Contents
- MPLS VPN--Route Target Rewrite
- Finding Feature Information
- Prerequisites for MPLS VPN--Route Target Rewrite
- Restrictions for MPLS VPN--Route Target Rewrite
- Information About MPLS VPN--Route Target Rewrite
- Route Target Replacement Policy
- Route Maps and Route Target Replacement
- How to Configure MPLS VPN--Route Target Rewrite
- Configuring a Route Target Replacement Policy
- Applying the Route Target Replacement Policy
- Associating Route Maps with Specific BGP Neighbors
- Refreshing BGP Session to Apply Route Target Replacement Policy
- Troubleshooting Tips
- Verifying the Route Target Replacement Policy
- Troubleshooting Your Route Target Replacement Policy
- Configuration Examples for MPLS VPN--Route Target Rewrite
- Configuring Route Target Replacement Policies Examples
- Applying Route Target Replacement Policies Examples
- Associating Route Maps with Specific BGP Neighbor Example
- Refreshing the BGP Session to Apply the Route Target Replacement Policy Example
- Additional References
- Feature Information for MPLS VPN--Route Target Rewrite
- Glossary
MPLS VPN--Route Target Rewrite
The MPLS VPN--Route Target Rewrite feature allows the replacement of route targets on incoming and outgoing Border Gateway Protocol (BGP) updates. Typically, Autonomous System Border Routers (ASBRs) perform the replacement of route targets at autonomous system boundaries. Route Reflectors (RRs) and provider edge (PE) routers can also perform route target replacement.
The main advantage of the MPLS VPN--Route Target Rewrite feature is that it keeps the administration of routing policy local to the autonomous system.
- Finding Feature Information
- Prerequisites for MPLS VPN--Route Target Rewrite
- Restrictions for MPLS VPN--Route Target Rewrite
- Information About MPLS VPN--Route Target Rewrite
- How to Configure MPLS VPN--Route Target Rewrite
- Configuration Examples for MPLS VPN--Route Target Rewrite
- Additional References
- Feature Information for MPLS VPN--Route Target Rewrite
- Glossary
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the Feature Information Table at the end of this document.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
Prerequisites for MPLS VPN--Route Target Rewrite
- You should know how to configure Multiprotocol Virtual Private Networks (MPLS VPNs).
- You need to configure your network to support interautonomous systems with different route target (RT) values in each autonomous system.
- You need to identify the RT replacement policy and target router for each autonomous system.
Restrictions for MPLS VPN--Route Target Rewrite
You can apply multiple replacement rules using the route-map continue clause. The MPLS VPN--Route Target Rewrite feature does not support the continue clause on outbound route maps.
Information About MPLS VPN--Route Target Rewrite
Route Target Replacement Policy
Routing policies for a peer include all configurations that may impact inbound or outbound routing table updates. The MPLS VPN Route Target Rewrite feature can influence routing table updates by allowing the replacement of route targets on inbound and outbound BGP updates. Route targets are carried as extended community attributes in BGP Virtual Private Network IP Version 4 (VPNv4) updates. Route target extended community attributes are used to identify a set of sites and VPN routing and forwarding (VRF) instances that can receive routes with a configured route target.
In general, ASBRs perform route target replacement at autonomous system borders when the ASBRs exchange VPNv4 prefixes. You can also configure the MPLS VPN Route Target Rewrite feature on PE routers and RR routers.
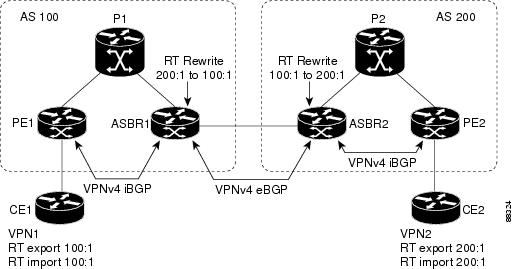
The figure below shows an example of route target replacement on ASBRs in an MPLS VPN interautonomous system topology. This example includes the following configurations:
- PE1 is configured to import and export RT 100:1 for VRF VPN1.
- PE2 is configured to import and export RT 200:1 for VRF VPN2.
- ASBR1 is configured to rewrite all inbound VPNv4 prefixes with RT 200:1 to RT 100:1.
- ASBR2 is configured to rewrite all inbound VPNv4 prefixes with RT 100:1 to RT 200:1.
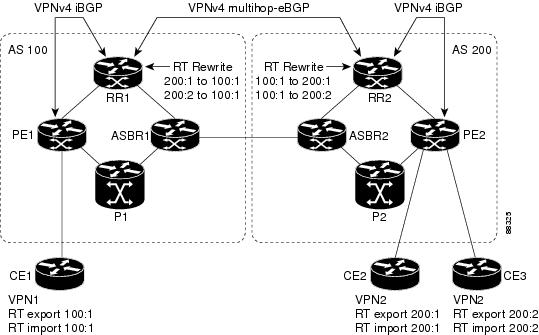
The figure below shows an example of route target replacement on route reflectors in an MPLS VPN interautonomous system topology. This example includes the following configurations:
- EBGP is configured on the route reflectors.
- EBGP and IBGP IPv4 label exchange is configured between all BGP routers.
- Peer groups are configured on the routers reflectors.
- PE2 is configured to import and export RT 200:1 for VRF VPN2.
- PE2 is configured to import and export RT 200:2 for VRF VPN3.
- PE1 is configured to import and export RT 100:1 for VRF VPN1.
- RR1 is configured to rewrite all inbound VPNv4 prefixes with RT 200:1 or RT 200:2 to RT 100:1.
- RR2 is configured to rewrite all inbound prefixes with RT 100:1 to RT 200:1 and RT 200:2.
Route Maps and Route Target Replacement
The MPLS VPN--Route Target Rewrite feature extends the BGP inbound/outbound route map functionality to enable route target replacement. The set extcomm-list delete command entered in route-map configuration mode allows the deletion of a route target extended community attribute based on an extended community list.
How to Configure MPLS VPN--Route Target Rewrite
- Configuring a Route Target Replacement Policy
- Applying the Route Target Replacement Policy
- Verifying the Route Target Replacement Policy
- Troubleshooting Your Route Target Replacement Policy
Configuring a Route Target Replacement Policy
Perform this task to configure an RT replacement policy for your internetwork.
If you configure a PE to rewrite RT x to RT y and the PE has a VRF that imports RT x , you need to configure the VRF to import RT y in addition to RT x .
DETAILED STEPS
Applying the Route Target Replacement Policy
Perform the following tasks to apply the route target replacement policy to your internetwork:
- Associating Route Maps with Specific BGP Neighbors
- Refreshing BGP Session to Apply Route Target Replacement Policy
- Troubleshooting Tips
Associating Route Maps with Specific BGP Neighbors
DETAILED STEPS
Refreshing BGP Session to Apply Route Target Replacement Policy
Perform this task to refresh the BGP session to apply the RT replacement policy.
After you have defined two routers to be BGP neighbors, the routers form a BGP connection and exchange routing information. If you subsequently change a routing policy, you must reset BGP connections for the configuration change to take effect. After configuring the RT replacement policy and applying it to the target routers in your system, you must refresh the BGP session to put the policy into operation.
DETAILED STEPS
Troubleshooting Tips
To determine whether a BGP router supports the route refresh capability, use the show ip bgp neighbors command. If a router supports the route refresh capability, the following message is displayed:
Received route refresh capability from peer.
You can issue the debug ip bgp updates command on the router where you entered the clear ip bgp command to verify that the updates are occurring.
 Note | Issuing the debug ip bgp updates command could impair performance if the router sends or receives a large number of BGP updates. |
Verifying the Route Target Replacement Policy
DETAILED STEPS
Troubleshooting Your Route Target Replacement Policy
DETAILED STEPS
Configuration Examples for MPLS VPN--Route Target Rewrite
- Configuring Route Target Replacement Policies Examples
- Applying Route Target Replacement Policies Examples
Configuring Route Target Replacement Policies Examples
This example shows the RT replacement configuration of an ASBR (ASBR1) that exchanges VPNv4 prefixes with another ASBR (ASBR2). The route map extmap is configured to replace RTs on inbound updates. Any incoming update with RT 100:3 is replaced with RT 200:3. Any other prefixes with an RT whose autonomous system number is 100 is rewritten to RT 200:4.
! ip extcommunity-list 1 permit rt 100:3 ip extcommunity-list 101 permit RT:100:* ! route-map extmap permit 10 match extcommunity 1 set extcomm-list 1 delete set extcommunity rt 200:3 additive ! route-map regexp permit 10 match extcommunity 101 set extcomm-list 101 delete set extcommunity rt 200:4 additive ! route-map regexp permit 20
This example shows the use of the route-map configuration continue command when you need to apply more than one replacement rule on an update. In this example, an incoming update with RT 100:3 is replaced with RT 200:3. Without the continue 20 command, route-map evaluation would stop when a match on sequence 10 is made. With the continue 20 command, route-map evaluation continues into sequence 20 even if a match occurs in sequence 10. If the incoming update has an RT 100:4, the router replaces it with RT 200:4.
! ip extcommunity-list 1 permit rt 100:3 ip extcommunity-list 2 permit rt 100:4 ! route-map extmap permit 10 match extcommunity 1 set extcomm-list 1 delete set extcommunity rt 200:3 additive continue 20 ! route-map extmap permit 20 match extcommunity 2 set extcomm-list 2 delete set extcommunity rt 200:4 additive ! route-map extmap permit 30
 Note | The route-map configuration continue command is not supported on outbound route maps. |
Applying Route Target Replacement Policies Examples
- Associating Route Maps with Specific BGP Neighbor Example
- Refreshing the BGP Session to Apply the Route Target Replacement Policy Example
Associating Route Maps with Specific BGP Neighbor Example
This example shows the association of route map extmap with a BGP neighbor. The BGP inbound route map is configured to replace RTs on incoming updates.
router bgp 100 . . . neighbor 172.16.0.2 remote-as 100 . . . ! address family vpnv4 neighbor 172.16.0.2 activate neighbor 172.16.0.2 send-community extended neighbor 172.16.0.2 route-map extmap in
This example shows the association of the same route map with the outbound BGP neighbor. The route map is configured to replace RTs on outgoing updates.
router bgp 100 . . . neighbor 172.16.0.2 remote-as 100 . . . ! address family vpnv4 neighbor 172.16.0.2 activate neighbor 172.16.0.2 send-community extended neighbor 172.16.0.2 route-map extmap out
Additional References
Related Documents
|
Related Topic |
Document Title |
|---|---|
|
MPLS, MPLS VPN, and MPLS VPN interautonomous systems configuration tasks |
MPLS Layer 3 Inter-AS and CSC Configuration Guide |
|
Commands to configure MPLS and MPLS VPNs |
Cisco IOS Multiprotocol Label Switching Command Reference |
|
BGP configuration tasks |
IP Routing Protocols Configuration Guide |
|
Commands to configure and monitor BGP |
Cisco IOS IP Routing Protocols Command Reference |
MIBs
Technical Assistance
|
Description |
Link |
|---|---|
|
The Cisco Support website provides extensive online resources, including documentation and tools for troubleshooting and resolving technical issues with Cisco products and technologies. To receive security and technical information about your products, you can subscribe to various services, such as the Product Alert Tool (accessed from Field Notices), the Cisco Technical Services Newsletter, and Really Simple Syndication (RSS) Feeds. Access to most tools on the Cisco Support website requires a Cisco.com user ID and password. |
Feature Information for MPLS VPN--Route Target Rewrite
The following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
| Table 1 | Feature Information for MPLS VPN--Route Target Rewrite |
|
Feature Name |
Releases |
Feature Information |
|---|---|---|
|
MPLS VPN--Route Target Rewrite |
12.0(26)S 12.2(25)S 12.2(33)SRA 12.2(33)SXH 12.4(20)T |
The MPLS VPN--Route Target Rewrite feature allows the replacement of route targets on incoming and outgoing Border Gateway Protocol (BGP) updates. Typically, Autonomous System Border Routers (ASBRs) perform the replacement of route targets at autonomous system boundaries. Route Reflectors (RRs) and provider edge (PE) routers can also perform route target replacement. The main advantage of the MPLS VPN--Route Target Rewrite feature is that it keeps the administration of routing policy local to the autonomous system. In 12.0(26)S, this feature was introduced for the Cisco 7200, 7500, and 12000 series routers. In 12.2(25)S, this feature was integrated into a Cisco IOS 12.2S release to support the Cisco 7500 series router. In 12.2(33)SRA, this feature was integrated into a Cisco IOS 12.2SRA release. In 12.2(33)SXH, this feature was integrated into a Cisco IOS 12.2SXH release. In 12.4(20)T, this feature was integrated into a Cisco IOS 12.4T release. The following command was modified: set extcomm-list delete. |
Glossary
autonomous system --A collection of networks that share the same routing protocol and that are under the same system administration.
ASBR --autonomous system border router. A router that connects and exchanges information between two or more autonomous systems.
BGP --Border Gateway Protocol. The exterior border gateway protocol used to exchange routing information between routers in separate autonomous systems. BGP uses Transmission Control Protocol (TCP). Because TCP is a reliable protocol, BGP does not experience problems with dropped or fragmented data packets.
CE router --customer edge router. The customer router that connects to the provider edge (PE) router.
EBGP --External Border Gateway Protocol.A BGP session between routers in different autonomous systems. When a pair of routers in different autonomous systems are more than one IP hop away from each other, an EBGP session between those two routers is called multihop EBGP.
IBGP --Internal Border Gateway Protocol.A BGP session between routers within the same autonomous system.
IGP --Interior Gateway Protocol. Internet protocol used to exchange routing information within an autonomous system. Examples of common Internet IGPs include Internal Gateway Routing Protocol (IGRP), Open Shortest Path First (OSPF), and Routing Information Protocol (RIP).
LDP --Label Distribution Protocol. A standard protocol between MPLS-enabled routers to negotiate the labels (addresses) used to forward packets. The Cisco proprietary version of this protocol is the Tag Distribution Protocol (TDP).
LER --label edge router. The edge router that performs label imposition and disposition.
LSR --label switch router. The role of an LSR is to forward packets in an MPLS network by looking only at the fixed-length label.
MPLS --Multiprotocol Label Switching. A switching method that forwards IP traffic using a label. This label instructs the routers and the switches in the network where to forward the packets based on preestablished IP routing information.
NLRI --Network Layer Reachability Information.BGP sends routing update messages containing NLRI, which describes the route. In this context, an NLRI is a prefix. A BGP update message carries one or more NLRI prefixes and the attributes of a route for the NLRI prefixes. The route attributes include a BGP next-hop gateway address, community values, and other information.
P router --provider router. The core router in the service provider network that connects to provider edge (PE) routers. In a packet-switched star topology, a router that is part of the backbone and that serves as the single pipe through which all traffic from peripheral networks must pass on its way to other peripheral networks.
PE router --provider edge router.The label edge router (LER) in the service provider network that connects to the customer edge (CE) router.
RD --route distinguisher. An 8-byte value that is concatenated with an IPv4 prefix to create a unique VPN IPv4 (VPNv4) prefix.
RR --route reflector. A router that advertises, or reflects, IBGP learned routes to other IBGP peers without requiring a full network mesh.
RT --route target. Extended community attribute used to identify the VRF routing table into which a prefix is to be imported.
VPN --Virtual Private Network.A group of sites that, as a result of a set of administrative policies, can communicate with each other over a shared backbone.
VPNv4 prefix --IPv4 prefix preceded by an 8-byte route distinguisher. The VPN addresses are made unique by adding a route distinguisher to the front of the address.
VRF --VPN routing and forwarding instance. A VRF consists of an IP routing table, a derived forwarding table, a set of interfaces that use the forwarding table, and a set of rules and routing protocols that determine what goes into the forwarding table. In general, a VRF includes the routing information that defines a customer VPN site that is attached to a provider edge (PE) router.
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.

 Feedback
Feedback