objects that successfully migrated.
The number of objects that successfully migrated.
■![]() The number of objects that failed to migrate.
The number of objects that failed to migrate.
You can check the Import Full Report for information on the objects that did not migrate. This lists:
If any of the ACS 4.x objects are not migrated, you must:
1.![]() Manually add the objects that are not migrated, or address these issues in the ACS 4.x application.
Manually add the objects that are not migrated, or address these issues in the ACS 4.x application.
2.![]() Rerun the Analyze and Export phase.
Rerun the Analyze and Export phase.
3.![]() Restore the ACS 5.8.1 database to its previous state (before import).
Restore the ACS 5.8.1 database to its previous state (before import).
Note: To verify that migration is complete, analyze the Import Summary Report. If the report indicates that all objects have migrated successfully, migration is complete.
Summary Report
Summary Report shows the Summary Report statistics for all migration phases. Table 27 contains the Summary Report column definitions.
|
|
|
|---|---|
Full Report
Full Report shows the Full Report statistics for all migration phases. Table 28 contains the Full Report column definitions.
|
|
|
|---|---|
Indicates if the operation was a success or if an error occurred. |
|
Errors and Exception Handling
Any errors during the Analysis and Export or Import phases are reported in the respective reports. For more information on the migration errors and the steps to resolve them, seeResolving Migration Issues.
For the error and informational messages that may appear during the migration of various ACS objects, seeMigration Utility Messages.
Confirming the Migration
Log into your ACS 5.8.1 target machine to confirm that you successfully migrated the ACS 4.x elements. In the migration process, the following ACS elements that were defined in ACS 4.x are migrated to
ACS 5.8.1:
To access the ACS 4.x objects, follow the instructions in the User Guide for Cisco Secure Access Control Server 4.2. To access the ACS 5.8.1 objects, follow the instructions in the User Guide for Cisco Secure Access Control System 5.8.1.
The following sections provide information on confirming the migration of:
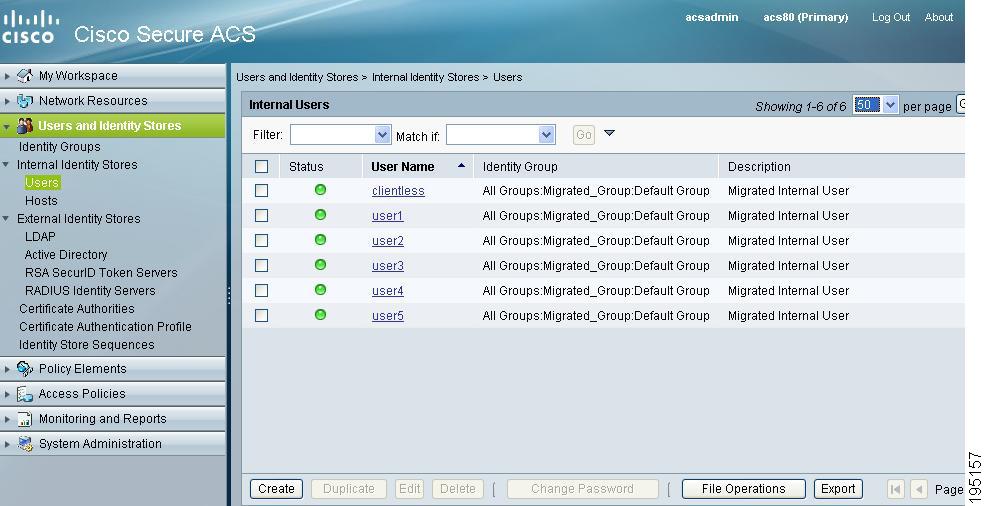
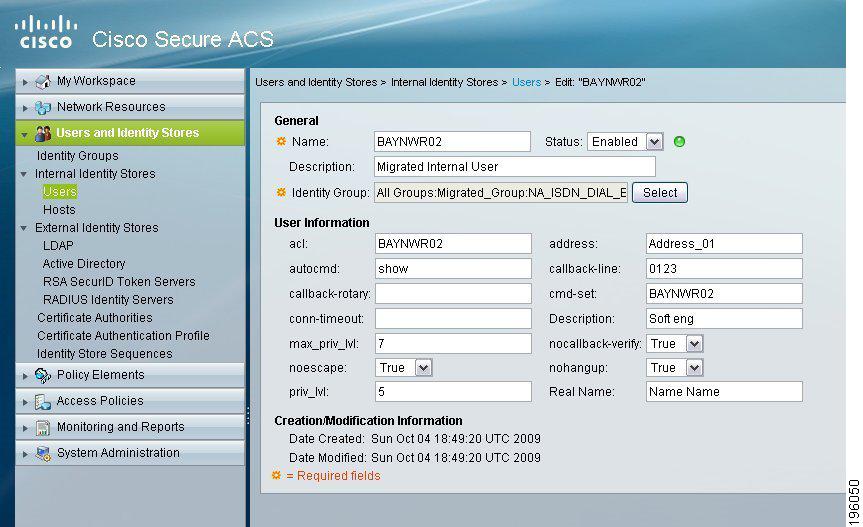
Users and User Groups
Figure 7 shows the users and user groups in ACS 4.x, and Figure 8 shows the users and user groups migrated to ACS 5.8.1. Choose Users and Identity Stores > Internal Identity Stores > Users to access the migrated users and user groups.
Figure 7 Users and User Groups Defined in ACS 4.x
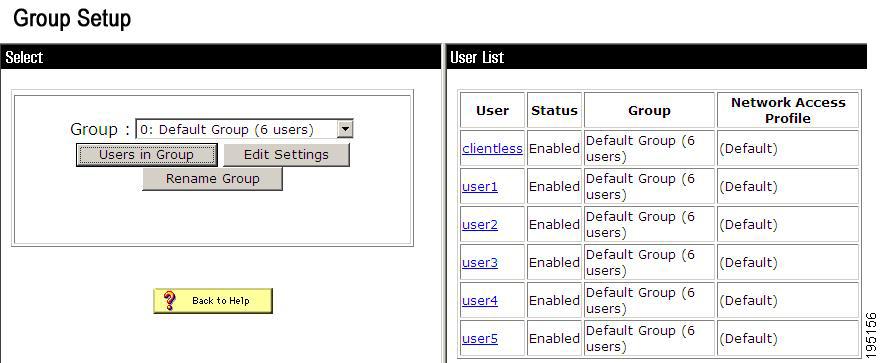
Figure 8 Users and User Groups Migrated to ACS 5.8.1
Command Shell Migration
Figure 9 shows the command shell attributes in ACS 4.x, and Figure 10 shows the group shell attributes migrated to ACS 5.8.1 as shell profiles.
Choose Policy Elements > Authorization and Permissions > Device Administration > Shell Profiles and click Edit to access the migrated group shell attributes.
Choose User and Identity Stores > Internal Identity Stores > Users and click on any user to access the migrated user shell attributes. Figure 11 shows the user shell attributes migrated to ACS 5.8.1.
Figure 9 Command Shell Attributes Defined in ACS 4.x
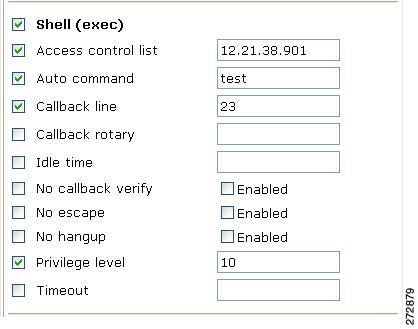
Figure 10 Group Shell Attributes Migrated to ACS 5.8.1
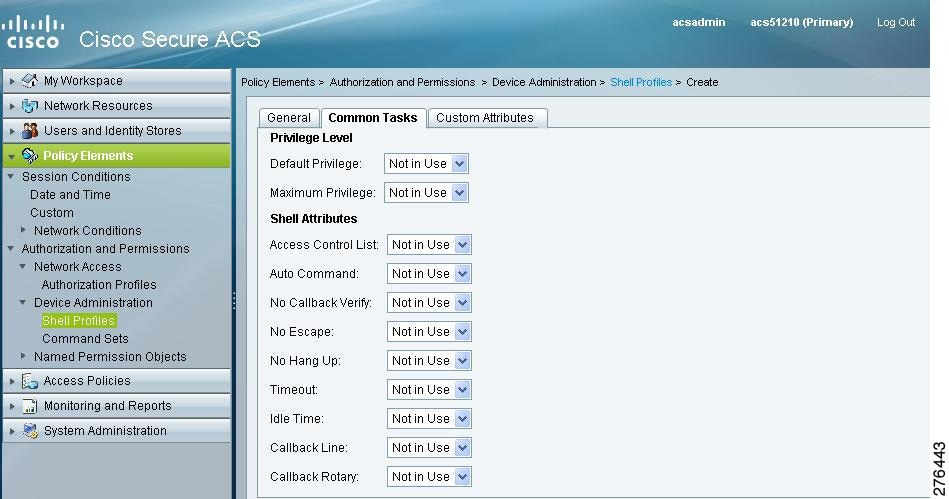
Figure 11 User Shell Attribute Migrated to ACS 5.8.1
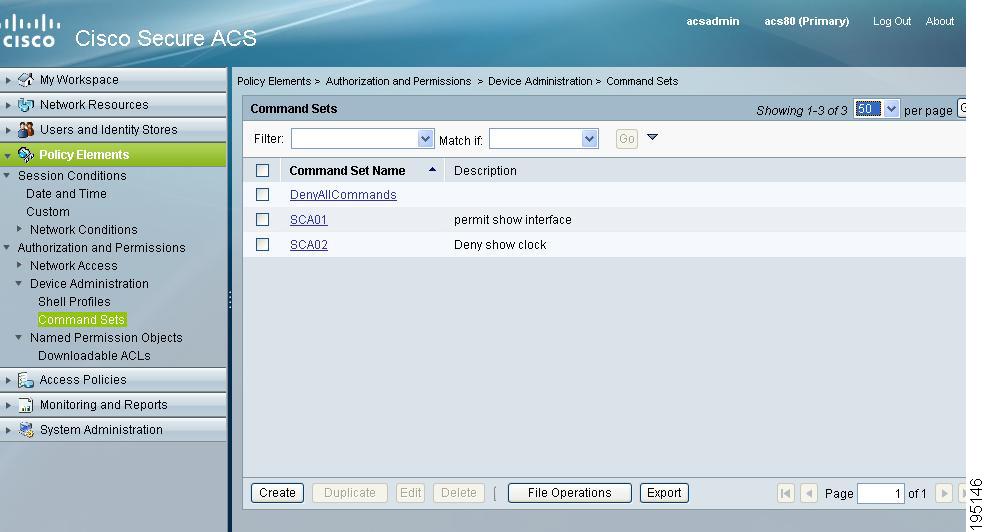
Command Set Migration
Figure 12 shows the command set in ACS 4.x, and Figure 13 shows the command set migrated to ACS 5.8.1. Choose Policy Elements > Device Administration > Command Sets to access the migrated command set attributes.
Figure 12 Command Set Defined in ACS 4.x
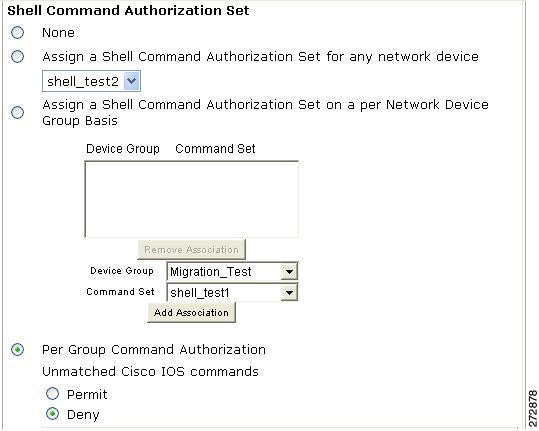
Figure 13 Command Set Migrated to ACS 5.8.1
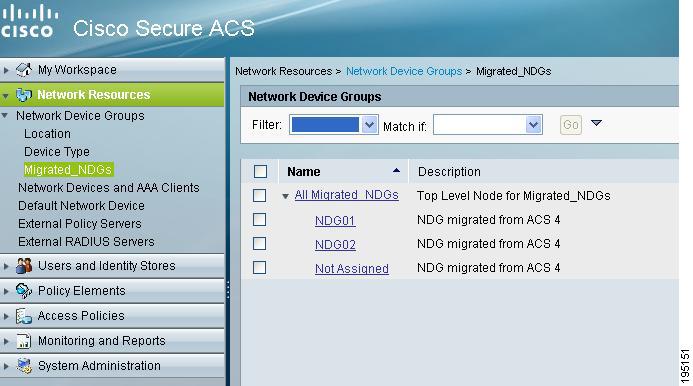
NDG Migration
Figure 14 shows the NDGs in ACS 4.x, and Figure 15 shows the NDGs migrated to ACS 5.8.1. Choose Network Resources > Network Device Groups to access the migrated NDGs.
Figure 14 NDGs Defined in ACS 4.x
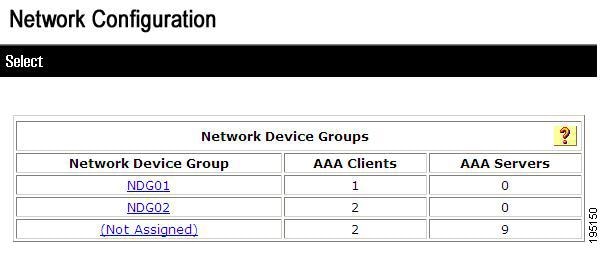
Figure 15 NDGs Migrated to ACS 5.8.1
Network Device Migration
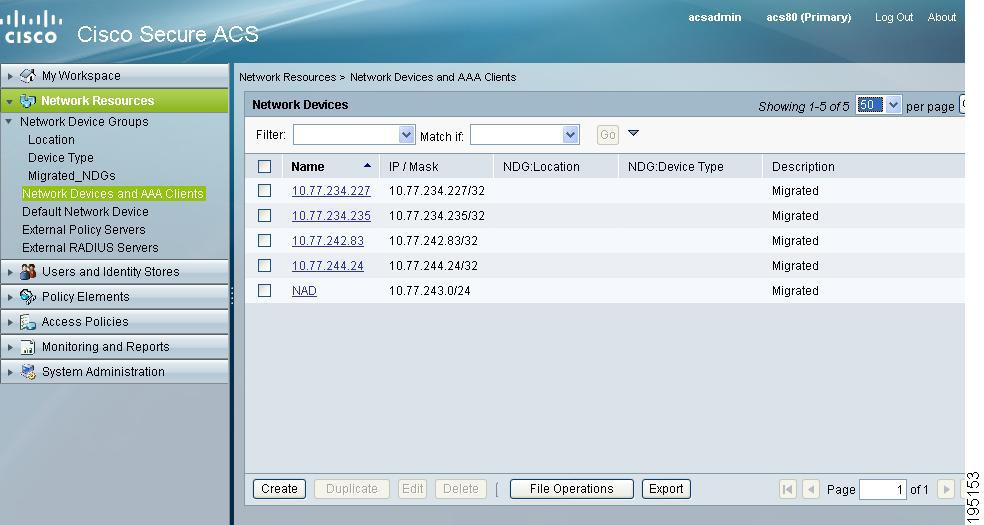
Figure 16 shows the network devices in ACS 4.x, and Figure 17 shows the network devices migrated to ACS 5.8.1. Choose Network Resources > Network Devices and AAA Clients to access the migrated network devices.
Figure 16 Network Devices Defined in ACS 4.x
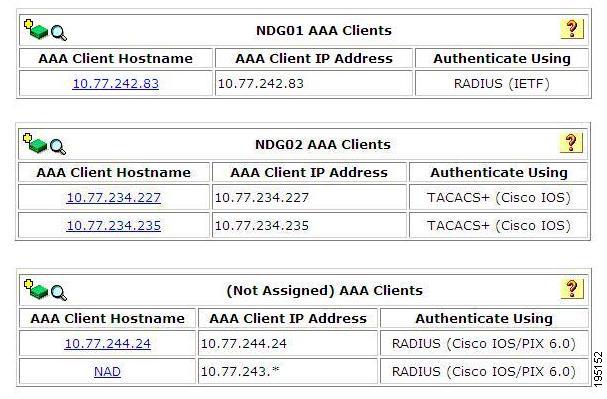
Figure 17 Network Devices Migrated to ACS 5.8.1
DACL Migration
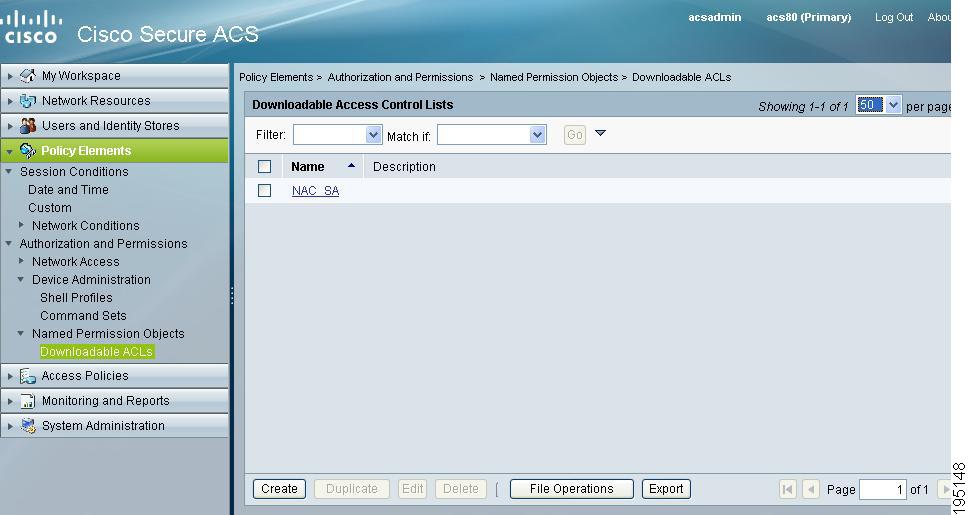
Figure 18 shows the downloadable access control lists (DACLs) in ACS 4.x, and Figure 19 shows the DACLs migrated to ACS 5.8.1.
Choose Policy Elements > Authorization and Permissions > Named Permission Objects > Downloadable ACLs to access the migrated DACLs.
Figure 18 DACLs Defined in ACS 4.x
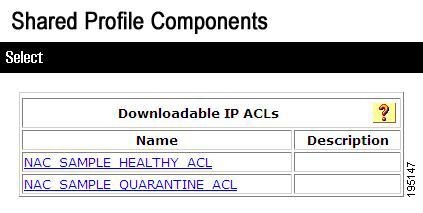
Figure 19 DACLs Migrated to ACS 5.8.1
MAB Migration
Figure 20 shows MAC Authentication Bypass (MAB) defined in ACS 4.x, and Figure 21 shows MAB migrated to ACS 5.8.1.
Choose Users and Identity Stores > Internal Identity Stores > Hosts and click Create to access the migrated MABs.
Figure 20 MAB Defined in ACS 4.x
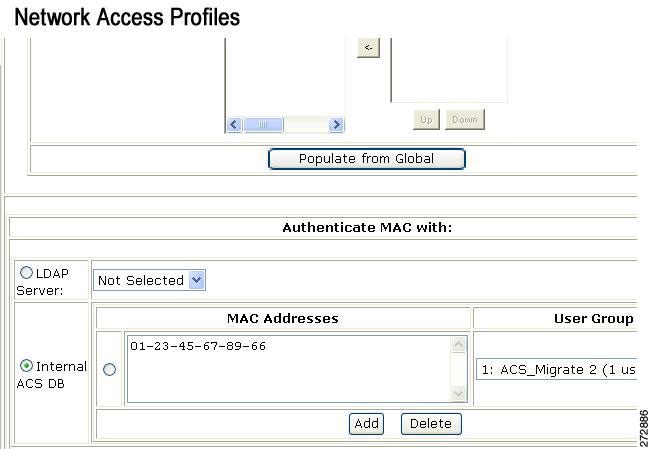
Figure 21 MAB Migrated to ACS 5.8.1

Shared RACs
Figure 22 shows shared RADIUS Authorization Components (RACs) defined in ACS 4.x, and Figure 23 shows shared RACs migrated to ACS 5.8.1.
Choose Policy Elements > Authorization and Permissions > Network Access > Authorization Profiles to access the migrated RACs.
Figure 22 Shared RACs Defined in ACS 4.x
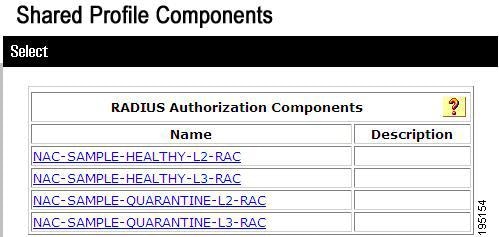
Figure 23 Shared RACs Migrated to ACS 5.8.1

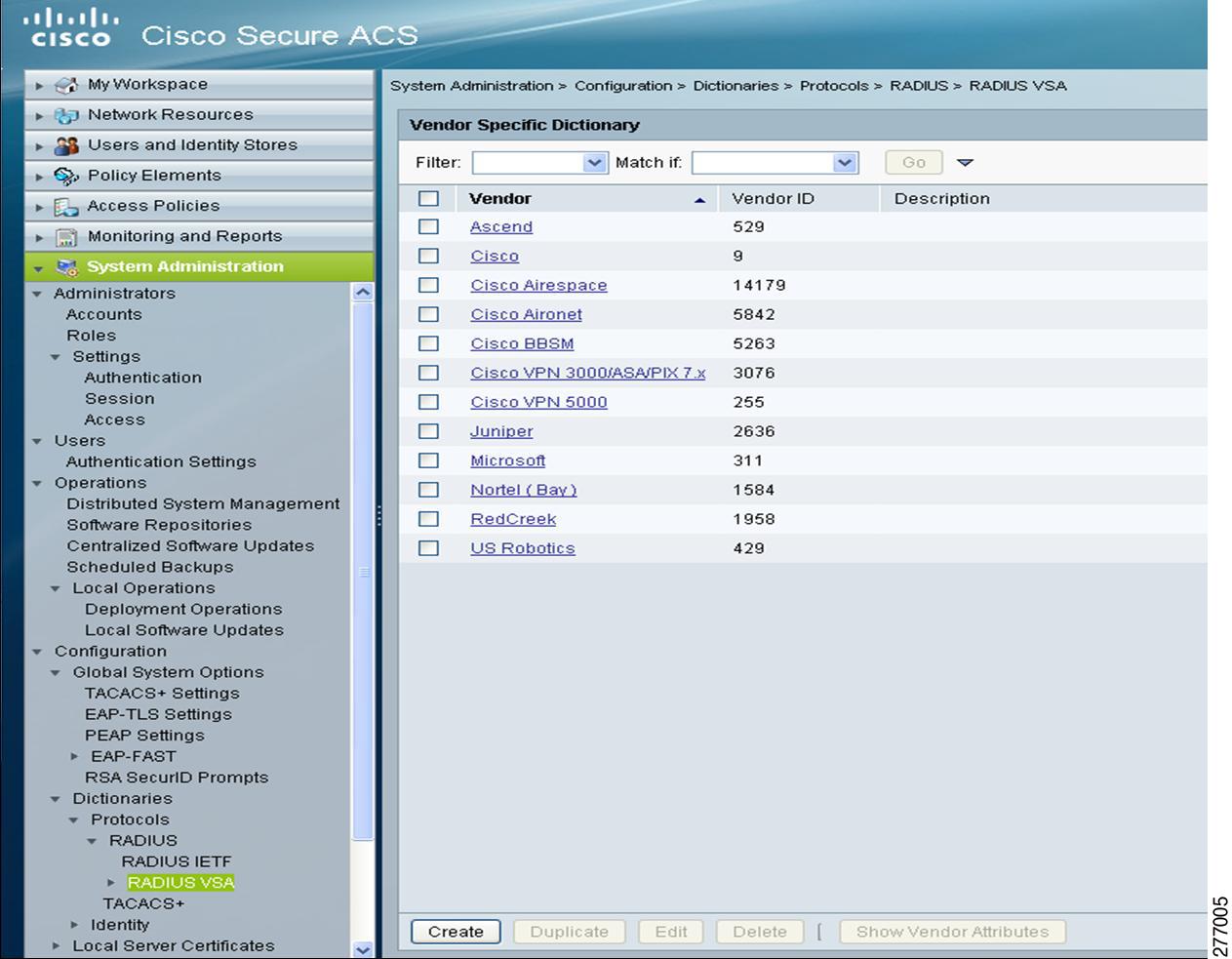
RADIUS VSA
Figure 24 shows RADIUS VSAs defined in ACS 4.x, and Figure 25 shows RADIUS VSAs migrated to ACS 5.8.1.
Choose System Administration > Configuration > Dictionaries > RADIUS > RADIUS VSA to access the migrated RADIUS VSAs.
Figure 24 RADIUS VSAs in ACS 4.x
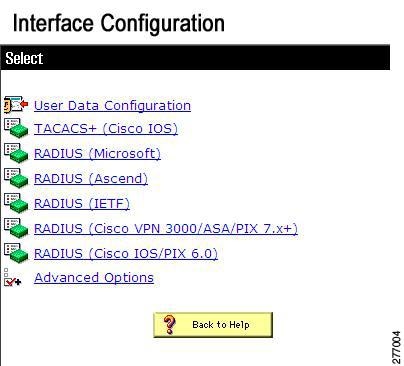
Figure 25 RADIUS VSAs Migrated to ACS 5.8.1
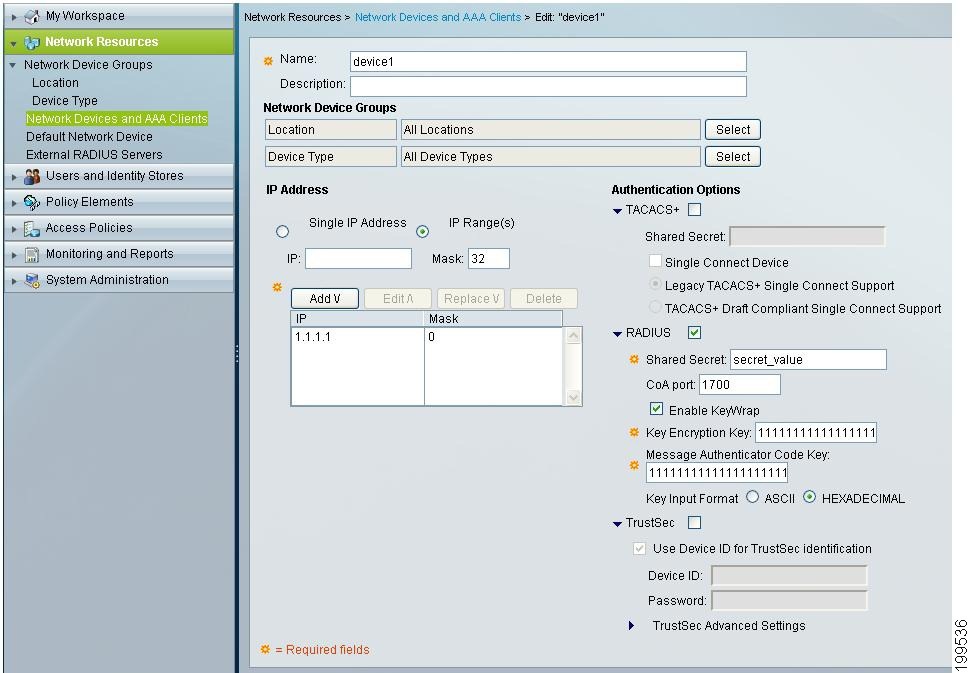
KEK and MACK Keys
Figure 26 shows Key Encryption Key (KEK) and Message Authentication Code Key (MACK) keys defined in ACS 4.x, and Figure 27 shows the KEK and MACK keys migrated to ACS 5.8.1.
Choose Network Devices > Network Devices and AAA Clients, select a device and click Edit to access the migrated KEK and MACK keys.
Figure 26 KEK and MACK Keys Defined in ACS 4.x

Figure 27 KEK and MACK Keys Migrated to ACS 5.8.1
 Feedback
Feedback