IPsec Management Configuration Guide, Cisco IOS Release 15.1M&T
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- February 18, 2008
Chapter: VPN Device Manager Client for Cisco IOS Software (XSM Configuration)
VPN Device Manager Client for Cisco IOS Software (XSM Configuration)

Note ![]() For the primary documentaiton of the latest version of the VPN Device Manager (version 1.2), see the "Installation Guide and Release Notes for VPN Device Manager 1.2" at http://www.cisco.com/univercd/cc/td/doc/product/rtrmgmt/vdm/vdm12rn.htm.
For the primary documentaiton of the latest version of the VPN Device Manager (version 1.2), see the "Installation Guide and Release Notes for VPN Device Manager 1.2" at http://www.cisco.com/univercd/cc/td/doc/product/rtrmgmt/vdm/vdm12rn.htm.
This document describes the command-line interface (CLI) Cisco IOS commands required to activate the VPN Device Manager (VDM) client and includes the following sections:
•![]() Supported Standards, MIBs, and RFCs
Supported Standards, MIBs, and RFCs
•![]() Configuration Examples for VDM
Configuration Examples for VDM
•![]() Feature Information for VPN Device Manager Client
Feature Information for VPN Device Manager Client
Feature Overview
VDM software is installed directly onto Cisco VPN devices. It allows network administrators to use a web browser to manage and configure site-to-site VPNs on a single device. VDM implements a wizard-based GUI that allows simplified VPN configuration of the device on which it resides and peer-to-peer interfaces from that device to remote devices. VDM requires configuration of some Cisco IOS commands before it can be fully operational.

Note ![]() In addition to having the relevant Cisco IOS image installed on your device, make sure the VDM client software has been preinstalled in the device Flash memory. If it has not been, you must download it from Cisco.com. See the Installation and Release Notes for VPN Device Manager for the product version you are using for details on completing this task. See the Cisco VPN Device Manager index (http://www.cisco.com/warp/public/cc/pd/nemnsw/vpdvmn) for further information.
In addition to having the relevant Cisco IOS image installed on your device, make sure the VDM client software has been preinstalled in the device Flash memory. If it has not been, you must download it from Cisco.com. See the Installation and Release Notes for VPN Device Manager for the product version you are using for details on completing this task. See the Cisco VPN Device Manager index (http://www.cisco.com/warp/public/cc/pd/nemnsw/vpdvmn) for further information.
VDM also monitors general system statistics and VPN-specific information such as tunnel throughput and errors. The graphing capability allows comparison of such parameters as traffic volume, tunnel counts, and system utilization. VDM supports site-to-site VPNs. Its step-by-step wizards simplify the configuration of common VPN setups, interfaces, and policies, including:
•![]() IPSec tunnels
IPSec tunnels
•![]() Preshared keys and Internet Key Exchange (IKE) policies
Preshared keys and Internet Key Exchange (IKE) policies
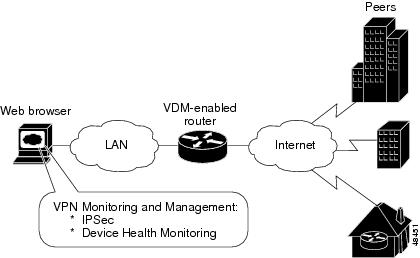
Figure 1 shows a simplified VDM deployment within a VPN.
Figure 1 Simplified VDM Deployment
XML Subscription Manager
XML Subscription Manager (XSM) is an HTTP-based service for retrieving information from a Cisco device. Once remote applications (such as VDM) are connected to the XSM server, they can subscribe to data sets called XML Request Descriptors (XRDs). These are XML-formatted messages describing configuration (access-control lists (ACLs), interfaces, crypto-maps, and others) and monitoring information (CPU, memory usage, interface statistics, and others).
XSM provides remote applications such as VDM with a constantly updated stream of data about Cisco device status by supplying real-time data without repeated device polling.
CLI Commands for VDM
This document gives details about Cisco IOS commands specific to VDM functionality. These commands are not related to general VPN functions but are designed to manage VDM itself via the XSM server. By using the Java-enabled VDM application, you can perform all VPN-related configuration and monitoring tasks within the application.
These commands are designed to complement VDM. The following tasks are performed by specific Cisco IOS XSM commands (command name in parentheses):
•![]() Enabling VDM to receive data from the XSM feature set on the device (xsm)
Enabling VDM to receive data from the XSM feature set on the device (xsm)
•![]() Enabling basic device monitoring, configuration, and data delivery for VDM (xsm edm)
Enabling basic device monitoring, configuration, and data delivery for VDM (xsm edm)
•![]() Enabling VPN-specific monitoring, configuration, and data delivery for VDM (xsm vdm)
Enabling VPN-specific monitoring, configuration, and data delivery for VDM (xsm vdm)
•![]() Enabling access to switch operations (for example, configuring switch ports and VLANs) when running VDM on a switch (xsm dvdm)
Enabling access to switch operations (for example, configuring switch ports and VLANs) when running VDM on a switch (xsm dvdm)
•![]() Enabling collection of selected statistics generic to embedded devices on the XSM server (xsm history edm)
Enabling collection of selected statistics generic to embedded devices on the XSM server (xsm history edm)
•![]() Enabling collection of specific selected VPN statistics on the XSM server (xsm history vdm)
Enabling collection of specific selected VPN statistics on the XSM server (xsm history vdm)
•![]() Clearing VDM client sessions (clear xsm)
Clearing VDM client sessions (clear xsm)
•![]() Displaying information about the XSM server and VDM (show xsm status)
Displaying information about the XSM server and VDM (show xsm status)
•![]() Displaying all XRDs available to VDM (show xsm xrd-list)
Displaying all XRDs available to VDM (show xsm xrd-list)
•![]() Setting user privilege levels for viewing VDM monitoring and configuration data (xsm privilege monitor level and xsm privilege configuration level)
Setting user privilege levels for viewing VDM monitoring and configuration data (xsm privilege monitor level and xsm privilege configuration level)
For more information on VDM, the Installation and Release Notes for VPN Device Manager for the product version you are using or the Documentation CD-ROM that shipped with the product. See the Cisco VPN Device Manager index (http://www.cisco.com/warp/public/cc/pd/nemnsw/vpdvmn) for further information.
Related Features and Technologies
•![]() Virtual Private Networks (VPNs)
Virtual Private Networks (VPNs)
•![]() Security
Security
Related Documents
•![]() Access VPN Solutions Using Tunneling Technology
Access VPN Solutions Using Tunneling Technology
•![]() Access VPDN Dial-in Using L2TP
Access VPDN Dial-in Using L2TP
•![]() Access VPDN Dial-in Using IPSec Over L2TP
Access VPDN Dial-in Using IPSec Over L2TP
•![]() Cisco IOS Dial Technologies Command Reference, Release 12.2
Cisco IOS Dial Technologies Command Reference, Release 12.2
•![]() Cisco IOS Security Configuration Guide, Release 12.2
Cisco IOS Security Configuration Guide, Release 12.2
•![]() Cisco IOS Security Command Reference, Release 12.2
Cisco IOS Security Command Reference, Release 12.2
•![]() "Configuring Virtual Private Networks" chapter in the "Virtual Templates, Profiles, and Networks" part of the Cisco IOS Dial Technologies Configuration Guide, Release 12.2
"Configuring Virtual Private Networks" chapter in the "Virtual Templates, Profiles, and Networks" part of the Cisco IOS Dial Technologies Configuration Guide, Release 12.2
•![]() Installation and Release Notes for VPN Device Manager
Installation and Release Notes for VPN Device Manager
•![]() VDM chapter in the Cisco Enterprise VPN Configuration Guide
VDM chapter in the Cisco Enterprise VPN Configuration Guide
•![]() IPSec VPN Acceleration Services Module Installation and Configuration Note
IPSec VPN Acceleration Services Module Installation and Configuration Note
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for VPN Device Manager Client" section.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Supported Standards, MIBs, and RFCs
Standards
No new or modified standards are supported by this feature.
MIBs
No new or modified MIBs are supported by this feature.
To obtain lists of supported MIBs by platform and Cisco IOS release, and to download MIB modules, go to the Cisco MIB website on Cisco.com at the following URL:
http://www.cisco.com/public/sw-center/netmgmt/cmtk/mibs.shtml
RFCs
No new or modified RFCs are supported by this feature.
Prerequisites
The VDM client software must be installed on your device. It might already have been installed if you chose the VPN option at the time of configuration.
Configuring VDM
See the following sections for configuration tasks for this feature. Each task in the list is identified as either required or optional.
•![]() Enabling the XSM Server for VDM (required)
Enabling the XSM Server for VDM (required)
•![]() Configuring XSM Privilege Levels for XRDs (optional)
Configuring XSM Privilege Levels for XRDs (optional)
•![]() Disabling the XSM Server for VDM (optional)
Disabling the XSM Server for VDM (optional)
•![]() Verifying VDM Status on the XSM Server (optional)
Verifying VDM Status on the XSM Server (optional)
•![]() Clearing XSM Client Sessions (optional)
Clearing XSM Client Sessions (optional)
•![]() Configuring XSM Statistics Collection (optional)
Configuring XSM Statistics Collection (optional)
Enabling the XSM Server for VDM
Use the xsm command in global configuration mode to activate XSM clients (such as VDM) on your device. Enabling this command also enables the xsm vdm and xsm edm global configuration commands, so there is no need to enable them separately.
|
|
|
|---|---|
Router(config)# xsm |
Enables XSM client access to the device. |
Configuring XSM Privilege Levels for XRDs
To set the minimum required privilege levels and grant appropriate access to view, monitor, or configure the XSM client (such as VDM), use the following commands in global configuration mode. Privilege levels set on the device determine which access level users possess (configuration and monitoring, monitoring only, or neither).
Users with privilege levels lower than the required monitoring privilege level will not have access to either the configuration or monitoring data required for subscription to XML Request Descriptors (XRDs). The higher the number, the higher the privilege level. The privilege level for the xsm privilege configuration level command must be greater than or equal to that of the xsm privilege monitor level command.
Disabling the XSM Server for VDM
To disable the XSM server, use the command below in global configuration mode. Disabling this command also disables the xsm vdm and xsm edm global configuration commands.
|
|
|
|---|---|
Router(config)# no xsm |
Disables XSM server. |
Verifying VDM Status on the XSM Server
Use the show xsm status command to verify the status of clients (such as VDM) on the XSM server.
|
|
|
|---|---|
Router# show xsm status |
Displays information and status about clients subscribed to the XSM server. |
Use the show xsm xrd-list command to verify all XML Request Descriptors (XRDs) for XSM clients (such as VDM) made available by subscription to the XSM server.
|
|
|
|---|---|
Router# show xsm xrd-list |
Displays all XRDs for clients subscribed to the XSM server. |
Clearing XSM Client Sessions
Use the clear xsm command to clear data from XSM clients (such as VDM) on the XSM server. To disconnect a specific client, you must identify the session number. Use the show xsm status command to obtain specific session numbers.
|
|
|
|---|---|
Router# clear xsm [session number] |
Clears XSM client sessions. • • |
Configuring XSM Statistics Collection
To configure the XSM server and its related clients (such as VDM) for Embedded Device Manager (EDM) or VPN-specific statistics collection of up to 5 days of data, use the following commands in global configuration mode.
Configuration Examples for VDM
This section provides the following configuration examples:
•![]() Enabling the XSM Server for VDM Example
Enabling the XSM Server for VDM Example
•![]() Configuring XSM Privilege Levels for XRDs Example
Configuring XSM Privilege Levels for XRDs Example
•![]() Disabling the XSM Server for VDM Example
Disabling the XSM Server for VDM Example
•![]() Configuring XSM Statistics Collection Example
Configuring XSM Statistics Collection Example
Enabling the XSM Server for VDM Example
The following example shows how to enable the XSM client on the device:
xsm
Configuring XSM Privilege Levels for XRDs Example
The following example shows how to set a privilege level of 11, for subscription to XRDs:
xsm privilege monitor level 11
Disabling the XSM Server for VDM Example
The following example shows how to enable and then disable the XSM client on the device to troubleshoot VDM:
no xsm
xsm
Configuring XSM Statistics Collection Example
The following example shows how to configure the XSM server and its related clients (such as VDM) for Embedded Device Manager (EDM) or VPN-specific statistics collection of up to 5 days of data:
xsm history edm
xsm history vdm
Feature Information for VPN Device Manager Client
Glossary
Internet Key Exchange (IKE)—A key management protocol standard used in conjunction with IPSec and other standards. IPSec can be configured without IKE, but IKE enhances IPSec by providing additional features, flexibility, and ease of configuration for the IPSec standard. IKE authenticates the IPSec peers, negotiates IPSec keys, and negotiates IPSec security associations. Before any IPSec traffic can be passed, each router/firewall/host must be able to verify the identity of its peer. This can be done by manually entering preshared keys into both hosts or by a CA service.
IP security (IPSec)—A framework of open standards that provides data confidentiality, data integrity, and data authentication between participating peers. IPSec provides these security services at the IP layer.
Virtual Private Network (VPN)—A virtual network that uses advanced encryption and tunneling to permit organizations to establish secure, end-to-end, private network connections over public IP infrastructure networks, such as the Internet or extranets.
VPN Device Manager (VDM)—A browser-based tool for configuring and monitoring VPNs on a VPN-enabled device. VDM allows users to configure and monitor advanced VPN functionality within Cisco devices.
XML Subscription Manager (XSM)— A Cisco IOS subsystem that allows embedded device managers such as VDM to receive XML-based configuration and monitoring information for managing network devices.
XML Request Descriptor (XRD)—A specific requested type of data from XSM.
Embedded Device Manager (EDM)—An XSM adapter that publishes general network device configuration and monitoring information for device managers such as VDM.

 Feedback
Feedback