Cisco Wireless Controller Configuration Guide, Release 8.3
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 28, 2016
Chapter: Configuring OfficeExtend Access Points
- Information About OfficeExtend Access Points
- OEAP 600 Series Access Points
- OEAP in Local Mode
- Supported WLAN Settings for 600 Series OfficeExtend Access Point
- WLAN Security Settings for the 600 Series OfficeExtend Access Point
- Authentication Settings
- Supported User Count on 600 Series OfficeExtend Access Point
- Remote LAN Settings
- Channel Management and Settings
- Firewall Settings
- Additional Caveats
- Implementing Security
- Licensing for an OfficeExtend Access Point
- Configuring OfficeExtend Access Points
Configuring OfficeExtend Access Points
Information About OfficeExtend Access Points
A Cisco OfficeExtend access point (Cisco OEAP) provides secure communications from a Cisco WLC to a Cisco AP at a remote location, seamlessly extending the corporate WLAN over the Internet to an employee’s residence. The user’s experience at the home office is exactly the same as it would be at the corporate office. Datagram Transport Layer Security (DTLS) encryption between the access point and the controller ensures that all communications have the highest level of security.
 Note | DTLS is permanently enabled on the Cisco OEAP. You cannot disable DTLS on this access point. |
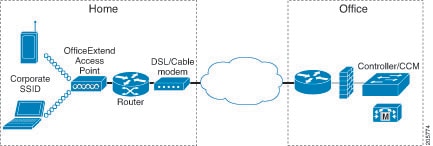
The following figure shows a typical OfficeExtend access point setup.
All the supported indoor AP models with integrated antenna can be configured as OEAP except the AP-700I, AP-700W, and AP802 series access points.
 Note | See the Release Notes for information about supported Cisco OEAPs. |
OEAP 600 Series Access Points
This section details the requirements for configuring a Cisco wireless LAN controller for use with the Cisco 600 Series OfficeExtend Access Point. The 600 Series OfficeExtend Access Point supports split mode operation, and it requires configuration through the WLAN controller in local mode. This section describes the configurations necessary for proper connection and supported feature sets.
 Note | IPv6 is not supported on Cisco 600 Series OfficeExtend Access Points. |
 Note | The CAPWAP UDP 5246 and 5247 ports must be open on the firewall between the WLAN controller and the 600 Series OfficeExtend Access Point. |
 Note | Multicast is not supported on Cisco 600 Series OfficeExtend Access Points. |
OEAP in Local Mode
The Cisco OEAP connects to the Cisco WLC in local mode. You cannot alter these settings.
 Note | Monitor mode, FlexConnect mode, Sniffer mode, Rogue Detector, Bridge, and SE-Connect are not supported on the Cisco OEAP and are not configurable. 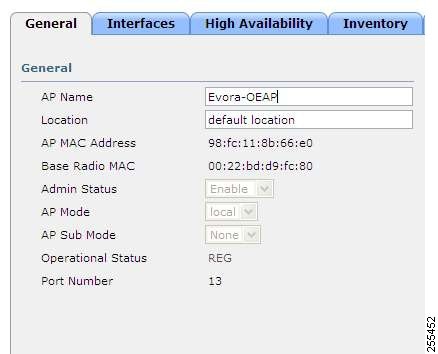 |
Supported WLAN Settings for 600 Series OfficeExtend Access Point
The 600 Series OfficeExtend Access Point supports a maximum of three WLANs and one remote LAN. If your network deployment has more than three WLANs, you must place the 600 Series OfficeExtend Access Point in an AP group. If the 600 Series OfficeExtend Access Points are added to an AP group, the same limit of three WLANs and one remote LAN still applies for the configuration of the AP group.
If the 600 Series OfficeExtend Access Point is in the default group, which means that it is not in a defined AP group, the WLAN/remote LAN IDs must be set lower than ID 8.
If additional WLANs or remote LANs are created with the intent of changing the WLANs or remote LAN being used by the 600 Series OfficeExtend Access Point, you must disable the current WLANs or remote LAN that you are removing before enabling the new WLANs or remote LAN on the 600 Series OfficeExtend Access Point. If there are more than one remote LANs enabled for an AP group, disable all remote LANs and then enable only one of them.
If more than three WLANs are enabled for an AP group, disable all WLANs and then enable only three of them.
WLAN Security Settings for the 600 Series OfficeExtend Access Point
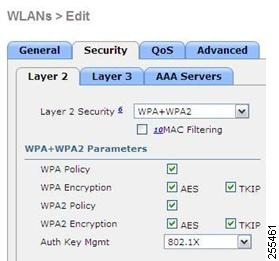
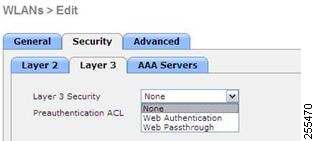
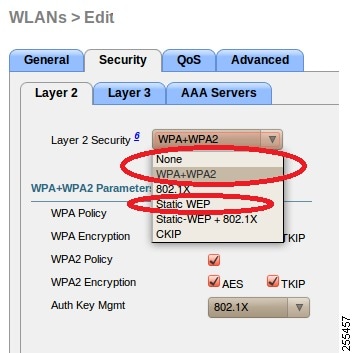
When configuring the security settings in the WLAN (see the following figure), note that there are specific elements that are not supported on the 600 Series OfficeExtend Access Point. CCX is not supported on the 600 Series OfficeExtend Access Point, and elements related to CCX are not supported.
For Layer 2 Security, the following options are supported for the 600 Series OfficeExtend Access Point:
In the Security tab (see the following figure), do not select CCKM in WPA+WPA2 settings. Select only 802.1X or PSK.
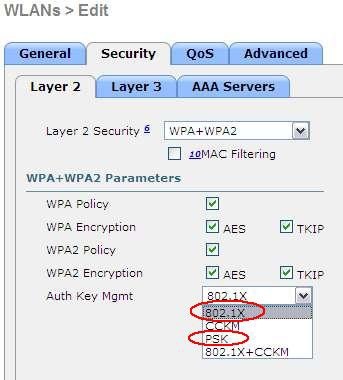
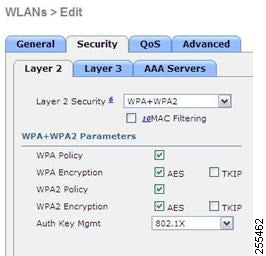
Security encryption settings must be identical for WPA and WPA2 for TKIP and AES. The following are examples of incompatible settings for TKIP and AES.
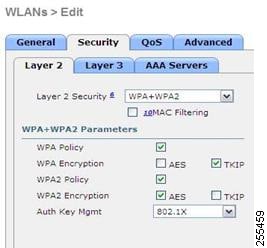
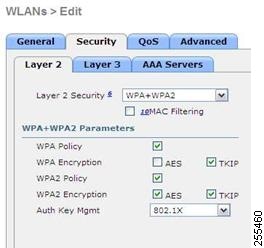
The following are examples of compatible settings:
QoS settings are supported (see the following figure), but CAC is not supported and should not be enabled.
 Note | Do not enable Coverage Hole Detection. |
 Note | Aironet IE should not be enabled. This option is not supported. 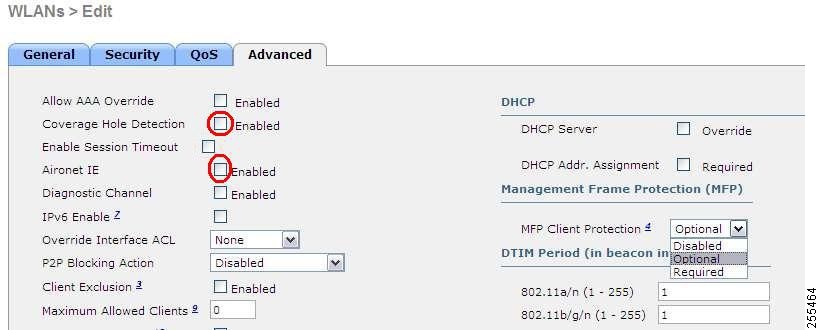 |
MFP is also not supported and should be disabled or set to optional.
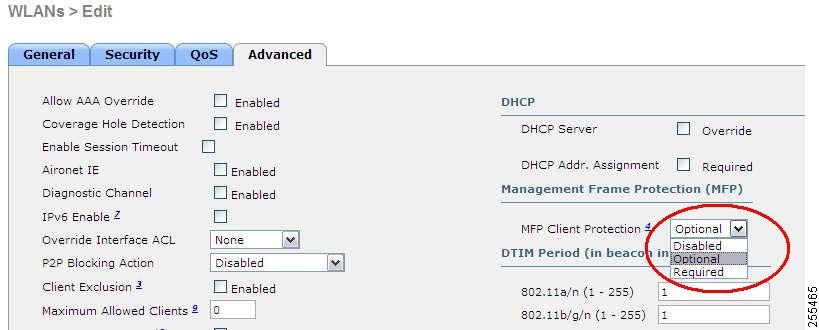
Client Load Balancing and Client Band Select are not supported.
Authentication Settings
For authentication on the 600 Series OfficeExtend Access Point, LEAP is not supported. This configuration must be addressed on the clients and RADIUS servers to migrate them to EAP-Fast, EAP-TTLS, EAP-TLS, or PEAP.
If Local EAP is being utilized on the controller, the settings would also have to be modified not to use LEAP.
Supported User Count on 600 Series OfficeExtend Access Point
Only 15 users are allowed to connect on the WLANs provided on the Cisco 600 Series OEAP at any one time, a sixteenth user cannot authenticate until one of the first clients is deauthenticated or timeout on the controller occurs. This number is cumulative across the controller WLANs on the 600 Series OfficeExtend Access Point.
For example, if two controller WLANs are configured and there are 15 users on one of the WLANs, no other users can join the other WLAN on the 600 Series OfficeExtend Access Point at that time.
This limit does not apply to the local private WLANs that the end user configures on the 600 Series OfficeExtend Access Point for personal use. Clients connected on these private WLANs or on the wired ports do not affect these limits.
 Note | This limit does not apply to other AP models that operate in the OfficeExtend mode. |
Remote LAN Settings
Only four clients can connect through a remote LAN port on the 600 Series OfficeExtend Access Point. This number does not affect the fifteen user limit imposed for the Controller WLANs. The remote LAN client limit supports connecting a switch or hub to the remote LAN port for multiple devices or connecting directly to a Cisco IP phone that is connected to that port. Only the first four devices can connect until one of the devices is idle for more than one minute.
Remote LAN is configured in the same way that a WLAN or Guest LAN is configured on the controller:
Security settings can be left open, set for MAC filtering, or set for Web Authentication. The default is to use MAC filtering. Additionally, you can specify 802.1X Layer 2 security settings.

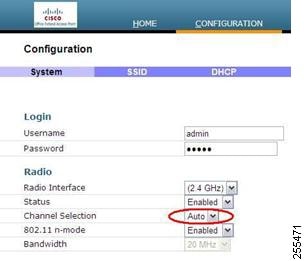
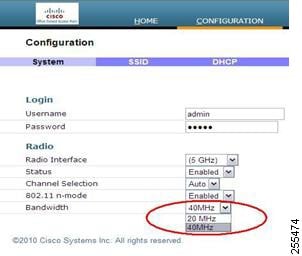
Channel Management and Settings
The radios for the 600 Series OfficeExtend Access Point are controlled through the Local GUI on the access point and not through the Wireless LAN Controller. The Tx power and channel settings can be set manually through the controller interface. RRM is not supported on the 600 Series OfficeExtend Access Point.
The 600 series scans and chooses channels for 2.4-GHz and 5-GHz during startup as long as the default settings on the local GUI are left as default in both spectrums.
The channel bandwidth for 5.0 GHz is also configured on the 600 Series OfficeExtend Access Point Local GUI, for 20-MHz or 40-MHz wide channels. Setting the channel width to 40 MHz for 2.4 GHz is not supported and fixed at 20 MHz.
Firewall Settings
Firewall can be enabled on Cisco 600 Series OfficeExtend Access Point and filtering and forwarding rules can be applied. These ten pre-configured applications can be enabled or disabled:
These applications can be unblocked by providing the protocol (TCP/UDP), LAN client IP range and destination port range.
 Note | The firewall is applicable only to the personal traffic on the OEAP 600 APs The data traffic between the controller and OEAP 600 APs is addressed by a firewall in the corporate network. |
600 Series OfficeExtend Access Point supports a maximum of ten port forwarding rules. Every rule takes protocol (TCP/UDP), WAN port range, Local LAN client IP (where traffic will be forwarded), LAN port range, and enable or disable as a parameter.
The DMZ feature allows one network computer connected to local LAN or WLAN to be exposed to the Internet for use of a special-purpose service like Internet gaming. DMZ forwards all the ports terminating on WAN IP at the same time to one PC. The Port Range Forwarding feature opens only the required ports to be opened, while DMZ opens all the ports of one computer, exposing the computer to the Internet or WAN. This will forward all the incoming WAN packets to any port which has the port forwarding rule configured on it. CAPWAP control and data connection ports will not be forwarded to DMZ IP.
Additional Caveats
-
The Cisco 600 Series OfficeExtend Access Points (OEAPs) are designed for single AP deployments, therefore client roaming between Cisco 600 Series OEAPs is not supported.
Disabling the 802.11a/n/ac or 802.11b/g/n on the controller may not disable these spectrums on the Cisco 600 Series OEAP because local SSID may be still working.
-
Your firewall must be configured to allow traffic from access points using CAPWAP. Make sure that UDP ports 5246 and 5247 are enabled and are not blocked by an intermediate device that could prevent an access point from joining the controller.
-
Cisco Aironet APs other than 600 Series OEAPs that are converted to OEAP mode and mapped to locally switched WLAN forward the DHCP request to the local subnet on the AP connected switch. To avoid this condition, you must disable local switching and local authentication.
-
For Cisco 600 Series OEAP to associate with Cisco Virtual Wireless LAN Controller, follow these steps:
- Configure the OEAP to associate with a physical controller that is using 7.5 or a later release and download the corresponding AP image.
- Configure the OEAP so that the OEAP does not associate with the physical controller again; for example, you can implement an ACL in the network to block CAPWAP between the OEAP and the physical controller.
- Configure the OEAP to associate with the Cisco Virtual Wireless LAN Controller.
Implementing Security
 Note | The LSC configuration is optional. The Cisco OEAPs points do not support LSC. |
Use local significant certificates (LSCs) to authorize your OfficeExtend access points, by following the instructions in Authorizing Access Points Using LSCs.
Implement AAA server validation using the access point’s MAC address, name, or both as the username in authorization requests, by entering this command:
config auth-list ap-policy authorize-ap username {ap_mac | Cisco_AP | both}
Using the access point name for validation can ensure that only the OfficeExtend access points of valid employees can associate with the controller. To implement this security policy, ensure that you name each OfficeExtend access point with an employee ID or employee number. When an employee is terminated, run a script to remove this user from the AAA server database, which prevents that employee’s OfficeExtend access point from joining the network.
Save your changes by entering this command:
Licensing for an OfficeExtend Access Point
To use Cisco OEAPs, a base license must be installed and in use on the Cisco WLC. After the license is installed, you can enable the OfficeExtend mode on the supported Cisco Aironet AP models that support OfficeExtend mode.
Configuring OfficeExtend Access Points
After Cisco Aironet access point has associated with the controller, you can configure it as an OfficeExtend access point.
- Configuring OfficeExtend Access Points (GUI)
- Configuring OfficeExtend Access Points (CLI)
- Configuring Split Tunneling for a WLAN or a Remote LAN
Configuring OfficeExtend Access Points (GUI)
Configuring OfficeExtend Access Points (CLI)
Enable FlexConnect on the access point by entering this command:
Configure one or more controllers for the access point by entering one or all of these commands:
config ap primary-base controller_name Cisco_AP controller_ip_address
config ap secondary-base controller_name Cisco_AP controller_ip_address
config ap tertiary-base controller_name Cisco_AP controller_ip_address

Note
You must enter both the name and IP address of the controller. Otherwise, the access point cannot join this controller.

Note
The names and IP addresses must be unique for the primary, secondary, and tertiary controllers.
Enable the OfficeExtend mode for this access point by entering this command:
config flexconnect office-extend {enable | disable} Cisco_AP
The default value is enabled. The disable parameter disables OfficeExtend mode for this access point. It does not undo all of the configuration settings on the access point. If you want to clear the access point’s configuration and return it to the factory-default settings, enter this command:
If you want to clear only the access point’s personal SSID, enter this command:
config flexconnect office-extend clear-personalssid-config Cisco_AP
Enable the access point to choose the controller with the least latency when joining by entering this command:
config flexconnect join min-latency {enable | disable} Cisco_AP
The default value is disabled. When you enable this feature, the access point calculates the time between the discovery request and discovery response and joins the Cisco WLC that responds first.
Configure a specific username and password that users at home can enter to log into the GUI of the OfficeExtend access point by entering this command:
config ap mgmtuser add username user password password enablesecret enable_password Cisco_AP
The credentials that you enter in this command are retained across controller and access point reboots and if the access point joins a new controller.
To configure access to the local network for the Cisco OfficeExtend access points, enter the following command:
config network oeap local-network {enable | disable}
When disabled, the local SSIDs, local ports are inoperative; and the console is not accessible. When reset, the default restores local access. This configuration does not affect the remote LAN configuration if configured on the access points.
Configure the Dual R-LAN Ports feature, which allows the Ethernet port 3 of Cisco OfficeExtend access points to operate as a remote LAN by entering this command:
config network oeap dual-rlan-ports {enable | disable}
This configuration is global to the controller and is stored by the AP and the NVRAM variable. When this variable is set, the behavior of the remote LAN is changed. This feature supports different remote LANs per remote LAN port.
The remote LAN mapping is different depending on whether the default group or AP Groups is used: -
Default Group—If you are using the default group, a single remote LAN with an even numbered remote LAN ID is mapped to port 4. For example, a remote LAN with remote LAN ID 2 is mapped to port 4. The remote LAN with an odd numbered remote LAN ID is mapped to port 3. For example, a remote LAN with remote LAN ID 1 is mapped to port 3.
-
AP Groups—If you are using an AP group, the mapping to the OEAP ports is determined by the order of the AP groups. To use an AP group, you must first delete all remote LANs and WLANs from the AP group leaving it empty. Then, add the two remote LANs to the AP group adding the port 3 AP remote LAN first, and the port 4 remote group second, followed by any WLANs.
-
Enable or disable split tunneling by entering this command: config network oeap split-tunnel {enable | disable}
Disabling split tunneling here disables split tunneling for all the WLANs and remote LANs. You can also disable split tunneling on a specific WLAN or remote LAN.
Enable split tunneling without gateway override by entering this command: config wlan split-tunnel wlan-id enabled apply-acl acl name
Enable split tunneling with gateway override by entering this command: config wlan split-tunnel wlan-id enabled override gateway gateway ip mask subnet mask apply-acl acl name
Save your changes by entering this command: save config

Note
If your controller supports only OfficeExtend access points, see the Configuring Radio Resource Management section for instructions on setting the recommended value for the DCA interval.
Configuring Split Tunneling for a WLAN or a Remote LAN
Configuring Split Tunneling for a WLAN or a Remote LAN (GUI)
Configuring Split Tunneling for a WLAN or a Remote LAN (CLI)
Enable or disable split tunneling for a WLAN by entering this command: config wlan split-tunnel wlan-id {enable | disable}
See the split tunneling status for a WLAN by entering this command: show wlan wlan-id
Enable or disable split tunneling for a remote LAN by entering this command: config remote-lan split-tunnel rlan-id {enable | disable}
See the split tunneling status for a remote LAN by entering this command: show remote-lan rlan-id

Note
When a remote LAN or wireless client on a corporate SSID communicate among themselves, all the traffic on the corporate SSID and remote LAN is tunneled back to the controller.
Configuring OEAP ACLs
Configuring OEAP ACLs (GUI)
Configuring OEAP ACLs (CLI)
Configuring a Personal SSID on an OfficeExtend Access Point Other than 600 Series OEAP
Viewing OfficeExtend Access Point Statistics
Use these commands to view information about the OfficeExtend access points on your network:
See a list of all OfficeExtend access points by entering this command:
See the link delay for OfficeExtend access points by entering this command:
See the encryption state of all access points or a specific access point by entering this command:
show ap link-encryption {all | Cisco_AP}
This command also shows authentication errors, which track the number of integrity check failures, and replay errors, which track the number of times that the access point receives the same packet. See the data plane status for all access points or a specific access point by entering this command:
Viewing Voice Metrics on OfficeExtend Access Points
Use this command to view information about voice metrics on the OfficeExtend access points in your network:
show ap stats 802.11{a | b} Cisco_APOEAP WMM Stats :
Best Effort:
Tx Frame Count............................... 0
Tx Failed Frame Count........................ 0
Tx Expired Count............................. 0
Tx Overflow Count............................ 0
Tx Queue Count............................... 0
Tx Queue Max Count........................... 0
Rx Frame Count............................... 0
Rx Failed Frame Count........................ 0
Background:
Tx Frame Count............................... 0
Tx Failed Frame Count........................ 0
Tx Expired Count............................. 0
Tx Overflow Count............................ 0
Tx Queue Count............................... 0
Tx Queue Max Count........................... 0
Rx Frame Count............................... 0
Rx Failed Frame Count........................ 0
Video:
Tx Frame Count............................... 0
Tx Failed Frame Count........................ 0
Tx Expired Count............................. 0
Tx Overflow Count............................ 0
Tx Queue Count............................... 0
Tx Queue Max Count........................... 0
Rx Frame Count............................... 0
Rx Failed Frame Count........................ 0
Voice:
Tx Frame Count............................... 0
Tx Failed Frame Count........................ 0
Tx Expired Count............................. 0
Tx Overflow Count............................ 0
Tx Queue Count............................... 0
Tx Queue Max Count........................... 0
Rx Frame Count............................... 0
Rx Failed Frame Count........................ 0
View the voice metrics on the OfficeExtend access points in your network using the WLC GUI as follows:
Running Network Diagnostics
Information About Running Network Diagnostics
Network Diagnostics determines the non-DTLS throughput of the system by running a speed test on demand. Network Diagnostics allows troubleshooting of root causes leading to failures. It also determines the link latency and jitter by running a test on demand or periodically.
Running Network Diagnostics (GUI)
Running Network Diagnostics on the Controller
Running Network Diagnostics (CLI)
To run network diagnostics, enter this command on the Cisco WLC: show ap network-diagnostics Ap_Name
Remote LANs
Information About Remote LANs
This section describes how to configure remote LANs.
Prerequisites
-
You must remove all remote LANs from a controller's configuration before moving to a release that does not support the remote LAN functionality. The remote LAN changes to a WLAN in earlier releases, which could cause an undesirable or unsecured WLAN being broadcast on the wireless network. Remote LAN is only supported in release 7.0.116.0 and later.
-
Remote LAN can be applied on a dedicated LAN port on a Cisco Aironet 600 Series OEAP.
Restrictions
-
Only four clients can connect to a Cisco Aironet 600 Series OEAP through a remote LAN port. This number does not affect the fifteen WLAN limit imposed for the controller WLANs. The remote LAN client limit supports connecting a switch or hub to the remote LAN port for multiple devices or connecting directly to a Cisco IP phone that is connected to that port. Only the first four devices can connect until one of the devices is idle for more than one minute.
-
It is not possible to configure 802.1X on remote LANs through the controller GUI; configuration only through CLI is supported.
Configuring a Remote LAN (GUI)
| Step 1 | Choose WLANs to open the WLANs page. This page lists all of the WLANs and remote LANs currently configured on the controller. For each WLAN, you can see its WLAN/remote LAN ID, profile name, type, SSID, status, and security policies. The total number of WLANs/Remote LANs appears in the upper right-hand corner of the page. If the list of WLANs/Remote LANs spans multiple pages, you can access these pages by clicking the page number links.
| ||
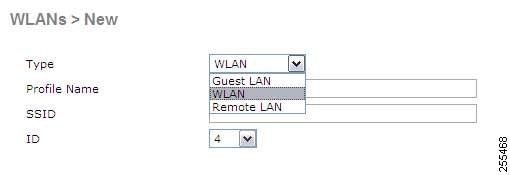
| Step 2 | Create a new Remote-LAN by choosing Create New from the drop-down list and clicking Go. The WLANs > New page appears. | ||
| Step 3 | From the Type drop-down list, choose Remote LAN to create a remote LAN. | ||
| Step 4 | In the Profile Name text box, enter up to 32 alphanumeric characters for the profile name to be assigned to this Remote WLAN. The profile name must be unique. | ||
| Step 5 | From the WLAN ID drop-down list, choose the ID number for this WLAN. | ||
| Step 6 | Click Apply to commit your changes. The WLANs > Edit page appears.
| ||
| Step 7 | Use the parameters on the General, Security, and Advanced tabs to configure this remote LAN. See the sections in the rest of this chapter for instructions on configuring specific features. | ||
| Step 8 | On the General tab, select the Status check box to enable this remote LAN. Be sure to leave it unselected until you have finished making configuration changes to the remote LAN.
| ||
| Step 9 | Click Apply to commit your changes. | ||
| Step 10 | Click Save Configuration to save your changes. |
Configuring a Remote LAN (CLI)
See the current configuration of the remote LAN by entering this command:
Enable or disable 802.1X authentication for remote LAN by entering this command:
config remote-lan security 802.1X {enable | disable} remote-lan-id

NoteThe encryption on a remote LAN is always “none.”
Enable or disable local EAP with the controller as an authentication server, by entering this command:
config remote-lan local-auth enable profile-name remote-lan-id
If you are using an external AAA authentication server, use the following command:
config remote-lan radius_server auth {add | delete} remote-lan-id server id
config remote-lan radius_server auth {add | delete} remote-lan-id
 Feedback
Feedback