使用Active Directory WMI提供程序配置ISE 2.2 PIC
下载选项
非歧视性语言
此产品的文档集力求使用非歧视性语言。在本文档集中,非歧视性语言是指不隐含针对年龄、残障、性别、种族身份、族群身份、性取向、社会经济地位和交叉性的歧视的语言。由于产品软件的用户界面中使用的硬编码语言、基于 RFP 文档使用的语言或引用的第三方产品使用的语言,文档中可能无法确保完全使用非歧视性语言。 深入了解思科如何使用包容性语言。
关于此翻译
思科采用人工翻译与机器翻译相结合的方式将此文档翻译成不同语言,希望全球的用户都能通过各自的语言得到支持性的内容。 请注意:即使是最好的机器翻译,其准确度也不及专业翻译人员的水平。 Cisco Systems, Inc. 对于翻译的准确性不承担任何责任,并建议您总是参考英文原始文档(已提供链接)。
目录
简介
本文档介绍如何使用Active Directory Windows Management Instrumentation(AD WMI)提供程序配置身份服务引擎被动身份连接器(ISE PIC)部署并排除其故障。ISE PIC是轻量级ISE版本,侧重于被动ID功能。
ISE PIC是适用于所有思科安全产品组合的单一ID解决方案,仅使用被动身份。这意味着无法在ISE PIC上配置授权或策略。它支持不同的提供程序(代理、WMI、系统日志、API),并可通过REST API进行集成。它能够查询终端(用户是否登录?终端是否仍连接?)
先决条件
要求
Cisco 建议您具有以下主题的基础知识:
-
思科身份服务引擎
- Microsoft Active Directory
- Microsoft WMI
使用的组件
本文档中的信息基于以下软件和硬件版本:
- 思科身份服务引擎被动身份连接器版本2.2.0.470
- Microsoft Windows 7 Service Pack 1
- Microsoft Windows Server 2012 r2
本文档中的信息都是基于特定实验室环境中的设备编写的。本文档中使用的所有设备最初均采用原始(默认)配置。如果您使用的是真实网络,请确保您已经了解所有命令的潜在影响。
背景信息
ISE PIC部署中的最大节点数为2。此示例显示如何配置ISE PIC部署以实现高可用性,因此使用2个虚拟机(VM)。在ISE PIC部署中,节点可以具有以下角色:主要和辅助。在此中,一次只能有一个节点是主节点,并且只能通过GUI手动更改角色。在主故障时,除UI外,所有功能仍在辅助上运行。只有手动升级到主要才能启用UI。
此示例显示如何为Active Directory配置WMI提供程序。WMI包括一组Windows驱动程序模型的扩展,提供操作系统界面,通过该界面,已检测的组件提供信息和通知。WMI是Microsoft从分布式管理任务组(DMTF)实施基于Web的企业管理(WBEM)和通用信息模型(CIM)标准。
注意:有关WMI的详细信息,请访问Microsoft官方网站:关于WMI
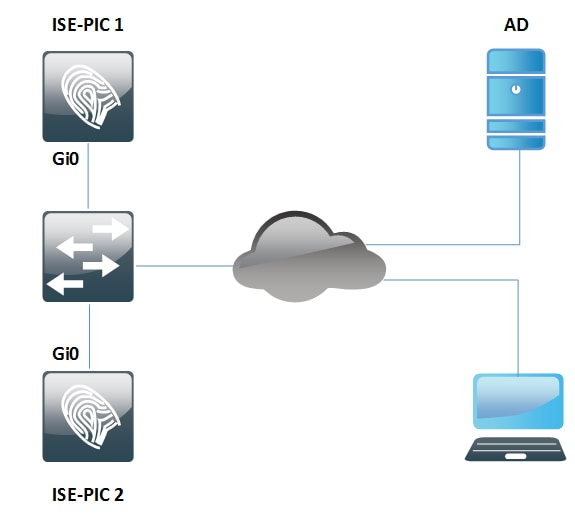
网络图
文档中的信息使用图中所示的网络设置:
工作流
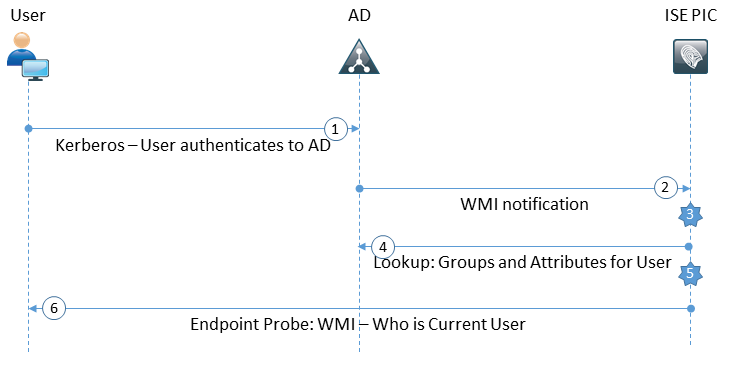
- 登录PC并在AD上进行身份验证。
- WMI将此身份验证通知ISE PIC。
- ISE将绑定用户名:IP_Address添加到其会话目录。
- ISE从AD检索用户组和属性。
- ISE将此信息保存到其会话目录。
- 每4小时(不可配置)ISE PIC运行终端探测:
- 首先,它尝试将WMI应用到终端。
- 如果WMI失败,则ISE PIC运行ISEExec。它查询用户的终端并启用WMI。
- ISE PIC还检索终端和操作系统类型的MAC地址。
在ISE PIC上,只能启用/禁用终端探测功能。主节点查询所有终端,辅助节点仅用于高可用性。
配置
配置ISE PIC部署
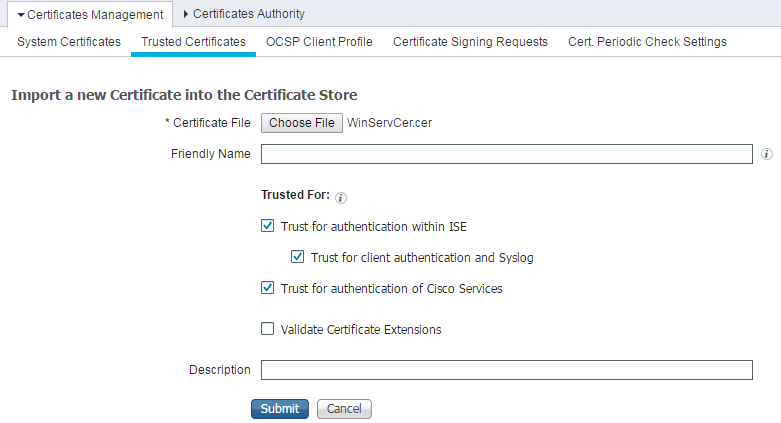
步骤 1(可选)。 安装受信任证书。
您的证书颁发机构(CA)的完整证书链应安装到ISE受信任存储。登录ISE PIC GUI并导航至“证书”>“证书管理”>“受信任证书”。单击Import,然后从PC中选择CA的证书。
如图所示,单击“提交”以保存更改。对链的所有证书重复此步骤。在辅助节点上重复步骤。
步骤 2(可选)。 安装系统证书。
选项1. CA已生成的证书和私钥。
导航至Certificates > Certificates Management > System Certificates,然后单击Import。选择Certificate File和Private Key File,如果私钥已加密,则输入Password字段。
如图所示,选中“使用选项”:
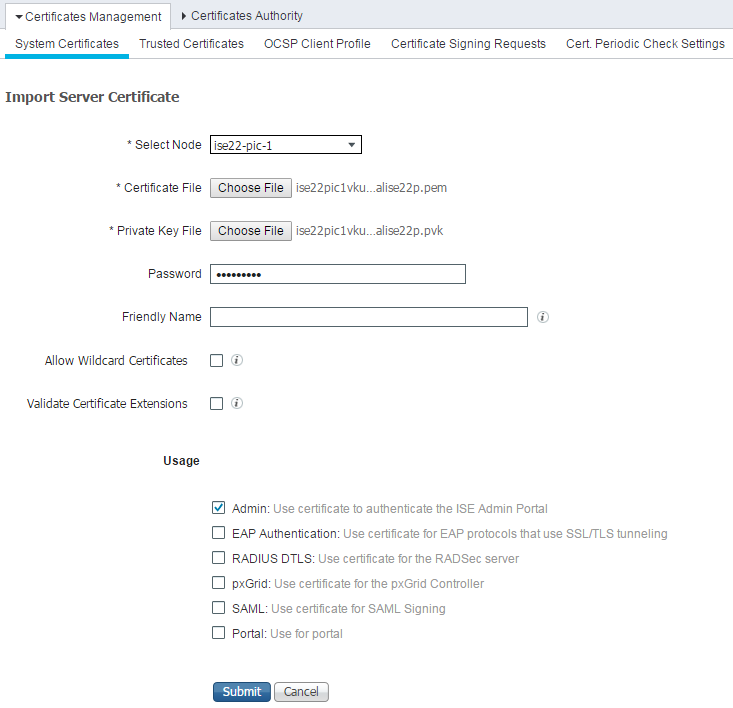
注意:由于ISE PIC基于ISE代码,并且可以轻松转换为具有适当许可证的全功能ISE,因此所有使用选项都可用。ISE PIC不使用EAP身份验证、RADIUS DTLS、SAML和门户等角色。
单击Submit以安装证书。在辅助节点上也重复此步骤。
注意:ISE PIC节点上的所有服务在服务器证书导入后重新启动。
选项2.生成证书签名请求(CSR),使用CA签名并在ISE上绑定。
导航至“证书”>“证书管理”>“证书签名请求”页,然后单击“生成证书签名请求(CSR)”。
选择节点和使用情况,如果需要,输入其他字段:
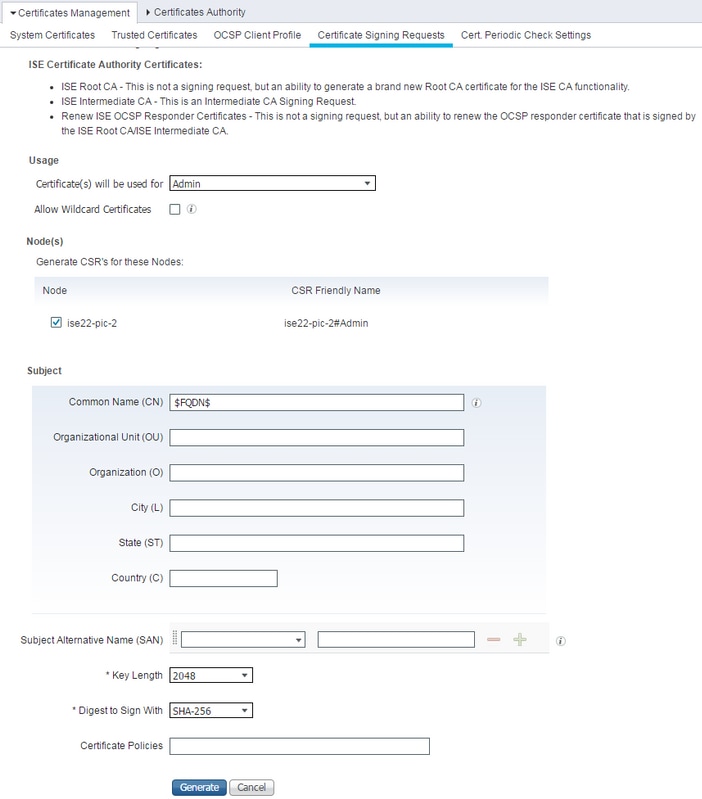
单击生成。系统随即会弹出新窗口,其中包含“导出生成的CSR:
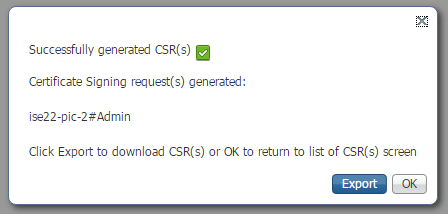
单击导出,保存生成的*.pem文件,并用CA签名。CSR签名后,导航回“证书”(Certificates)>“证书管理”(Certificates Management)>“证书签名请求”(Certificate Signing Requests)页面,选择您的CSR,然后点击“绑定证书”(Bind Certificate):
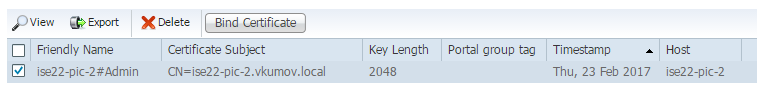
选择已与CA签名的证书,然后单击“提交”以应用更改:

单击“提交”(Submit)安装证书后,ISE PIC节点上的所有服务将重新启动。
步骤3.将辅助节点添加到部署。
ISE PIC允许在部署中有2个节点以实现高可用性。它不需要证书的双向信任(与通常的ISE部署相比)。 要向部署添加辅助节点,请导航至主ISE PIC节点上的“管理”>“部署”页,如图所示:
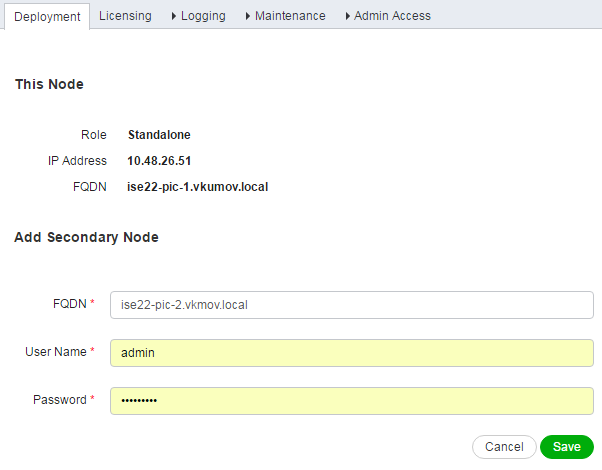
输入辅助节点的完全限定域名(FQDN),该节点的管理员凭据,然后单击保存。如果主ISE PIC节点无法验证其要求确认的第二个节点的管理证书,则在受信任存储中安装该证书。
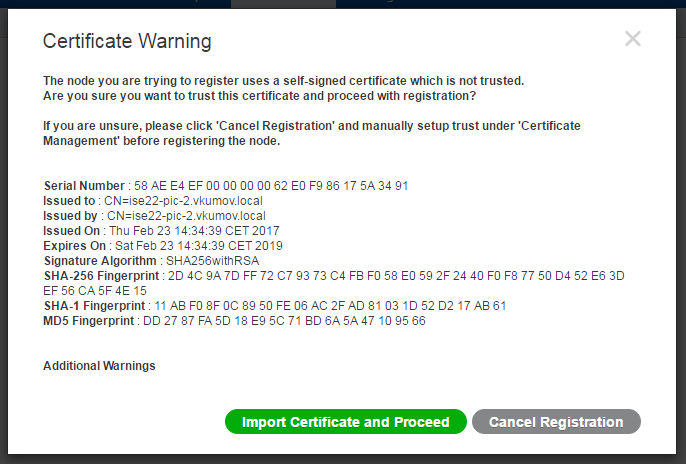
在这种情况下,单击Import Certificate and Proceed以将节点加入部署。您应收到节点添加成功的通知。辅助节点上的所有服务都会重新启动。
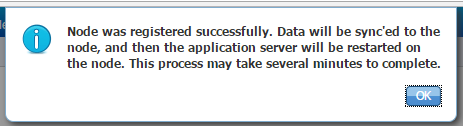
在10-20分钟内,节点应同步,节点的状态应从
配置Active Directory提供程序
ISE PIC使用Windows Management规范(WMI)从AD收集有关会话的信息,并像Pub/Sub通信一样,这意味着:
- ISE PIC订用某些事件
- 发生以下事件时,WMI会向ISE PIC发出警报:
- 4768(Kerberos票证授予)和4770(Kerberos票证续订)
- 会话目录中的条目过期(清除)
步骤1.将ISE PIC加入域。
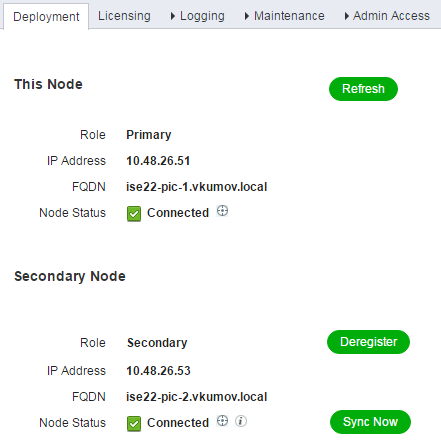
要将ISE PIC加入域,请导航至“提供程序”>“Active Directory”,然后单击“添加:
填写加入点名称和Active Directory域字段,然后单击提交以保存更改。加入点名称是仅在ISE PIC中使用的名称。Active Directory域是应加入ISE PIC的域的名称,它应可在ISE PIC上配置DNS服务器时进行解析。
创建加入点后,ISE PIC应询问您是否要将节点加入域。单击 Yes。您应会弹出一个窗口,提供加入域的凭据:
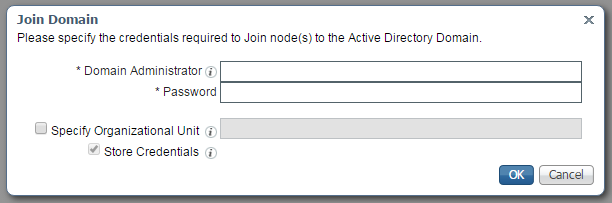
填写域管理员和密码字段并单击确定。
即使该字段称为域管理员,也无需使用管理员用户将ISE PIC加入域。此用户应具有足够的权限,以在域中创建和删除计算机帐户,或更改之前创建的计算机帐户的密码。在本文中可找到执行各种操作所需的Active Directory帐户权限。
但是,如果要使用WMI,则在加入期间需要使用域管理员凭据。配置WMI选项需要:
- 注册表更改
- 使用DCOM的权限
- 远程使用WMI的权限
- 读取AD域控制器的安全事件日志的权限
- Windows防火墙必须允许来自/流向ISE PIC的流量(在配置WMI期间将创建相应的Windows防火墙策略)
注意:存储凭据始终在ISE PIC上启用,因为终端探测和WMI配置需要它。ISE在内部存储加密。
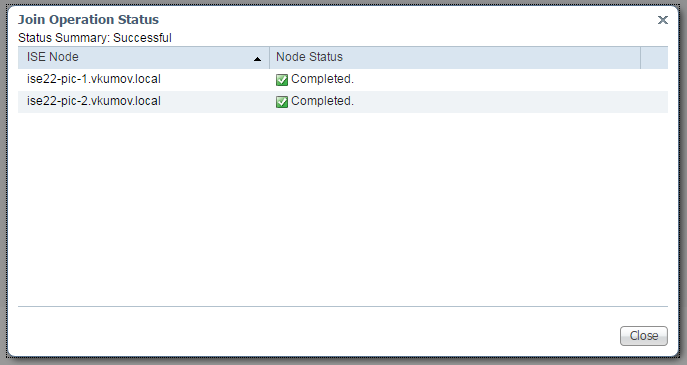
如图所示,ISE PIC在新窗口中显示操作结果:
步骤2.调整AD上的权限。
根据文档检查和调整用户在AD上的权限:身份服务引擎被动身份连接器(ISE-PIC)安装和管理员指南:
在域管理组中设置AD用户时的权限
对于Windows 2008 R2、Windows 2012和Windows 2012 R2,默认情况下,域管理员组对Windows操作系统中的某些注册表项没有完全控制。Active Directory管理员必须授予Active Directory用户对以下注册表项的完全控制权限
- HKEY_CLASSES_ROOT\CLSID\{76A64158-CB41-11D1-8B02-00600806D9B6}
- HKLM\Software\Classes\Wow6432Node\CLSID\{76A64158-CB41-11D1-8B02-00600806D9B6}
步骤3.添加PassiveID代理。
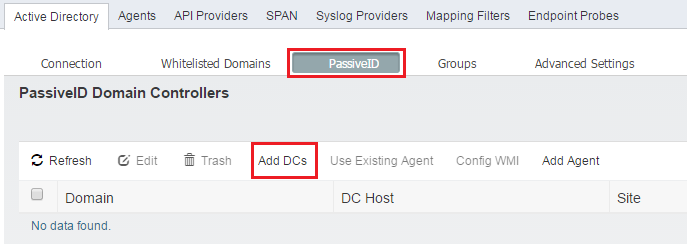
在“AD域”(AD domain)页面,导航至“被动ID”(PassiveID)选项卡,然后单击“添加DC”(Add DCs),如图所示:
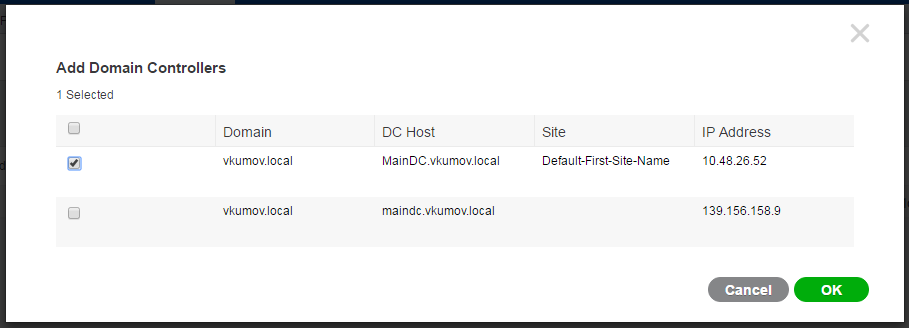
系统将弹出一个新窗口,ISE将加载所有可用域控制器的列表。选择要在其中配置WMI的DC,然后单击确定保存更改,如图所示:
选定的DC将添加到PassiveID域控制器列表。选择DC,然后单击“Config WMI”按钮:

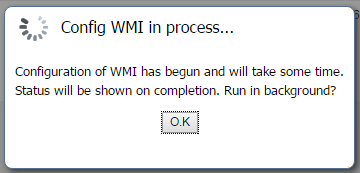
ISE PIC显示一条消息,表明配置过程正在进行:
几分钟后,它会向您显示一条消息,表明已在所选DC上成功配置WMI:

验证
部署
可通过以下几种方式检查部署状态:
部署页面
导航至“管理”>“部署”页,可以检查部署的当前状态:
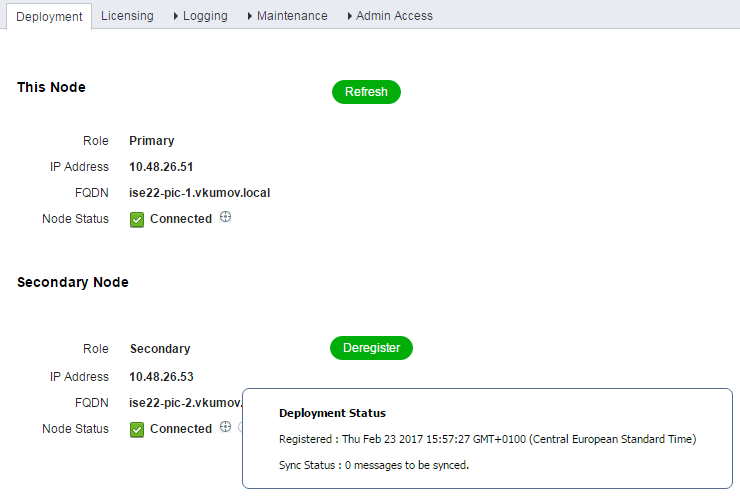
在此页中,辅助节点可以取消注册(如果需要)。可以启动手动同步,并检查同步状态。
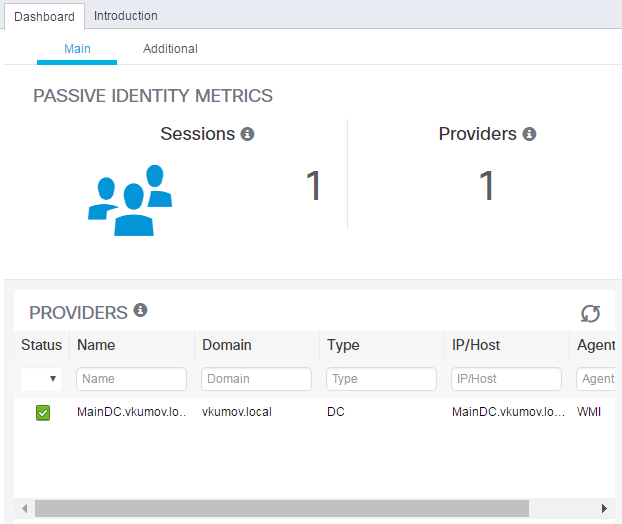
控制面板页面
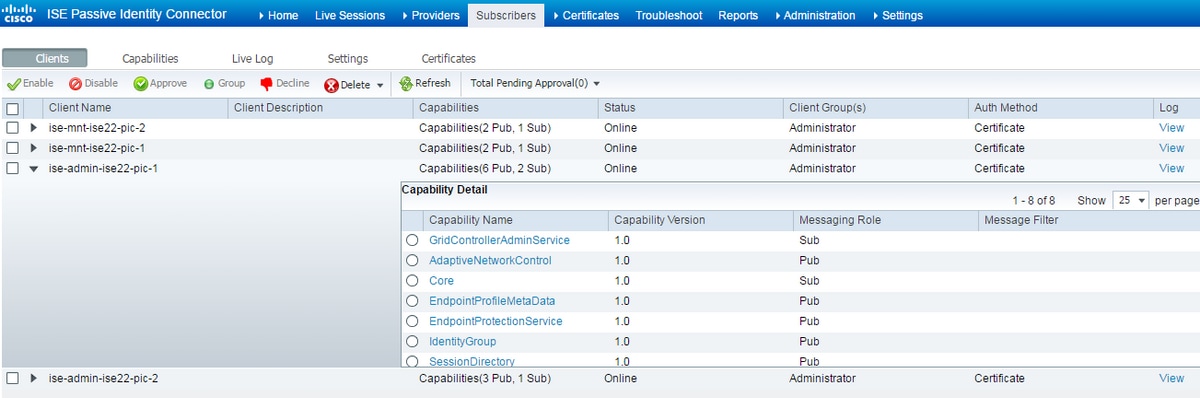
在ISE PIC主页上,有一个名为Subscribers的dashlet。使用此Dashlet,您可以检查ISE PIC节点的当前状态,如图所示:

ISE PIC为每个节点创建2个订用户 — 管理。所有节点都应处于在线状态,这意味着节点可恢复且运行正常。
用户
用户页面是ISE PIC主页中用户Dashlet的扩展版本。此页显示所有与pxGrid相关的,但ISE PIC节点的状态也可在此处检查:
系统概要
ISE PIC也允许监控节点的运行状况摘要。此Dashlet可在Home > Dashboard > Additional(其他)中找到:
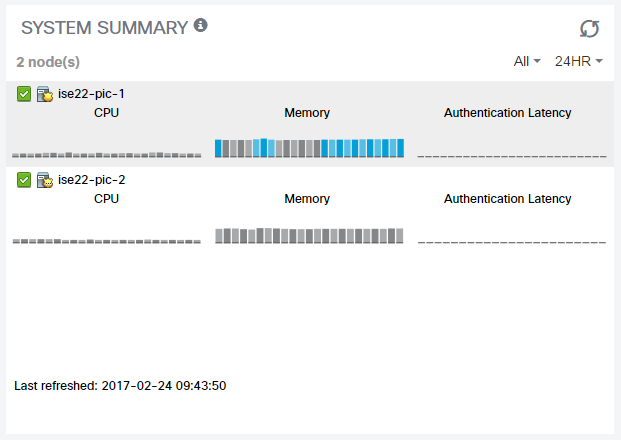
由于ISE PIC不执行任何身份验证/授权,因此身份验证延迟始终为0毫秒。
提供商和会话
主页
导航至“主页”>“控制面板”页时,可以检查提供程序状态、其找到的会话的数量和数量:
实时会话
有关所有已找到用户会话的详细信息,请访问Live Sessions页面:
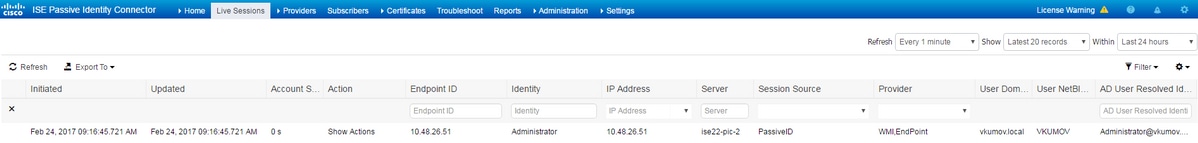
它包含以下信息:
- 提供程序 — 哪些提供程序用于标识此会话
- 已启动和更新 — 会话启动并相应更新时的时间戳
- IP地址 — 终端的地址
- 操作 — ISE可以执行的操作(例如,检查终端状态,或者如果ISE PIC与pxGrid集成,则发送请求以清除会话)
故障排除
部署
要排除部署和复制问题,请查看这些日志文件:
- replication.log
- deployment.log
- ise-psc.log
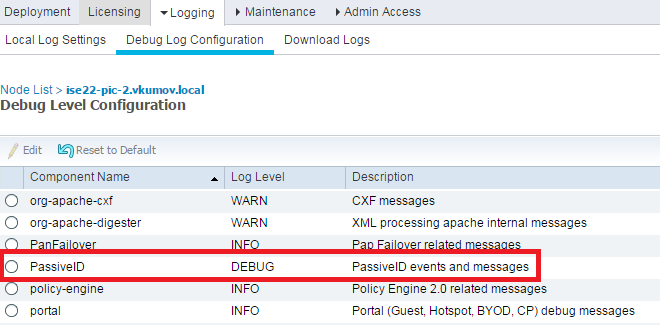
要启用调试,请导航至管理>日志>调试日志配置:
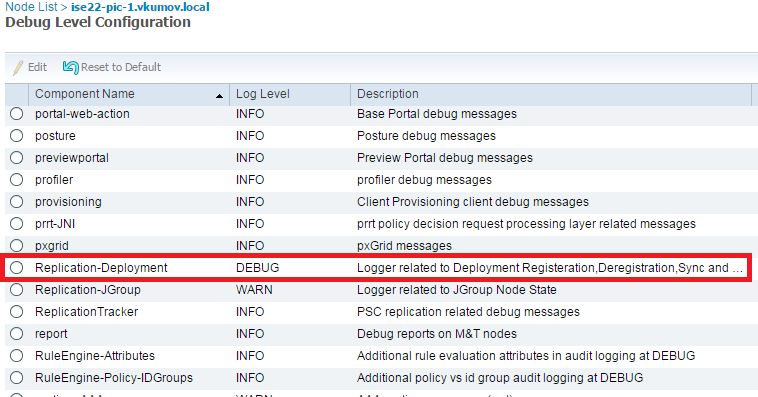
这些调试将写入replication.log文件。以下是正常复制过程的示例:
2017-02-24 10:11:06,893 INFO [pool-215-thread-1][] cisco.cpm.deployment.replication.PublisherImpl -::::- Calling the publisher job from clusterstate processor
2017-02-24 10:11:06,893 DEBUG [pool-214-thread-1][] cisco.cpm.deployment.replication.PublisherImpl -::::- Started executing publisher job
2017-02-24 10:11:06,894 DEBUG [pool-214-thread-1][] cisco.cpm.deployment.replication.PublisherImpl -::::- Number of messages with no sequence number is 0
2017-02-24 10:11:06,894 DEBUG [pool-214-thread-1][] cisco.cpm.deployment.replication.PublisherImpl -::::- Finished executing publisher job
2017-02-24 10:11:06,895 DEBUG [pool-214-thread-1][] api.services.persistance.dao.ChangeDataDaoImpl -::::- Data returned in getMinMaxBySequence method=[id=[63ce2fe0-f8cd-11e6-b0ad-005056991a2e],startTime=[0],endTime=[0],applied=[false],data length=[794],sequenceNumber=[502]2017-02-22 08:06:10.782]
2017-02-24 10:11:06,895 DEBUG [pool-214-thread-1][] api.services.persistance.dao.ChangeDataDaoImpl -::::- Data returned in getMinMaxBySequence method=[id=[3ded93c0-fa70-11e6-b684-005056990fbb],startTime=[0],endTime=[0],applied=[false],data length=[794],sequenceNumber=[1600]2017-02-24 10:04:26.364]
2017-02-24 10:11:06,895 DEBUG [pool-214-thread-1][] cisco.cpm.deployment.replication.ClientNodeProxy -::::- Calling setClusterState(name: ise22-pic-1, minSequence: 502, sequence: 1600, active: {ise22-pic-1-5015})
2017-02-24 10:11:06,896 INFO [pool-214-thread-1][] cisco.cpm.deployment.replication.PublisherImpl -::::- Finished sending the clusterState !!!
2017-02-24 10:11:06,899 DEBUG [pool-216-thread-1][] cisco.cpm.deployment.replication.NodeStateMonitorImpl -:::NodeStateMonitor:- MonitorJob starting
2017-02-24 10:11:06,901 DEBUG [pool-216-thread-1][] cisco.cpm.deployment.replication.ClientNodeProxy -:::NodeStateMonitor:- Calling getNodeStates()
2017-02-24 10:11:06,904 INFO [pool-216-thread-1][] cisco.cpm.deployment.replication.NodeStateMonitorImpl -:::NodeStateMonitor:- Nodes in distrubution: {ise22-pic-2=nodeName: ise22-pic-2, status: SYNC COMPLETED, transientStatus: , lastStatusTime: 1487927436906, seqNumber: 1600, createTime: 2017-02-24 10:04:26.364} --- Nodes in cluster: [name: ise22-pic-2, Address: ise22-pic-2-38077, sequence: 1600, createtime: 2017-02-24 10:04:26.364]
2017-02-24 10:11:06,904 DEBUG [pool-216-thread-1][] cisco.cpm.deployment.replication.NodeStateMonitorImpl -:::NodeStateMonitor:- Adding [ nodeName: ise22-pic-2, status: SYNC COMPLETED, transientStatus: , lastStatusTime: 1487927436906, seqNumber: 1600, createTime: 2017-02-24 10:04:26.364 ] to liveDeploymentMembers
2017-02-24 10:11:06,905 DEBUG [pool-216-thread-1][] api.services.persistance.dao.ChangeDataDaoImpl -:::NodeStateMonitor:- Data returned in getMinMaxBySequence method=[id=[63ce2fe0-f8cd-11e6-b0ad-005056991a2e],startTime=[0],endTime=[0],applied=[false],data length=[794],sequenceNumber=[502]2017-02-22 08:06:10.782]
2017-02-24 10:11:06,905 DEBUG [pool-216-thread-1][] api.services.persistance.dao.ChangeDataDaoImpl -:::NodeStateMonitor:- Data returned in getMinMaxBySequence method=[id=[3ded93c0-fa70-11e6-b684-005056990fbb],startTime=[0],endTime=[0],applied=[false],data length=[794],sequenceNumber=[1600]2017-02-24 10:04:26.364]
2017-02-24 10:11:06,905 INFO [pool-216-thread-1][] cisco.cpm.deployment.replication.NodeStateMonitorImpl -:::NodeStateMonitor:- Primary node current status minmum sequence[ 1600 ], cluster state: [ name: ise22-pic-1, minSequence: 502, sequence: 1600, active: {ise22-pic-1-5015} ]
2017-02-24 10:11:06,905 DEBUG [pool-216-thread-1][] cisco.cpm.deployment.replication.NodeStateMonitorImpl -:::NodeStateMonitor:- Processing node state [ name: ise22-pic-2, Address: ise22-pic-2-38077, sequence: 1600, createtime:2017-02-24 10:04:26.364 ]
2017-02-24 10:11:06,905 DEBUG [pool-216-thread-1][] cisco.cpm.deployment.replication.NodeStateMonitorImpl -:::NodeStateMonitor:- ise22-pic-2 - [ nodeName: ise22-pic-2, status: SYNC COMPLETED, transientStatus: , lastStatusTime: 1487927436906, seqNumber: 1600, createTime: 2017-02-24 10:04:26.364 ]
2017-02-24 10:11:06,905 DEBUG [pool-216-thread-1][] cisco.cpm.deployment.replication.NodeStateMonitorImpl -:::NodeStateMonitor:- Adding nodeName: ise22-pic-2, status: SYNC COMPLETED, transientStatus: , lastStatusTime: 1487927436906, seqNumber: 1600, createTime: 2017-02-24 10:04:26.364 to liveJGroupMembers
2017-02-24 10:11:06,905 INFO [pool-216-thread-1][] cisco.cpm.deployment.replication.NodeStateMonitorImpl -:::NodeStateMonitor:- No Of deployedNodes: [ 1 ], No Of liveJGroupNodes: [ 1 ], deadOrSyncInPrgMembersExist: [ false ], latestMinSequence: [ 502 ]
2017-02-24 10:11:06,905 DEBUG [pool-216-thread-1][] cisco.cpm.deployment.replication.NodeStateMonitorImpl -:::NodeStateMonitor:- deadOrSyncInPrgMembersExist =[false], minSequence=[1598],clusterState=[502]
来自ise-psc.log的消息:
2017-02-24 10:19:36,902 INFO [pool-216-thread-1][] api.services.persistance.dao.DistributionDAO -:::NodeStateMonitor:- Host Name: ise22-pic-2, DB 'SEC_REPLICATIONSTATUS' = SYNC COMPLETED, Node Persona: SECONDARY, ReplicationStatus obj status: SYNC_COMPLETED
常见问题:辅助节点不可访问
如果辅助节点变得不可达,则会显示在“管理”>“部署”页:
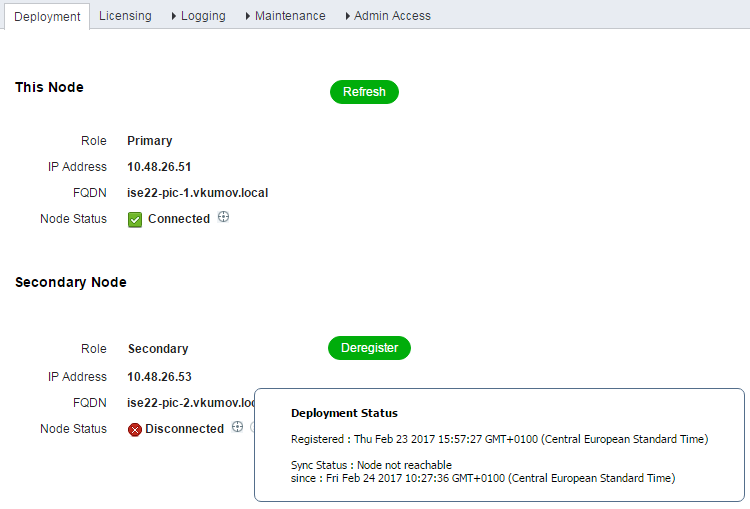
ise-psc.log包含以下消息:
2017-02-24 10:43:21,587 INFO [admin-http-pool155][] admin.restui.features.deployment.DeploymentIDCUIApi -::::- Replication status for node ise22-pic-2 = NODE NOT REACHABLE
此消息解释了哪些不可达,例如节点不响应ping:
2017-02-24 11:03:53,359 INFO [counterscheduler-call-1][] cisco.cpm.infrastructure.utils.GenericUtil -::::- Received pingNode response : Node is reachable
要采取的操作:检查备用节点的FQDN是否可解析,检查节点之间的基本网络连接。
如果应用程序在辅助节点上未处于运行状态或节点之间存在防火墙,则ise-psc.log可能会显示以下消息:
2017-02-24 11:08:14,656 INFO [Thread-10][] com.cisco.epm.util.NodeCheck -::::- Now checking against secondary pap ise22-pic-2 2017-02-24 11:08:14,656 INFO [Thread-10][] com.cisco.epm.util.NodeCheckHelper -::::- inside getHostConfigRemoteServer 2017-02-24 11:08:14,766 WARN [Thread-10][] deployment.client.cert.validator.HttpsCertPathValidatorImpl -::::- Error while connecting to host: ise22-pic-2.vkumov.local. java.net.ConnectException: Connection refused 2017-02-24 11:08:14,871 WARN [Thread-10][] com.cisco.epm.util.NodeCheckHelper -::::- Unable to retrieve the host config from standby pap java.net.ConnectException: Connection refused 2017-02-24 11:08:14,871 WARN [Thread-10][] com.cisco.epm.util.NodeCheckHelper -::::- returning null from getHostConfigRemoteServer 2017-02-24 11:08:14,871 INFO [Thread-10][] com.cisco.epm.util.NodeCheck -::::- remotePrimaryConfig.getNodeRoleStatus() NULL 2017-02-24 11:08:14,871 INFO [Thread-10][] com.cisco.epm.util.NodeCheck -::::- remoteClusterInfo.getDeploymentName NULL
要采取的操作:检查辅助节点上的应用状态,如果允许节点之间的所有连接,则检查网络连接。
Active Directory和WMI
要排除Active Directory WMI故障,请查看这些文件:
- passive-wmi.log
- passive-endpoint.log
- ise-psc.log
- ad_agent.log
而且,可以在Administration > Logging > Debug Log Configuration中启用有用的调试:
和:

以下是从passive-wmi.log获取的新会话的示例,其中启用了调试功能:
2017-02-24 11:36:22,584 DEBUG [Thread-11][] com.cisco.idc.dc-probe- New login event retrieved from Domain Controller. Identity Mapping.ticket =
instance of __InstanceCreationEvent
{
SECURITY_DESCRIPTOR = {1, 0, 20, 128, 96, 0, 0, 0, 112, 0, 0, 0, 0, 0, 0, 0, 20, 0, 0, 0, 2, 0, 76, 0, 3, 0, 0, 0, 0, 0, 20, 0, 69, 0, 15, 0, 1, 1, 0, 0, 0, 0, 0, 5, 18, 0, 0, 0, 0, 0, 24, 0, 69, 0, 0, 0, 1, 2, 0, 0, 0, 0, 0, 5, 32, 0, 0, 0, 32, 2, 0, 0, 0, 0, 24, 0, 65, 0, 0, 0, 1, 2, 0, 0, 0, 0, 0, 5, 32, 0, 0, 0, 61, 2, 0, 0, 1, 2, 0, 0, 0, 0, 0, 5, 32, 0, 0, 0, 32, 2, 0, 0, 1, 1, 0, 0, 0, 0, 0, 5, 18, 0, 0, 0};
TargetInstance =
instance of Win32_NTLogEvent
{
Category = 14339;
CategoryString = "Kerberos Authentication Service";
ComputerName = "MainDC.vkumov.local";
EventCode = 4768;
EventIdentifier = 4768;
EventType = 4;
InsertionStrings = {"Administrator", "vkumov.local", "S-1-5-21-2952046201-2792970045-1866348404-500", "krbtgt", "S-1-5-21-2952046201-2792970045-1866348404-502", "0x40810010", "0x0", "0x12", "2", "::1", "0", "", "", ""};
Logfile = "Security";
Message = "A Kerberos authentication ticket (TGT) was requested.
\n
\nAccount Information:
\n\tAccount Name:\t\tAdministrator
\n\tSupplied Realm Name:\tvkumov.local
\n\tUser ID:\t\t\tS-1-5-21-2952046201-2792970045-1866348404-500
\n
\nService Information:
\n\tService Name:\t\tkrbtgt
\n\tService ID:\t\tS-1-5-21-2952046201-2792970045-1866348404-502
\n
\nNetwork Information:
\n\tClient Address:\t\t::1
\n\tClient Port:\t\t0
\n
\nAdditional Information:
\n\tTicket Options:\t\t0x40810010
\n\tResult Code:\t\t0x0
\n\tTicket Encryption Type:\t0x12
\n\tPre-Authentication Type:\t2
\n
\nCertificate Information:
\n\tCertificate Issuer Name:\t\t
\n\tCertificate Serial Number:\t
\n\tCertificate Thumbprint:\t\t
\n
\nCertificate information is only provided if a certificate was used for pre-authentication.
\n
\nPre-authentication types, ticket options, encryption types and result codes are defined in RFC 4120.";
RecordNumber = 918032;
SourceName = "Microsoft-Windows-Security-Auditing";
TimeGenerated = "20170224103621.575178-000";
TimeWritten = "20170224103621.575178-000";
Type = "Audit Success";
};
TIME_CREATED = "131324061825752057";
};
, Identity Mapping.dc-domainname = vkumov.local , Identity Mapping.dc-connection-type = Current events , Identity Mapping.dc-name = MainDC.vkumov.local , Identity Mapping.dc-host = MainDC.vkumov.local/10.48.26.52 ,
2017-02-24 11:36:22,587 DEBUG [Thread-11][] com.cisco.idc.dc-probe- Replaced local IP. Identity Mapping.ticket =
instance of __InstanceCreationEvent
{
SECURITY_DESCRIPTOR = {1, 0, 20, 128, 96, 0, 0, 0, 112, 0, 0, 0, 0, 0, 0, 0, 20, 0, 0, 0, 2, 0, 76, 0, 3, 0, 0, 0, 0, 0, 20, 0, 69, 0, 15, 0, 1, 1, 0, 0, 0, 0, 0, 5, 18, 0, 0, 0, 0, 0, 24, 0, 69, 0, 0, 0, 1, 2, 0, 0, 0, 0, 0, 5, 32, 0, 0, 0, 32, 2, 0, 0, 0, 0, 24, 0, 65, 0, 0, 0, 1, 2, 0, 0, 0, 0, 0, 5, 32, 0, 0, 0, 61, 2, 0, 0, 1, 2, 0, 0, 0, 0, 0, 5, 32, 0, 0, 0, 32, 2, 0, 0, 1, 1, 0, 0, 0, 0, 0, 5, 18, 0, 0, 0};
TargetInstance =
instance of Win32_NTLogEvent
{
Category = 14339;
CategoryString = "Kerberos Authentication Service";
ComputerName = "MainDC.vkumov.local";
EventCode = 4768;
EventIdentifier = 4768;
EventType = 4;
InsertionStrings = {"Administrator", "vkumov.local", "S-1-5-21-2952046201-2792970045-1866348404-500", "krbtgt", "S-1-5-21-2952046201-2792970045-1866348404-502", "0x40810010", "0x0", "0x12", "2", "::1", "0", "", "", ""};
Logfile = "Security";
Message = "A Kerberos authentication ticket (TGT) was requested.
\n
\nAccount Information:
\n\tAccount Name:\t\tAdministrator
\n\tSupplied Realm Name:\tvkumov.local
\n\tUser ID:\t\t\tS-1-5-21-2952046201-2792970045-1866348404-500
\n
\nService Information:
\n\tService Name:\t\tkrbtgt
\n\tService ID:\t\tS-1-5-21-2952046201-2792970045-1866348404-502
\n
\nNetwork Information:
\n\tClient Address:\t\t::1
\n\tClient Port:\t\t0
\n
\nAdditional Information:
\n\tTicket Options:\t\t0x40810010
\n\tResult Code:\t\t0x0
\n\tTicket Encryption Type:\t0x12
\n\tPre-Authentication Type:\t2
\n
\nCertificate Information:
\n\tCertificate Issuer Name:\t\t
\n\tCertificate Serial Number:\t
\n\tCertificate Thumbprint:\t\t
\n
\nCertificate information is only provided if a certificate was used for pre-authentication.
\n
\nPre-authentication types, ticket options, encryption types and result codes are defined in RFC 4120.";
RecordNumber = 918032;
SourceName = "Microsoft-Windows-Security-Auditing";
TimeGenerated = "20170224103621.575178-000";
TimeWritten = "20170224103621.575178-000";
Type = "Audit Success";
};
TIME_CREATED = "131324061825752057";
};
, Identity Mapping.dc-domainname = vkumov.local , Identity Mapping.dc-connection-type = Current events , Identity Mapping.probe = WMI , Identity Mapping.event-local-ip-address = ::1 , Identity Mapping.dc-name = MainDC.vkumov.local , Identity Mapping.dc-host = MainDC.vkumov.local/10.48.26.52 , Identity Mapping.server = ise22-pic-2 , Identity Mapping.event-ip-address = 10.48.26.52 ,
2017-02-24 11:36:22,589 DEBUG [Thread-11][] com.cisco.idc.dc-probe- Received login event. Identity Mapping.ticket =
instance of __InstanceCreationEvent
{
SECURITY_DESCRIPTOR = {1, 0, 20, 128, 96, 0, 0, 0, 112, 0, 0, 0, 0, 0, 0, 0, 20, 0, 0, 0, 2, 0, 76, 0, 3, 0, 0, 0, 0, 0, 20, 0, 69, 0, 15, 0, 1, 1, 0, 0, 0, 0, 0, 5, 18, 0, 0, 0, 0, 0, 24, 0, 69, 0, 0, 0, 1, 2, 0, 0, 0, 0, 0, 5, 32, 0, 0, 0, 32, 2, 0, 0, 0, 0, 24, 0, 65, 0, 0, 0, 1, 2, 0, 0, 0, 0, 0, 5, 32, 0, 0, 0, 61, 2, 0, 0, 1, 2, 0, 0, 0, 0, 0, 5, 32, 0, 0, 0, 32, 2, 0, 0, 1, 1, 0, 0, 0, 0, 0, 5, 18, 0, 0, 0};
TargetInstance =
instance of Win32_NTLogEvent
{
Category = 14339;
CategoryString = "Kerberos Authentication Service";
ComputerName = "MainDC.vkumov.local";
EventCode = 4768;
EventIdentifier = 4768;
EventType = 4;
InsertionStrings = {"Administrator", "vkumov.local", "S-1-5-21-2952046201-2792970045-1866348404-500", "krbtgt", "S-1-5-21-2952046201-2792970045-1866348404-502", "0x40810010", "0x0", "0x12", "2", "::1", "0", "", "", ""};
Logfile = "Security";
Message = "A Kerberos authentication ticket (TGT) was requested.
\n
\nAccount Information:
\n\tAccount Name:\t\tAdministrator
\n\tSupplied Realm Name:\tvkumov.local
\n\tUser ID:\t\t\tS-1-5-21-2952046201-2792970045-1866348404-500
\n
\nService Information:
\n\tService Name:\t\tkrbtgt
\n\tService ID:\t\tS-1-5-21-2952046201-2792970045-1866348404-502
\n
\nNetwork Information:
\n\tClient Address:\t\t::1
\n\tClient Port:\t\t0
\n
\nAdditional Information:
\n\tTicket Options:\t\t0x40810010
\n\tResult Code:\t\t0x0
\n\tTicket Encryption Type:\t0x12
\n\tPre-Authentication Type:\t2
\n
\nCertificate Information:
\n\tCertificate Issuer Name:\t\t
\n\tCertificate Serial Number:\t
\n\tCertificate Thumbprint:\t\t
\n
\nCertificate information is only provided if a certificate was used for pre-authentication.
\n
\nPre-authentication types, ticket options, encryption types and result codes are defined in RFC 4120.";
RecordNumber = 918032;
SourceName = "Microsoft-Windows-Security-Auditing";
TimeGenerated = "20170224103621.575178-000";
TimeWritten = "20170224103621.575178-000";
Type = "Audit Success";
};
TIME_CREATED = "131324061825752057";
};
, Identity Mapping.dc-domainname = vkumov.local , Identity Mapping.dc-connection-type = Current events , Identity Mapping.probe = WMI , Identity Mapping.event-local-ip-address = ::1 , Identity Mapping.dc-name = MainDC.vkumov.local , Identity Mapping.event-user-name = Administrator , Identity Mapping.dc-host = MainDC.vkumov.local/10.48.26.52 , Identity Mapping.server = ise22-pic-2 , Identity Mapping.event-ip-address = 10.48.26.52 ,
从passive-endpoint.log进行终端检查的示例(在本例中,终端无法从ISE实现):
2017-02-23 13:48:29,298 INFO [EndPointProbe-Workers-Check-2][] com.cisco.idc.endpoint-probe- [PsExec-10.48.26.51] is User=vkumov.local/Administrator Still There ? ... 2017-02-23 13:48:32,335 INFO [EndPointProbe-Workers-Check-2][] com.cisco.idc.endpoint-probe- [PsExec-10.48.26.51] Identity check result is - > Endpoint UNREACHABLE
常见问题:ISE PIC抛出“无法在<DC name>...上运行可执行文件” 错误
如果用于将ISE PIC加入域的用户没有足够的权限,ISE PIC在WMI配置期间抛出错误:
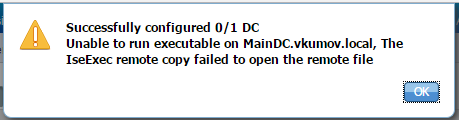
在ad_agent.log文件中可以找到相应的调试(Active Directory日志级别应设置为DEBUG):
26/02/2017 19:15:45,VERBOSE,139954093012736,SMBGSSContextNegotiate: state = 1,lwio/server/smbcommon/smbkrb5.c:460 26/02/2017 19:15:45,VERBOSE,139956055955200,Session 0x7f49bc001430 is eligible for reaping,lwio/server/rdr/session2.c:290 26/02/2017 19:15:45,VERBOSE,139954101405440,Error at ../../lsass/server/auth-providers/ad-open-provider/provider-main.c:7503 [code: C0000022],lsass/server/auth-providers/ad-open-provider/provider-main.c:7503 26/02/2017 19:15:45,VERBOSE,139954101405440,Extended Error code: 60190 (symbol: LW_ERROR_ISEEXEC_CP_OPEN_REMOTE_FILE),lsass/server/auth-providers/ad-open-provider/provider-main.c:7627 26/02/2017 19:15:45,VERBOSE,139954101405440,Error at ../../lsass/server/auth-providers/ad-open-provider/provider-main.c:7628 [code: C0000022],lsass/server/auth-providers/ad-open-provider/provider-main.c:7628 26/02/2017 19:15:45,VERBOSE,139954101405440,Error code: 5 (symbol: ERROR_ACCESS_DENIED),lsass/server/auth-providers/ad-open-provider/provider-main.c:7782 26/02/2017 19:15:45,VERBOSE,139954101405440,Error code: 5 (symbol: ERROR_ACCESS_DENIED),lsass/server/auth-providers/ad-open-provider/provider-main.c:7855 26/02/2017 19:15:45,VERBOSE,139954101405440,Error code: 5 (symbol: ERROR_ACCESS_DENIED),lsass/server/api/api2.c:2713 26/02/2017 19:15:45,VERBOSE,139956064347904,(session:ee880a4e15e682f4-08401b84f371a140) Dropping: LWMSG_STATUS_PEER_CLOSE,lwmsg/src/peer-task.c:625 26/02/2017 19:15:50,VERBOSE,139956055955200,RdrSocketRelease(0x7f496800b6e0, 38): socket is eligible for reaping,lwio/server/rdr/socket.c:2239
要采取的操作:使用域管理员凭据将ISE PIC节点重新加入域,或将用于加入操作的用户添加到AD中的域管理员组。
 反馈
反馈