- Preface
- Using the Command-Line Interface
- Using the Web Graphical User Interface
- Configuring MLD Snooping
- Configuring IPv6 Unicast Routing
- Configuring IPv6 Client IP Address Learning
- Configuring IPv6 WLAN Security
- Configuring IPv6 ACL
- Configuring IPv6 Web Authentication
- Configuring IPv6 Client Mobility
- Configuring IPv6 Mobility
- Configuring IPv6 NetFlow
- Index
IPv6 Configuration Guide, Cisco IOS XE Release 3SE (Catalyst 3850 Switches)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- October 7, 2013
Chapter: Configuring IPv6 WLAN Security
Configuring IPv6 WLAN Security
Prerequisites for IPv6 WLAN Security
Restrictions for IPv6 WLAN Security
RADIUS Server Support
Radius ACS Support
Information About IPv6 WLAN Security
Information About RADIUS
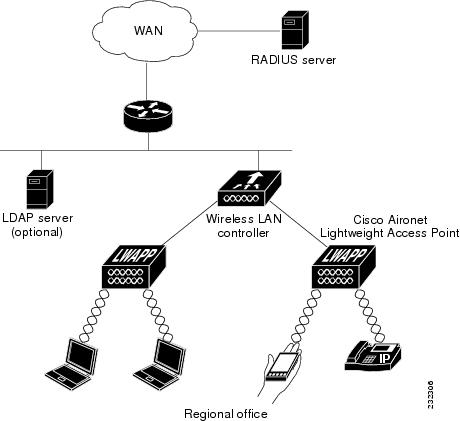
Remote Authentication Dial-In User Service (RADIUS) is a client/server protocol that provides centralized security for users attempting to gain management access to a network. It serves as a back-end database similar to Local EAP and provides authentication and accounting services.
- Authentication—The process of verifying users when they attempt to log into the switch Users must enter a valid username and password for the switch to authenticate users to the RADIUS server. If multiple databases are configured, then specify the sequence in which the backend database must be tried.
- Accounting— The process of recording user actions and changes. Whenever a user successfully executes an action, the RADIUS accounting server logs the changed attributes, the user ID of the person who made the change, the remote host where the user is logged in, the date and time when the command was executed, the authorization level of the user, and a description of the action performed and the values provided. If the RADIUS accounting server is unreachable, the users can continue their sessions uninterrupted.
User Datagram Protocol— RADIUS uses User Datagram Protocol (UDP) for its transport. It maintains a database and listens on UDP port 1812 for incoming authentication requests and UDP port 1813 for incoming accounting requests. The switch, which requires access control, acts as the client and requests AAA services from the server. The traffic between the switch and the server is encrypted by an algorithm defined in the protocol and a shared secret key configured on both devices.
Configures multiple RADIUS accounting and authentication servers. For example, you can have one central RADIUS authentication server but several RADIUS accounting servers in different regions. If you configure multiple servers of the same type and the first one fails or becomes unreachable, the controller automatically tries the second one, then the third one if necessary, and so on.
When RADIUS method is configured for the WLAN, the switch will use the RADIUS method configured for the WLAN. When the WLAN is configured to use local EAP, the RADIUS method configured on the WLAN points to Local. The WLAN must also be configured with the name of the local EAP profile to use.
If no RADIUS method is configured in the WLAN, the switch will use the default RADIUS method defined in global mode.
Information About Local EAP
Local EAP is an authentication method that allows users and wireless clients to be authenticated locally. It is designed for use in remote offices that maintain connectivity to wireless clients when the back-end system is disrupted or the external authentication server goes down. When you enable local EAP, the switch serves as the authentication server and the local user database, which removes dependence on an external authentication server. Local EAP retrieves user credentials from the local user database or the LDAP back-end database to authenticate users. Local EAP supports LEAP, EAP-FAST, EAP-TLS, PEAPv0/MSCHAPv2, and PEAPv1/GTC authentication between the controller and wireless clients.
 Note |
The LDAP back-end database supports these local EAP methods: EAP-TLS, EAP-FAST/GTC, and PEAPv1/GTC. LEAP, EAP-FAST/MSCHAPv2, and PEAPv0. MSCHAPv2 is supported only if the LDAP server is set up to return a clear-text password. |
 Note |
Switch support Local EAP authentication against external LDAP databases such as Microsoft Active Directory and Novell’s eDirectory. For more information about configuring the controller for Local EAP authentication against Novell’s eDirectory, see the Configure Unified Wireless Network for Authentication Against Novell's eDirectory Database whitepaper. |
How to Configure IPv6 WLAN Security
Configuring Local Authentication
Creating a Local User
1. configure terminal
2. username aaa_test
3. password 0 aaa_test
4. end
DETAILED STEPS
Switch# configure terminal Switch(config)# username aaa_test password 0 aaa_test Switch(config)# end
Creating an Client VLAN and Interface
1. configure terminal
2. vlan
3. exit
4. interface vlan vlan_ID
5. ip address
6. ipv6 address
7. end
DETAILED STEPS
Switch# configure terminal Switch(config)# vlan 137 Switch(config-vlan)#exit Switch(config)#interface vlan 137 Switch(config-if)#ip address 10.7.137.10 255.255.255.0 Switch(config-if)#ipv6 address 2001:db8::20:1/64 Switch(config-if)#end
Configuring a EAP Profile
1. eap profile name
2. method leap
3. method tls
4. method peap
5. method mschapv2
6. method md5
7. method gtc
8. method fast profile my-fast
9. description my_localeap profile
10. exit
11. eap method fast profilemyFast
12. authority-id [identity|information]
13. local-key 0 key-name
14. pac-password 0 password
15. end
DETAILED STEPS
Switch(config)#eap profile wcm_eap_prof Switch(config-eap-profile)#method leap Switch(config-eap-profile)#method tls Switch(config-eap-profile)#method peap Switch(config-eap-profile)#method mschapv2 Switch(config-eap-profile)#method md5 Switch(config-eap-profile)#method gtc Switch(config-eap-profile)#eap method fast profile my-fast Switch (config-eap-profile)#description my_local eap profile Switch(config-eap-profile)# exit Switch (config)# eap method fast profile myFast Switch(config-eap-method-profile)#authority-id identity my_identity Switch(config-eap-method-profile)#authority-id information my_information Switch(config-eap-method-profile)#local-key 0 test Switch(config-eap-method-profile)#pac-password 0 test Switch(config-eap-method-profile)# end
Creating a Local Authentication Model
1. aaa new-model
2. authentication dot1x default local
3. dot1x method_list local
4. aaa authentication dot1x dot1x_name local
5. aaa authorization credential-download name local
6. aaa local authentication auth-name authorization authorization-name
7. session ID
8. dot1x system-auth-control
DETAILED STEPS
Switch(config)# aaa new-model Switch(config)# aaa authentication dot1x default local Switch(config)# aaa authentication dot1x wcm-local local Switch(config)# aaa authentication dot1x aaa_auth local Switch(config)# aaa authorization credential-download wcm_author local Switch(config)# aaa local authentication wcm_local authorization wcm_author Switch(config)# aaa session-id common Switch(config)# dot1x system-auth-control
Creating a Client WLAN
 Note |
This example uses 802.1x with dynamic WEP. You can use any other security mechanism supported by the wireless client and configurable on the switch |
1. configure terminal
2. wlan wlan name <identifier> SSID
3. broadcast-ssid
4. no security wpa
5. security dot1x
6. security dot1x authentication-list wcm-local
7. local-auth wcm_eap_prof
8. client vlan 137
9. no shutdown
10. end
DETAILED STEPS
Switch# config terminal Switch(config)#wlan wlanProfileName 1 ngwcSSID Switch(config-wlan)#broadcast-ssid Switch(config-wlan)#no security wpa Switch(config-wlan)#security dot1x Switch(config-wlan)#security dot1x authentication-list wcm-local Switch (config-wlan)# local-auth wcm_eap_prof Switch(config-wlan)#client vlan 137 Switch(config-wlan)#no shutdown Switch(config-wlan)#end Switch#
Configuring Local Authentication with WPA2+AES
1. configure terminal
2. aaa new model
3. dot1x system-auth-control
4. aaa authentication dot1x default local
5. aaa local authorization credential-download default local
6. aaa local authentication default authorization default
7. eap profile wcm_eap_profile
8. method leap
9. end
DETAILED STEPS
Switch# configure terminal Switch(config)# aaa new-model Switch(config)# dot1x system-auth-control Switch(config)# aaa authentication dot1x default local Switch(config)# aaa authorization credential-download default local Switch(config)# aaa local authentication default authorization default Switch(config)#eap profile wcm_eap_profile Switch(config)# method leap Switch(config)# end
Creating Client VLAN for WPA2+AES
Create a VLAN for the WPA2+AES type of local authentication. This VLAN is later mapped to a WLAN.
1. configure terminal
2. vlan vlan_ID
3. exit
4. interface vlan vlan_ID
5. ip address
6. ipv6 address
7. exit
DETAILED STEPS
Switch# configure terminal Switch(config)# vlan105 Switch (config-vlan)# exit Switch (config)# interface vlan 105 Switch(config-if)#ip address 10.8.105.10 255.255.255.0 Switch(config-if)#ipv6 address 2001:db8::10:1/64 Switch(config-if)#exit Switch(config)#
Creating WLAN for WPA2+AES
Create a WLAN and map it to the client VLAN created for WPA2+AES.
1. configure terminal
2. wlan wpas2-aes-wlan 1 wpas2-aes-wlan
3. client vlan 105
4. local-auth wcm_eap_profile
5. security dot1x authentication-list default
6. no shutdown
7. end
DETAILED STEPS
Switch# configure terminal Switch(config)#wlan wpa2-aes-wlan 1 wpa2-aes-wlan Switch(config-wlan)#client vlan 105 Switch(config-wlan)#local-auth wcm_eap_profile Switch(config-wlan)#security dot1x authentication-list default Switch(config-wlan)#no shutdown Switch(config-wlan)# exit
Configuring External RADIUS Server
Configuring RADIUS Authentication Server Host
1. configure terminal
2. radius server One
3. address ipv4 address auth-portauth_port_number acct-port acct_port_number
4. address ipv6 address auth-portauth_port_number acct-port acct_port_number
5. key 0cisco
6.
DETAILED STEPS
Switch# configure terminal Switch (config)# radius server One Switch (config-radius-server)# address ipv4 10.10.10.10 auth-port 1812 acct-port 1813 Switch (config-radius-server)# address ipv6 2001:db8::25:2 auth-port 1812 acct-port 1813 Switch (config-radius-server)# key 0 cisco Switch (config-radius-server)#exit
Configuring RADIUS Authentication Server Group
1. configure terminal
2. aaa new-model
3. aaa group server radius wcm_rad
4. server <ip address>auth-port1812acct-port1813
5. aaa authentication dot1x method_list group wcm_rad
6. dot1x system-auth-control
7. aaa session-idcommon
DETAILED STEPS
Switch# configure terminal Switch(config)# aaa new-model Switch(config)# aaa group server radius wcm_rad Switch(config-sg-radius)# server One auth-port 1812 acct-port 1813 Switch(config-sg-radius)# server Two auth-port 1812 acct-port 1813 Switch(config-sg-radius)# server Three auth-port 1812 acct-port 1813 Switch(config)# aaa authentication dot1x method_list group wcm_rad Switch(config)# dot1x system-auth-control Switch(config)# aaa session-id common Switch(config)#
Creating a Client VLAN
1. configure terminal
2. vlan 137
3. exit
4. interface vlan 137
5. ip address 10.7.137.10 255.255.255.0
6. ipv6 address 2001:db8::30:1/64
7. end
DETAILED STEPS
Switch# configure terminal Switch(config)# vlan137 Switch(config-vlan)# exit Switch(config)# interface vlan137 Switch(config-if)# ip address 10.7.137.10 255.255.255.0 Switch(config-if)# ipv6 address 2001:db8::30:1/64 Switch(config-if)# end
Creating 802.1x WLAN Using an External RADIUS Server
1. configure terminal
2. wlan ngwc-1x<ssid>ngwc-1x
3. broadcast-ssid
4. no security wpa
5. security dot1x
6. security dot1x authentication-list wcm-rad
7. client vlan 137
8. no shutdown
9. end
DETAILED STEPS
Switch# configure terminal Switch(config)#wlan ngwc_8021x 2 ngwc_8021x Switch(config-wlan)# broadcast-ssid Switch(config-wlan)# no security wpa Switch(config-wlan)# security dot1x Switch(config-wlan)# security dot1x authentication-list wcm-rad Switch(config-wlan)# client vlan 137 Switch(config-wlan)# no shutdown Switch(config-wlan)# end
Additional References
Related Documents
| Related Topic | Document Title |
|---|---|
| IPv6 command reference | IPv6 Command Reference (Catalyst 3850 Switches) |
| WLAN command reference | WLAN Command Reference, Cisco IOS XE Release 3SE (Catalyst 3850 Switches) |
| WLAN configuration | WLAN Configuration Guide, Cisco IOS XE Release 3SE (Catalyst 3850 Switches) |
Error Message Decoder
| Description | Link |
|---|---|
| To help you research and resolve system error messages in this release, use the Error Message Decoder tool. |
https://www.cisco.com/cgi-bin/Support/Errordecoder/index.cgi |
MIBs
| MIB | MIBs Link |
|---|---|
| All supported MIBs for this release. | To locate and download MIBs for selected platforms, Cisco IOS releases, and feature sets, use Cisco MIB Locator found at the following URL: |
Technical Assistance
| Description | Link |
|---|---|
| The Cisco Support website provides extensive online resources, including documentation and tools for troubleshooting and resolving technical issues with Cisco products and technologies. To receive security and technical information about your products, you can subscribe to various services, such as the Product Alert Tool (accessed from Field Notices), the Cisco Technical Services Newsletter, and Really Simple Syndication (RSS) Feeds. Access to most tools on the Cisco Support website requires a Cisco.com user ID and password. |
Feature Information for IPv6 WLAN Security
| Feature |
Release |
Modification |
|---|---|---|
| IPv6 WLAN Security Functionality |
Cisco IOS XE 3.2SE |
This feature was introduced. |
 Feedback
Feedback