配置并声明独立Nexus用于Intersight连接
非歧视性语言
此产品的文档集力求使用非歧视性语言。在本文档集中,非歧视性语言是指不隐含针对年龄、残障、性别、种族身份、族群身份、性取向、社会经济地位和交叉性的歧视的语言。由于产品软件的用户界面中使用的硬编码语言、基于 RFP 文档使用的语言或引用的第三方产品使用的语言,文档中可能无法确保完全使用非歧视性语言。 深入了解思科如何使用包容性语言。
关于此翻译
思科采用人工翻译与机器翻译相结合的方式将此文档翻译成不同语言,希望全球的用户都能通过各自的语言得到支持性的内容。 请注意:即使是最好的机器翻译,其准确度也不及专业翻译人员的水平。 Cisco Systems, Inc. 对于翻译的准确性不承担任何责任,并建议您总是参考英文原始文档(已提供链接)。
目录
简介
本文档介绍在Intersight中启用和声明独立Nexus交换机以获得增强的Cisco TAC支持所需的步骤。
先决条件
您必须在Intersight.com上拥有帐户,Cisco NX-OS®申请无需许可证。如果需要创建新的Intersight帐户,请参阅帐户创建。
要求
Cisco 建议您了解以下主题:
在独立Nexus交换机上,NXDC具有以下准则和限制:
- Cisco NX-OS必须运行版本10.2(3)F或更高版本
- 必须在正确的虚拟路由和转发(VRF)下配置DNS
svc.intersight.com 必须解析并允许端口443上的出站发起HTTPS连接。可以通过openssl和curl进行查看这个值。Internet控制消息协议(ICMP)请求会被忽略。- 如果HTTPS连接需要代理
svc.intersight.com,可在Nexus交换机设备连接器(NXDC)配置中配置代理。有关代理配置,请参阅配置NXDC。
使用的组件
使用的组件本文档中的信息基于以下软件和硬件版本:
- 思科Nexus N9K-C93240YC-FX2
- 思科NX-OS 10.3(4a)M
本文档中的信息都是基于特定实验室环境中的设备编写的。本文档中使用的所有设备最初均采用原始(默认)配置。如果您的网络处于活动状态,请确保您了解所有命令的潜在影响。
背景信息
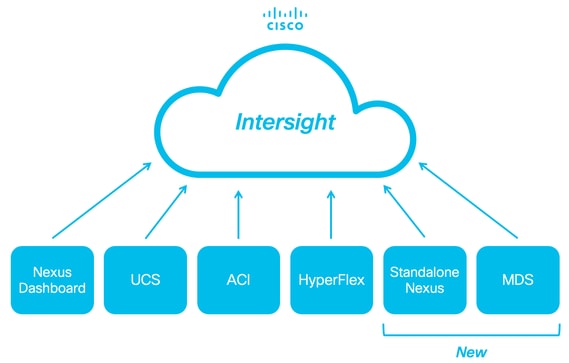
背景信息Cisco Intersight是一个云操作平台,由高级基础设施、工作负载优化和Kubernetes服务的可选模块化功能组成。有关详细信息,请访问Intersight概述。
设备通过嵌入在每个系统的Cisco NX-OS映像中的NXDC连接到Intersight门户。从Cisco NX-OS版本10.2(3)F开始,支持设备连接器功能,为连接的设备提供安全的方式,使用安全的互联网连接从Cisco Intersight门户发送信息和接收控制指令。
连接优势
连接优势Intersight连接为基于Cisco NX-OS的平台提供以下功能和优势:
- 通过快速问题解决自动收集
show tech-support details(RPR for the TAC Service Requests open) - 远程按需收集
show tech-support details - 未来的功能包括:
- 根据遥测或硬件故障打开主动TAC服务请求
- 单个show命令的远程按需收集及其他
连接验证
连接验证
注意:抑制Ping响应(丢弃ICMP数据包)。
要检查传输层安全(TLS)和HTTPS连接,建议在所需VRF (ip netns exec <VRF>)中启用bash并执行openssl和curl命令。
! Enable bash
config terminal ; feature bash ; end
! Verify TLS
run bash ip netns exec management openssl s_client -connect svc.intersight.com:443
! Verify https
run bash ip netns exec management curl -v -I -L -k https://svc.intersight.com:443
run bash ip netns exec management curl -v -I -L -k https://svc.intersight.com:443 --proxy [protocol://]host[:port]
使用OpenSSL客户端进行TLS验证
使用OpenSSL客户端进行TLS验证使用OpenSSL,您可以检查与svc.intersight.com:443的TLS连接。成功后,检索服务器的公共签名证书并显示证书颁发机构链。

注意:下一个示例在VRF管理中执行openssl s_client命令。 替换ip netns exec <VRF>结构中所需的。
Switch# run bash ip netns exec management openssl s_client -connect svc.intersight.com:443 CONNECTED(00000004) depth=2 C = US, O = Amazon, CN = Amazon Root CA 1 verify return:1 depth=1 C = US, O = Amazon, CN = Amazon RSA 2048 M01 verify return:1 depth=0 CN = us-east-1.intersight.com verify return:1 --- Certificate chain 0 s:CN = us-east-1.intersight.com i:C = US, O = Amazon, CN = Amazon RSA 2048 M01 1 s:C = US, O = Amazon, CN = Amazon RSA 2048 M01 i:C = US, O = Amazon, CN = Amazon Root CA 1 2 s:C = US, O = Amazon, CN = Amazon Root CA 1 i:C = US, ST = Arizona, L = Scottsdale, O = "Starfield Technologies, Inc.", CN = Starfield Services Root Certificate Authority - G2 3 s:C = US, ST = Arizona, L = Scottsdale, O = "Starfield Technologies, Inc.", CN = Starfield Services Root Certificate Authority - G2 i:C = US, O = "Starfield Technologies, Inc.", OU = Starfield Class 2 Certification Authority --- Server certificate -----BEGIN CERTIFICATE----- MIIGfzCCBWegAwIBAgIQD859tBjpT+QUyVOXqkG2pzANBgkqhkiG9w0BAQsFADA8 MoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kg UlNBIDIwNDggTTAxMB4XDTIzMDQwNTAwMDAwMFoXDTI0MDUwMzIzNTk1OVowIzEh MB8GA1UEAxMYdXMtZWFzdC0xLmludGVyc2lnaHQuY29tMIIBIjANBgkqhkiG9w0B AoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kn BDM+MCNnvmgNDlGnU6/t1jOC780QpKXr2ksbGC0FzHfMvNjEk9kMCUe179dummrs pOOFzvIrJGqYvkIXT5WLtiU9aP3+VSEWQO1kTeDHoDfLLJLON42cKjskYt0jCTwE poKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0KI elf3tYBhuQK3y4DoSqg1/gptnUOlNwSqMu4zXjI7neGyHnzjsPUyI8qilXbPS9tV KoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kw HwYDVR0jBBgwFoAUgbgOY4qJEhjl+js7UJWf5uWQE4UwHQYDVR0OBBYEFM7X7s7c NoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kp Z2h0LmNvbYIac3ZjLXN0YXRpYzEuaW50ZXJzaWdodC5jb22CGioudXMtZWFzdC0x LoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0K1 Y3MtY29ubmVjdC5jb22CE3N2Yy51Y3MtY29ubmVjdC5jb22CDmludGVyc2lnaHQu Y29tghJzdmMuaW50ZXJzaWdodC5jb20wDgYDVR0PAQH/BAQDAgWgMB0GA1UdJQQW MBQGCCsGAQUFBwMBBggrBgEFBQcDAjA7BgNVHR8ENDAyMDCgLqAshipodHRwOi8v YoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0KI BgZngQwBAgEwdQYIKwYBBQUHAQEEaTBnMC0GCCsGAQUFBzABhiFodHRwOi8vb2Nz coKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Ku cjJtMDEuYW1hem9udHJ1c3QuY29tL3IybTAxLmNlcjAMBgNVHRMBAf8EAjAAMIIB fgYKKwYBBAHWeQIEAgSCAW4EggFqAWgAdwDuzdBk1dsazsVct520zROiModGfLzs 3oKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0K5 CSFqTpBjlOdOLQ4YuQIhAO10VDrLJMM+9EtOwmZd8Q1MRHJlOlr2VWmOTF6GGkCV AHUAc9meiRtMlnigIH1HneayxhzQUV5xGSqMa4AQesF3crUAAAGHUp9iOwAABAMA RjBEAiAFPPLvt7TN7mTRnQZ+FZLGR/G04KQqSjYuszDNPArT3wIgf/sQbQqNjCk7 joFUuL9cEPYfNm7n1nZIFIRAK6UqwG0AdgBIsONr2qZHNA/lagL6nTDrHFIBy1bd LoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0K8 MXtts5t/C5lYw5peGAIgK0eFmxTptEfMkBZti39vepUxb5meDvKaZdtXVvFpkCMw DQYJKoZIhvcNAQELBQADggEBANl6HKZ9P6AIufr7qdNCcW+DXClY6dqX1KN0sCh+ UoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0KM z5R1VV+81gN2HHiuUsEOFwHDbbhiGBJiJteFm0blpruKHennx8HQYfC7bup4N5JH YoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kb LKFl6c+EN0Y76YaCV8doujG3qD/bO9VDx7dhvbSEECYuzbYyPDGnb7Drmhny0Eki smLUZ3TVcCvPc+1dE/jrbBzPeIY7jGr8eL7masFCuZZn2lM= -----END CERTIFICATE----- subject=CN = us-east-1.intersight.com issuer=C = US, O = Amazon, CN = Amazon RSA 2048 M01 --- No client certificate CA names sent Peer signing digest: SHA256 Peer signature type: RSA Server Temp Key: ECDH, P-256, 256 bits --- SSL handshake has read 5754 bytes and written 442 bytes Verification: OK --- New, TLSv1.2, Cipher is ECDHE-RSA-AES128-GCM-SHA256 Server public key is 2048 bit Secure Renegotiation IS supported Compression: NONE Expansion: NONE No ALPN negotiated SSL-Session: Protocol : TLSv1.2 Cipher : ECDHE-RSA-AES128-GCM-SHA256 Session-ID: 66D0B69FAA7EB69FAA7EC54C9764966ED9A1289650B69FAA7EB69FAA7E9A5FD5ADE Session-ID-ctx: Master-Key: B69FAA7E45891555D83DFCAEB69FAA7EB69FAA7EA3A99E7689ACFB69FAA7EAD7FD93DB69FAA7EB1AF821 PSK identity: None PSK identity hint: None SRP username: None TLS session ticket lifetime hint: 86400 (seconds) TLS session ticket: 0000 - 36 12 b2 36 b3 53 07 29-54 ac 56 f0 06 83 4f b1 6..6.S.)T.V...O. 0010 - 49 35 51 40 22 07 bd 7e-59 d7 7e 44 29 ff c6 2a I5Q@"..~Y.~D)..* 0020 - ec bc 11 e1 d3 5d 69 e8-7a d2 f1 c2 08 f6 5b 8f .....]i.z.....[. 0030 - 2c 5b 5e 50 e3 e2 8f e7-c4 44 8f e4 6d 45 d2 64 ,[^P.....D..mE.d 0040 - 93 98 f5 e8 b0 f7 1d 00-26 4b 88 ea 2d 7d 42 58 ........&K..-}BX 0050 - 05 9f 71 3a fe ac f0 15-a5 5c 1d 74 74 bf 32 1b ..q:.....\.tt.2. 0060 - d8 a8 23 84 08 cc f9 3e-54 ..#....>T Start Time: 1707515659 Timeout : 7200 (sec) Verify return code: 0 (ok) Extended master secret: yes --- HTTPS可达性验证
HTTPS可达性验证要检查HTTPS连接,请将curl命令与-v verbose flag(显示是否使用代理)一起使用。

注意:为了检查启用或禁用代理的影响,您可以添加选项--proxy [protocol://]host[:port]或--noproxy [protocol://]host[:port]。
结构ip netns exec <VRF>用于在所需的VRF中执行curl;例如,ip netns exec management用于VRF管理。
run bash ip netns exec management curl -v -I -L -k https://svc.intersight.com:443
run bash ip netns exec management curl -v -I -L -k https://svc.intersight.com:443 --proxy [protocol://]host[:port]
# run bash ip netns exec management curl -v -I -L -X POST https://svc.intersight.com:443 --proxy http://proxy.esl.cisco.com:80
Trying 10.201.255.40:80...
* Connected to proxy.esl.cisco.com (10.201.255.40) port 80 * CONNECT tunnel: HTTP/1.1 negotiated
* allocate connect buffer
* Establish HTTP proxy tunnel to svc.intersight.com:443
> CONNECT svc.intersight.com:443 HTTP/1.1
> Host: svc.intersight.com:443
> User-Agent: curl/8.4.0
> Proxy-Connection: Keep-Alive
>
< HTTP/1.1 200 Connection established HTTP/1.1 200 Connection established
< snip >
配置
配置声明设备在 intersight.com
声明设备在 intersight.com要在Intersight中声明一个新目标,请完成上述步骤。
在Nexus设备上
在Nexus设备上发出Cisco NX-OS命令show system device-connector claim-info。

注意:对于NX-OS 10.3(4a)之前的版本,请使用“show intersight claim-info”命令

注意:Nexus生成的声明信息映射到以下Intersight声明字段:
序列号= Intersight领款申请ID
Device-ID Security Token = Intersight Claim Code
# show system device-connector claim-info
SerialNumber: FDO23021ZUJ
SecurityToken: 9FFD4FA94DCD
Duration: 599
Message:
Claim state: Not Claimed
此处报告的持续时间以秒为单位。
在Intersight门户上
1. 在10分钟内使用帐户管理员、设备管理员或设备技术人员权限登录Intersight。
2. 从Service Selector下拉列表中选择System。
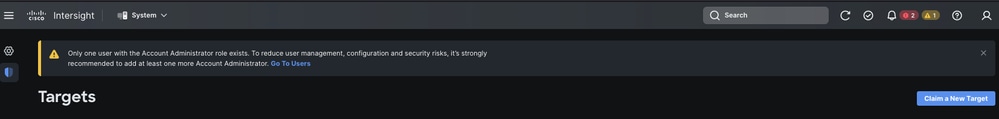
3. 定位至ADMIN > Targets > Claim a New Target。
3.1.单击Claim a New Target,如图所示。
4. 选择可用于申请,然后选择您要申请的目标类型(例如,网络)。单击开始。
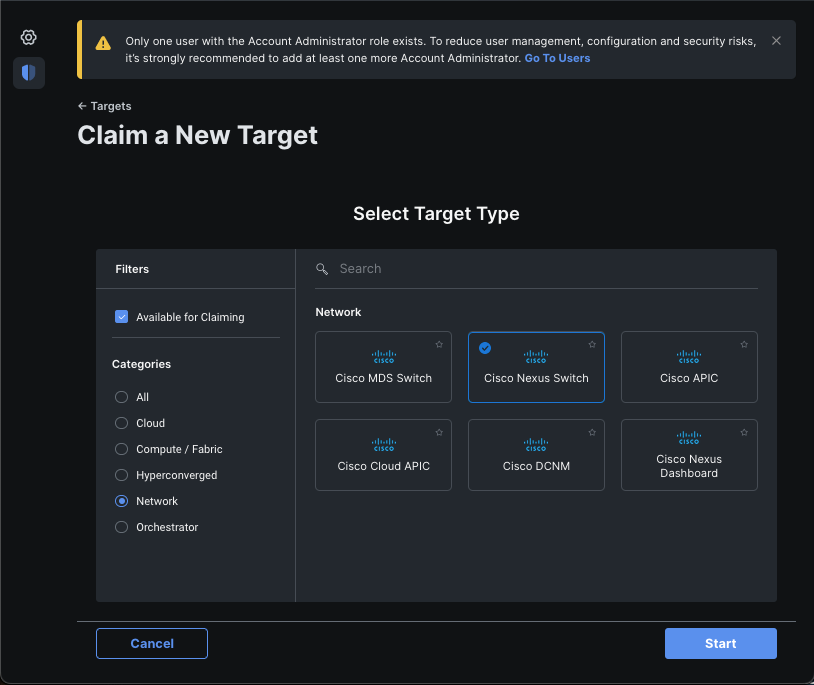
5. 输入所需的详细信息并单击Claim 以完成申请流程。

注意:交换机上的安全令牌用作声明代码,交换机的序列号为设备ID。

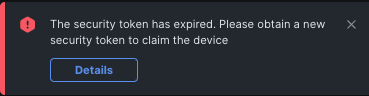
注意:安全令牌过期。您必须在之前完成领款申请,否则系统会提示您重新生成领款申请。
使用Ansible在intersight.com中声明一到多个独立Nexus设备®
为了逐一声明Nexus设备,可以运行Ansible手册。
- ansible资产和攻略可以从https://github.com/datacenter/ansible-intersight-nxos克隆。
- 在Ansible
inventory.yaml中,ansible_connection类型设置为ansible.netcommon.network_cli,以便向Nexus交换机发送命令。可以将其更改为ansible.netcommon.httpapi,以便允许通过NXAPI进行连接。 - 与Intersight终结点的Ansible连接需要API密钥,可通过您的intersight.com帐户生成。
配置Nexus NXAPI(仅在使用ansible.netcommon.httpapi时使用)

注意:如果配置了系统级代理(HTTP(S)_PROXY),并且Ansible不能使用代理连接Nexus NXAPI终端,则需要设置ansible_httpapi_use_proxy: False(默认为True)。
# configure terminal # cfeature nxapi # nxapi port 80 # no nxapi https port 443 # end # show nxapi nxapi enabled NXAPI timeout 10 NXAPI cmd timeout 300 HTTP Listen on port 80 HTTPS Listen on port 443 Certificate Information: Issuer: issuer=C = US, ST = CA, L = San Jose, O = Cisco Systems Inc., OU = dcnxos, CN = nxos Expires: Feb 10 22:30:38 2024 GMT
为了独立验证到NXAPI终端的HTTP连接,您可以尝试发送show clock。在下一个示例中,交换机使用基本身份验证对客户端进行身份验证。也可以配置NXAPI服务器以根据X.509用户证书对客户端进行身份验证。

注意:基本身份验证哈希是从username:password的base64编码中获取的。在本示例中,admin:cisco!123 base64编码为YWRtaW46Y2lzY28hMTIz。
curl -v --noproxy '*' \ --location 'http://10.1.1.3:80/ins' \ --header 'Content-Type: application/json' \ --header 'Authorization: Basic YWRtaW46Y2lzY28hMTIz' \ --data '{ "ins_api": { "version": "1.0", "type": "cli_show", "chunk": "0", "sid": "sid", "input": "show clock", "output_format": "json" } }'
卷曲响应:
* Trying 10.1.1.3... * TCP_NODELAY set * Connected to 10.1.1.3 (10.1.1.3) port 80 (#0) > POST /ins HTTP/1.1 > Host: 10.1.1.3 > User-Agent: curl/7.61.1 > Accept: */* > Content-Type: application/json > Authorization: Basic YWRtaW56Y2lzY28hBNIz > Content-Length: 297 > * upload completely sent off: 297 out of 297 bytes < HTTP/1.1 200 OK < Server: nginx/1.19.6 < Date: Fri, 09 Feb 2024 23:17:10 GMT < Content-Type: text/json; charset=UTF-8 < Transfer-Encoding: chunked < Connection: keep-alive < Set-Cookie: nxapi_auth=dzqnf:xRYwR0l1Tra64VfOMVuD4oI4=; Secure; HttpOnly; < anticsrf: /i3vzCvxhOr4w2IrKP+umbDnzHQ= < Strict-Transport-Security: max-age=31536000; includeSubDomains < X-Frame-Options: SAMEORIGIN < X-Content-Type-Options: nosniff < Content-Security-Policy: block-all-mixed-content; base-uri 'self'; default-src 'self'; script-src 'self' 'nonce-zHx12KP1tervan1s6lrFQz7N6PF0rh'; style-src 'self' 'nonce-zHx12KP1tervan1s6lrFQz7N6P40rh'; img-src 'self'; connect-src 'self'; font-src 'self'; object-src 'self'; media-src 'self'; form-action 'self'; frame-ancestors 'self'; < { "ins_api": { "type": "cli_show", "version": "1.0", "sid": "eoc", "outputs": { "output": { "input": "show clock", "msg": "Success", "code": "200", "body": { "simple_time": "23:17:10.814 UTC Fri Feb 09 2024\n", "time_source": "NTP" } } } } * Connection #0 to host 10.1.1.3 left intact }%
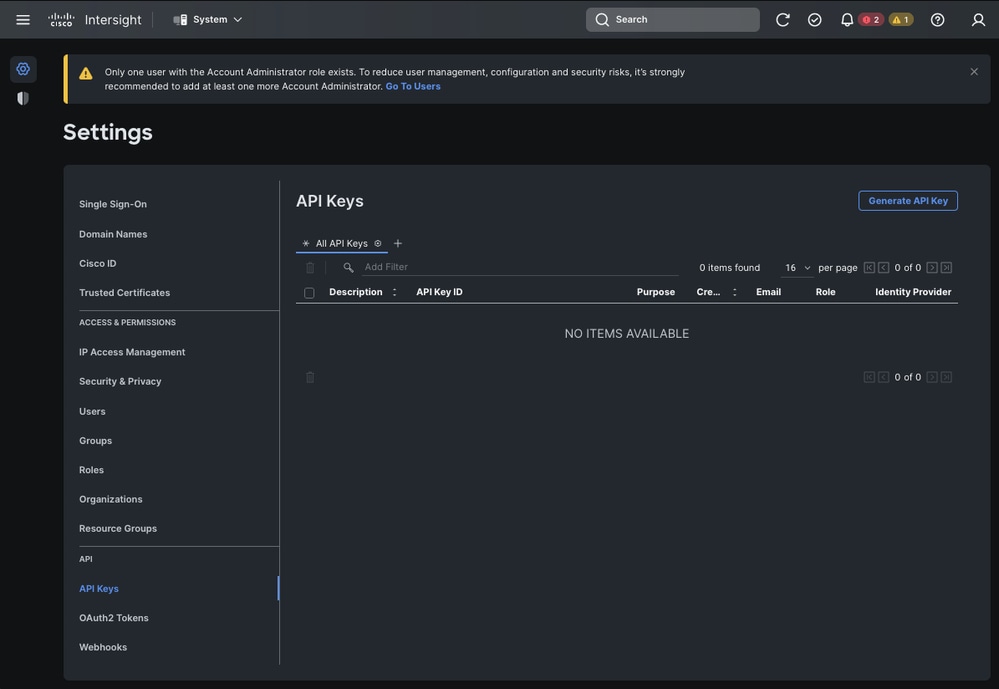
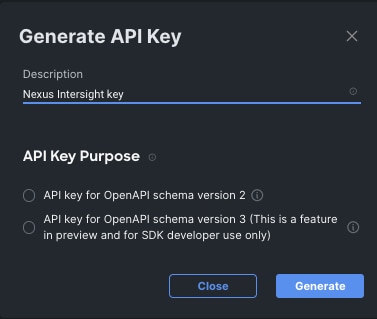
生成Intersight API密钥
有关如何从Intersight System > Settings > API keys > Generate API Key获取API密钥,请参阅README.md部分。
示例:Ansible inventory.yaml

注意:在下一个示例中,配置了ansible以便使用ansible_httpapi_use_proxy: False忽略操作系统代理设置。如果您需要Ansible服务器使用代理才能访问交换机,则可以删除该配置或将其设置为True(默认值)。

注意:API密钥ID是一个字符串。API私钥包括包含私钥的文件的完整路径。对于生产环境,建议使用Ansible保管库。
---
all:
hosts:
switch1:
ansible_host: "10.1.1.3"
intersight_src: "mgmt0"
intersight_vrf: "management"
vars:
ansible_user: "admin"
ansible_password: "cisco!123"
ansible_connection: ansible.netcommon.network_cli
ansible_network_os: cisco.nxos.nxos
ansible_httpapi_use_proxy: False
remote_tmp: "/bootflash"
proxy_env:
- no_proxy: "10.1.1.3/24"
intersight_proxy_host: 'proxy.cisco.com'
intersight_proxy_port: '80'
api_key_id: "5fcb99d97564612d33fdfcal/5fcb99d97564612d33fdf1b2/65c6c09d756461330198ce7e"
api_private_key: "/home/admin/ansible-intersight-nxos/my_intersight_private_key.txt"
...
示例:playbook.yaml执行
有关使用Ansible对独立Nexus设备进行编程的详细信息,请参阅您当前版本的Cisco Nexus 9000系列NX-OS可编程性指南的Applications/Using Ansible使用Cisco NX-OS部分。
❯ ansible-playbook -i inventory.yaml playbook.yaml PLAY [all] ********************************************************************************************************************************************************* TASK [Enable feature intersight] *********************************************************************************************************************************** [WARNING]: To ensure idempotency and correct diff the input configuration lines should be similar to how they appear if present in the running configuration on device changed: [switch1] TASK [Configure proxy] ********************************************************************************************************************************************* ok: [switch1] TASK [Unconfigure proxy] ******************************************************************************************************************************************* skipping: [switch1] TASK [Configure src interface] ************************************************************************************************************************************* ok: [switch1] TASK [Unconfigure src interface] *********************************************************************************************************************************** skipping: [switch1] TASK [Configure src vrf] ******************************************************************************************************************************************* ok: [switch1] TASK [Unconfigure src vrf] ***************************************************************************************************************************************** skipping: [switch1] TASK [Await connection to Intersight] ****************************************************************************************************************************** FAILED - RETRYING: [switch1]: Await connection to Intersight (10 retries left). FAILED - RETRYING: [switch1]: Await connection to Intersight (9 retries left). FAILED - RETRYING: [switch1]: Await connection to Intersight (8 retries left). FAILED - RETRYING: [switch1]: Await connection to Intersight (7 retries left). FAILED - RETRYING: [switch1]: Await connection to Intersight (6 retries left). FAILED - RETRYING: [switch1]: Await connection to Intersight (5 retries left). FAILED - RETRYING: [switch1]: Await connection to Intersight (4 retries left). ok: [switch1] TASK [Get show system device-connector claim-info] ***************************************************************************************************************** ok: [switch1] TASK [Set claiminfoDict] ******************************************************************************************************************************************* ok: [switch1] => (item=SerialNumber: FDO21112E2L) ok: [switch1] => (item= SecurityToken: 0A70886FE1B8) ok: [switch1] => (item= Duration: 599) ok: [switch1] => (item= Message: ) ok: [switch1] => (item= Claim state: Not Claimed) TASK [claim device - PROXY] **************************************************************************************************************************************** skipping: [switch1] TASK [claim device - NO PROXY] ************************************************************************************************************************************* changed: [switch1] PLAY RECAP ********************************************************************************************************************************************************* switch1 : ok=8 changed=2 unreachable=0 failed=0 skipped=4 rescued=0 ignored=0
验证
要验证新目标的声明,请完成以下操作:
在Nexus交换机上
10.3(4a)M之前的版本
#运行bash sudo cat /mnt/pss/connector.db
Nexus# run bash sudo cat /mnt/pss/connector.db { "AccountOwnershipState": "Claimed", "AccountOwnershipUser": "bpaez@cisco.com", "AccountOwnershipTime": "2024-04-25T22:37:25.173Z", "AccountOwnershipId": "TAC-DCRS", "DomainGroupMoid": "6620503275646133014ec978", "AccountMoid": "6620503275646133014ec977", "CloudDns": "svc.ucs-connect.com", "CloudDnsList": [ "svc.intersight.com", "svc-static1.intersight.com", "svc.ucs-connect.com", "svc-static1.ucs-connect.com" ], "CloudCert": "", "UserCloudCerts": {}, "Identity": "662adb256f72613901e8bc19", "AccessKeyId": "98facfdbf3855bcfd340f2bbb0c388f8", "AccessKey": "", "PrivateAccessKey": "-----BEGIN RSA PRIVATE KEY----- -CUT- 5Do\nD18Ta5YvuIYFLZrYlHLyCDOhS5035AUEGNtEceiPhQjOCvRumyJD\n-----END RSA PRIVATE KEY-----\n", "CloudEnabled": true, "ReadOnlyMode": false, "LocalConfigLockout": false, "TunneledKVM": false, "HttpProxy": { "ProxyHost": "proxy.cisco.com", "ProxyPort": 8080, "Preference": 0, "ProxyType": "Manual", "Targets": [ { "ProxyHost": "proxy.cisco.com", "ProxyPort": 8080, "Preference": 0 } ] }, "LogLevel": "info", "DbVersion": 1, "AutoUpgradeAdminState": "Automatic"
以10.3(4a)M开头的版本
# show system device-connector claim-info
N9k-Leaf-2# show system device-connector claim-info SerialNumber: FDO23021ZUJ SecurityToken: Duration: 0 Message: Cannot fetch claim code for already claimed device Claim state: Claimed Claim time: 2024-02-09T15:38:57.561Z Claimed by: brvarney@cisco.com Account: ACI-DCRS-TAC Site name: Site ID:
# show system internal intersight info
# show system internal intersight info Intersight connector.db Info: ConnectionState :Connected ConnectionStateQual : AccountOwnershipState :Claimed AccountOwnershipUser :brvarney@cisco.com AccountOwnershipTime :2024-02-09T15:38:57.561Z AccountOwnershipId :ACI-DCRS-TAC DomainGroupMoid :5eb2e1e47565612d3079fe9a AccountMoid :5eb2e1e47565612d3079fe92 CloudDns :svc.ucs-connect.com CloudDnsList: 1. :svc.ucs-connect.com 2. :svc.intersight.com 3. :svc-static1.intersight.com 4. :svc-static1.ucs-connect.com Identity :65c647116f72513501e75530 CloudEnabled :true ReadOnlyMode :false LocalConfigLockout :false TunneledKVM :false HttpProxy: ProxyHost :proxy.cisco.com ProxyPort :8080 Preferenc :0 ProxyType :Manual Target[1]: ProxyHost :proxy.cisco.com ProxyPort :8080 Preference :0 LogLevel :info DbVersion :1 AutoUpgradeAdminState :Automatic
Ansible
可以在playbook.yaml末尾添加一个任务来获取交换机插入信息。
- name: Get intersight info nxos_command: commands: - show system internal intersight info register: intersightInfo_claimed retries: 10 delay: 10 until: intersightInfo.stdout is search("Connecte") - name: Display intersight info vars: msg: |- output from {{ inventory_hostname }}: {{ intersightInfo_claimed.stdout | join("") }} debug: msg: "{{ msg.split('\n') }}"
以下是相应的输出:
TASK [Get intersight info] *************************************************************************************************** ok: [switch1] TASK [Display intersight info] *********************************************************************************************** ok: [switch1] => { "msg": [ "output from switch1:", "Intersight connector.db Info:", "ConnectionState :Connected", "ConnectionStateQual :", "AccountOwnershipState :Claimed", "AccountOwnershipUser :vricci@cisco.com", "AccountOwnershipTime :2024-02-10T01:00:28.516Z", "AccountOwnershipId :vricci", "DomainGroupMoid :5fcb98d97565612d33fdf1ae", "AccountMoid :5fcb98d97565612d33fdf1ac", "CloudDns :svc.intersight.com", "CloudDnsList: ", " 1. :svc.intersight.com", " 2. :svc-static1.intersight.com", " 3. :svc.ucs-connect.com", " 4. :svc-static1.ucs-connect.com", "Identity :65c6caac6f72613901f841c1", "CloudEnabled :true", "ReadOnlyMode :false", "LocalConfigLockout :false", "TunneledKVM :false", "HttpProxy: ", " ProxyHost :proxy.cisco.com", " ProxyPort :80", " Preferenc :0", " ProxyType :Manual", " Target[1]: ", " ProxyHost :proxy.cisco.com", " ProxyPort :80", " Preference :0", "LogLevel :info", "DbVersion :1", "AutoUpgradeAdminState :Automatic" ] }
禁用设备连接器
命令或操作
目的
第 1 步
no feature intersight
示例:
switch(config)# no feature intersight
禁用intersight进程并删除所有NXDC配置和日志存储。
修订历史记录
| 版本 | 发布日期 | 备注 |
|---|---|---|
2.0 |
02-Apr-2024 |
添加了“禁用设备连接器”部分 |
1.0 |
22-Feb-2024 |
初始版本 |
由思科工程师提供
- 布兰登·瓦尼技术主管
- 文森特·里奇技术主管
- 约格什·拉姆多斯首席工程师
 反馈
反馈