Overview of Port-Based Traffic Control
Port-based traffic control is a set of Layer 2 features on the Cisco Catalyst switches used to filter or block packets at the port level in response to specific traffic conditions. The following port-based traffic control features are supported in the Cisco IOS Release for which this guide is written:
-
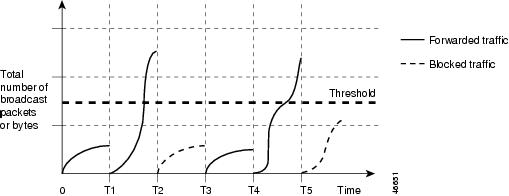
Storm Control
-
Protected Ports
-
Port Blocking
-
Port Security
-
Protocol Storm Protection

 Feedback
Feedback