- Introduction
- Cisco Service Control Solution Overview
- Cisco SCA BB System Overview
- Introduction to Traffic Processing
- Getting Started with Cisco SCA BB Console
- The Network Navigator
- Using the Service Configuration Editor
- Traffic Classification Using Service Configuration Editor
- Traffic Accounting and Reporting Using the Service Configuration Editor
- Traffic Control Using the Service Configuration Editor
- Service Configuration Editor: Additional Options
- Subscriber Manager GUI Tool
- Anonymous Group Manager GUI Tool
- The Signature Editor Overview
- Additional Management Tools and Interfaces
Cisco Service Control Application for Broadband (Cisco SCA BB) User Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- February 17, 2015
Chapter: Service Configuration Editor: Additional Options
- The Service Security Dashboard
- Viewing the Service Security Dashboard
- Introduction to Managing Worm Detection
- Managing Anomaly Detection Overview
- Managing Spam Detection Overview
- Malicious Traffic Reports Overview
Service Configuration Editor: Additional Options
This chapter explains how to use additional, advanced functionality available in the Service Configuration Editor.
This chapter consists of these sections:
- The Service Security Dashboard
- Traffic Flow Filtering
- Managing Subscriber Notifications Overview
- Managing Subscriber Redirection Overview
- Managing the System Settings Overview
- Managing VAS Settings Overview
- Managing the Protected URL Database
The Service Security Dashboard
The Service Security Dashboard allows you to view and control all Cisco SCA BB security functionality.
The Dashboard is a gateway to a set of features that help you protect your network from security threats such as worms, DDoS attacks, and spam zombies. It allows configuration of the detection mechanisms (for example, attack thresholds) and of the actions to be taken when an attack is detected.
The Dashboard also allows you to access malicious traffic reports in the Reporter tool.
 Note | If anomaly-based detection of malicious traffic is enabled, any access control list (ACL) that is configured on the Cisco Service Control Engine (Cisco SCE) platform but is not applied to anything (for example, an interface, an access map, or an SNMP community string) might be deleted when a service configuration is applied to the platform. Workaround : Disable anomaly-based detection of malicious traffic. (Clear the Enable anomaly detection check box.) |
- Viewing the Service Security Dashboard
- Introduction to Managing Worm Detection
- Managing Anomaly Detection Overview
- Managing Spam Detection Overview
- Malicious Traffic Reports Overview
Viewing the Service Security Dashboard
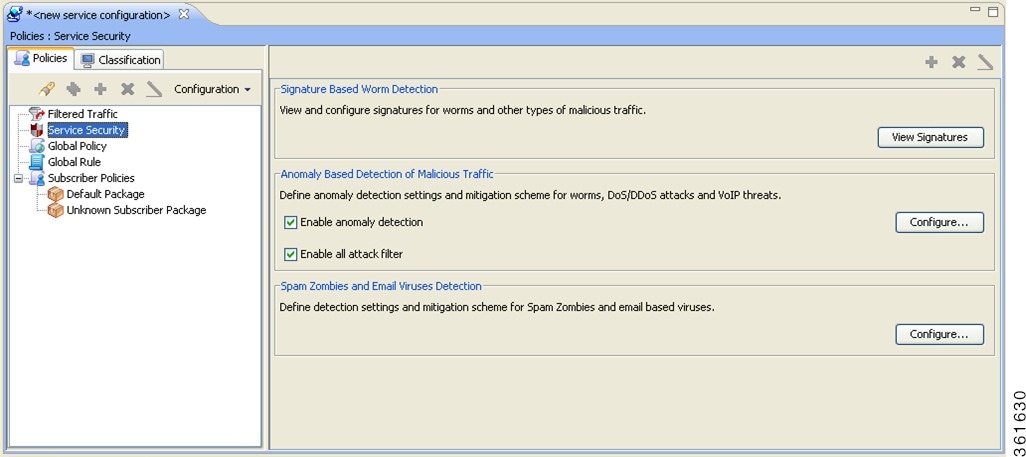 |
Introduction to Managing Worm Detection
Cisco SCA BB uses three mechanisms for detecting worms:
- Signature-based detection—The stateful Layer 7 capabilities of the Cisco SCE platform can detect malicious activity that is not easily detectable by other mechanisms. You can add signatures for new worms.
- Anomaly-based detection—Overall traffic analysis can detect anomalies that might indicate worm activity. See Managing Anomaly Detection Overview section.
- Mass-mailing based detection—E-mail traffic analysis can detect anomalies that might indicate e-mail-based worms. See Configuring Spam Detection Settings section.
For more information, see Introduction to Managing Protocol Signatures section.
Viewing Supported Worm Signatures
| Step 1 | In the Service Security Dashboard, click View Signatures . The Signatures Settings dialog box appears, with Worm Signatures selected in the Signature Type drop-down list. All supported worm signatures are listed. |
| Step 2 | Click Close. The Signatures Settings dialog box closes. |
Adding New Worm Signatures to a Service Configuration
Either import the latest DSS or SPQI file provided by Cisco or create a DSS file containing any worm signatures that you wish to add to the service configuration.
Managing Anomaly Detection Overview
The most comprehensive threat detection method is anomaly detection.
- Anomaly Detection
- Anomaly Detection Parameters
- Viewing Anomaly Detection Settings
- Adding Anomaly Detectors
- Editing Anomaly Detectors
- Deleting Anomaly Detectors
Anomaly Detection
The basic principle of anomaly detection is monitoring successful (correctly established for TCP, bidirectional for other protocols) and unsuccessful (not properly established for TCP, unidirectional for other protocols) connection rates both to and from any IP address viewed by the system, and triggering an anomaly detection condition based of one of the following criteria:
- The total connection rate exceeds a predefined threshold.
- The suspicious connection rate exceeds a predefined threshold and the ratio of suspicious to unsuspicious connections exceeds a predefined threshold.
The ratio metric is a robust indicator of malicious activity, and together with a rate qualifier it serves as a reliable identifier for malicious activity.
Anomaly detection is divided into three categories based on the directional nature of the detected anomaly condition. The concepts used for the three categories are identical, but the nature of the detected malicious activity is different for each category.
- Scan/Sweep detector—Detects malicious activity based on an anomaly in connection rates from an IP address.
- DoS detector—Detects an anomaly in the connection rate between a pair of IP addresses: one of them is attacking the other. This can be either an isolated attack or part of a larger scale DDoS attack.
- DDoS detector—Detects an anomaly in the connection rate coming to an IP address, which means that it is being attacked. The attack can be by either a single IP address (DoS) or multiple IP addresses.
 Note | When the IP address common to all flows of an attack is on the network side, the Cisco SCE may require more flows (than the configured threshold) to detect the attack. |
For all kinds of anomaly detection conditions, maximum flexibility is provided by the ability to define detection thresholds and the trigger actions to be taken for each:
- Flow direction
- Flow protocol
- (Optional) Port uniqueness for TCP and UDP
 Note | The GUI configuration described here replaces the CLI command set for configuring the Attack Filtering Module of the Cisco SCE platform, which was available in previous releases. |
Anomaly Detection Parameters
For each anomaly detector category (Scan/Sweep, DoS, DDoS) there is one default detector. You can add additional detectors of each category. Detectors in each category are checked in order; the first match (according to the threshold settings of the detector) triggers detection. You set the order in which detectors are checked; the default detector is checked last.
- Network initiated—Malicious traffic
initiated from the network side:
- TCP—Aggregate TCP traffic on all ports
- TCP Specific Ports—TCP traffic on any single port
- UDP—Aggregate UDP traffic on all ports
- UDP Specific Ports—UDP traffic on any single port
- ICMP—Aggregate ICMP traffic on all ports
- Other—Aggregate traffic using other protocol types on all ports
- Subscriber
initiated—Malicious traffic initiated from the subscriber side:
- TCP
- TCP Specific Ports
- UDP
- UDP Specific Ports
- ICMP
- Other
 Note | ICMP and Other anomaly types are not available for DoS attack detectors. |
- Detection
thresholds—There are two thresholds, crossing either of them means that an
attack is defined to be in progress:
- Session Rate threshold—The number of sessions (per second) over specified ports for a single IP address that trigger the anomaly detection condition.
- Suspected sessions threshold—Suspected sessions are sessions that are not properly established (for TCP), or that are unidirectional sessions (for other protocols). Exceeding both the Suspected Session Rate and the Suspected Session Ratio triggers the anomaly detection condition. (A relatively high session rate with a low response rate typically indicates malicious activity.)
- Suspected Session Rate—The number of suspected sessions (per second) over specified ports for a single IP address.
- Suspected Session Ratio—The ratio (as a percentage) between the suspected session rate and the total session rate. A high ratio indicates that many sessions received no response, an indication of malicious activity.
- Actions—Zero or
more of the following actions may be taken when an anomaly detection condition
is triggered (by default, no action is enabled):
- Alert User—Generate an SNMP trap indicating the beginning and end of an anomaly. For details on SNMP traps, see the “SCA BB Proprietary MIB Reference” chapter of Cisco Service Control Application for Broadband Reference Guide for information about the Cisco proprietary MIB.
- Notify Subscriber—Notify the relevant subscriber of the malicious activity by redirecting the browsing sessions to a captive portal. To configure network attack subscriber notification, see Managing Subscriber Notifications Overview section.
- Block Attack—Block the relevant sessions. Blocking is performed based on the specification of the malicious traffic that triggered the anomaly detection condition. If subscriber notification is enabled for the anomaly type, blocking is not applied to the port relevant for browsing (by default, this is TCP port 80; see Advanced Service Configuration Options section).

Note
Logging of the anomaly to an on-device log file and generation of RDRs is not configurable per anomaly type. - User-defined
detectors can also have one or more of the following attributes:
- IP address list—Limit detection to the listed IP address ranges. This applies to the source IP when detecting IP sweeps and port scans. It applies to the destination IP when detecting DoS and DDoS attacks.
- TCP port list—Limit detection to the listed destination TCP ports. This list is applied to TCP Specific Ports anomaly types only.
- UDP port list—Limit detection to the listed destination UDP ports. This list is applied to UDP Specific Ports anomaly types only.
Viewing Anomaly Detection Settings
You can view a list of all anomaly detectors. The anomaly detectors are displayed in a tree, grouped according to detector category (Scan/Sweep, DoS, or DDoS).
For each anomaly detector, you can view its associated parameters and see a list of all anomaly types included in the detector, together with their parameters.
Adding Anomaly Detectors
A service configuration can contain up to 100 anomaly detectors.
You define IP address ranges and TCP and UDP ports for the new detector, and one anomaly type.
After you have defined the detector, you can add other anomaly types (see “Editing Anomaly Detectors” section).
The new detector is added to the detector tree.
You can now add additional anomaly types to the detector. See “Editing Anomaly Detectors” section.
Editing Anomaly Detectors
You can perform the following actions on a user-defined anomaly detector:
- Edit detector parameters.
- Edit anomaly types.
- Add anomaly types.
- Delete anomaly types.
- Change the order of the detectors in the detector tree.
For each detector category, detectors are checked, bottom-up, in the order that they are listed in the detector tree; the default detector is checked last.
You can edit the anomaly types of the three default detectors.
Editing Detector Parameters
| Step 1 | In the Service Security Dashboard, in the Anomaly Based Detection of Malicious Traffic pane, click Configure . The Anomaly Detection Settings dialog box appears. |
| Step 2 | In the detector tree, select a detector. The detector parameters are displayed in the upper right area of the dialog box. |
| Step 3 | In the Name field, enter a new name for the detector. |
| Step 4 | Check or uncheck the IP address range and ports check boxes. |
| Step 5 | Enter or modify lists of IP addresses or ports in the relevant fields. |
| Step 6 | Click OK. The Anomaly Detection Settings dialog box closes. Your changes are saved. |
Editing Anomaly Types
| Step 1 | In the Service Security Dashboard, in the Anomaly Based Detection of Malicious Traffic pane, click Configure . The Anomaly Detection Settings dialog box appears. |
| Step 2 | In the detector tree, select a detector. Information about the anomaly types is displayed in the lower right area of the dialog box. |
| Step 3 | Double-click an anomaly type. The Anomaly Detector Creation wizard appears, open to the Anomaly Detection Thresholds page (see Adding an Anomaly Type section). |
| Step 4 | Set the
detector settings for this anomaly type.
Do one of the following:
|
| Step 5 | Click Next. The Anomaly Detection Action Settings page of the Anomaly Detector Creation wizard opens. |
| Step 6 | Change Block, Alert, and Notify Subscriber actions. |
| Step 7 | Click Finish . The Anomaly Detector Creation wizard closes. The anomaly type is updated with your changes. |
| Step 8 | Repeat Steps 3 to 7 (or Steps 2 to 7) for other anomaly types. |
| Step 9 | Click OK. The Anomaly Detection Settings dialog box closes. |
Adding an Anomaly Type
| Step 1 | In the Service Security Dashboard, in the Anomaly Based Detection of Malicious Traffic pane, click Configure . The Anomaly Detection Settings dialog box appears. |
| Step 2 | In the detector tree, select a detector. The anomaly types are listed in the lower right area of the dialog box. |
| Step 3 | Click the Create
New Detector Item Under Detector Items Feature
|
| Step 4 | Select an origin for the anomaly type you are defining. |
| Step 5 | Select a transport type for the anomaly type you are defining. |
| Step 6 | Click Next . The Anomaly Detection Thresholds page of the Anomaly Detector Creation wizard opens. |
| Step 7 | Set the detector
settings for this anomaly type.
|
| Step 8 | Click Next . The Anomaly Detection Action Settings page of the Anomaly Detector Creation wizard opens. |
| Step 9 | Select Block, Alert, and Notify Subscriber actions. |
| Step 10 | Click Finish.
The Anomaly Detector Creation wizard closes. The new anomaly type is added to the anomaly type list. |
| Step 11 | Repeat Steps 3 to 10 (or Steps 2 to 10) for other anomaly types. |
| Step 12 | Click OK. The Anomaly Detection Settings dialog box closes. |
Deleting an Anomaly Type
| Step 1 | In the Service Security Dashboard, in the Anomaly Based Detection of Malicious Traffic pane, click Configure . The Anomaly Detection Settings dialog box appears. |
| Step 2 | In the detector tree, select a detector. The anomaly types are listed in the lower right area of the dialog box. |
| Step 3 | In the anomaly type list, select an anomaly type. |
| Step 4 | Click the Delete
 icon.
The
selected anomaly type is deleted from the anomaly type list.
icon.
The
selected anomaly type is deleted from the anomaly type list.
|
| Step 5 | Repeat Steps 3 and 4 (or Steps 2 to 4) for other anomaly types. |
| Step 6 | Click OK. The Anomaly Detection Settings dialog box closes. |
Changing the Order in which Detectors are Checked
| Step 1 | In the Service
Security Dashboard, in the Anomaly Based Detection of Malicious Traffic pane,
click Configure .
The Anomaly Detection Settings dialog box appears. |
| Step 2 | In the detector
tree, select a detector.
The move up arrow, the move down arrow, or both are enabled, depending on the detectors location in the tree. 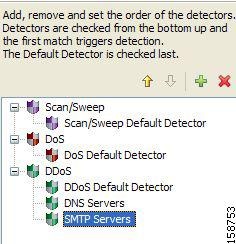 |
| Step 3 | Using these navigation arrows, move the detector to its desired location. |
| Step 4 | Repeat Steps 2 and 3 for other detectors. |
| Step 5 | Click OK.
The Anomaly Detection Settings dialog box closes. Your changes are saved. |
Deleting Anomaly Detectors
You can delete any or all user-defined detectors.
You cannot delete the three default detectors.
| Step 1 | In the Service Security Dashboard, in the Anomaly Based Detection of Malicious Traffic pane, click Configure . The Anomaly Detection Settings dialog box appears. |
| Step 2 | In the detector tree, select one or more user-defined detectors. |
| Step 3 | Click the Delete
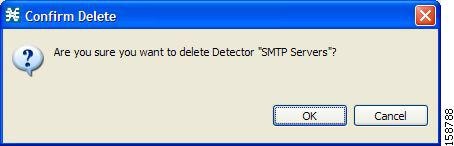 |
| Step 4 | Click OK. The selected detectors are deleted and are no longer displayed in the detector tree |
| Step 5 | Click OK . The Anomaly Detection Settings dialog box closes. |
Managing Spam Detection Overview
The anomalous e-mail detection method monitors SMTP session rates for individual subscribers. A high rate of SMTP sessions from an individual subscriber is usually an indicator of malicious activity that involves sending e-mail (either mail-based viruses or spam-zombie activity).
This method works only if the system is configured in subscriber-aware or anonymous subscriber mode. This allows the Cisco SCE to accurately account the number of SMTP sessions generated per subscriber.
The detection method is based on the following:
- Typical broadband subscribers generate few SMTP sessions (at most a single session each time they send an e-mail message).
- Typical broadband subscribers normally use the SMTP server of the ISP (as configured in their mail client) as their only mail relay, and do not communicate with off-net SMTP servers.
- Spam zombies create many SMTP sessions, mainly to off-net servers (the mail servers of the destined recipient of the messages).
When configuring spam detection, you select an appropriate service to monitor. By default, this is the built-in SMTP service.
- Configuring Spam Detection Settings
- Configuring Outgoing Spam Mitigation Settings per Package from Subscriber Policies
Configuring Spam Detection Settings
| Step 1 | In the Service
Security Dashboard, in the Spam Zombies and Email Viruses Detection pane, click
Configure.
The Spam
Detection and Mitigation settings dialog box appears.
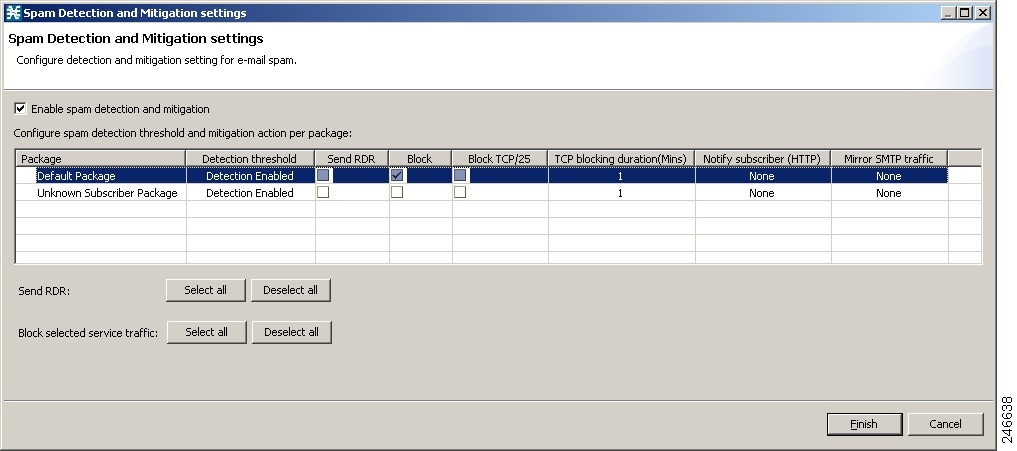 | ||||
| Step 2 | (Optional) To disable spam detection, uncheck the Enable Spam detection and mitigation check box. All other fields are disabled. If you are disabling spam detection, continue at Step 6 . | ||||
| Step 3 | For each
package, do the following:
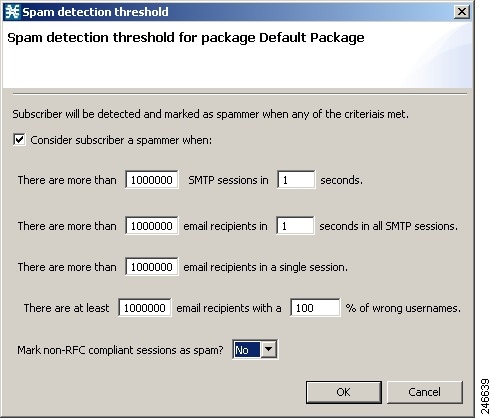 | ||||
| Step 4 | Define one or
more actions to be taken upon detecting mass-mailing activity.
Available
actions are:
| ||||
| Step 5 | If you selected
Notify Subscriber (HTTP), choose or enter a notify subscriber.
| ||||
| Step 6 | If you selected Mirror SMTP traffic, choose a server group. | ||||
| Step 7 | Click Finish.
The Spam Detection and Mitigation settings dialog box closes. |
Configuring Outgoing Spam Mitigation Settings per Package from Subscriber Policies
| Step 1 | In the Service Configuration Editor Policies tab, select a Package from the Subscriber Policies. |
| Step 2 | Right-click on the Package and select Edit Package. The Package Settings window appears. |
| Step 3 | Click Spam
Settings tab to view the Spam Detection Settings and Spam Action Settings.
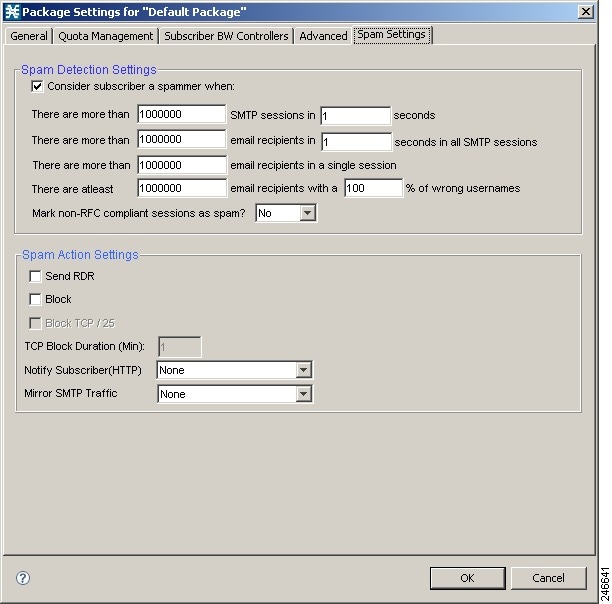 |
| Step 4 | Select the Consider Subscriber a spammer when: check box to enable the spam detection. |
| Step 5 | Define when to consider the subscriber a spammer and the actions to be taken. |
| Step 6 | Click OK. |
For more details on spam mitigation, see the Cisco Service Control Service Security: Outgoing Spam Mitigation Solution Guide.
Malicious Traffic Reports Overview
Information about detected traffic anomalies is stored in the Collection Manager database. You can use this information for network trending, detection of new threats, and tracking of malicious hosts or subscribers.
- Malicious Traffic Reports
- How to View a Service Security Report
Malicious Traffic Reports
A number of reports dealing with malicious traffic can be displayed in the SCA Reporter tool:
- Global reports:
- Global Scan or Attack Rate
- Global DoS Rate
- Infected Subscribers
- Infected Subscribers versus Active Subscribers
- DoS Attacked Subscribers
- Top Scanned or Attacked ports
- Individual subscriber or hosts reports:
- Top Scanning or Attacking hosts
- Top DoS Attacked hosts
- Top DoS Attacked Subscribers
- Top Scanning or Attacking Subscribers
Viewing a Service Security Report
| Step 1 | In the Service Security Dashboard, in the relevant pane, click View
Report. A Choose a report dialog box appears, displaying a tree of relevant reports. |
| Step 2 | Select a report from the report tree. |
| Step 3 | Click OK. The Choose a report dialog box closes. |
The Reporter tool opens in the Console, and displays the requested report.
For information about manipulating and saving the report, see the “Working with Reports” chapter of Cisco Service Control Application Reporter User Guide.
Traffic Flow Filtering
Filter rules are part of service configurations. They allow you to instruct the Cisco SCE platform, based on a flow’s Layer 3 and Layer 4 properties, to:
- Bypass—Ignore the flow and transmit it unchanged.
- Quick forward—Duplicate the flow and send one copy directly to the transmit queue to ensure minimal delay. The second copy goes through the normal packet path.
When a traffic flow enters the Cisco SCE platform, the platform checks whether a filter rule applies to this flow.
If a filter rule applies to this traffic flow, the Cisco SCE platform passes the traffic flow to its transmit queues. No RDR generation or service configuration enforcement is performed; these flows do not appear in any records generated for analysis purposes and are not controlled by any rule belonging to the active service configuration.
It is recommended that you add filter rules for OSS protocols (such as DHCP) and routing protocols (such as BGP) that might traverse the Cisco SCE platform. These protocols usually should not be affected by policy enforcement, and their low volume makes them insignificant for reporting.
A number of predefined filter rules are included in every new service configuration.
 Note | By default, some, but not all, of the predefined filter rules are active. |
Flows of certain protocols can also be filtered according to the Layer 7 characteristics of the flow (see Advanced Service Configuration Options section). Like other filtered flows, Layer 7 filtered flows are not controlled, but can be classified and reported. The flows of the protocols that can be filtered are typically short and their overall volume is negligible. So filtering these protocols has little effect on network bandwidth and on the accuracy of the Cisco SCA BB reports.
- Information About Traffic Filtering
- Viewing Filter Rules for a Package
- Setting Flexible Configuration of Port based Filters
- Adding Filter Rules
- Adding Filter Rules for IPv6 Configuration
- Editing Filter Rules
- Deleting Filter Rules
- Activating and Deactivating Filter Rules
Information About Traffic Filtering
For certain types of traffic, service providers may need to reduce the latency and jitter introduced by the Cisco SCE platform or even to bypass the Cisco SCE platform to avoid traffic control as well. Typically, such decisions are made for a portion of the traffic, to reduce latency for delay sensitive applications, such as voice, and to bypass mission-critical traffic, such as routing protocols. The Cisco SCA BB Filtered Traffic mechanism is used to address this need.
 Note | To reduce latency, Cisco SCE platform automatically handles most voice traffic. For details, seeAutomatic Quick Forwarding of Media Flows section. |
- The Cisco SCA BB Filtered Traffic Mechanism
- Filter Rule Actions
- Filter Rules and Service Rules
- Automatic Quick Forwarding of Media Flows
- Filtering L2TP Traffic
The Cisco SCA BB Filtered Traffic Mechanism
The Cisco SCA BB Filtered Traffic mechanism reduces latency or completely bypasses portions of the traffic by defining filter rules that match relevant flows and assign the correct action to them. A filter rule matches a packet according to its Layer 3 and Layer 4 properties, such as IP address, port number, and DSCP ToS, as well as the Cisco SCE platform interface (subscriber or network) from which the packet arrived. For packets that match a filter rule, the following actions can be applied:
When this action is applied, the current packet is directly transmitted from the Cisco SCE platform without going through any service configuration processing or reporting. You must map the bypassed packet to a Class of Service (CoS) to assign it to one of the transmit queues of the Cisco SCE platform.
Possible values for CoS are BE, AF1, AF2, AF3, AF4, and EF; where EF implies high processing priority and the other classes imply normal processing priority.
When this action is applied, the current packet and all subsequent packets belonging to the same flow are duplicated and sent through two different paths: the original packet goes directly to the transmit queue, and thus has only a minimal delay, while a copy of the packet goes through the normal service configuration processing path for classification and reporting, and is then discarded.
 Note | Not all platforms support this option. |
When this action is applied, the current packet and all subsequent packets belonging to the same flow enter the high priority processing input queue. They go through the normal service configuration processing path ahead of other packets that arrive simultaneously. You should map the flow to the EF CoS to assign it to the high processing priority transmit queue of the Cisco SCE platform.
 Note | In an MPLS environment, the Cisco SCE platform does not map the DSCP bits to the EXP bits of the MPLS header. |
A filter rule can perform DSCP ToS marking (by changing the DSCP ToS field of the packet) of the matched traffic with any of the above actions.
 Note | DSCP ToS marking and the assignment to CoS only take place when the operational mode of the system is Full Functionality (see System Operational Mode section). |
The Cisco SCE processes the traffic based on the Class of Service (CoS). Possible values for CoS are BE, AF1, AF2, AF3, AF4, and EF; where EF implies high processing priority and the other classes imply normal processing priority.
In SCE 8000SCE10000, if there are 4 output queues—EF, AF n ,AF1, and BE, this is how the queues are prioritized:
- EF—Gets the highest priority and strictly gets priority over all other queues.
- AF1 and AF n (AF2, AF3, AF4)—Gets the weighted priority on top of AF1. For each n packets of AF n , one packet is sent for AF1. The value of n can be configured from the FPGA. The default value is 3.
- BE—Gets lowest priority. BE packets are transmitted only if packets for transmission are not available in other queues.
The Cisco SCE transmits only the received packet and do not generate the traffic internally; other than rarely transmit inject for reset or redirect. So, there can never be a long time in which lower priority queues are starved.
When there are only buckets—EF and the rest. In CoS other than EF (AF1,AF2,AF3,AF4,BE), the order of priority would be AF1 > AF2 > and so on. However, the bandwidth is allocated in the order EF > AF n > AF1 > BE. Queues AF2, AF3, and AF4 would have the same weight.
Filter Rule Actions
The Bypass and Quick forward actions apply to different scopes of traffic:
- The Bypass action only bypasses the current packet; every subsequent packet of the
same flow goes through the Filtered Traffic mechanism. This means, for example, that
when traffic is to be bypassed based on its destination port number, two rules
should be created to match packets from both sides of a bidirectional flow.
For example, to bypass all traffic to destination port 23, two filter rules are needed, one for packets arriving from the subscriber side addressed to network side port 23, and another for packets arriving from the network side addressed to subscriber side port 23.
- The Quick forward action is applied to the entire flow; once identified, all
subsequent packets do not go through the filter rule mechanism, instead going
through normal service configuration processing.
A packet may match more than one filter rule. If both Bypass and Quick forward are matched, the packet/flow is bypassed with minimum delay. Furthermore, if only Bypass is matched, the packet/flow is also be bypassed with minimum delay.
Filter Rules and Service Rules
Filter rule actions to reduce latency allow the flow to be controlled by the Cisco SCE platform. This means that the flow can be blocked or given limited bandwidth if it matches a service rule. For example, if a filter rule is applied to reduce latency, but a service configuration rule is applied to block the same traffic, the traffic is blocked.
The Bypass action is designed to avoid service configuration processing; bypassed traffic is not affected by service rules.
Automatic Quick Forwarding of Media Flows
The Cisco SCE platform reduces the latency of delay-sensitive voice and video media flows by applying the quick-forwarding action to SIP, MGCP, H323, Skinny, and RTSP media flows during classification. When a media flow is classified as being of one of these types, it is subjected to quick forwarding immediately.
The Cisco SCE platform does this automatically, regardless of filter rule configuration. These media flows might still be blocked or given limited bandwidth if they match a service rule.
Filtering L2TP Traffic
If you know the version of the L2TP tunnel that is being used, configure the relevant filters. If you do not know the version, enable filter for both type of tunnels (L2TPv2 and L2TPv3).
 Note | The L2TPv3 data encapsulation is done directly over IP with protocol ID 115. Cisco SCA BB provides a filter for this type of traffic and you can enable it from Cisco SCA BB. However, L2TPv2 protocol data encapsulation is done over UDP protocol at Layer 4 with default destination port 1701. Cisco SCA BB does not provide any filter for this type of traffic. To filter L2TPv2 traffic, create a new filter with the transport type as UDP and destination UDP port value as 1701. |
Viewing Filter Rules for a Package
You can view a list of the filter rules included in a service configuration.
The listing for each filter rule includes the name, the status, and a brief description (generated by the system) of the rule.
To see more information about a filter rule, open the Edit Filter Rule dialog box (see “How to Edit Filter Rules” section).
A list of all filter rules is displayed in the right (Rule) pane.
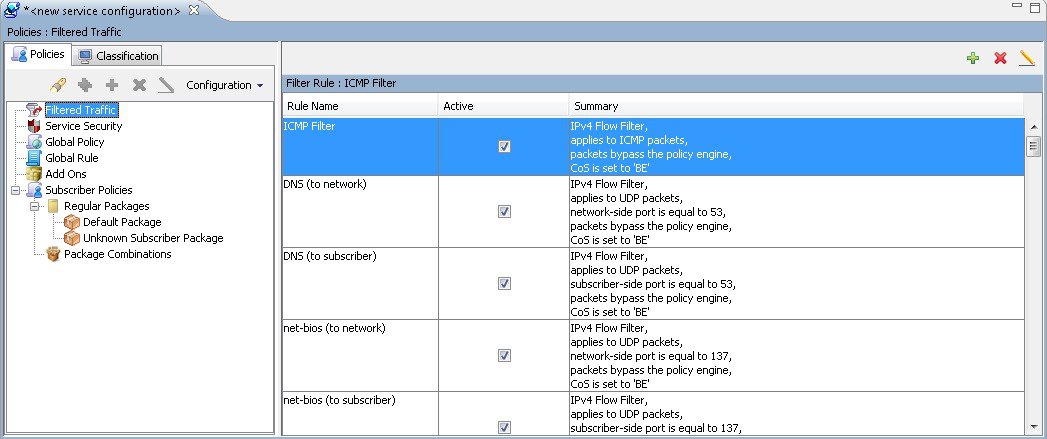 |
Setting Flexible Configuration of Port based Filters
| Step 1 | Choose Windows > Preferences. |
| Step 2 | In the Preferences window, expand the Service Configuration. |
| Step 3 | Click Filtered Traffic. |
| Step 4 | For SCE 8K-
Enter the value of the port based filters. The valid integer values of the port
based filters range between 21 and 50. The default value is 21.
For SCE10k - Enter the value of the port based filters. The valid integer values of the port based filters range between 38 and 121. The default value is 38.
|
| Step 5 | Click Apply. |
| Step 6 | Click OK.
8K Calculation: The number of IP based flow filters is reduced, based on the configured flow filters count. For example, if the number of port based flow filter count is increased as 27, the result is as follows: 10K Calculation: The number of IP based flow filters is reduced based on the configured flow filters count. For example, if the number of port based flow filter 10K count is increased as 40, the result is as follows: |
Adding Filter Rules
The Add Filter Rule wizard guides you through the process of adding a filter rule.
 Note | You can use a maximum of 39 IPv4 and IPv6 rules combined on the Cisco SCE 8000 devices. The Cisco SCA BB applies one internal rule automatically. |
 Note | IPv4 Rule Ranges: IP Based: Out of 90 rules, 88 rules can be custom configured on the Cisco SCE10000 devices. One rule will be allotted for default rule during the policy apply. This rule will be written to SCE only if the System mode is in either Transparent or report only mode. It will not be avail during full functionality mode and another rule will be allotted during PQI Installation as default rule. Port Based : 38 rules can be configured. |
 Note | IPv6 Rule Ranges: IP Based: Out of 90 rules, 89 rules can be custom configured on the Cisco SCE 10000 devices. One default rule will be allotted during PQI Installation. Port Based : All the 38 rules can be configured There is no common rule behavior for port based filter configurations. |
| Step 1 | In the Policies tab of Service Configuration Editor window, select the Filtered Traffic node. | ||
| Step 2 | Click
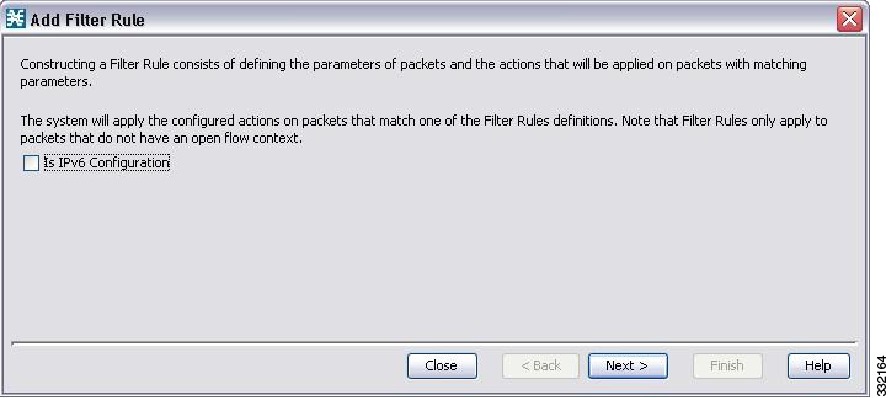 | ||
| Step 3 | Click Next.
The
Transport Type and Direction screen of the Add Filter Rule wizard appears.
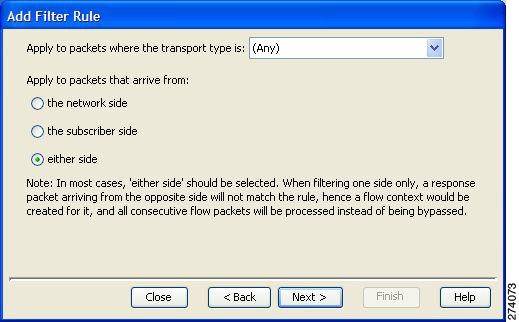 | ||
| Step 4 | Select the
transport type and initiating side and click Next .
The
Subscriber-Side IP Address screen of the Add Filter Rule wizard appears.
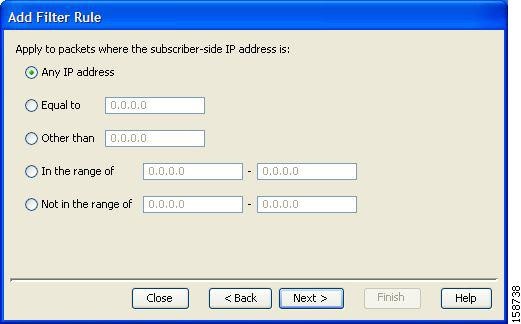 | ||
| Step 5 | Define the
subscriber-side IP address and click Next.
The
Network-Side IP Address screen of the Add Filter Rule wizard appears.
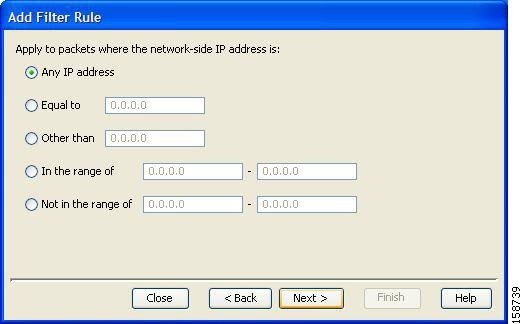 | ||
| Step 6 | Define the
network-side IP address and click Next.
If the transport type selected in Step 4 was not TCP or UDP, the ToS screen of the Add Filter Rule wizard appears. Go to Step 9. If the transport type selected in Step 4 was TCP or UDP, the Subscriber-Side Port screen of the Add Filter Rule wizard appears. 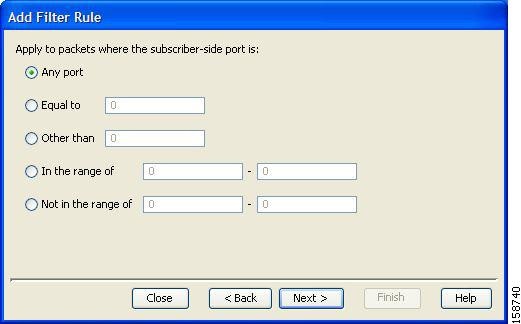 | ||
| Step 7 | Define the
subscriber-side port and click Next.
The Network-Side Port screen of the Add Filter Rule wizard appears. 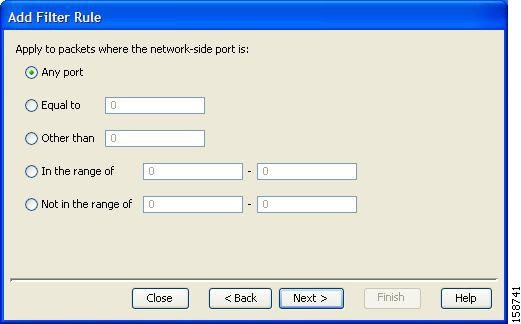 | ||
| Step 8 | Define the
network-side port and click Next.
The Type of Service (ToS) screen of the Add Filter Rule wizard appears. 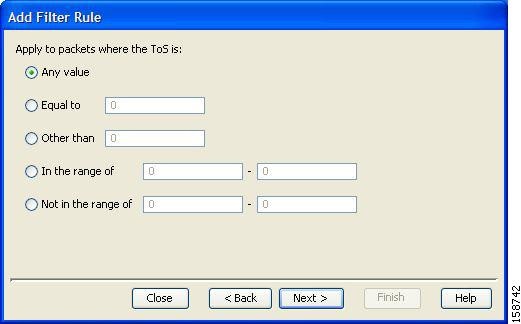 | ||
| Step 9 | Define the ToS
and click Next.
The acceptable
values for ToS are 0 to 63.
The Action and Class-of-Service screen of the Add Filter Rule wizard appears. 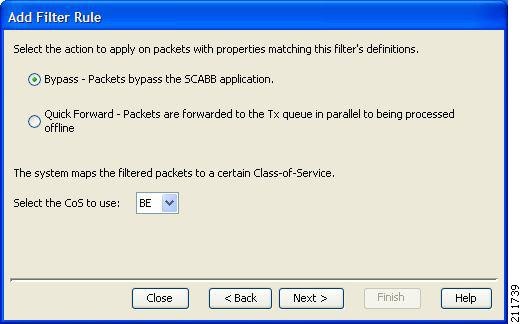 | ||
| Step 10 | Select the radio button for the required action. | ||
| Step 11 | Select a
Class-of-Service value, and click Next.
The ToS Marking screen of the Add Filter Rule wizard appears. 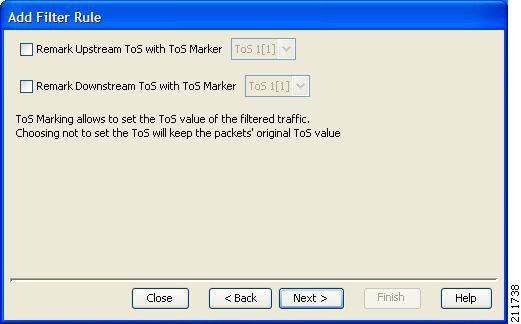 | ||
| Step 12 | (Optional)To change the
DSCP ToS marker of packets in the filtered traffic, check the Remark Upstream
ToS with ToS Marker and Remark Downstream ToS with ToS Marker check boxes, as
required, select the required ToS marker from the drop-down list, and click
Next .
The Finish page of the Add Filter Rule wizard opens. 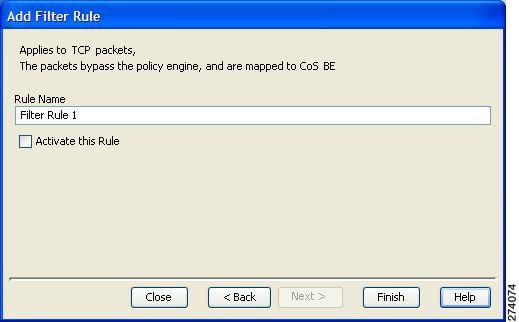 | ||
| Step 13 | In the Rule Name
field, enter a unique name for the new filter rule.
| ||
| Step 14 | (Optional)To activate the filter rule, check the Activate this rule check box. Traffic is filtered according to the rule only when it is activated. | ||
| Step 15 | Click Finish. The Add Filter Rule wizard closes. |
The filter rule is added and is displayed in the Filter Rule table.
Adding Filter Rules for IPv6 Configuration
The Add Filter Rule wizard guides you through the process of adding a filter rule for IPv6 configuration.
| Step 1 | In the Policies tab of Service Configuration Editor window, select the Filtered Traffic node. | ||
| Step 2 | Click Add Rule
 in the right (Rule) pane.
in the right (Rule) pane.
The Add Filter Rule wizard appears. 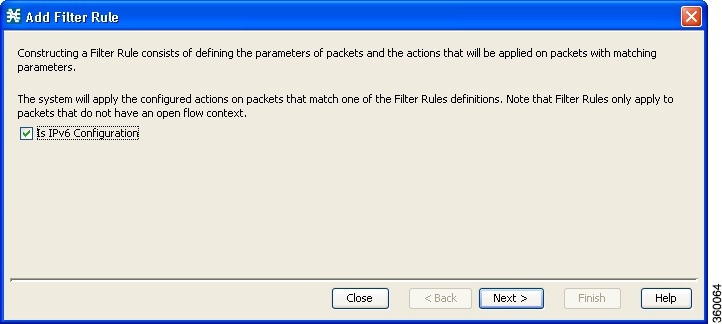 | ||
| Step 3 | Select the Is
IPv6 Configuration check box and click Next.
The Transport Type and Direction screen of the Add Filter Rule wizard appears. 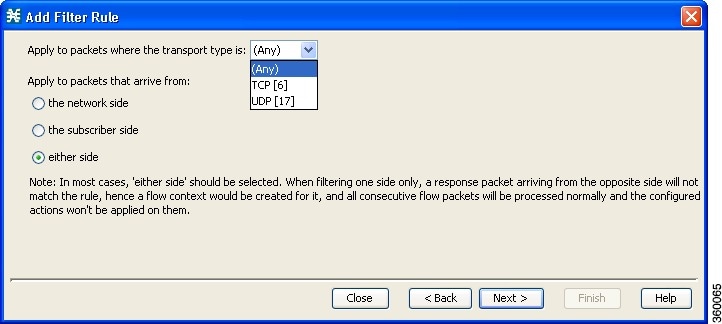 | ||
| Step 4 | Select the
transport type and the initiating side and click
Next.
The Subscriber-Side IP Address screen of the Add Filter Rule wizard appears. 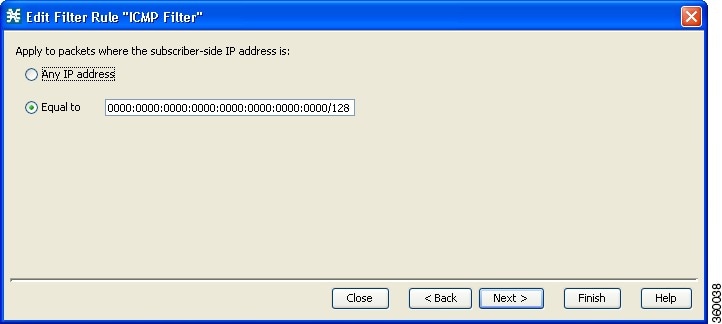 | ||
| Step 5 | Define the
subscriber-side IP address and click Next .
The Network-Side IP Address screen of the Add Filter Rule wizard appears. 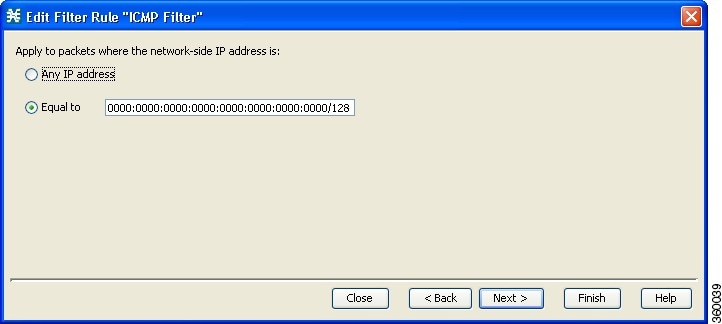 | ||
| Step 6 | Define the
network-side IP address and click Next .
You can use 128-bit masks for the subscriber side IP addresses and the network side IP addresses. If the transport type selected in Step 4 was not TCP or UDP, the ToS screen of the Add Filter Rule wizard appears. Go to Step 9. If the transport type selected in Step 4 was TCP or UDP, the Subscriber-Side Port screen of the Add Filter Rule wizard appears. 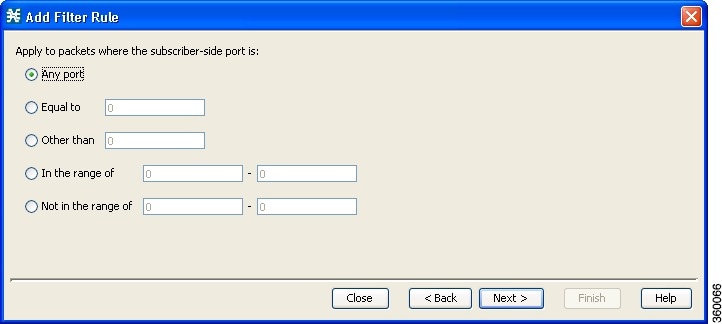 | ||
| Step 7 | Define the
subscriber-side port and click Next .
The Network-Side Port screen of the Add Filter Rule wizard appears. 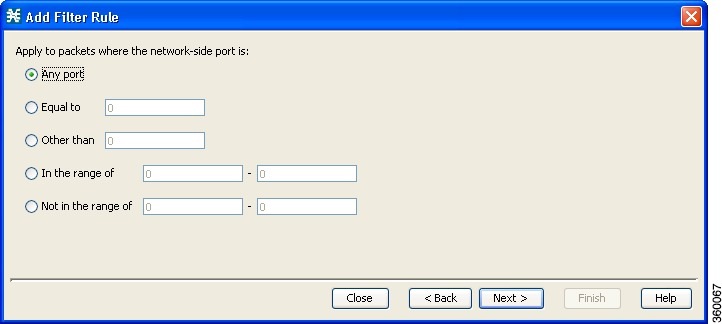 | ||
| Step 8 | Define the
network-side port and click Next.
The ToS screen of the Add Filter Rule wizard appears. 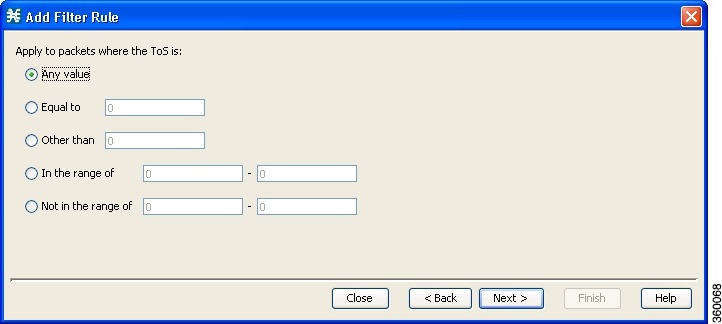 | ||
| Step 9 | Define the ToS
and click Next .
The acceptable
values for ToS are 0 to 63
The Action and Class-of-Service screen of the Add Filter Rule wizard appears. 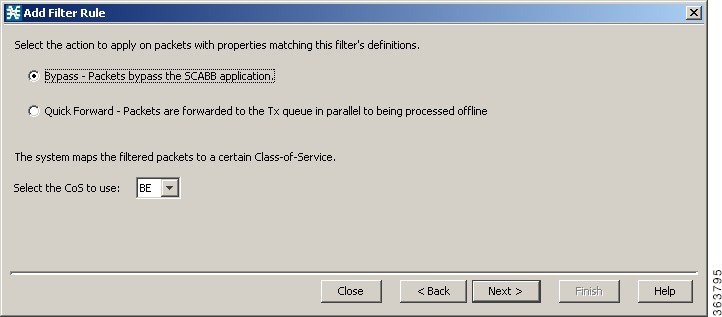 | ||
| Step 10 | Select the following radio button for the corresponding action: | ||
| Step 11 | Select a
Class-of-Service value, and click Next .
The ToS Marking screen of the Add Filter Rule wizard appears. 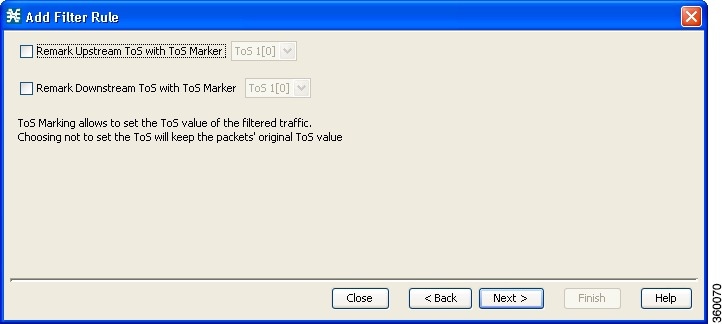 | ||
| Step 12 | (Optional)To change the
DSCP ToS marker of packets in the filtered traffic, check the Remark Upstream
ToS with ToS Marker and Remark Downstream ToS with ToS Marker check boxes,
select the required ToS marker from the drop-down list, and click
Next.
The Finish screen of the Add Filter Rule wizard appears. 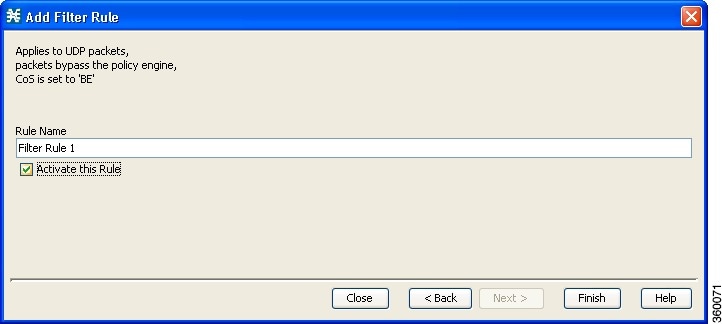 | ||
| Step 13 | In the Rule
Name field, enter a unique name for the new filter rule.
| ||
| Step 14 | (Optional) To activate the filter rule, check the Activate this rule check box. Traffic is filtered according to the rule only when it is activated. | ||
| Step 15 | Click Finish.
The Add
Filter Rule wizard closes. The Filter Rule Warning message is displayed.
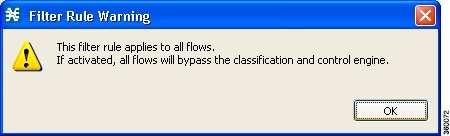 |
The filter rule that has been added is displayed in the Filter Rule table.
Editing Filter Rules
You can view and edit the parameters of a filter rule.
| Step 1 | In the Policies tab of Service Configuration Editor window, select the Filtered Traffic node. A list of all filter rules is displayed in the right (Rule) pane. |
| Step 2 | Select a rule in the Filter Rule table. |
| Step 3 | Click the Edit
Rule
 icon.
icon.
The Introduction page of the Edit Filter Rule wizard appears. The Edit Filter Rule wizard is the same as the Add Filter Rule wizard. |
| Step 4 | Follow the instructions in the section Adding Filter Rules, Steps 4 to 14. |
| Step 5 | Click Finish.
The filter rule is changed and the corresponding changes are displayed in the Filter Rule table. |
Deleting Filter Rules
You can delete filter rules. This is useful, for example, when you want the system to resume handling the IP addresses and their attributes according to the individual rules that were previously defined for each subscriber IP address.
| Step 1 | In the Policies
tab, select the Filtered Traffic node.
A list of all filter rules is displayed in the right (Rule) pane. |
| Step 2 | Select a rule in the Filter Rule table. |
| Step 3 | Click the Delete
Rule
 (158940.jpg)
icon.
A Filter
Rule Warning message is displayed. (158940.jpg)
icon.
A Filter
Rule Warning message is displayed.
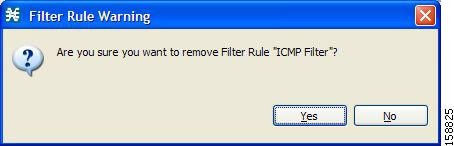 |
| Step 4 | Click Yes. The filter rule is deleted and is no longer displayed in the Filter Rule table. |
Activating and Deactivating Filter Rules
You can activate or deactivate filter rules at any time. Deactivating a filter rule has the same effect as deleting it, but the parameters are retained in the service configuration, and you can reactivate the filter rule at a later date.
| Step 1 | In the Policies tab, select the Filtered Traffic node. A list of all filter rules is displayed in the right (Rule) pane. |
| Step 2 | Select a rule in the Filter Rule table. |
| Step 3 | To activate the rule, check the Active check box. |
| Step 4 | To deactivate the rule, uncheck the Active check box. |
| Step 5 | Repeat Steps 3 and 4 for other rules. |
Managing Subscriber Notifications Overview
The subscriber notification feature pushes web-based messages to a subscriber by redirecting the subscriber HTTP traffic to relevant web pages. These web pages contain information relevant to the subscriber, such as notifications of quota depletion. HTTP redirection starts when the subscriber notification is activated and ceases when the notification is dismissed.
 Note | Subscriber notification is not supported when unidirectional classification is enabled. |
Each set of subscriber redirection parameters comprises a notification redirect profile. The Cisco SCA BB supports a maximum of 128 redirect profiles, including notification and redirect profiles. There are 3 default redirect profiles that cannot be deleted: Default Notification, Network Attack Notification, and Default Redirection. You configure which notification redirect profile to use when defining rules.
- Subscriber Notification Parameters
- Network Attack Notification
- Adding a Notification Redirect Profile
Subscriber Notification Parameters
Each redirect profile of type notification contains the following subscriber notification parameters:
 Note | The Activation trigger configuration options are only available for redirect profile of type redirect. |
 Note | You cannot change the name of the Default Notification or the Network Attack Notification. |
- Redirect profile type—Each profile must be one of two types:
- Set of Redirection URLs—A configurable set of destination URLs, to which the HTTP flows of the subscriber are redirected after redirection is activated. This web page usually contains the message that needs to be conveyed to the subscriber. The redirection set can optionally include one, or several parameters appended to the destination URL including the redirect reason and subscriber ID.
The destination web server can use these parameters to carry a more purposeful message to the subscriber.
- Activation frequency—Indicates when to activate the notification redirect. The activation frequency is one of the following:
 Note | The Periodically option is only available for redirect profile of type redirect. |
- Only once—The subscriber is redirected to the notification only the first time the conditions are met.
For example, if a quota was exceeded, the subscriber browses to the destination URL that informs them of this fact, only once (even though the subscriber remains in a breach state).
For example, if a quota was exceeded, the subscriber is continuously redirected to the notification until the subscriber completes the procedure to refresh their quota.
- Until the subscriber browses to—Every time the conditions are met, the subscriber is redirected to the notification, until the subscriber proceeds from the destination URL to a different, final URL.
For example, if a quota was exceeded, the web page at the destination URL may ask the subscriber to press an Acknowledge button after reading the message. The acknowledge URL would be defined as the dismissal URL and would deactivate further notifications.
The dismissal URL is composed of the URL hostname and the URL path, separated by a colon, in the following format:
- List of Allowed URLs—A list of URLs that are not blocked and redirected even though redirection is activated.
After redirection is activated, all HTTP flows, except flows to the destination URL and to the dismissal URL, are blocked and redirected to the destination URL. However, subscribers can be permitted to access an additional set of URLs. This is useful, for example, to give subscribers access to additional support information.
Allowed URLs have the same format as the dismissal URL.
These parameters are defined when you add a new notification redirect profile (see Adding a Set of Redirection URLs section). You can modify them at any time.
-
Once in a day—The subscriber is redirected only the first time when the conditions are met and this also happens the first time every day.
-
Once in a week—The subscriber is redirected only the first time when the conditions are met and this also happens the first time every week.
-
Once in a Month—The subscriber is redirected only the first time when the conditions are met and this also happens the first time every month.

Note
By default "Across login " support is enabled for the above three options . Redirection History RDR will be generated every time , when the redirection condition is met . The Subscriber manager processes those RDRs and shares the redirected profile information on the next login The Redirection History RDR will be generated to reset the marked profiles, once at the end of a Day, a Week and a Month . By this way we are achieving the redirection only once in a Day , Week and Month .
For more information, see "Subscriber Redirection" section in Cisco Subscriber Manger user guide.
For more information, see "Redirection History RDR" section in Cisco Service Control Application for Broadband reference guide and see "Configuring the Subscriber Redirection Across Login" section in Cisco SCE 10000 Software Configuration Guide
Network Attack Notification
Subscriber notification informs a subscriber in real-time about current attacks involving IP addresses mapped to that subscriber. (Enabling these notifications is described in “The Service Security Dashboard” section.) Cisco SCA BB notifies the subscriber about the attack by redirecting HTTP flows originating from the subscriber to a server that supplies information about the attack.
One subscriber notification, Network Attack Notification, is dedicated to providing these notifications; it cannot be deleted. A Network Attack Notification is not dismissed at the end of an attack; subscribers must respond to it.
To allow redirection when blocking traffic, the system is configured to leave open one specified TCP port (by default, port 80). See “Advanced Service Configuration Options” section.
 Note | In earlier releases of Cisco SCA BB, configuring network attack notifications was performed using CLI commands. CLI commands should no longer be used for this purpose. |
Network Attack Notification Parameters
When a network attack is detected, HTTP flows of the subscriber are redirected to a configurable destination URL. This web page should display the warning that needs to be conveyed to the subscriber.
Optionally, the destination URL can include a query part containing notification parameters. The destination web server can use these parameters to create a more specific warning to the subscriber.
The query part of the URL has the following format:
?ip=<ip>&side=<side>&dir=<dir>&prot=<protocol>&no=<open-flows>&nd=<suspected-flows>&to=<open-flows-threshold>&td=<suspected-flows-threshold>&ac=<action>&nh=>handled-flows>
| Field | Description | Possible Values |
|---|---|---|
|
ip |
Detected IP address |
|
|
side |
— |
|
|
dir |
— |
|
|
protocol |
— |
|
|
open-flows |
Number of open flows |
— |
|
suspected flows |
Number of attack-suspected flows |
— |
|
open-flows-threshold |
Threshold for open flows |
— |
|
suspected-flows-threshold |
Threshold for attack-suspected flows |
— |
|
action |
— |
|
|
handled-flows |
Number of flows handled since the attack began (Non-zero only during and at the end of an attack) |
— |
Example of URL with Description Tail
Adding a Notification Redirect Profile
 Note | Creating a notification redirect profile does not activate the subscriber notification feature. After the notification redirect profile is defined, it must be activated for a particular package |
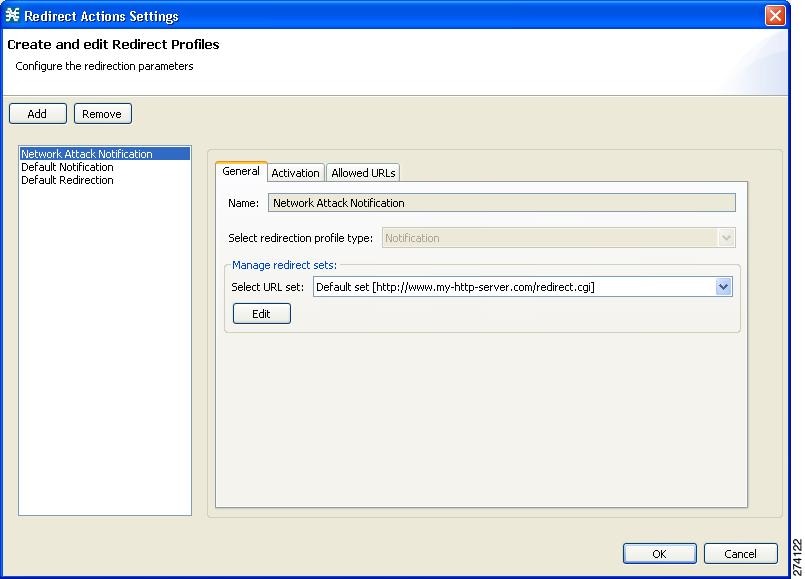
| Step 1 | From the
Policies tab in the left pane, choose
Configuration >
Policies >
Subscriber Redirection.
The
Redirect Actions Settings dialog box appears.
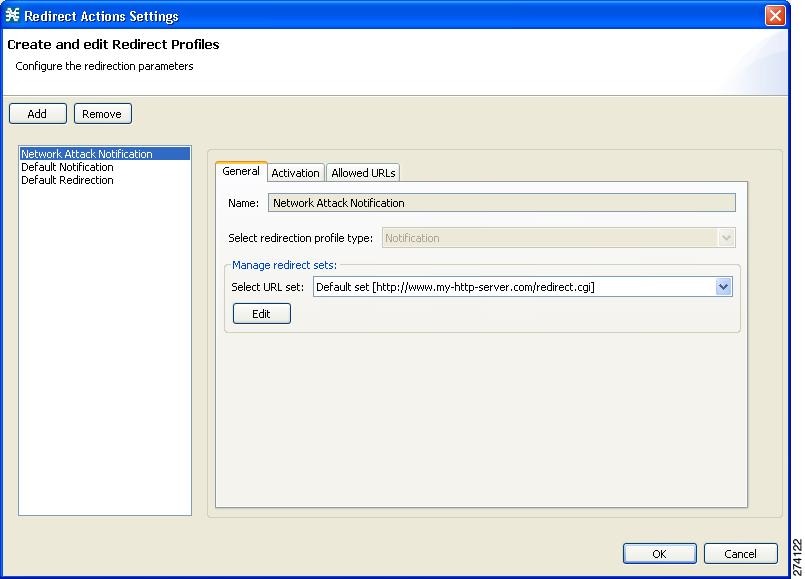 | ||
| Step 2 | Click Add. A new redirection profile containing the default redirection URL set is added to the redirection profile list. | ||
| Step 3 | In the Name field, enter a unique name for the new notification redirect profile. You can use the default name for the notification redirect profile. It is recommended that you enter a meaningful name. | ||
| Step 4 | In the Select redirection profile type field, select Notification. Do not skip this step or a redirect profile is created instead of a notification redirect profile. | ||
| Step 5 | Choose a URL set. | ||
| Step 6 | Click the
Activation tab.
The
Activation tab opens.
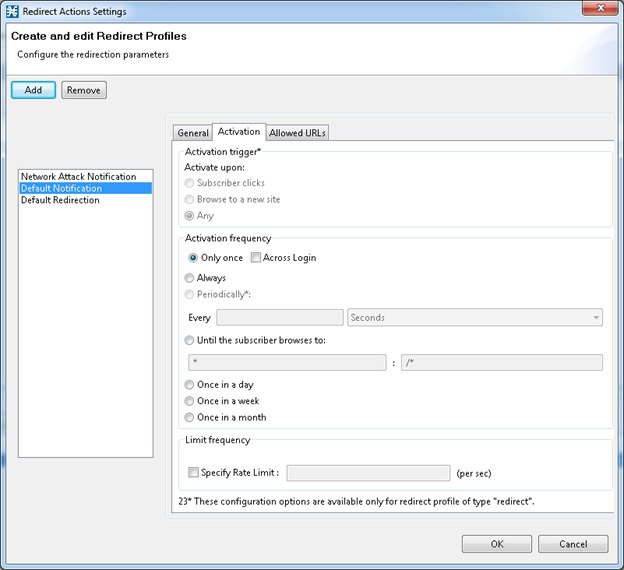 | ||
| Step 7 | Configure the frequency in which the redirection is triggered. Choose one of the Activation frequency radio buttons: | ||
| Step 8 | If you chose the
Until the subscriber browses to: radio button, enter the dismissal URL
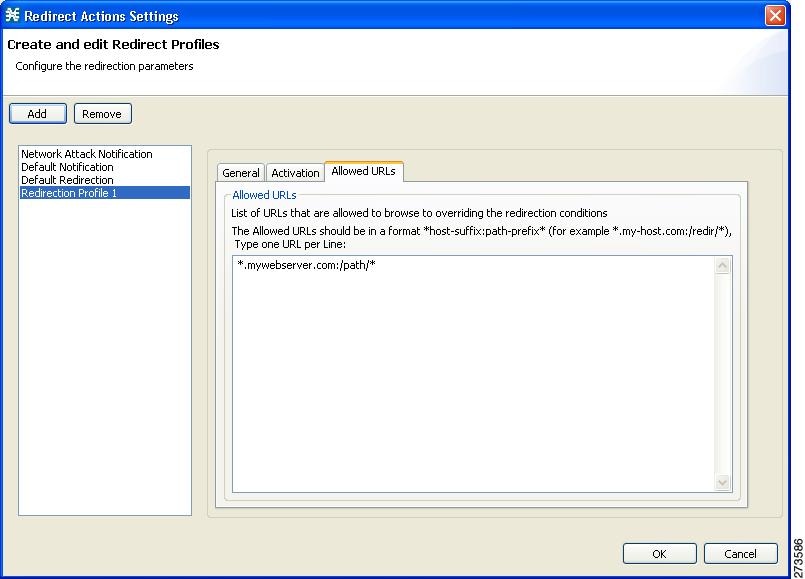
host-suffix and path-prefix in the fields provided.
| ||
| Step 9 | Click the
Allowed URLs tab.
The
Allowed URLs tab opens.
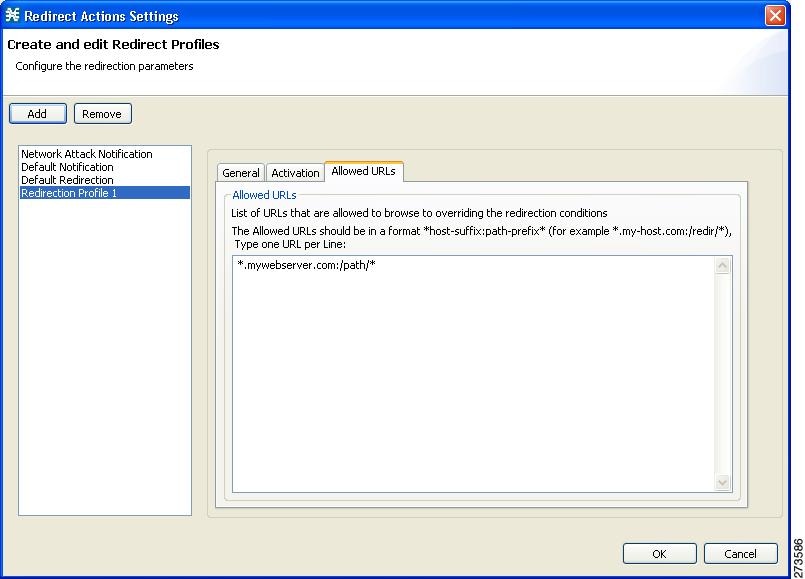 | ||
| Step 10 | Enter any allowed URLs, one per line. | ||
| Step 11 | Click OK. The Redirect Actions Settings dialog box closes. |
The notification redirect profile is added to the profile list.
Managing Subscriber Redirection Overview
The rules for a package may deny access to selected protocols. When a subscriber to the package tries to access a blocked protocol, the traffic flow can be redirected to a server where a posted web page explains the reason for the redirection. For example, a “Silver” subscriber trying to access a service available only to “Gold” subscribers. This web page can offer subscribers the opportunity to upgrade their packages. You configure which redirection profile to use when defining rules.
 Note | Redirection is not supported when unidirectional classification is enabled. |
Each redirect profile consists of a set of redirect parameters. The Cisco SCA BB supports a maximum of 128 redirect profiles, including notification redirect and redirect profiles.
- Subscriber Redirect Parameters
- Adding a Redirect Profile
- Deleting a Redirection Profile
- Adding a Set of Redirection URLs
- Deleting a Set of Redirection URLs
Subscriber Redirect Parameters
Each redirect profile of type redirect contains the following parameters:
 Note | You cannot change the name of the Default Redirection Profile. |
- Redirect profile type—Each profile must be one of two types:
- Set of Redirection URLs—A configurable set of destination URLs, to which the subscriber’s HTTP flows are redirected after redirection is activated. The redirection set can optionally include one, or several parameters appended to the destination URL including the redirect reason or subscriber ID.
- Activation trigger—The action that initiates the redirect. The activation trigger is one of the following:
- Activation
frequency—Indicates when to activate the redirect. The activation frequency is
one of the following:
- Only once—The subscriber is redirected only the first time the conditions are met. Enable the GT_GLB_RedirectOnHomePage tunable to redirect from a home page.
- Always—The subscriber is redirected every time the conditions are met.
- Periodically—The redirection is based on a periodic counter and the counter is reset after the redirection is complete.
- Triggering events
- KBytes
- Until the subscriber browses to—Every time the conditions are met, the subscriber is redirected, until the subscriber proceeds from the destination URL to a different, final URL.
For example, the entry *. some-isp.net:/redirect /* matches all the following URLs:
• www.some-isp.net/redirect/index.html
• support.some-isp.net/redirect/info/warning.asp
• noquota.some-isp.net/redirect/acknowledge.aspx?ie=UTF-8
- List of Allowed URLs—A list of URLs that are not blocked and redirected even though redirection is activated.
After redirection is activated, all HTTP flows, except flows to the destination URL and to the dismissal URL, are blocked and redirected to the destination URL. However, subscribers can be permitted to access an additional set of URLs. This is useful, for example, to give subscribers access to additional support information.
Allowed URLs have the same format as the dismissal URL. But, for Allowed URLs, you must specify the HTTP port and the port must be 80. If the URL contains any port other than 80, the URL is considered as a normal URL and is redirected.
These parameters are defined when you add a new notification redirect profile. You can modify them at any time.
-
-
Once in a day—The subscriber is redirected only the first time when the conditions are met and this also happens the first time every day.
-
Once in a week—The subscriber is redirected only the first time when the conditions are met and this also happens the first time every week.
-
Once in a Month—The subscriber is redirected only the first time when the conditions are met and this also happens the first time every month.

Note
By default "Across login " support is enabled for the above three options . Redirection History RDR will be generated every time , when the redirection condition is met . The Subscriber manager processes those RDRs and shares the redirected profile information on the next login The Redirection History RDR will be generated to reset the marked profiles, once at the end of a Day, a Week and a Month . By this way we are achieving the redirection only once in a Day , Week and Month .
-
-
Limit Frequency—Used to rate limit the number of redirections occuring per second for this redirection profile. Remaining flows will be redirect to the next new flow.
For more information, see "Subscriber Redirection" section in Cisco Subscriber Manger user guide.
For more information, see "Redirection History RDR" section in Cisco Service Control Application for Broadband reference guide and see "Configuring the Subscriber Redirection Across Login" section in Cisco SCE 10000 Software Configuration Guide
Adding a Redirect Profile
A redirect profile contains a set of redirection URLs as well as conditions in which to use the redirect feature, such as the action that triggers the redirect, or the frequency in which the redirect occurs.
| Step 1 | From the
Policies tab in the left pane, choose
Configuration >
Policies >
Subscriber Redirection.
The
Redirect Actions Settings dialog box appears.
 | ||
| Step 2 | Click Add. A new redirect profile containing the default redirection URL set is added to the redirect profile list. | ||
| Step 3 | In the Name
field, enter a unique name for the new redirect profile.
| ||
| Step 4 | Choose a URL set. | ||
| Step 5 | Click the
Activation tab.
The
Activation tab opens.
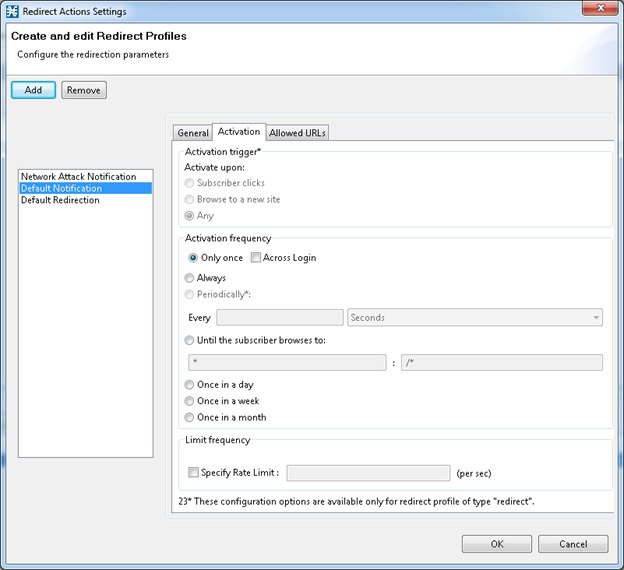 | ||
| Step 6 | Configure the activity that triggers the redirection. Choose one of the Activation trigger radio buttons: | ||
| Step 7 | To configure the frequency in which the redirection is triggered, choose one of the following activation frequency radio buttons: | ||
| Step 8 | If you selected the Periodically radio button, enter a number and an increment in the Every fields, to specify the frequency in which the redirection occurs. | ||
| Step 9 | If you selected the Until the subscriber browses to: radio button, enter the dismissal URL in the fields provided. | ||
| Step 10 | Click the
Allowed URLs tab.
 | ||
| Step 11 | Enter a URL, or multiple URLs (with HTTP port 80), that can be
browsed, overriding the redirect conditions.
| ||
| Step 12 | Click OK. The Redirect Actions Settings dialog box closes. |
The Redirection profile is added to the redirection profile list.
Deleting a Redirection Profile
You cannot delete the Default Redirection Profile.
| Step 1 | From the Policies tab in the left pane, choose Configuration > Policies > Subscriber Redirection. The Redirect Actions Settings dialog box appears. |
| Step 2 | Click the name of the profile. |
| Step 3 | Click Remove. |
| Step 4 | Click OK. The Redirect Actions Settings dialog box closes. |
The Redirection settings are saved.
Adding a Set of Redirection URLs
The Console Redirection feature supports only three protocols:
Each redirection set contains one redirection option for each of these three protocols. The system provides a default redirection set, which cannot be deleted. You can add up to 127 additional sets.
<URL>?n=<subscriber-ID>&s=<service-ID>
Optionally, the URL can contain one or multiple parameters appended to it.
| Step 1 | From the Policies tab of the left pane, choose Configuration > Policies > Subscriber Redirection. The Redirect Actions Settings dialog box appears. | ||||||||||||||||||||||||||||||||||||||||||||
| Step 2 | In the General
tab, click Edit.
The
Redirect Set Settings dialog box appears.
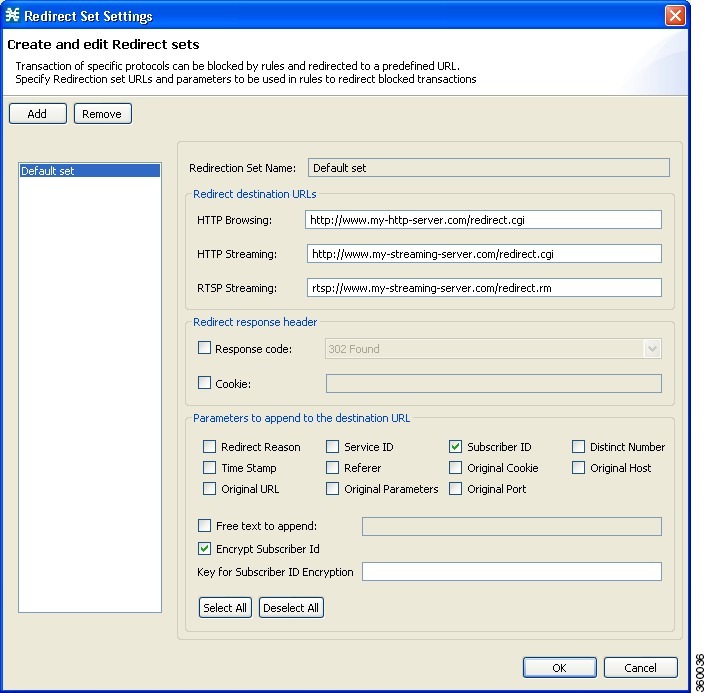 | ||||||||||||||||||||||||||||||||||||||||||||
| Step 3 | Click Add. A new redirection set containing the default redirection URLs is added. | ||||||||||||||||||||||||||||||||||||||||||||
| Step 4 | In the
Redirection Set Name field, enter unique name for the new redirection set.
| ||||||||||||||||||||||||||||||||||||||||||||
| Step 5 | Enter new values
in the Redirection destination URLs section of the new redirection set.
| ||||||||||||||||||||||||||||||||||||||||||||
| Step 6 | To include a response code, check the Response code check box, and choose a response code from the drop-down list. see Table 10-2 for a listing and description of the redirection parameters. | ||||||||||||||||||||||||||||||||||||||||||||
| Step 7 | To include a cookie, check the Cookie check box, and enter a value. see Table for a listing and description of the redirection parameters. | ||||||||||||||||||||||||||||||||||||||||||||
| Step 8 | Check the check boxes of any parameters you wish to append to
the destination URL see Table for a listing and description of the redirection
parameters.
The Subscriber ID in the redirected URL can be encrypted by checking the Encrypt Subscriber ID check box. After you check the Encrypt Subscriber ID check box, enter your encryption key in the Key for the Subscriber ID Encryption field. The key must contain 32 hexadecimal characters. Subscriber ID encryption is applicable only for Cisco SCE 10000 platforms. If you check the Free text to append check box, enter text into the text box to append to the URL. see Table 10-2 for a listing and description of the redirection parameters. The examples in Table is based on the following URL redirection: http:// <URL> ?n=N/A&reason=2&s=119&id=0:10&ts=1327285422&str=this is free text to append content&referer=&cookie=&host= <URL> &url=/p-cube.htm¶ms=
| ||||||||||||||||||||||||||||||||||||||||||||
| Step 9 | Click OK. |
Your settings are saved and the Redirect Set Settings dialog box closes.
 Note | Keep the total number of characters appended to the redirect URL below 1200. To keep it below 1200, we recommend that you enable only the required parameters under the Parameters to append to the destination URL pane. |
Deleting a Set of Redirection URLs
| Step 1 | From the Policies tab of the left pane, choose Configuration > Policies > Subscriber Redirection. The Redirect Actions Settings dialog box appears. |
| Step 2 | In the General tab, click Edit. The Redirect Set Settings dialog box appears. |
| Step 3 | Click the name of the redirection set. |
| Step 4 | Click Remove . |
| Step 5 | Click OK. The Redirect Set Settings dialog box closes. |
The Redirection settings are saved.
Managing the System Settings Overview
The Console allows you to determine various system parameters that control:
System Operational Mode
The operational mode of the system defines how the system handles network traffic.
 Note | Each rule has its own operational mode (state). If this differs from the system mode, the “lower” of the two modes is used. For example, if a rule is enabled, but the system mode is report-only, the rule generates only RDRs. |
The three operational modes are:
- Full Functionality—The system enforces active rules on the network traffic and performs reporting functions (that is, generates RDRs).
- Report Only—The system generates RDRs only. No active rule enforcement is performed on the network traffic.
- Transparent—The system does not generate RDRs and does not enforce active rules on the network traffic.
Setting the Operational and Topological Modes of the System
| Step 1 | From the
Policies tab of the left pane, choose
.
The System Settings dialog box appears. |
| Step 2 | Select one of the System Operational Mode radio buttons: |
| Step 3 | To change the
routing classification mode, check or uncheck the
Enable
the Asymmetric Routing Classification Mode check box.
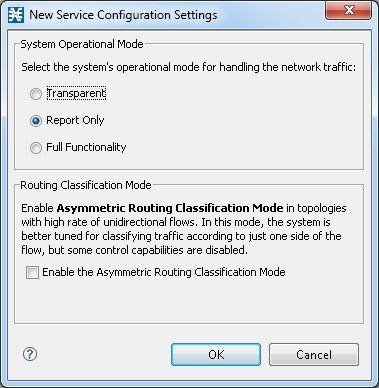
|
| Step 4 | To add the flavors in the asymmetric mode, check the Enable the Asymmetric Routing Classification Mode with Flavors check box before setting the System Operational Mode. |
| Step 5 | To enable the
Asymmetric
Routing Classification Mode with Flavors:
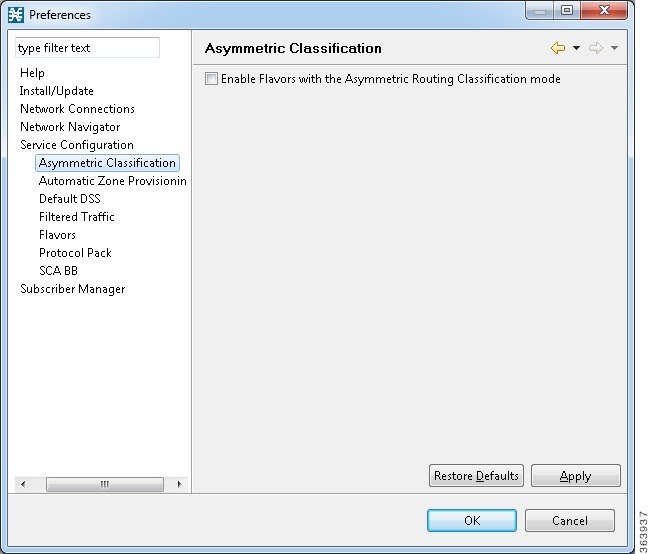 |
| Step 6 | Click
OK.
The System Settings dialog box closes. The new System Mode setting is saved. |
Asymmetric Routing Classification Mode
Enabling unidirectional classification significantly improves classification accuracy when the Cisco SCE platform is deployed in an environment with a high rate of unidirectional flows.
Unsupported Features
The following Cisco SCA BB features are not supported when unidirectional classification is enabled:
- Flavors
- External quota provisioning
- Subscriber notification
- Redirection
- Flow Signaling RDRs
- Content filtering
- VAS traffic forwarding
When unidirectional classification is enabled, the service configuration editor indicates (in the Problems View) if the service configuration is consistent with the features that are supported in this mode.
The following features, which are not part of the service configuration, are also affected when unidirectional classification is enabled:
- Subscriber-Aware Mode (a mode in which subscriber information is dynamically bound to the IP address currently in use by the subscriber) is not supported.
- Enhanced flow open mode must be enabled.
The system gives no indication if the state of the above features is consistent with the state of the routing classification mode.
Protocol Classification
When unidirectional classification is enabled, protocol classification is performed in the normal way except for unidirectional UDP flows. Because it is impossible to know the server side of a unidirectional UDP flow, Cisco SCA BB tries to classify the protocol using the destination port of the first packet; if no exact match is found, Cisco SCA BB tries to classify the protocol using the source port.
Switching to Asymmetric Routing Classification Mode
If you create a service configuration in symmetric mode and switch to asymmetric routing classification mode:
- Flavors are not used for classification.
- Periodic quota management mode is used.
- Data is not lost when you switch to asymmetric routing classification mode, but you cannot apply the service configuration to a Cisco SCE platform until all unsupported features are removed from the service configuration.
Switching from Asymmetric Routing Classification Mode
If you create a service configuration in asymmetric routing classification mode:
- The Suspected Session Rate is set equal to the Session Rate for all anomaly detectors.
- No flavors are created in the default service configuration, and no service elements have specified flavors.
- The quota management mode is periodic, with a daily aggregation period.
- Asymmetric routing classification mode limitations remain if you switch to symmetric mode. To change them, you must edit the service configuration.
Asymmetric Routing Classification Mode with Flavors
Enabling unidirectional classification with flavors significantly associate the flavors to specific services and those flavors are updated to respective lookup tables when applying the service configuration to a Cisco SCE platform.
Unsupported Features
The following Cisco SCA BB features are not supported when unidirectional classification with flavors is enabled:
Advanced Service Configuration Options
Advanced service configuration options control the more sophisticated and less frequently changed attributes of the system. It is recommended that you do not change these options.
The Advanced Service Configuration Properties
| Property | Default Value | Description | ||
|---|---|---|---|---|
|
Add On Package |
||||
|
Enable Add On Package |
FALSE |
Enables addition of the Add On Packages |
||
|
Bandwidth Management |
||||
|
Level of BWC enforcement on networking flows of P2P and IM applications. |
SCE to use Default Service BWCs. |
Specifies the level of BWC enforcement on networking flows of P2P and IM applications. |
||
|
Use Global Bandwidth Management in Virtual Links Mode |
FALSE |
Specifies whether to use the Global Bandwidth Management in Virtual Links Mode. |
||
|
Classification |
||||
|
Apply this order of priority between different criteria for service classification |
Zone > Flavor > Protocol > Init-Side |
Specifies the order of priority between different criteria for service classification. Values are: |
||
|
Character '/' denotes absence of Params part in URL |
TRUE |
Specifies that the character '/' is taken as default value when Params field is left empty. |
||
|
ClickStream Event recognition |
TRUE |
Specifies whether to recognize ClickStream Events. |
||
|
Enable sending ‘404, Page Not Found’ upon blocking |
FALSE |
Specifies whether to send ‘404, Page Not Found’ upon blocking. |
||
|
Guruguru detailed inspection mode enabled |
FALSE |
The Guruguru protocol is used by the Guruguru file-sharing application popular in Japan. Cisco SCA BB provides two inspection modes for classification of this protocol: |
||
|
Kuro detailed inspection mode enabled |
FALSE |
The Kuro protocol is used by the Kuro file-sharing application popular in Japan. Cisco SCA BB provides two inspection modes for classification of this protocol: |
||
|
Number of HTTP GET detections |
1 |
Specifies the number of HTTP GET detections. The Cisco SCE classifies the HTTP based on the number of GET requests configured. Range is 1 to 65535, and the default value is 1.
|
||
|
Soribada detailed inspection mode enabled |
FALSE |
The Soribada protocol is used by the Soribada file-sharing application popular in Japan. Cisco SCA BB provides two inspection modes for classification of this protocol: |
||
|
TCP destination port signatures |
1720:H323 |
TCP destination port numbers for signatures that require a port hint for correct classification. Valid values are comma-separated items, each item in the form <port-number>:<signature-name>. Applicable signature names are: H323, Radius Access, Radius Accounting, and DHCP. |
||
|
UDP destination port signatures |
67:DHCP, 68:DHCP, 1812:Radius Access, 1645:Radius Access, 1813:Radius Accounting, 1646:Radius Accounting |
UDP destination port numbers for signatures that require a port hint for correct classification. Valid values are comma-separated items, each item in the form <port-number>:<signature-name>. Applicable signature names are: H323, Radius Access, Radius Accounting, and DHCP. |
||
|
UDP ports for which flow should be opened on the first IPv6 packet |
5060, 5061, 69, 546, 547, 2427, 2727, 9201, 9200, 123, 1900, 5190, 10000 |
Enhanced flow-open mode is disabled on the specified UDP ports to allow classification according to the first IPv6 packet of the flow. Effective with Cisco SCE Release 4.0.0, you can use a maximum of 21 unique ports for IPv4 and IPv6 addresses on the Cisco SCE 8000 devices. Enhanced flow-open mode is disabled on the specified UDP ports to allow the classification according to the first IPv6 packet of the flow. You can use a maximum of 38 unique ports for IPv4 and IPv6 addresses on the Cisco SCE 10000 devices. |
||
|
UDP ports for which flow should be opened on the first packet |
5060, 5061, 67, 68, 69, 1812, 1813, 1645, 1646, 2427, 2727, 9201, 9200, 123, 1900, 5190, 10000 |
Enhanced flow-open mode is disabled on the specified UDP ports to allow the classification according to the first packet of the flow. Effective with Cisco SCE Release 4.0.0, you can use a maximum of 21 unique ports for IPv4 and IPv6 addresses on the Cisco SCE 8000 devices. Enhanced flow-open mode is disabled on the specified UDP ports to allow the classification according to the first packet of the flow. You can use a maximum of 38 unique ports for IPv4 and IPv6 addresses on the Cisco SCE 10000 devices. |
||
|
UDP source port signatures |
1812:Radius Access, 1645:Radius Access, 1813:Radius Accounting, 1646:Radius Accounting |
UDP source port numbers for signatures that require a port hint for correct classification. Valid values are comma-separated items, each item in the form <port-number>:<signature-name>. Applicable signature names are: H323, Radius Access, Radius Accounting, and DHCP. |
||
|
V-Share detailed inspection mode enabled |
FALSE |
The V-Share protocol is used by the V-Share file-sharing application popular in Japan. Cisco SCA BB provides two inspection modes for classification of this protocol: |
||
|
Winny detailed inspection mode enabled |
FALSE |
The Winny P2P protocol is used by the Winny file-sharing application popular in Japan. Cisco SCA BB provides two inspection modes for classification of this protocol: |
||
|
WinnyP aggressive classification enabled |
FALSE |
— |
||
|
WinnyP classification enabled |
FALSE |
— |
||
|
Malicious Traffic |
||||
|
Malicious Traffic RDRs enabled |
TRUE |
Specifies whether to generate Malicious Traffic RDRs. |
||
|
Number of seconds between Malicious Traffic RDRs on the same attack |
60 |
A Malicious Traffic RDR is generated when an attack is detected. Malicious Traffic RDRs are then generated periodically, at user-configured intervals, for the duration of the attack. |
||
|
TCP port that should remain open for Subscriber Notification |
80 |
You can choose to block flows that are part of any detected network attack, but this may hinder subscriber notification of the attack. The specified TCP port is not blocked to allow notification of the attack to be sent to the subscriber. |
||
|
Multi Stage Classification |
||||
|
Blocking |
FALSE |
Specifies whether to block the sub services under the main service. |
||
|
Enable |
TRUE |
Specifies whether to enable the sub service classification of a service. Multi stage classification describes the application level services that can be enabled or disabled. By default sub service classification of the services is enabled. For example, Google talk service contains Google talk file transfer, Google talk Networking, Google talk VoIP as sub services. |
||
|
Policy Check |
||||
|
Ongoing policy check mode enabled |
TRUE |
Specifies whether policy changes affect flows that are already open. |
||
|
Time to bypass between policy checks (seconds) |
30 |
Maximum time (in seconds) that may pass before policy changes affect flows that are already open. |
||
|
Quota Management |
||||
|
Grace period before first breach (seconds) |
2 |
The time (in seconds) to wait after a quota limit is breached before the breach action is performed. Policy servers should use this period to provision quota to a subscriber that just logged in. |
||
|
Length of the time frame for quota replenish scatter (minutes) |
0 |
The size of the window across which to scatter the periodic quota replenishment randomly. |
||
|
Time to bypass between policy checks for quota limited flows |
30 |
Maximum time (in seconds) that may pass before a quota breach affects flows that are already open. |
||
|
Volume to bypass between policy checks for quota limited flows |
0 |
Maximum flow volume (in bytes) that may pass before a quota breach affects flows that are already open. A value of zero means that unlimited volume may pass. |
||
|
Redirection |
||||
|
Adds original host to redirection URL |
FALSE |
Specifies whether to add the original host to the redirection URL. |
||
|
Adds original URL to redirect URL |
FALSE |
Specifies whether to add the original URL to the redirection URL. |
||
|
Maximum redirect URL Length |
500 |
Specifies the maximum length of the redirect URL. |
||
|
Redirect subscriber ID format |
Complete - n=<user>@<realm> |
Specifies the redirect subscriber ID format to be configured. Valid Options are:
If the subscriber name does not match the format of <user>@<realm>, the full subscriber name is appended to the URL, regardless of the redirect subscriber format configured. |
||
|
Reporting |
||||
|
Extract Full User Agent details |
FALSE |
Specifies whether to extract full user agent details. |
||
|
Flow Accounting RDRs enabled |
FALSE |
Specifies whether to generate Flow Accounting RDRs. |
||
|
Flow Accounting RDRs interval for each Service (in seconds) |
60 |
Specifies the interval at which the Flow Accounting RDRs are generated for each service. |
||
|
Flow Accounting RDRs limit per second |
100 |
Specifies the limit of Flow Accounting RDRs to be generated each second. |
||
|
Hide Subscriber IP and ID in RDRs |
FALSE |
Specifies whether to hide the IP address and Subscriber ID in the following RDRs:
See the Cisco Service Control for Broadband Reference Guide for details on the RDRs. |
||
|
Media Flow RDRs enabled |
TRUE |
Specifies whether to generate Media Flow RDRs. |
||
|
Minimal volume for generating HTTP Transaction Usage RDR (bytes) |
0 |
Specifies the minimum volume for generating HTTP Transaction Usage RDR. |
||
|
Minimal volume for generating RTSP Transaction Usage RDR (bytes) |
0 |
Specifies the minimum volume for generating RTSP Transaction Usage RDR. |
||
|
Minimal volume for generating Video Transaction Usage RDR (bytes) |
1024000 |
Specifies the minimum volume for generating Video Transaction Usage RDRs. |
||
|
Video Transaction Usage RDRs enabled |
TRUE |
Specifies whether to generate Video Transaction Usage RDRs. |
||
|
Enable VSA Fields for Subscriber, HTTP Transaction, and Video Transaction RDRs |
FALSE |
Specifies whether to generate VSA fields for Subscriber, HTTP Transaction, and Video Transaction RDRs. |
||
|
Subscriber Accounting RDR enabled |
||||
Editing Advanced Service Configuration Options
| Step 1 | From the Policies tab of the left pane, choose Configuration > Policies > System Settings . |
| Step 2 | Click the
Advanced Options tab.
The Advanced Options tab opens. 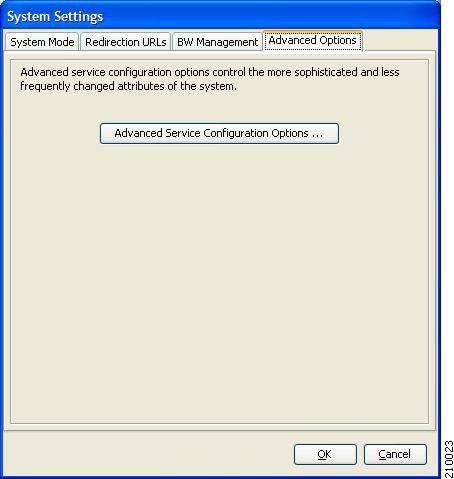 |
| Step 3 | Click Advanced
Service Configuration Options .
The Advanced Service Configuration Options dialog box opens. 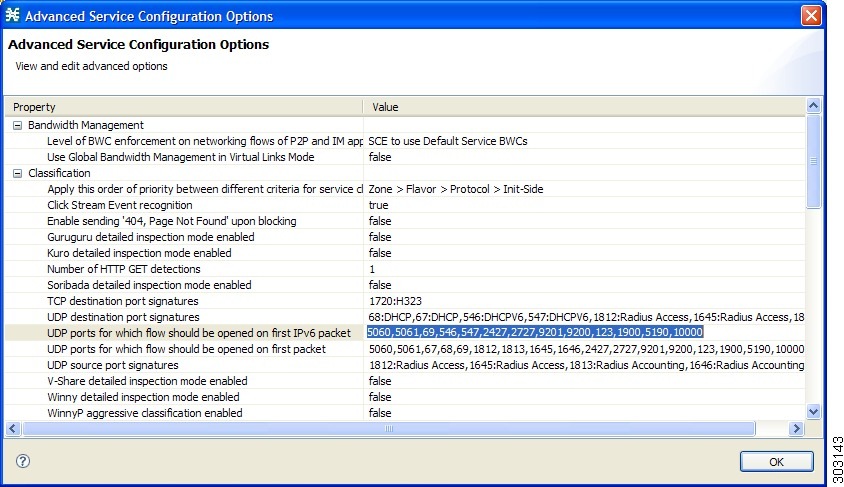 |
| Step 4 | Make your changes to the configuration options. |
| Step 5 | Click OK .
The Advanced Service Configuration Options dialog box closes. The changes to the advanced options are saved. |
| Step 6 | Click OK .
The System Settings dialog box closes. |
Managing VAS Settings Overview
Value Added Service (VAS) settings includes the following features:
- Traffic mirroring—Traffic mirroring allows using the Cisco SCE to mirror a portion of the traffic based on its application and subscriber awareness. Traffic to be mirrored continues forwarding as is, and copies of the packets are sent to the corresponding VAS VLAN, thereby minimizing traffic.
- Traffic forwarding—Traffic forwarding servers allows you to use an external expert system (VAS server) for additional traffic processing, such as intrusion detection and content filtering to subscribers. After processing, flows are sent back to the Cisco SCE platform, which then sends them to their original destinations.
The flows to be forwarded are selected based on the subscriber package and the flow type (IP protocol type and destination port number).
VAS mirroring has the following limitations:
- The Cisco SCE 8000Cisco SCE 10000 support traffic mirroring.
- Traffic mirroring is supported on any Cisco SCE platform that has at least 2 ports.
- A Cisco SCE 8000 can contain 64 distinct VLANs.
- A Cisco SCE 10000 can contain 64 distinct VLANs.
VAS forwarding has the following limitations:
- Only the Cisco SCE 8000 Cisco SCE 10000 platforms support VAS traffic forwarding.
- A single Cisco SCE platform can support up to eight VAS servers.
- A service configuration can contain up to 64 traffic-forwarding tables.
- A traffic-forwarding table can contain up to 64 table parameters.
- VAS traffic forwarding is not supported when unidirectional classification is enabled.
 Note | Because of the complexity of the VAS settings features, VAS flows are not subject to global bandwidth control. |
To use VAS traffic forwarding:
- You must configure VAS services on the Cisco SCE platform.
- You must also assign the VAS traffic-forwarding tables to packages in the Advanced tab of the Edit Packages dialog. VAS traffic-forwarding is based on per-package configuration of where to forward what traffic.
- Enabling VAS Traffic Forwarding
- Enabling VAS Traffic Mirroring
- Renaming VAS Server Groups
- Configuring VAS Traffic-Mirroring
- Viewing VAS Traffic-Forwarding Tables
- Deleting VAS Traffic-Forwarding Tables
- Adding VAS Traffic-Forwarding Tables
- Managing VAS Table Parameters Overview
Enabling VAS Traffic Forwarding
By default, VAS traffic forwarding is disabled. You can enable it at any time.
 Note | VAS traffic forwarding is not supported when unidirectional classification is enabled. |
| Step 1 | From the
Policies tab of the left pane, choose
Configuration >
Policies >
VAS
Settings.
The VAS
Settings dialog box appears.
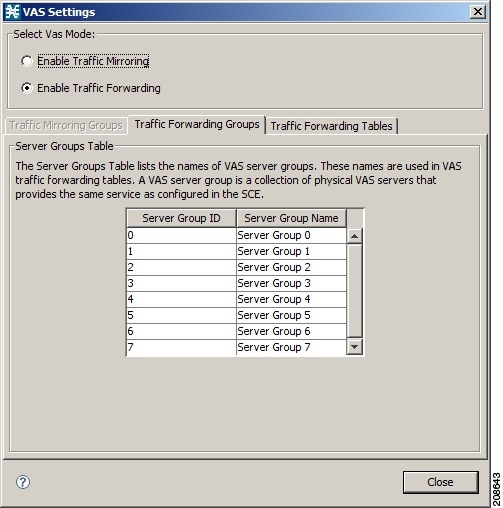 | ||
| Step 2 | Click the Enable
Traffic Forwarding radio button.
| ||
| Step 3 | Click OK. | ||
| Step 4 | Click Close. The VAS Settings dialog box closes. |
Enabling VAS Traffic Mirroring
Traffic Mirroring in enabled and configured in the VAS Setting dialog box. However, you configure which server group to use when defining rules.
| Step 1 | From the
Policies tab of the left pane, choose
Configuration >
Policies >
VAS
Settings.
The VAS
Settings dialog box appears.
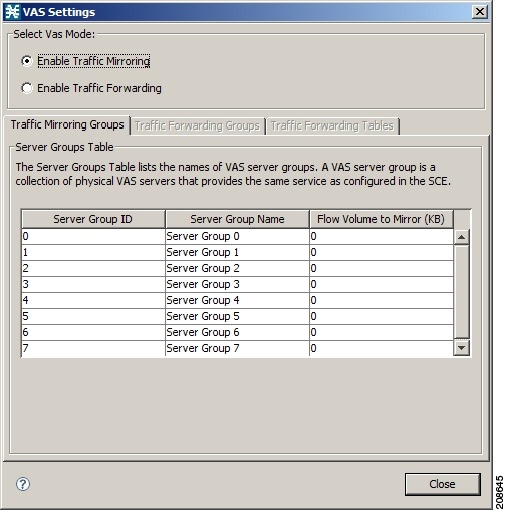 |
| Step 2 | Choose the Enable Traffic Mirroring radio button. A VAS warning message appears. |
| Step 3 | Click OK. |
| Step 4 | Click
Close.
The VAS Settings dialog box closes. |
Renaming VAS Server Groups
A Cisco SCE platform can forward flows to up to eight different VAS server groups. By default, the eight server groups are named “Server Group n”, where n takes a value from 0 to 7. Give the server groups meaningful names; the names you give appears in the drop-down list in the Control and Breach Handling tabs of the Add Rule to Package dialog box (see “How to Set Advanced Package Options” section) and in the Server Group field of the table parameters added to each traffic-forwarding table (see “Managing VAS Table Parameters” section).
| Step 1 | From the
Policies tab of the left pane, choose Configuration > Policies > VAS
Settings .
The VAS Settings dialog box appears. |
| Step 2 | In the table in the Server Groups Table area, double-click in a cell containing a server group name. |
| Step 3 | Enter a meaningful name in the cell. |
| Step 4 | Repeat Step 2
and Step 3 for other server groups you wish to rename.
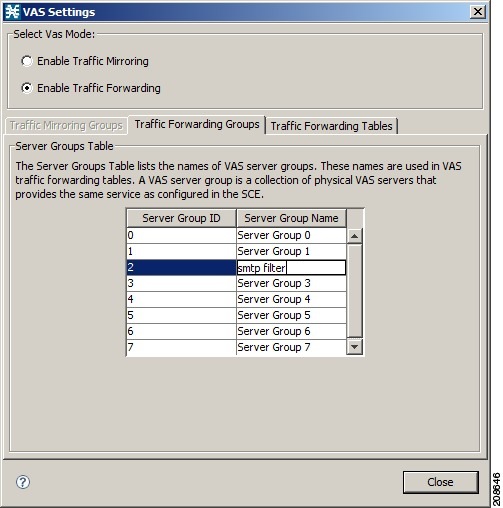 |
| Step 5 | Click Close . The VAS Settings dialog box closes. |
Configuring VAS Traffic-Mirroring
| Step 1 | From the
Policies tab of the left pane, choose Configuration > Policies > VAS
Settings.
The VAS Settings dialog box appears. 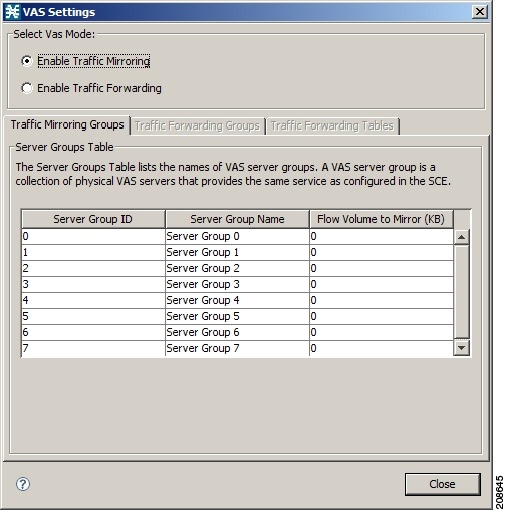 |
| Step 2 | Click the Enable Traffic Forwarding radio button. |
| Step 3 | For each server group, in the Flow Volume to Mirror (KB) column, enter the maximum amount of volume to mirror, in KB. |
| Step 4 | Click Close . The VAS Settings dialog box closes. |
Viewing VAS Traffic-Forwarding Tables
Cisco SCA BB decides whether a flow passing through a Cisco SCE platform should be forwarded to a VAS server group based on a traffic-forwarding table. Each entry (table parameter) in a traffic-forwarding table defines to which VAS server group the specified flows should be forwarded.
| Step 1 | From the Policies tab of the left pane, choose Configuration > Policies > VAS Settings. The VAS Settings dialog box appears. |
| Step 2 | Click the Enable Traffic Forwarding radio button. |
| Step 3 | Click the
Traffic
Forwarding Tables tab.
The Traffic Forwarding Tables tab opens. A list of all traffic-forwarding tables is displayed in the Traffic Forwarding Tables area. |
| Step 4 | Click a table in
the list of traffic-forwarding tables to display its table parameters.
A list of
all table parameters defined for this traffic-forwarding table opens in the
Table Parameters tab.
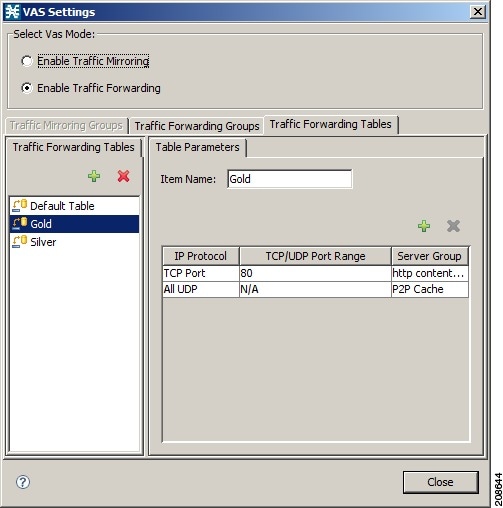 |
| Step 5 | Click Close .
The VAS Settings dialog box closes. |
Deleting VAS Traffic-Forwarding Tables
You can delete all user-created traffic-forwarding tables. The default traffic-forwarding table cannot be deleted.
 Note | A traffic-forwarding table cannot be deleted while it is associated with a package. |
| Step 1 | From the
Policies tab of the left pane, choose
.
The VAS Settings dialog box appears. |
| Step 2 | Click the Enable Traffic Forwarding radio button. |
| Step 3 | Click the Traffic Forwarding Tables tab. |
| Step 4 | From the list of traffic-forwarding tables in the Traffic Forwarding Tables area, select a table. |
| Step 5 | Click the Delete
(158940.jpg) icon.
A VAS Warning message appears. 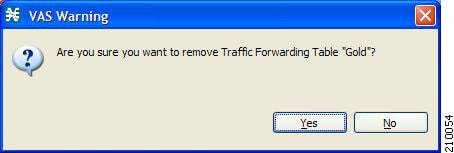 |
| Step 6 | Click
Yes.
The selected table is deleted and is no longer displayed in the list of traffic-forwarding tables. |
| Step 7 | Click
Close .
The VAS Settings dialog box closes. |
Adding VAS Traffic-Forwarding Tables
A default traffic-forwarding table is included in the service configuration. You can add up to 63 more traffic-forwarding tables, and then assign different traffic-forwarding tables to different packages.
| Step 1 | From the Policies tab in the left pane, choose Configuration > Policies > VAS Settings. The VAS Settings dialog box appears. |
| Step 2 | Click the Enable Traffic Forwarding radio button. |
| Step 3 | Click the
Traffic
Forwarding Tables tab.
The
Traffic Forwarding Tables tab opens.
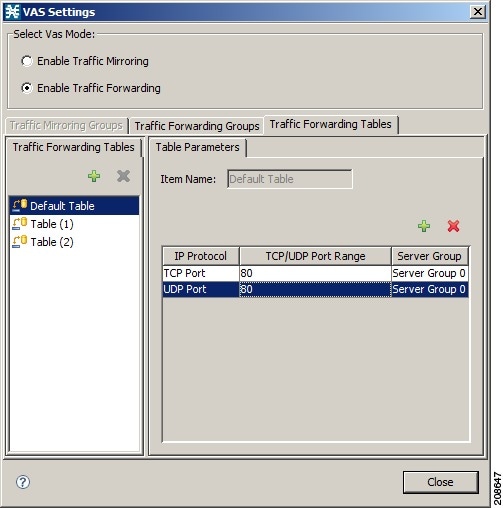 |
| Step 4 | In the Traffic
Forwarding Tables area, click the Add (158725.jpg) icon.
A new
table named Table (n), where n is a value from 1 through 63, is added to the
list of traffic-forwarding tables in the Traffic Forwarding Tables area.
The table name is also displayed in the Item Name box in the Table Parameters tab. |
| Step 5 | In the Item Name field, enter a unique and relevant name for the traffic-forwarding table. |
You can now add table parameters to the new traffic-forwarding table, see “How to Add VAS Table Parameters” section.
Managing VAS Table Parameters Overview
A table parameter is an IP protocol type, an associated TCP/UDP port (where applicable), and a VAS server group or a range of IP addresses.
A traffic-forwarding table is a collection of related table parameters.
A traffic-forwarding table can contain up to 64 table parameters.
Adding VAS Table Parameters
| Step 1 | From the Policies tab in the left pane, choose Configuration > Policies > VAS Settings . The VAS Settings dialog box appears. | ||||||||||||||||
| Step 2 | Click the Enable Traffic Forwarding radio button. | ||||||||||||||||
| Step 3 | Click the Traffic Forwarding Tables tab. The Traffic Forwarding Tables tab opens. | ||||||||||||||||
| Step 4 | From the list of traffic-forwarding tables in the Traffic Forwarding Tables area, select a table. | ||||||||||||||||
| Step 5 | In the Traffic Parameters tab, click the Add (158725.jpg) icon. A new table parameter is added to the list of table parameters in the Table
Parameters tab.
You can now edit the new table parameter, as described in the following section. | ||||||||||||||||
| Step 6 | Click Close . The VAS Settings dialog box closes. |
Editing VAS Table Parameters
| Step 1 | From the Policies tab in the left pane, choose Configuration > Policies > VAS Settings. The VAS Settings dialog box appears. |
| Step 2 | Click the Enable Traffic Forwarding radio button. |
| Step 3 | Click the Traffic Forwarding Tables tab. The Traffic Forwarding Tables tab opens. |
| Step 4 | From the list of traffic-forwarding tables in the Traffic Forwarding Tables area, select a table. |
| Step 5 | In the table in the Table Parameters tab select a protocol, port, and server group. |
| Step 6 | Click in a cell
in the IP Protocol column, and, from the drop-down list that opens, select an
IP protocol type.
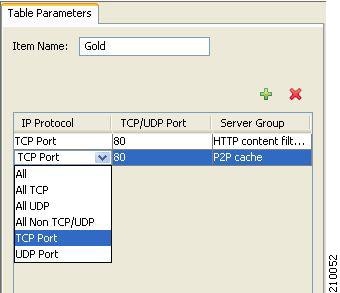 If you select All, All TCP, All UDP, or All Non TCP/UDP, “N/A” appears in the TCP/UDP Port cell when you move to another cell in the table. |
| Step 7 | If you selected TCP Port or UDP Port, double-click in the cell in the TCP/UDP Port Range column, and enter the port number or a range of ports. |
| Step 8 | Click in the
cell in the Server Group column, and, from the drop-down list that opens,
select a server group.
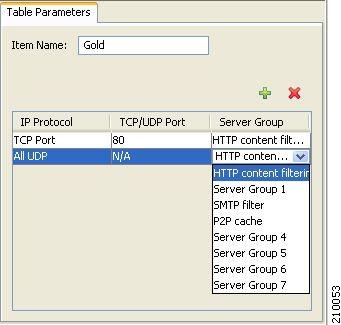 |
| Step 9 | Click Close.
The VAS Settings dialog box closes. |
Deleting VAS Table Parameters
| Step 1 | From the
Policies tab in the left pane, choose
.
The VAS Settings dialog box appears. |
| Step 2 | Click the Enable Traffic Forwarding radio button. |
| Step 3 | Click the
Traffic
Forwarding Tables tab.
The Traffic Forwarding Tables tab opens. |
| Step 4 | From the list of traffic-forwarding tables in the Traffic Forwarding Tables area, select a table. |
| Step 5 | From the list of table parameters in the Table Parameters tab, select a table parameter. |
| Step 6 | Click the Delete
( )
icon. )
icon.
The selected table parameter is deleted and is no longer displayed in the list of table parameters. |
| Step 7 | Click Close .
The VAS Settings dialog box closes. |
Managing the Protected URL Database
The Cisco SCE Protected URL Database is a database that contains a blacklist, a list of websites that are considered off limits or dangerous. You can configure the Cisco SCE to apply a specific action, such as blocking a site, when a subscriber attempts to access a site listed on the blacklist.
The database is encrypted so that no one, including the operator, can view the blacklist. The blacklist is managed on the Cisco SCE and cannot be withdrawn to the management PC.
RDRs are created when a subscriber attempts to access a link included in the blacklist. However, the RDRs do not contains the URL or Host information of the site.
To enable the blacklist feature:
What to Do Next
For more information about the Protected URL Database, see the Cisco Service Control URL Blacklisting Solution Guide .
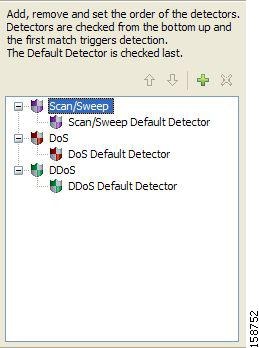
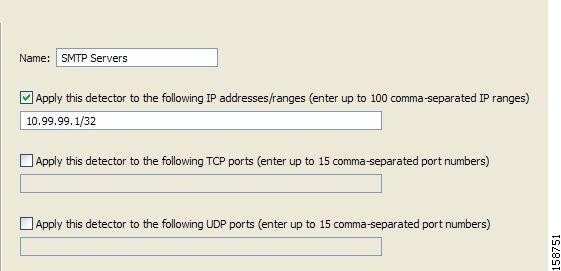
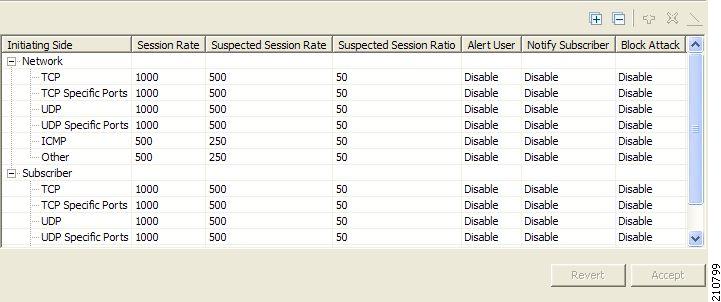
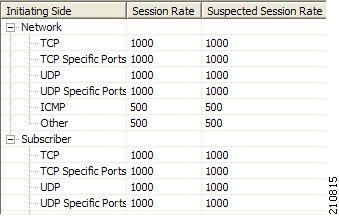
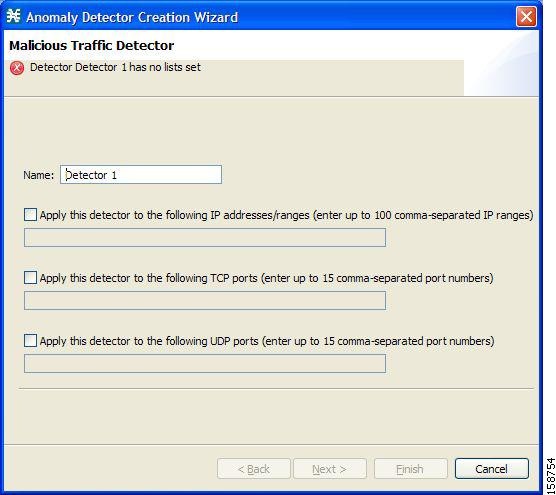
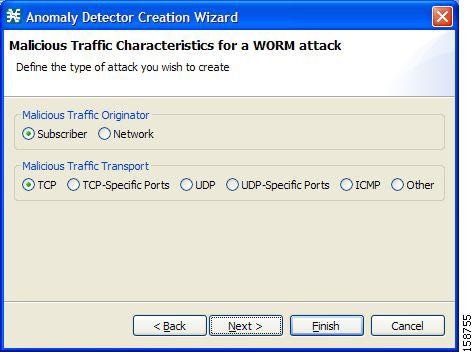
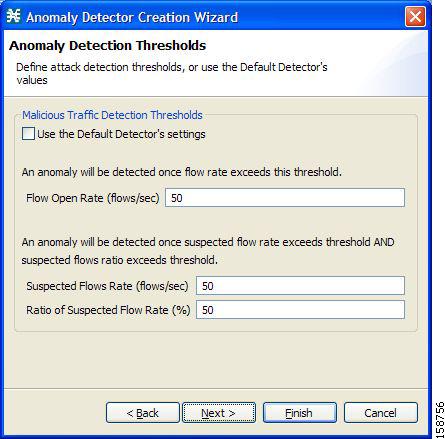
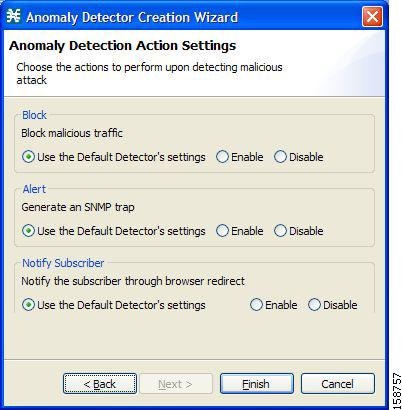
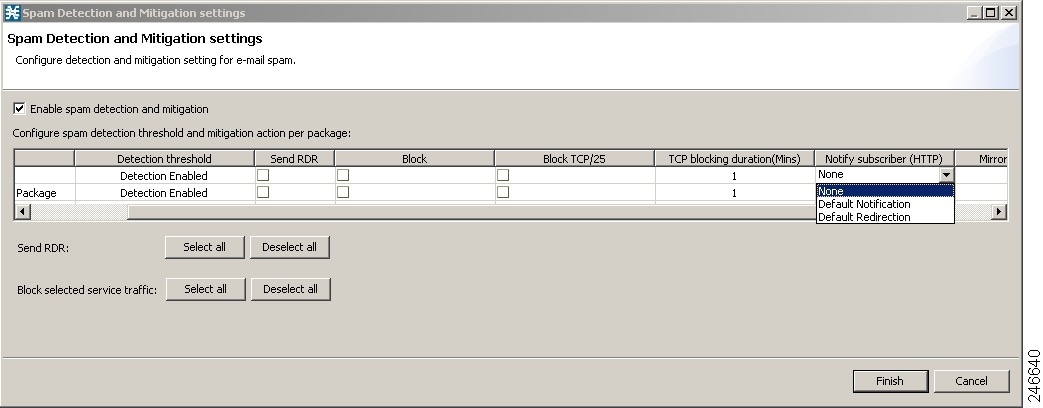
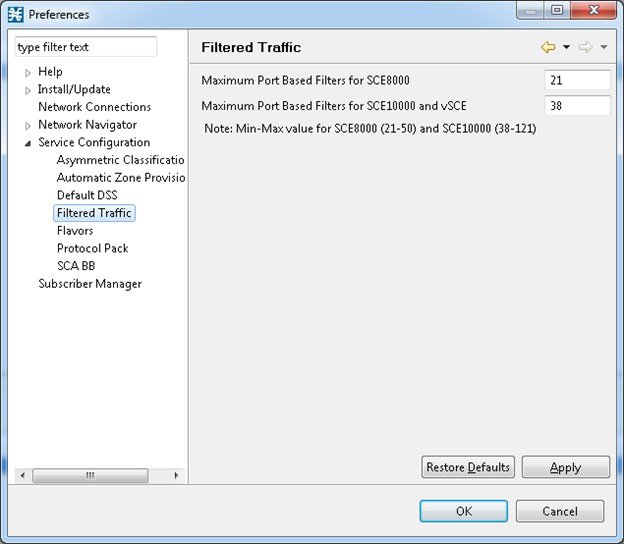
 Feedback
Feedback