Cisco NIR Components

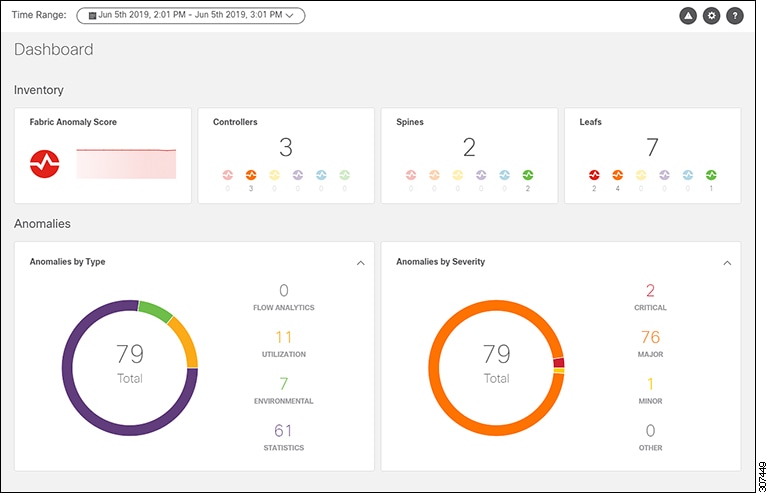
The Cisco Network Insights for Resources (Cisco NIR) is a real-time monitoring and analytics application.
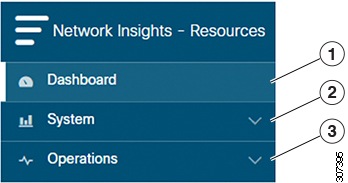
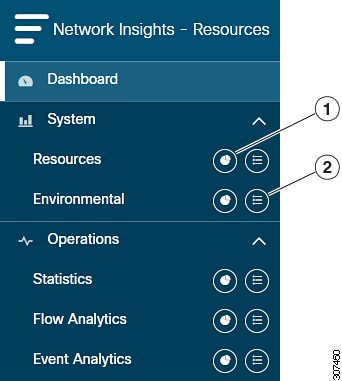
The Cisco NIR application consists of the following components:
-
Data Collection—The streaming of telemetry data is done by the Operating Systems on the fabric switches. As each data source is different and the format in which data is streamed is different, there are corresponding collectors running analytics that translate the telemetry events from the devices into data records to be stored in the data lake. The data stored in the data lake is a format that the analytics pipeline can understand and work upon.
The following telemetry information collected from various devices in the fabric to achieve the goal:
-
Resources Analytics—This includes monitoring software and hardware resources of fabric switches on the Cisco APIC.
-
Environmental—This includes monitoring environmental statistics of hardware resources such as fan, CPU, memory, and power of the fabric switches.
-
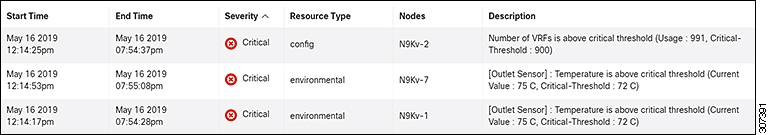
Event Analytics—This includes monitoring of events, faults and configuration changes.
-
Statistics Analytics—This includes monitoring of nodes, interfaces, and protocols on the Cisco APIC and fabric switches.
-
Flow Analytics—This includes the anomalies in the behavior of fabric switches such as average latency, packet drop indicator, and flow move indicator across the entire ACI.
-
-
Resource and Environmental Utilization—Resource analytics supports configuration, operational and hardware resources. Environmental covers CPU, memory, temperature, fan utilization, power, and storage related to the leaf switches, spine switches, and Cisco APIC. System analytics also covers anomalies, the trending information of each resource, and graphing of parameters, which help network operators debug devices over periods of time.
-
Predictive Analytics and Correlation—The value-add of this platform is predicting failures in the fabric and correlating internal fabric failures to the user-visible/interested failures.
-
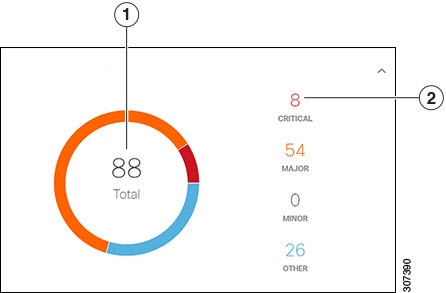
Anomaly Detection—Involves understanding the behavior of each component well using different machine learning algorithms and raising anomalies when the resource behavior deviates from the expected pattern. Anomaly detector applications use different supervised and unsupervised learning algorithms to detect the anomalies in the resources and they log the anomalies in a anomaly database.


 Feedback
Feedback