Release Notes for Cisco Aironet 802.11a/b/g Client Adapters (CB21AG and PI21AG) Install Wizard 2.0
Available Languages
Table Of Contents
Release Notes for Cisco Aironet 802.11a/b/g Client Adapters (CB21AG and PI21AG)
Install Wizard 2.0Customized Installation Images (Notice to IT Professionals)
Client Adapter Software Compatibility
Enabling CCKM Fast Secure Roaming
Access Point Setting for LEAP or EAP-FAST Authentication
Reboot Required When Uninstalling ACU and ADU
Uninstalling Software Components
Auto Profile Selection Enables Scan of All Wireless Modes
Windows Wireless Network Connection Icon Shows Unavailable Connection (Windows XP Only)
Support for EAP-FAST Authentication
Additional LEAP Option Added to ADU
Support for Domain Logon with EAP-TLS
Host Based EAP Option Added to ADU
CCKM Fast Secure Roaming Supported with All EAP Types
Group Policy Delay Parameter Added to ADU
Installing or Upgrading Client Adapter Software
Installing the Client Adapter Software
Upgrading the Client Adapter Software
Resolved Install Wizard Caveats
Getting Bug Information on Cisco.com
Cisco Product Security Overview
Reporting Security Problems in Cisco Products
Obtaining Technical Assistance
Cisco Technical Support Website
Definitions of Service Request Severity
Obtaining Additional Publications and Information
Release Notes for Cisco Aironet 802.11a/b/g Client Adapters (CB21AG and PI21AG)
Install Wizard 2.0
Contents
This document contains the following sections:
•
Installing or Upgrading Client Adapter Software
•
Cisco Product Security Overview
•
Obtaining Technical Assistance
•
Obtaining Additional Publications and Information
Introduction
This document describes system requirements, important notes, new and changed information, installation and upgrade procedures, and caveats for CB21AG and PI21AG client adapter Install Wizard release 2.0 and the following software included in the Install Wizard file:
•
CB21AG and PI21AG client adapter driver release 2.0
•
Aironet Desktop Utility (ADU) release 2.0
System Requirements
You need the following in order to install Install Wizard 2.0 and use its software components:
•
One of the following Cisco Aironet client adapters:
–
CB21AG PC-Cardbus card
–
PI21AG PCI card
•
A computer running the Windows 2000 or XP operating system

Note
Cisco recommends a 300-MHz (or greater) processor.
•
Service Pack 2 for Windows XP
•
20 MB of free hard disk space (minimum)
•
128 MB of RAM or greater (recommended)
•
If your wireless network uses EAP-TLS or PEAP authentication, Certificate Authority (CA) and user certificates for EAP-TLS authentication or CA certificate for PEAP authentication
•
If your wireless network uses PEAP (EAP-GTC) authentication with a One-Time Password (OTP) user database:
–
A hardware token device from OTP vendors or the Secure Computing SofToken program (release 2.1 or later)
–
Your hardware or software token password
•
The Microsoft 802.1X supplicant, if your client adapter is installed on a Windows 2000 device and uses PEAP (EAP-MSCHAPV2) with machine authentication
•
All necessary infrastructure devices (such as access points, servers, gateways, user databases, etc.) must be properly configured for any authentication type you plan to enable on the client.
•
The following information from your system administrator:
–
The logical name for your workstation (also referred to as client name)
–
The protocols necessary to bind to the client adapter, such as TCP/IP
–
The case-sensitive service set identifier (SSID) for your RF network
–
If your network setup does not include a DHCP server, the IP address, subnet mask, and default gateway address of your computer
–
The wired equivalent privacy (WEP) keys of the access points with which your client adapter will communicate, if your wireless network uses static WEP for security
–
The username and password for your network account
–
Protected access credentials (PAC) file if your wireless network uses EAP-FAST authentication with manual PAC provisioning
Important Notes
Customized Installation Images (Notice to IT Professionals)

CautionUse caution when bundling the client adapter software into a customized installation image. If the registry settings are modified, the software may not install and uninstall properly.
Client Adapter Software Compatibility

CautionCisco Aironet CB21AG and PI21AG client adapter software is incompatible with other Cisco Aironet client adapter software. The Aironet Desktop Utility (ADU) must be used with CB21AG and PI21AG cards, and the Aironet Client Utility (ACU) must be used with all other Cisco Aironet client adapters.
Enabling CCKM Fast Secure Roaming
If you want to enable CCKM on the client adapter, you must choose the WPA/WPA2/CCKM security option, regardless of whether you want the adapter to use WPA or WPA2. The configuration of the access point to which your client adapter associates determines whether CCKM will be used with 802.1x, WPA, or WPA2.
Access Point Setting for LEAP or EAP-FAST Authentication
Access points must be set for both Network-EAP and open authentication in order to associate to CB21AG and PI21AG client adapters running LEAP with WPA/WPA2/CCKM or EAP-FAST.
GINA Error on Bootup
If your computer ever experiences a GINA error on bootup, boot to the safe mode command prompt. Then copy the msgina.dll file in the WinNT\System32 directory (Windows 2000) or Windows\System32 directory (Windows XP) over to a file named cscogina.dll. The copy command enables you to copy a source file (msgina.dll) to a destination file (cscogina.dll) within the same directory.
Reboot Required When Uninstalling ACU and ADU

CautionWhen you uninstall ACU and ADU, make sure you reboot your computer when prompted. Otherwise, the system may be rendered unable to boot, displaying the message "The Logon User Interface DLL cswGina.dll failed to load. Contact your system administrator to replace the DLL or restore the original DLL."
Uninstalling Software Components
All profiles and stored PAC files are deleted if you use the Uninstall the previous installation option on the Previous Installation Detected Install Wizard window to uninstall the client adapter software. Cisco recommends that you use the Profile Manager's export feature to save your profiles before uninstalling the software.
Profiles for PC-Cardbus Cards
The profiles for PC-Cardbus cards are tied to the slot in which the card is inserted. Therefore, you must always insert your PC-Cardbus card into the same slot, create profiles for both slots, or export the profiles for one slot and import them for the other slot.
Auto Profile Selection Enables Scan of All Wireless Modes
When you enable auto profile selection, the client adapter scans all wireless modes (5 GHz, 54 Mbps; 2.4 GHz, 11 Mbps; and 2.4 GHz, 54 Mbps) for an available network. The client ignores the selected profile's wireless mode setting, which was configured on the ADU Profile Management (Advanced) window. Using this method, the client does not need to drop the current connection nor change the current profile while looking for networks in other profiles.
ASTU Exit Option
The Exit option on the Aironet System Tray Utility (ASTU) pop-up menu closes both ASTU and ADU.
Windows Wireless Network Connection Icon Shows Unavailable Connection (Windows XP Only)
If your computer is running Windows XP and you configured your client adapter using ADU, the Windows Wireless Network Connection icon in the Windows system tray may be marked with a red X and show an unavailable connection even though a wireless connection exists. This condition is caused by a conflict between ADU and Windows XP's wireless network settings. Simply ignore the Windows icon and use the ASTU icon to check the status of your client adapter's wireless connection.
Supporting Documentation
The Cisco Aironet 802.11a/b/g Wireless LAN Client Adapters (CB21AG and PI21AG) Installation and Configuration Guide (part number OL-4211-03) pertains specifically to CB21AG and PI21AG client adapters. If you are using a Cisco Aironet 340, 350, or CB20A client adapter, refer to the Installation and Configuration Guide for that client adapter and your computer's operating system.
New and Changed Information
Support for EAP-FAST Authentication
Extensible Authentication Protocol-Flexible Authentication via Secure Tunneling (EAP-FAST) authentication is a new IEEE 802.1X authentication type available for Cisco Aironet CB21AG and PI21AG client adapters on computers running Windows 2000 or XP. EAP-FAST offers flexible easy deployment and management, supports a variety of user and password database types, supports server-initiated password expiration and change, and does not require digital certificates. Cisco developed EAP-FAST for customers who want to deploy an 802.1X EAP type that does not use certificates and provides protection from dictionary attacks. For example, a customer using Cisco LEAP who cannot enforce a strong password policy and does not want to use certificates can migrate to EAP-FAST for protection from dictionary attacks. EAP-FAST allows for a seamless migration from LEAP.
EAP-FAST uses a three-phased tunneled authentication process to provide advanced 802.1X EAP mutual authentication.
•
Phase 0 enables the client to dynamically provision a protected access credentials (PAC) when necessary. During this phase, a PAC is generated securely between the user and the network.
•
Phase 1 uses the PAC to establish a mutually authenticated and secure tunnel between the client and the RADIUS server. RADIUS servers that support EAP-FAST include Cisco Secure ACS version 3.2.3 and later.
•
Phase 2 performs client authentication in the established tunnel.
EAP-FAST is enabled or disabled for a specific profile through ADU. A variety of EAP-FAST configuration options are available, including how and when a username and password are entered to begin the authentication process and whether automatic or manual PAC provisioning is used.
The client adapter uses the username, password, and PAC to perform mutual authentication with the RADIUS server through the access point. The username and password need to be re-entered each time the client adapter is inserted or the Windows device is rebooted, unless you configure your adapter to use saved EAP-FAST credentials.
PACs are created by Cisco Secure ACS and are identified by an ID. The user obtains his or her own copy of the PAC from the server, and the ID links the PAC to the profile created in ADU. When manual PAC provisioning is enabled, the PAC is manually copied from the server and imported onto the client device.
The following rules govern PAC storage:
•
PACs are stored as encrypted data files in either the global or private store on the user's computer.
–
Global PACs can be accessed and used by any user at any logon stage. They are available before or during logon or after the user is logged off if the profile is not configured with the No Network Connection Unless User Is Logged In option.
–
Private PACs can be accessed and used only by the user who provisioned them or the system administrator.

Note
Global PACs are stored on C:\Document and Settings\All Users\Application Data\Cisco\cscostore, and private PACs are stored on C:\Document and Settings\user\
Application Data\Cisco\cscostore.
•
If automatic PAC provisioning is enabled and it occurs after the user is logged on, the PAC is stored in the private store of the currently logged-on user. Otherwise, the PAC is stored in the global store.
•
PAC files can be added or overwritten using the import feature.
•
PAC files can be removed using the delete feature. They are also deleted when you uninstall the client adapter software.
EAP-FAST authentication is designed to support the following user databases over a wireless LAN:
•
Cisco Secure ACS internal user database
•
Cisco Secure ACS ODBC user database
•
Windows NT/2000/2003 domain user database
•
LDAP user database
LDAP user databases (such as NDS) support only manual PAC provisioning while the other three user databases support both automatic and manual PAC provisioning.

Note
Refer to Chapter 5 of the Cisco Aironet 802.11a/b/g Wireless LAN Client Adapters (CB21AG and PI21AG) Installation and Configuration Guide (part number OL-4211-03) for instructions on enabling EAP-FAST authentication for your client adapter.
Additional LEAP Option Added to ADU
An Automatically Prompt for User Name and Password option has been added to the LEAP Settings window in ADU. This option requires you to enter a separate LEAP username and password (which are registered with the RADIUS server) in addition to your regular Windows login in order to start the LEAP authentication process.
Support for Domain Logon with EAP-TLS
The CB21AG and PI21AG client adapters now support domain logon with EAP-TLS. This feature enables you to attempt to log into a domain using machine authentication with a machine certificate and machine credentials. Doing so enables your computer to connect to the network prior to user logon.
To support this feature, a new check box has been added to the Define Certificate window in ADU. The check box, which is entitled Use Machine Information for Domain Logon, is disabled by default.
•
If the check box is checked, a machine certificate is always tried at domain logon (before the user logs on).
•
If the check box is not checked, machine authentication is not performed. Authentication does not occur until the user is logged in.
Follow these steps to ensure that domain logon with EAP-TLS functions properly.
Step 1
Follow your organization's standard procedure to obtain a machine certificate from the server and ensure that client machine access is enabled on the server.
Step 2
Ensure that the permissions for the MachineKeys folder, which stores the certificate pair keys for both the computer and users, are set correctly. Refer to Microsoft knowledgebase article Q278381 for information on correctly setting up folder permissions:
http://support.microsoft.com/default.aspx?scid=kb;en-us;Q278381

Note
If you ever change permissions on higher-level directories and those settings are applied to all subdirectories, you may need to reset the permissions for the MachineKeys folder.
Step 3
Create and activate a profile that uses EAP-TLS authentication and has the Use Machine Information for Domain Logon check box checked.
Step 4
When you check the Use Machine Information for Domain Logon check box, a new check box entitled Always Do User Authentication becomes active.
•
Check this check box if you want the client to switch from using machine authentication to using user authentication after you log on using your username and password.
•
Uncheck this check box if you want the client to continue to use machine authentication after your computer logs into the domain.
Host Based EAP Option Added to ADU
A new option, entitled Host Based EAP, has been added to the list of 802.1x EAP Type options on the Profile Management (Security) window in ADU. This option enables client adapters that are configured through ADU to attempt to log into a domain using PEAP (EAP-MSCHAP V2) machine authentication with machine credentials. Doing so enables your computer to connect to the network prior to user logon. Follow these steps to enable this authentication type.

Note
Because this feature requires the Microsoft Wireless Configuration Manager to start and stop as you switch between host-based EAP and non-host-based EAP profiles, it works only for users with administrator or power-user privileges. An error message appears if you attempt to switch to or from a host-based EAP profile and you do not have the proper permissions.

Note
To use this feature on a computer running Windows 2000, your computer must have the Microsoft 802.1X supplicant installed.

Note
Host Based EAP is not included in the list of WPA/WPA2/CCKM EAP Type options on the Profile Management (Security) window in ADU because this feature is not supported for use with WPA or WPA2.
Step 1
Create a profile in ADU that specifies Host Based EAP as the 802.1x EAP Type.
Step 2
Activate this profile. The Microsoft Wireless Configuration Manager starts.
Step 3
Click Start > Settings > Control Panel > Network and Dial-up Connections or Network Connections.
Step 4
Right-click your wireless connection.
Step 5
Click Properties. The Connection Properties window appears.
Step 6
Perform one of the following:
•
On Windows 2000, click the Authentication tab.
•
On Windows XP, choose the Wireless Networks tab, make sure that the Use Windows to configure my wireless network settings check box is checked, click the SSID of the access point to which you want the client adapter to associate from the list of available networks, click Configure, and choose the Authentication tab.
Step 7
For EAP type, choose Protected EAP (PEAP).
Step 8
Configure any applicable settings on the Protected EAP Properties window and subwindows.
Step 9
After you have finished the configuration, PEAP authentication should begin. Depending on the configuration settings you selected, you may be prompted for your PEAP username, password, and domain name. You may need to minimize ADU in order to access the pop-up window that prompts you for your credentials.

Note
You can have multiple host-based EAP profiles in ADU, but the Microsoft Wireless Configuration Manager maintains only one configuration. If you want to use different PEAP property settings for different host-based EAP profiles, you need to repeat the previous steps beginning with Step 2 every time you switch to a different host-based EAP profile.

Note
When you activate a host-based EAP profile, the Microsoft Wireless Configuration Manager takes control of the client adapter's authentication attempt. However, when you activate a non-host-based EAP profile, ADU assumes this control.

Note
If you experience problems while using a host-based EAP profile, make sure that 802.1X authentication is disabled for any other network connection.
Support for WPA2
Wi-Fi Protected Access 2 (WPA2) is now available for use with CB21AG and PI21AG client adapters. WPA2 is a standards-based security solution from the Wi-Fi Alliance that provides data protection and access control for wireless LAN systems. WPA is compatible with the IEEE 802.11i standard but was implemented prior to the standard's ratification; WPA2 is the Wi-Fi Alliance's implementation of the ratified IEEE 802.11i standard.
WPA uses Temporal Key Integrity Protocol (TKIP) and message integrity check (MIC) for data protection while WPA2 uses the stronger Advanced Encryption Standard encryption algorithm using Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (AES-CCMP). Both WPA and WPA2 use 802.1X for authenticated key management.
WPA and WPA2 support two mutually exclusive key management types: WPA/WPA2 and WPA/WPA2 passphrase (also known as WPA pre-shared key or WPA-PSK). Using WPA or WPA2, clients and the authentication server authenticate to each other using an EAP authentication method, and the client and server generate a pairwise master key (PMK). The server generates the PMK dynamically and passes it to the access point. Using WPA or WPA2 passphrase, however, you configure a passphrase (or pre-shared key) on both the client and the access point, and that passphrase is used as the PMK.
To enable WPA or WPA2 on your client adapter, you must create a profile that uses a WPA/WPA2 passphrase or WPA/WPA2/CCKM with LEAP, EAP-FAST, EAP-TLS, PEAP (EAP-GTC), or PEAP (EAP-MSCHAP V2).

Note
WPA must also be enabled on the access point. To use WPA, access points must use Cisco IOS Release 12.2(11)JA or later. To use WPA2, access points must use Cisco IOS Release 12.3(2)JA or later. Refer to the documentation for your access point for instructions on enabling this feature.
CCKM Fast Secure Roaming Supported with All EAP Types
CCKM fast secure roaming is now supported for use with all EAP authentication types [LEAP, EAP-FAST, EAP-TLS, PEAP (EAP-GTC), and PEAP (EAP-MSCHAP V2)]. To enable this feature on your client adapter, you must create a profile that uses WPA/WPA2/CCKM with one of these EAP authentication types.

Note
If you want to enable CCKM fast secure roaming on your client adapter, you must choose the WPA/WPA2/CCKM security option on the Profile Management (Security) window, regardless of whether you want the adapter to use WPA or WPA2. The configuration of the access point to which your client adapter associates determines whether CCKM will be used with 802.1x, WPA, or WPA2.

Note
This feature must also be enabled on the access point. Access points must use Cisco IOS Release 12.2(11)JA or later to enable CCKM fast secure roaming. Refer to the documentation for your access point for instructions on enabling this feature.

Note
The Microsoft Wireless Configuration Manager and the Microsoft 802.1X supplicant, if installed, must be disabled in order for CCKM fast secure roaming to operate correctly. If your computer is running Windows XP and you chose to configure your client adapter using ADU during installation, these features should already be disabled. Similarly, if your computer is running Windows 2000, the Microsoft 802.1X supplicant, if installed, should already be disabled.
Support for Wi-Fi Multimedia
Wi-Fi Multimedia (WMM) is a component of the IEEE 802.11e wireless LAN standard for quality of service (QoS). It specifically supports priority tagging and queuing. QoS is an access point feature that enables networking professionals to provide preferential treatment to certain traffic at the expense of other traffic. Without QoS, the access point offers best-effort service to each packet, regardless of the packet contents or size. Implementing QoS in a wireless LAN makes network performance more predictable and bandwidth usage more effective.
Cisco recommends that you enable WMM if your computer is running a time-sensitive application for QoS-aware clients such as voice or video (for example, Cisco IP SoftPhone).
WMM is supported automatically on the client adapter in the software included in Install Wizard 2.0. However, you must enable the Windows QoS Packet Scheduler to ensure WMM support. Follow the instructions in the Cisco Aironet 802.11a/b/g Wireless LAN Client Adapters (CB21AG and PI21AG) Installation and Configuration Guide (part number OL-4211-03) to enable the QoS Packet Scheduler.

Note
The QoS Packet Scheduler must be installed before you can enable it. It comes preinstalled on Windows XP; however, you must install it on Windows 2000.

Note
QoS and WMM must also be enabled on the access point to which the client will associate. These features are supported on the access point in Cisco IOS Release 12.3(2)JA or later. Refer to the documentation for your access point for instructions on enabling these features.
Group Policy Delay Parameter Added to ADU
A new parameter entitled Group Policy Delay has been added to the Profile Management (Security) window in ADU. This parameter enables you to specify how much time elapses before the Windows logon process starts Group Policy, a Windows feature used by administrators to specify configuration options for groups of users. The objective is to delay the start of Group Policy until wireless network authentication occurs.
The Group Policy Delay parameter is available on the Profile Management (Security) window only when EAP-based authentication is selected. The value that you set for this parameter goes into effect after the computer reboots with this profile set as the active profile.
Range: 0 to 65535 seconds (However, Microsoft supports only values between 30 and 600 seconds.)
Default: 60 secondsA Microsoft hot fix is required in order to use this feature on computers running Windows 2000. (The hot fix is incorporated into Windows XP Service Pack 2 and later.) Follow the steps below to install the hot fix on a Windows 2000 machine.

Note
You must be a registered Cisco customer and log into Cisco.com in order to download the hot fix. If you are unable to access the hot fix from Cisco.com, contact Microsoft Support to obtain it. The Windows 2000 support page provides the contact information:
http://support.microsoft.com/oas/default.aspx?&c1=508&gprid=7274&
Step 1
Use your computer's web browser to access the following URL:
http://www.cisco.com/cgi-bin/tablebuild.pl/aironet_hotfix
Step 2
Click the hot fix file (userenv.zip).
Step 3
Complete the encryption authorization form and click Submit.
Step 4
Click the file again to download it.
Step 5
Save the file to your computer's hard drive.
Step 6
Find the file using Windows Explorer, double-click it, and extract its files to a folder.
Step 7
Reboot your computer and press F8 while your computer is booting.
Step 8
When the boot menu appears, select Safe Mode with Command Prompt.

Note
You must complete this procedure in safe mode; otherwise, system file protection (SFP) will silently restore the original version of the file you are replacing.
Step 9
Copy the hot fix file (userenv.dll) to %systemroot%\System32 and overwrite the existing version of this file.
Step 10
Delete the copy of userenv.dll in %systemroot%\System32\DllCache.
Step 11
Reboot your computer.
New Site Survey Utility
A site survey utility is now available for the CB21AG and PI21AG client adapters. The utility, which is designed to be used by people responsible for conducting a site survey, is useful in determining the best placement of infrastructure devices within a wireless network. The utility is a stand-alone application, separate from ADU, that runs from an executable file. If you check the Install Cisco Aironet Site Survey Utility check box during installation of Install Wizard 2.0, the site survey executable file is installed in the C:\Program Files\Cisco Aironet directory (unless you specify a different directory).
During a site survey, the current status of the network is read from the client adapter, and the status display is updated four times per second so you can accurately gauge network performance. The feedback that you receive can help you to eliminate areas of low RF signal levels that can result in a loss of connection between the client adapter and its associated access point (or other infrastructure device).
To open the site survey utility, choose Start > Programs > Cisco Aironet > Aironet Site Survey Utility. (If you specify a different program folder during installation, you must access the site survey utility from that folder.)

Note
The site survey utility is supported for use with only CB21AG and PI21AG client adapters.

Note
Refer to Appendix F of the Cisco Aironet 802.11a/b/g Wireless LAN Client Adapters (CB21AG and PI21AG) Installation and Configuration Guide (part number OL-4211-03) for more information on the site survey utility.
Other Changes
The following changes have been made to the CB21AG and PI21AG client adapter software and are included in Install Wizard 2.0:
•
The client adapter must be inserted in your computer before you attempt to install or upgrade to Install Wizard 2.0. If your client adapter is not inserted, the software cannot be installed.
•
The Signal Strength Display Units parameter on the Display Settings window has been removed in ADU 2.0. All signal strength values are shown in decibels with respect to milliwatts (dBm) or decibels (dB).
•
The LEAP Authentication Status window now includes a Show Minimized Next Time check box that causes the window to appear minimized in the Windows taskbar on future LEAP authentication attempts.
•
The Manual LEAP Login menu option in both ADU and ASTU has been changed to Manual Login so that it can apply to both LEAP and EAP-FAST. This option enables you to manually invoke the authentication process for a profile that is configured to use a manually prompted LEAP or EAP-FAST username and password.
•
The Reauthenticate menu option in both ADU and ASTU is now available for all EAP authentication types [LEAP, EAP-FAST, EAP-TLS, PEAP (EAP-GTC), and PEAP (EAP-MSCHAP V2)]. This option is used to force your client adapter to attempt to reauthenticate using the username and password of the current profile.
•
The Available Infrastructure and Ad Hoc Networks window in ADU now displays the client adapter's signal-to-noise ratio (SNR) rather than its signal strength.
•
The Advanced Status window in ADU and the Connection Status window in ASTU now display the Current Receive Rate and the Current Transmit Rate rather than the Current Link Speed. These values indicate the rate at which your client adapter is currently receiving or transmitting data packets, respectively.
•
The Tool Tip window in ASTU now displays the 802.11 mode that the client adapter is using for communications. This value appears to the right of the Link Speed value. Possible values for the 802.11 mode are 11a, 11b, and 11g.
Installing or Upgrading Client Adapter Software
This section describes how to initially install or upgrade to CB21AG and PI21AG Install Wizard 2.0 on a computer running Windows 2000 or XP. If the client adapter software is not installed on your computer, follow the instructions in the "Installing the Client Adapter Software" section below. If you are upgrading your client adapter software to release 2.0, follow the instructions in the "Upgrading the Client Adapter Software" section.
Installing the Client Adapter Software
Follow these steps to install CB21AG and PI21AG Install Wizard 2.0 on your computer.

CautionDo not eject your client adapter at any time during the installation process, including during the reboot.

Note
Only one wireless client adapter can be installed and used at a time. The software does not support the use of multiple cards.
Step 1
Make sure the client adapter is inserted in your computer.

Note
If your client adapter is not inserted, the software cannot be installed.
Step 2
Use your computer's web browser to access the following URL:
http://www.cisco.com/public/sw-center/sw-wireless.shtml
Step 3
Click Option #2: Aironet Wireless Software Display Tables.

Note
If you prefer to use an automated tool, you can download software from the Software Selector tool instead of the display tables. To do so, click Option #1: Aironet Wireless Software Selector, follow the instructions on the window, and go to Step 7.
Step 4
Click Cisco Aironet Wireless LAN Client Adapters.
Step 5
Under Aironet Client Adapter Installation Wizard (For Windows), click 802.11a/b/g (CB21AG, PI21AG).
Step 6
Click the Win-Client-802.11a-b-g-Ins-Wizard-v20.exe file.
Step 7
Complete the encryption authorization form; then read and accept the terms and conditions of the Software License Agreement.
Step 8
Click the file again to download it.
Step 9
Save the file to your computer's hard drive.
Step 10
Use Windows Explorer to find the file.
Step 11
Double-click the file. The "Starting InstallShield Wizard" message appears followed by the Preparing Setup window (see Figure 1) and the Cisco Aironet Installation Program window (see Figure 2).
Figure 1 Preparing Setup Window
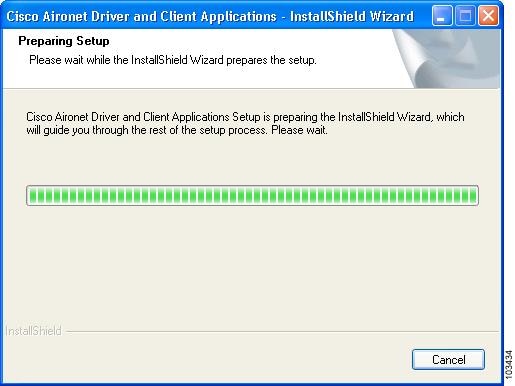
Figure 2 Cisco Aironet Installation Program Window

Step 12
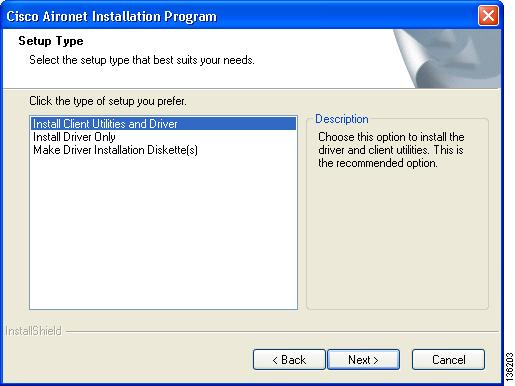
Click Next. The Setup Type window appears (see Figure 3).
Figure 3 Setup Type Window
Step 13
Choose one of the following options:

Note
To ensure compatibility among software components, Cisco recommends that you install the client utilities and driver.
•
Install Client Utilities and Driver—Installs the client adapter driver and client utilities.
•
Install Driver Only—Installs only the client adapter driver. If you choose this option, click Next and go to Step 26.
•
Make Driver Installation Diskette(s)—Enables you to create driver installation diskettes that can be used to install drivers using the Windows Device Manager.
Step 14
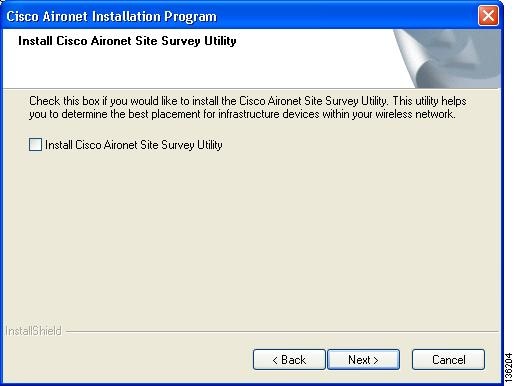
Click Next. The Install Cisco Aironet Site Survey Utility window appears (see Figure 4).
Figure 4 Install Cisco Aironet Site Survey Utility Window
Step 15
Check the Install Cisco Aironet Site Survey Utility check box if you want to install a utility that helps you to determine the best placement of infrastructure devices within your wireless network. Click Next.

Note
The site survey utility is a stand-alone application, separate from ADU, that runs from an executable file. If you check the Install Cisco Aironet Site Survey Utility check box, the Install Wizard installs the site survey executable file in the C:\Program Files\Cisco Aironet directory (unless you specify a different directory in Step 17).
Step 16
If a message appears indicating that you are required to restart your computer at the end of the installation process, click Yes.

Note
If you click No, you are asked to confirm your decision. If you proceed, the installation process terminates.
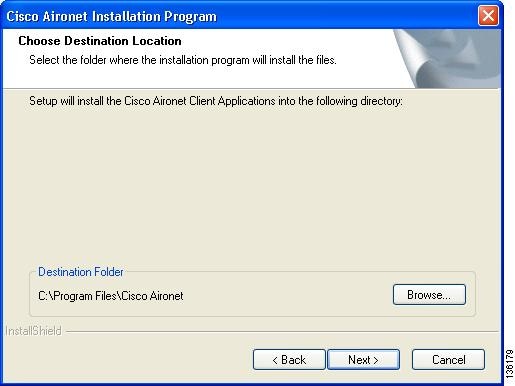
The Choose Destination Location window appears (see Figure 5).
Figure 5 Choose Destination Location Window
Step 17
Perform one of the following:
•
If you chose the first option in Step 13, click Next to install the client utility files in the C:\Program Files\Cisco Aironet directory.

Note
If you want to install the client utilities in a different directory, click Browse, choose a different directory, click OK, and click Next.
•
If you chose the Make Driver Installation Diskette(s) option in Step 13, insert a floppy disk into your computer and click Next to copy the driver to the diskette. Go to Step 26.

Note
If you want to copy the driver to a different drive or directory, click Browse, choose a new location, click OK, and click Next.
Step 18
The Select Program Folder window appears (see Figure 6).
Figure 6 Select Program Folder Window

Step 19
Click Next to add program icons to the Cisco Aironet program folder.

Note
If you want to specify a different program folder, choose a folder from the Existing Folders list or type a new folder name in the Program Folder field and click Next.
Step 20
If your computer is running Windows 2000, go to Step 26. If your computer is running Windows XP, the IMPORTANT: Please Read! window appears (see Figure 7).
Figure 7 IMPORTANT: Please Read! Window

Step 21
Read the information displayed and click Next. The Choose Configuration Tool window appears (see Figure 8).
Figure 8 Choose Configuration Tool Window

Step 22
Choose one of the following options based on the tool you want to use to configure your client adapter:
•
Cisco Aironet Desktop Utility (ADU)—Enables you to configure your client adapter using ADU.
•
Third-Party Tool—Enables you to configure your client adapter using a third-party tool such as the Microsoft Wireless Configuration Manager in Windows XP.

Note
If you choose Cisco Aironet Desktop Utility (ADU) above, the Microsoft Wireless Configuration Manager is disabled. If you ever manually enable it, you are prompted to disable it whenever ADU is activated.
Step 23
Click Next.
Step 24
If you chose Cisco Aironet Desktop Utility (ADU) in Step 22, go to Step 26. If you chose Third-Party Tool, the Enable Tray Icon window appears (see Figure 9).
Figure 9 Enable Tray Icon Window
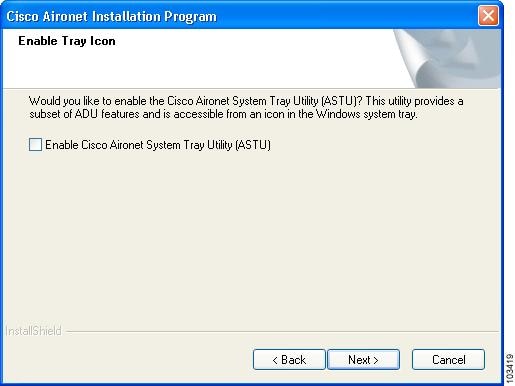
Step 25
Check the Enable Cisco Aironet System Tray Utility (ASTU) check box if you want to be able to use ASTU even though you have chosen to configure your client adapter through a third-party tool instead of ADU and click Next.
Step 26
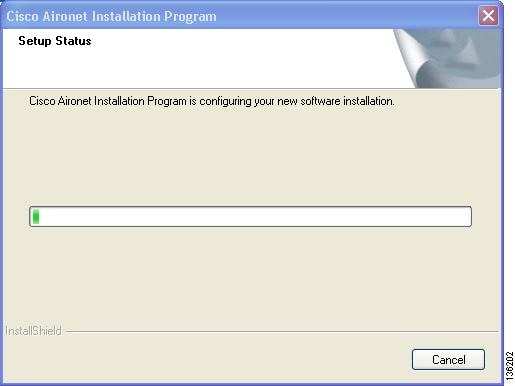
When prompted to insert your client adapter, click OK. The Setup Status window appears (see Figure 10).
Figure 10 Setup Status Window
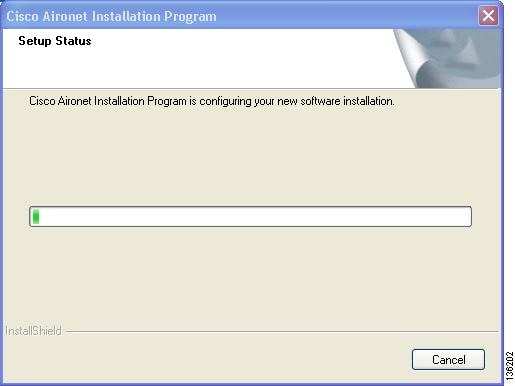
The installation process begins, and you are notified as each software component is installed.
Step 27
When a message appears indicating that your computer needs to be rebooted, click OK and allow your computer to restart.
Step 28
If the Windows Found New Hardware Wizard appears after your computer reboots, click Next, allow the wizard to install the software for the client adapter, and click Finish.
Step 29
If your network setup does not include a DHCP server and you plan to use TCP/IP, follow these steps for your operating system.
•
Windows 2000
a.
Double-click My Computer, Control Panel, and Network and Dial-up Connections.
b.
Right-click Local Area Connection x (where x represents the number of the connection).
c.
Click Properties.
d.
In the Components Checked Are Used by This Connection field, click Internet Protocol (TCP/IP) and Properties.
e.
Choose Use the following IP address and enter the IP address, subnet mask, and default gateway address of your computer (which can be obtained from your system administrator).
f.
Click OK to close each open window.
•
Windows XP
a.
Double-click My Computer, Control Panel, and Network Connections.
b.
Right-click Wireless Network Connection x (where x represents the number of the connection).
c.
Click Properties.
d.
In the This Connection Uses the Following Items field, click Internet Protocol (TCP/IP) and Properties.
e.
Choose Use the following IP address and enter the IP address, subnet mask, and default gateway address of your computer (which can be obtained from your system administrator).
f.
Click OK to close each open window.
Step 30
If you are prompted to restart your computer, click Yes. The installation is complete.
Upgrading the Client Adapter Software
Follow these steps to upgrade your CB21AG or PI21AG client adapter software to release 2.0 using the settings that were selected during the last installation.

Note
If you want to upgrade your client adapter software using new installation settings, you must uninstall the previous installation [see the instructions in Chapter 9 of the Cisco Aironet 802.11a/b/g Wireless LAN Client Adapters (CB21AG and PI21AG) Installation and Configuration Guide] and then follow the instructions in the "Installing the Client Adapter Software" section to install the new software.
Step 1
Make sure the client adapter is inserted in your computer.

Note
If your client adapter is not inserted, the software cannot be upgraded.
Step 2
Use your computer's web browser to access the following URL:
http://www.cisco.com/public/sw-center/sw-wireless.shtml
Step 3
Click Option #2: Aironet Wireless Software Display Tables.

Note
If you prefer to use an automated tool, you can download software from the Software Selector tool instead of the display tables. To do so, click Option #1: Aironet Wireless Software Selector, follow the instructions on the window, and go to Step 7.
Step 4
Click Cisco Aironet Wireless LAN Client Adapters.
Step 5
Under Aironet Client Adapter Installation Wizard (For Windows), click 802.11a/b/g (CB21AG, PI21AG).
Step 6
Click the Win-Client-802.11a-b-g-Ins-Wizard-v20.exe file.
Step 7
Complete the encryption authorization form; then read and accept the terms and conditions of the Software License Agreement.
Step 8
Click the file again to download it.
Step 9
Save the file to your computer's hard drive.
Step 10
Use Windows Explorer to find the file.
Step 11
Double-click the file. The "Starting InstallShield Wizard" message appears followed by the Preparing Setup window (see Figure 11) and the Previous Installation Detected window (see Figure 12).
Figure 11 Preparing Setup Window
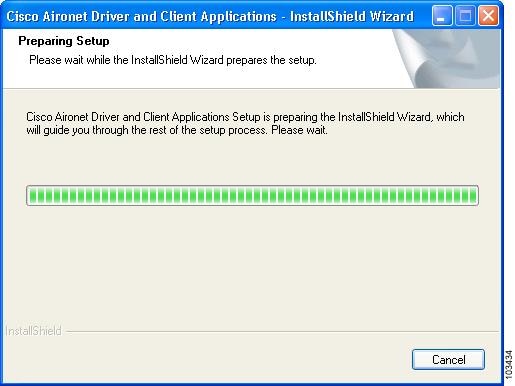
Figure 12 Previous Installation Detected Window
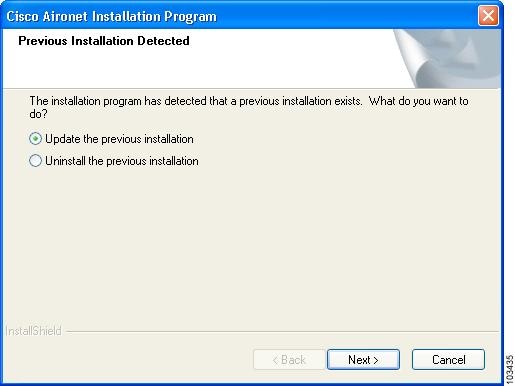
Step 12
Choose Update the previous installation and click Next.
Step 13
When a message appears indicating that you are required to restart your computer at the end of the installation process, click Yes.

Note
If you click No, you are asked to confirm your decision. If you proceed, the installation process terminates.
The Setup Status window appears (see Figure 13).
Figure 13 Setup Status Window
The upgrade process begins, and you are notified as each software component is installed.
Step 14
When a message appears indicating that your computer needs to be rebooted, click OK and allow your computer to restart. The client adapter's software has been upgraded.
Finding Version Numbers
Follow the instructions in this section to find the version numbers of your client adapter's software components.
Finding the Driver Version
To find the driver version that is currently installed for your client adapter, open ADU, click the Diagnostics tab, and click Adapter Information. The Driver Version field on the Adapter Information window shows the current driver version.
Finding the ADU Version
To find the version of ADU that is currently installed for your client adapter, open ADU and choose the About Aironet Desktop Utility option from the Help drop-down menu. The About window shows the current ADU version.
Caveats
This section describes open, resolved, and other caveats for the software components in this release.
Open Caveats
Open Install Wizard Caveats
The following caveat is not resolved in CB21AG and PI21AG client adapter Install Wizard 2.0.
•
CSCeh25691—Error may occur during upgrade of client adapter software
The following message may appear when you upgrade from an earlier version of the Install Wizard: "The installer has detected that this is a major upgrade. To assure that there are no incompatibilities, the previous install needs to be deleted. Do you wish to continue?" If you click Yes, you are asked if you want to completely remove the selected application and all of its features. If you click Cancel and then choose to update the previous installation, the following error messages appear: "Feature transfer error" and "Unknown error." To work around this problem, uninstall the client adapter software and then reinstall it.
Open Driver Caveats
The following caveats are not resolved in CB21AG and PI21AG client adapter driver 2.0.
•
CSCed40520—Up to 5-minute delay for initial boot
Some computers may experience up to a 5-minute delay during the first boot after installation. Subsequent boots are normal.
•
CSCee89506—Driver fails to install when using install disk on Windows 2000
When you create a driver installation disk (on a floppy or by storing the files in a folder) using the Install Wizard on a computer running Windows 2000, the driver may fail to install. Specifically, when you install the driver via Windows Device Manager > Driver > Properties > Driver Update Driver, Windows indicates that it has finished installing the driver software. However, the Windows Network and Dial-up Connections window shows the following message: "An unexpected error occurred." Also, after you reboot the computer, the Windows Device Manager shows an incomplete installation of the driver software.
•
CSCef74909—IPX auto frame detection may not work correctly
When using Novell IPX client software, the client adapter may not allow proper detection of the IPX frame type. As a result, the Novell IPX stack is unable to log into the Novell server. The IPX stack RIP requester stops trying after 2.5 seconds, which is the default value. To work around this problem, you can change the timeout value in the registry at the following location: \HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NwlnkIpx\Parameters
The parameter is a REG_DWORD named RipCount. Increase the value to 20 seconds by entering hex 28 (40 decimal). The units are in half seconds.
•
CSCeh03426—Client experiences throughput values below 1 Mbps
When 6 or 9 Mbps is enabled on the access point, the client adapter experiences throughput values below 1 Mbps. To work around this problem, set the access point to its default data rate.
•
CSCeh45986—CB21AG in ACER Travelmate 529TX fails DHCP and LEAP
When the CB21AG client adapter is installed in an ACER Travelmate 529TX running Windows 2000 with Service Pack 4 and configured for static WEP with open authentication, it fails to obtain an IP address through DHCP. In addition, the client adapter also fails to LEAP authenticate.
Open ADU Caveats
The following caveats are not resolved in ADU 2.0.
•
CSCeh19611—Incorrect EAP-FAST authentication failure error message
ADU may show the incorrect error message when EAP-FAST authentication fails. This occurs when the access point returns an incorrect error code rather than timing out.
•
CSCeh59373—ADU unmanageable after first install
If ADU is unusable after you install the client adapter software, uninstall the client adapter software and then reinstall it.
•
CSCeh66276—ADU does not prompt for PIN during PEAP (EAP-GTC) reauthentication
During PEAP (EAP-GTC) reauthentication, ADU does not prompt you to enter a PIN. When the client roams out of the coverage area and then returns or its radio is disabled and then reenabled, you are not prompted to re-enter your credentials. The client reconnects to the network and starts to transfer data.
•
CSCeh66882—User is prompted for EAP-FAST PAC when it should be present
The following message may appear even if you have already specified a PAC to use with EAP-FAST: "The current EAP-FAST profile does not have a PAC or the configured PAC does not match the authentication server. Do you want to use another PAC found on your local system that matches the authentication server without reconfiguring the current EAP-FAST profile?"
ADU matches the username and server name that it is trying to use with those in the PAC. If they do not match or the configured PAC does not exist, ADU searches the private and global stores. If a matching PAC is found, the user is prompted with the above message before the PAC is used. Click Yes to attempt to authenticate using another PAC on your system without having to reconfigure your profile.
•
CSCeh69073 and CSCeh72204—Auto-provisioned PAC does not support unicode usernames
An auto-provisioned PAC is not stored in a user's private store if he or she logs into Windows with a username containing two-byte characters. Automatic PAC provisioning succeeds, but the PAC does not appear in the Select EAP-FAST PAC window of the private store and therefore cannot be deleted. To work around this problem, go to the global store on your computer (C:\Document and Settings\All Users\Application Data\Cisco\cscostore). You can see the PAC here and delete it if desired.
•
CSCeh74184—Client fails to associate when configured for WPA/WPA2 passphrase and multiple SSIDs
The client adapter fails to connect to the network when using a profile that is configured for WPA/WPA2 passphrase and more than one SSID. To work around this problem, create separate profiles for the desired SSIDs.
Resolved Caveats
Resolved Install Wizard Caveats
The following caveat is resolved in CB21AG and PI21AG client adapter Install Wizard 2.0.
•
CSCed72084—Text in Install Wizard cut off on Japanese Windows
The text on the Install Wizard - Select Program Folder window is cut off on computers running Japanese Windows 2000 or XP. This issue is resolved in Install Wizard 2.0.
Resolved Driver Caveats
The following caveats are resolved in CB21AG and PI21AG client adapter driver 2.0.
•
CSCed33703—Wireless mode shows incorrect value when client roams to .11g AP
When the client roams to an access point with an 802.11g radio, ADU shows the wireless mode as 2.4 GHz 11 Mbps rather than 2.4 GHz 54 Mbps. This issue is resolved in driver 2.0.
•
CSCef40331—Client fails to reconnect to access point after recovering from standby mode
On Windows XP systems, if the client adapter is ejected during standby or hibernate mode and is not reinserted before the system resumes, the client fails to reauthenticate to the access point upon the system resume. This problem occurs only for client adapters using EAP authentication. This issue is resolved in driver 2.0.
•
CSCeg81842—Client unable to get IP address
The client sometimes fails to get an IP address when using power save mode. This issue is resolved in driver 2.0.
•
CSCin73086—"show dot11 adjacent-ap" does not show information about previous AP
The "show dot11 adjacent-ap" frame does not display any information about the access point to which the client adapter was previously associated. This issue is resolved in driver 2.0.
•
CSCin74956 and CSCee69323—Client fails to get IP address when CCKM CKIP+CMIC is used with 12.2(15)JA
Clients fail to obtain an IP address when attempting to associate to an access point that is running Cisco IOS Release 12.2(15)JA and is configured for CCKM with CKIP+CMIC. To work around this problem, configure the access point for CCKM with TKIP+Michael MIC rather than CKIP+CMIC or upgrade your access points to Cisco IOS Release 12.2(15)XR or greater. This issue is resolved in driver 2.0.
Resolved ADU Caveats
The following caveats are resolved in ADU 2.0
•
CSCed72076—Channels 13 and 14 not available in ad hoc mode for Japanese cards
The Japan regulatory domain supports channels 1 through 14 for IEEE 802.11b communications and channels 1 through 13 for IEEE 802.11g communications. However, channels 13 and 14 do not appear in the Channels drop-down list on the ADU Profile Management (Advanced) window for client adapters that are configured for use in Japan. This issue is resolved in ADU 2.0.
•
CSCee06008—ADU-activated PEAP (EAP-MSCHAP V2) machine authentication fails domain logon
Machine authentication does not work when you activate an ADU profile that has PEAP (EAP-MSCHAP V2) enabled. Users without cached credentials cannot log into the Windows domain. You can resolve this problem by performing one of the following:
–
Selecting the Host Based EAP 802.1x EAP Type option in ADU and then configuring PEAP settings in the Microsoft Wireless Configuration Manager

Note
Refer to the "Host Based EAP Option Added to ADU" section for details.
–
Configuring your client adapter for Protected EAP (PEAP) authentication in the Microsoft Wireless Configuration Manager in Windows XP rather than in ADU
•
CSCee22943—Signal strength displayed incorrectly
The Signal Strength values on the Available Infrastructure and Ad Hoc Networks window in ADU are not signal strength values but signal-to-noise ratio (SNR) values. In ADU 2.0, the Signal Strength heading has been appropriately renamed Signal-to-Noise Ratio (SNR).
•
CSCef85128—Windows login fails and registry change occurs
Upon reboot, a computer running Windows 2000 fails the Windows login when the user tries to log into a domain. In addition, part of the registry is changed. This issue is resolved in ADU 2.0.
•
CSCeg74346—PEAP (EAP-MSCHAPV2) authentication fails with self-signed certificates
PEAP (EAP-MSCHAP V2) authentication fails when ACS 3.3.2.2 is used with self-signed certificates. This issue is resolved in ADU 2.0.
•
CSCeh00792—Saved LEAP username and password not used when Novell client installed
When Windows XP Service Pack 1 or Service Pack 2 is installed followed by ADU and Novell Client 4.90 Service Pack 2 (4.90.2.20040617) and ADU is configured for LEAP and WPA with a saved username and password, you are prompted to enter your username and password upon reboot. Although ADU has your saved username and password, it does not use them. This issue is resolved in ADU 2.0.
•
CSCeh31338—Client fails domain login when Windows Auto Admin Logon enabled
The client is unable to log into a domain when Windows Auto Admin Logon is enabled. This issue is resolved in ADU 2.0.
•
CSCin57337—SSID not shown in ASTU Tool Tip window
When the client adapter is not associated to an access point, the Tool Tip window in ASTU does not show an SSID. In ADU 2.0, when the client adapter is not associated and auto profile selection is disabled, the Tool Tip window now shows the profile's SSID. However, when the client adapter is not associated and auto profile selection is enabled, the SSID still does not appear.
•
CSCin75469—LEAP Authentication Status window always in foreground
The LEAP Authentication Status window always appears in the foreground, even after another application is selected. This issue is resolved in ADU 2.0.
Other Caveats
The following caveats, which are listed as open caveats in the Release Notes for Install Wizard 1.2, have been closed and are not resolved in Install Wizard 2.0.
•
CSCec08294—Client remains in access point's association table
The client remains in the access point's association table for approximately 30 minutes after it has been disabled.
•
CSCec39604—EAP-TLS authentication attempts fail for users with zero-length passwords
EAP-TLS authentication attempts fail for users with zero-length passwords. To work around this problem, set up a Windows password that contains at least one character.
•
CSCed23644—DHCP does not operate if MIC is enabled on VxWorks access points
DHCP does not operate with CB21AG and PI21AG client adapters if MIC is enabled on VxWorks access points. To work around this problem, upgrade the VxWorks access points to firmware version 12.04 or later.
•
CSCee14610—PEAP authentication attempts fail for users with zero-length passwords
PEAP authentication attempts fail for users with zero-length passwords. To work around this problem, set up a Windows password that contains at least one character.
•
CSCef54644—Problem getting IP address on 802.11a radio after rebooting switch
When the client adapter is set to operate in 5-GHz, 54-Mbps wireless mode, the client may fail to get an IP address via DHCP after the upper switch reboots. To work around this problem, shut down both the client adapter and the access point to which it is associated and reauthenticate.
•
CSCeg69646—Group Policy does not work with LEAP
Group Policy does not function correctly on computers that are configured for LEAP. To work around this problem, use saved LEAP credentials and increase the value of the Group Policy Delay parameter on the Profile Management (Security) window in ADU.

Note
Group Policy also does not function correctly on computers that are configured for open authentication. Group Policy operates the first time for a new user but does not work for the same user upon reboot. Increasing the value of the Group Policy Delay parameter has no effect.
•
CSCin58718—ADU shows invalid IP address for VxWorks access points
The ADU Advanced Status window shows an Associated AP IP Address of 0.0.0.0 when the client adapter is associated to a VxWorks access point. To work around this problem, upgrade the VxWorks access point to firmware version 12.04 or later.
Getting Bug Information on Cisco.com
If you are a Cisco registered user, you can use the Cisco TAC Software Bug Toolkit, which consists of three tools (Bug Navigator, Bug Watcher, and Search by Bug ID Number) that help you to identify existing bugs (or caveats) in Cisco software products.
Access the TAC Software Bug Toolkit at the following URL:
http://www.cisco.com/cgi-bin/Support/Bugtool/launch_bugtool.pl
Troubleshooting
For the most up-to-date, detailed troubleshooting information, refer to the Cisco TAC website at
http://www.cisco.com/en/US/support/index.html
Click Product Support > Wireless. Then choose your product and Troubleshooting to find information on the problem you are experiencing.
Related Documentation
For more information about Cisco Aironet CB21AG and PI21AG client adapters, refer to the following document:
•
Cisco Aironet 802.11a/b/g Wireless LAN Client Adapters (CB21AG and PI21AG) Installation and Configuration Guide, OL-4211-03
http://www.cisco.com/univercd/cc/td/doc/product/wireless/cb21ag/index.htm
Obtaining Documentation
Cisco documentation and additional literature are available on Cisco.com. Cisco also provides several ways to obtain technical assistance and other technical resources. These sections explain how to obtain technical information from Cisco Systems.
Cisco.com
You can access the most current Cisco documentation at this URL:
http://www.cisco.com/univercd/home/home.htm
You can access the Cisco website at this URL:
You can access international Cisco websites at this URL:
http://www.cisco.com/public/countries_languages.shtml
Documentation DVD
Cisco documentation and additional literature are available in a Documentation DVD package, which may have shipped with your product. The Documentation DVD is updated regularly and may be more current than printed documentation. The Documentation DVD package is available as a single unit.
Registered Cisco.com users (Cisco direct customers) can order a Cisco Documentation DVD (product number DOC-DOCDVD=) from the Ordering tool or Cisco Marketplace.
Cisco Ordering tool:
http://www.cisco.com/en/US/partner/ordering/
Cisco Marketplace:
http://www.cisco.com/go/marketplace/
Ordering Documentation
You can find instructions for ordering documentation at this URL:
http://www.cisco.com/univercd/cc/td/doc/es_inpck/pdi.htm
You can order Cisco documentation in these ways:
•
Registered Cisco.com users (Cisco direct customers) can order Cisco product documentation from the Ordering tool:
http://www.cisco.com/en/US/partner/ordering/
•
Nonregistered Cisco.com users can order documentation through a local account representative by calling Cisco Systems Corporate Headquarters (California, USA) at 408 526-7208 or, elsewhere in North America, by calling 1 800 553-NETS (6387).
Documentation Feedback
You can send comments about technical documentation to bug-doc@cisco.com.
You can submit comments by using the response card (if present) behind the front cover of your document or by writing to the following address:
Cisco Systems
Attn: Customer Document Ordering
170 West Tasman Drive
San Jose, CA 95134-9883We appreciate your comments.
Cisco Product Security Overview
Cisco provides a free online Security Vulnerability Policy portal at this URL:
http://www.cisco.com/en/US/products/products_security_vulnerability_policy.html
From this site, you can perform these tasks:
•
Report security vulnerabilities in Cisco products.
•
Obtain assistance with security incidents that involve Cisco products.
•
Register to receive security information from Cisco.
A current list of security advisories and notices for Cisco products is available at this URL:
If you prefer to see advisories and notices as they are updated in real time, you can access a Product Security Incident Response Team Really Simple Syndication (PSIRT RSS) feed from this URL:
http://www.cisco.com/en/US/products/products_psirt_rss_feed.html
Reporting Security Problems in Cisco Products
Cisco is committed to delivering secure products. We test our products internally before we release them, and we strive to correct all vulnerabilities quickly. If you think that you might have identified a vulnerability in a Cisco product, contact PSIRT:
•
Emergencies — security-alert@cisco.com
•
Nonemergencies — psirt@cisco.com

Tip
We encourage you to use Pretty Good Privacy (PGP) or a compatible product to encrypt any sensitive information that you send to Cisco. PSIRT can work from encrypted information that is compatible with PGP versions 2.x through 8.x.
Never use a revoked or an expired encryption key. The correct public key to use in your correspondence with PSIRT is the one that has the most recent creation date in this public key server list:
http://pgp.mit.edu:11371/pks/lookup?search=psirt%40cisco.com&op=index&exact=on
In an emergency, you can also reach PSIRT by telephone:
•
1 877 228-7302
•
1 408 525-6532
Obtaining Technical Assistance
For all customers, partners, resellers, and distributors who hold valid Cisco service contracts, Cisco Technical Support provides 24-hour-a-day, award-winning technical assistance. The Cisco Technical Support Website on Cisco.com features extensive online support resources. In addition, Cisco Technical Assistance Center (TAC) engineers provide telephone support. If you do not hold a valid Cisco service contract, contact your reseller.
Cisco Technical Support Website
The Cisco Technical Support Website provides online documents and tools for troubleshooting and resolving technical issues with Cisco products and technologies. The website is available 24 hours a day, 365 days a year, at this URL:
http://www.cisco.com/techsupport
Access to all tools on the Cisco Technical Support Website requires a Cisco.com user ID and password. If you have a valid service contract but do not have a user ID or password, you can register at this URL:
http://tools.cisco.com/RPF/register/register.do

Note
Use the Cisco Product Identification (CPI) tool to locate your product serial number before submitting a web or phone request for service. You can access the CPI tool from the Cisco Technical Support Website by clicking the Tools & Resources link under Documentation & Tools. Choose Cisco Product Identification Tool from the Alphabetical Index drop-down list, or click the Cisco Product Identification Tool link under Alerts & RMAs. The CPI tool offers three search options: by product ID or model name; by tree view; or for certain products, by copying and pasting show command output. Search results show an illustration of your product with the serial number label location highlighted. Locate the serial number label on your product and record the information before placing a service call.
Submitting a Service Request
Using the online TAC Service Request Tool is the fastest way to open S3 and S4 service requests. (S3 and S4 service requests are those in which your network is minimally impaired or for which you require product information.) After you describe your situation, the TAC Service Request Tool provides recommended solutions. If your issue is not resolved using the recommended resources, your service request is assigned to a Cisco TAC engineer. The TAC Service Request Tool is located at this URL:
http://www.cisco.com/techsupport/servicerequest
For S1 or S2 service requests or if you do not have Internet access, contact the Cisco TAC by telephone. (S1 or S2 service requests are those in which your production network is down or severely degraded.) Cisco TAC engineers are assigned immediately to S1 and S2 service requests to help keep your business operations running smoothly.
To open a service request by telephone, use one of the following numbers:
Asia-Pacific: +61 2 8446 7411 (Australia: 1 800 805 227)
EMEA: +32 2 704 55 55
USA: 1 800 553-2447For a complete list of Cisco TAC contacts, go to this URL:
http://www.cisco.com/techsupport/contacts
Definitions of Service Request Severity
To ensure that all service requests are reported in a standard format, Cisco has established severity definitions.
Severity 1 (S1)—Your network is "down," or there is a critical impact to your business operations. You and Cisco will commit all necessary resources around the clock to resolve the situation.
Severity 2 (S2)—Operation of an existing network is severely degraded, or significant aspects of your business operation are negatively affected by inadequate performance of Cisco products. You and Cisco will commit full-time resources during normal business hours to resolve the situation.
Severity 3 (S3)—Operational performance of your network is impaired, but most business operations remain functional. You and Cisco will commit resources during normal business hours to restore service to satisfactory levels.
Severity 4 (S4)—You require information or assistance with Cisco product capabilities, installation, or configuration. There is little or no effect on your business operations.
Obtaining Additional Publications and Information
Information about Cisco products, technologies, and network solutions is available from various online and printed sources.
•
Cisco Marketplace provides a variety of Cisco books, reference guides, and logo merchandise. Visit Cisco Marketplace, the company store, at this URL:
http://www.cisco.com/go/marketplace/
•
Cisco Press publishes a wide range of general networking, training and certification titles. Both new and experienced users will benefit from these publications. For current Cisco Press titles and other information, go to Cisco Press at this URL:
•
Packet magazine is the Cisco Systems technical user magazine for maximizing Internet and networking investments. Each quarter, Packet delivers coverage of the latest industry trends, technology breakthroughs, and Cisco products and solutions, as well as network deployment and troubleshooting tips, configuration examples, customer case studies, certification and training information, and links to scores of in-depth online resources. You can access Packet magazine at this URL:
•
iQ Magazine is the quarterly publication from Cisco Systems designed to help growing companies learn how they can use technology to increase revenue, streamline their business, and expand services. The publication identifies the challenges facing these companies and the technologies to help solve them, using real-world case studies and business strategies to help readers make sound technology investment decisions. You can access iQ Magazine at this URL:
http://www.cisco.com/go/iqmagazine
•
Internet Protocol Journal is a quarterly journal published by Cisco Systems for engineering professionals involved in designing, developing, and operating public and private internets and intranets. You can access the Internet Protocol Journal at this URL:
•
World-class networking training is available from Cisco. You can view current offerings at this URL:
http://www.cisco.com/en/US/learning/index.html
This document is to be used in conjunction with the documents listed in the "Related Documentation" section.
CCSP, CCVP, the Cisco Square Bridge logo, Follow Me Browsing, and StackWise are trademarks of Cisco Systems, Inc.; Changing the Way We Work, Live, Play, and Learn, and iQuick Study are service marks of Cisco Systems, Inc.; and Access Registrar, Aironet, ASIST, BPX, Catalyst, CCDA, CCDP, CCIE, CCIP, CCNA, CCNP, Cisco, the Cisco Certified Internetwork Expert logo, Cisco IOS, Cisco Press, Cisco Systems, Cisco Systems Capital, the Cisco Systems logo, Cisco Unity, Empowering the Internet Generation, Enterprise/Solver, EtherChannel, EtherFast, EtherSwitch, Fast Step, FormShare, GigaDrive, GigaStack, HomeLink, Internet Quotient, IOS, IP/TV, iQ Expertise, the iQ logo, iQ Net Readiness Scorecard, LightStream, Linksys, MeetingPlace, MGX, the Networkers logo, Networking Academy, Network Registrar, Packet, PIX, Post-Routing, Pre-Routing, ProConnect, RateMUX, ScriptShare, SlideCast, SMARTnet, StrataView Plus, TeleRouter, The Fastest Way to Increase Your Internet Quotient, and TransPath are registered trademarks of Cisco Systems, Inc. and/or its affiliates in the United States and certain other countries.
All other trademarks mentioned in this document or Website are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (0502R)
Copyright © 2005 Cisco Systems, Inc.
All rights reserved.
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback