- New and Changed Information
- Preface
- Cisco DCNM Introduction
- Part 1: Cisco DCNM-SAN Installation
- Preparing Cisco DCNM-SAN Client
- Installing Cisco DCNM-SAN Database
- Installing Cisco DCNM-SAN
- Maintaining Cisco DCNM-SAN
- Uninstalling Cisco DCNM-SAN
- Licensing Cisco DCNM-SAN
- Part 2: Cisco DCNM-LAN Installation
- Deploying Cisco DCNM-LAN
- Preparing Cisco DCNM-LAN Database
- Installing Cisco DCNM-LAN Servers
- Licensing Cisco DCNM-LAN Deployment
- Upgrading Cisco DCNM-LAN Servers
- Configuring Cisco DCNM-LAN Servers
- Installing and Administering Cisco DCNM VSB
- Uninstalling Cisco DCNM-LAN Servers
- Troubleshooting Cisco DCNM-LAN Server Installation
- Index
Cisco DCNM Installation and Licensing Guide, Release 5.x
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- November 27, 2012
Chapter: Installing Cisco DCNM-SAN
- Installing the Management Software
- Upgrading DCNM-SAN
- Upgrading Fabric Manager in Cisco SAN-OS Releases Prior to 3.1(2b)
- Upgrading Fabric Manager in Cisco SAN-OS Releases 3.1(2b) and Later to 3.2(1)
- Upgrading the Management Software
- Upgrading DCNM-SAN Federated Server
- Upgrading Fabric Manager Server and Fabric Manager Standalone Version Using the Fabric Manager Update Installer
- Integrating Cisco DCNM-SAN with Other Management Tools
- Running DCNM-SAN Behind a Firewall
Installing Cisco DCNM-SAN Management Software
This chapter describes about installing DCNM-SAN components and contains the following sections:
Installing the Management Software
To install the software for the first time, or if you want to update or reinstall the software, access the supervisor module with a web browser. Click the Install links on the web page that is displayed. The software running on your workstation is verified to make sure you are running the most current version of the software. If it is not current, the most recent version is downloaded and installed on your workstation.

Note![]() Before upgrading or uninstalling DCNM-SAN or Device Manager, make sure any instances of these applications have been shut down.
Before upgrading or uninstalling DCNM-SAN or Device Manager, make sure any instances of these applications have been shut down.
- Upgrade—The installer detects your current version of DCNM-SAN and Device Manager, and it provides the option to upgrade. The default is to upgrade to the latest version of DCNM-SAN or Device Manager.
- Uninstall—If you are downgrading from Fabric Manager 2.x or later to Fabric Manager 1.3x or earlier, use the Uninstall batch file or shell script. Do not delete the MDS 9000 folder as this might prevent your installation from being upgraded in the future.

Note![]() We recommend that you install the latest version of the DCNM-SAN applications. DCNM-SAN is backward-compatible with the Cisco MDS SAN-OS and Cisco FabricWare software running on the switches. When upgrading, upgrade the DCNM-SAN software first, and then upgrade the Cisco MDS SAN-OS or NX-OS or Cisco FabricWare software on the switch.
We recommend that you install the latest version of the DCNM-SAN applications. DCNM-SAN is backward-compatible with the Cisco MDS SAN-OS and Cisco FabricWare software running on the switches. When upgrading, upgrade the DCNM-SAN software first, and then upgrade the Cisco MDS SAN-OS or NX-OS or Cisco FabricWare software on the switch.
This section includes the following topics:
- Prerequisites
- Installing DCNM-SAN on Solaris
- Installing DCNM-SAN on Windows
- Importing PM Statitics Data to DCNM-SAN
Prerequisites
Before you can install Cisco DCNM-SAN, ensure that the Cisco DCNM-SAN system meets the following prerequisites:
- Users installing DCNM-SAN must have full administrator privileges to create user accounts and start services. Users should also have access to all ports. These are the ports used by DCNM-SAN Server and the PostgreSQL database: 1098, 1099, 4444, 4445, 8009, 8083, 8090, 8092, 8093, 514, 5432.
- Starting from Cisco MDS NX-OS Release 4.1(3a), DCNM-SAN is no longer packaged with a Cisco MDS 9000 Family switch.
- For switches running Cisco MDS 9000 FabricWare, you can download DCNM-SAN from Cisco.com. To download the software from Cisco.com, go to the following website:
http://cisco.com/cgi-bin/tablebuild.pl/mds-fm - When you connect to the server for the first time, DCNM-SAN checks to see if you have the correct Sun Java Virtual Machine version installed on your workstation. DCNM-SAN looks for version 1.6(x) during installation. If required, install the Sun Java Virtual Machine software.
- On Windows, remote DCNM-SAN installations or upgrades should be done through the console using VNC or through the Remote Desktop Client (RDC) in console mode (ensuring RDC is used with the /Console option). This is very important if the default PostgreSQL database is used with DCNM-SAN, because this database requires the local console for all installations and upgrades.
- Before installing Cisco DCNM-SAN on a Windows Vista system, turn the User Account Control (UAC) off. To turn off UAC, select Start > Control Panel > User Accounts > Turn User Account Control on or off, clear the Use User Account Control (UAC) to help protect your computer check box, and then click OK. Click Restart Now to apply the change.
- Telnet Client application is not installed by default on Microsoft Windows Vista. To install Telnet Client, select Start > Programs > Control Panel > Click Turn Windows features on or off (if you have UAC turned on you will need to give it the permission to continue). Check the Telnet Client check box and then click OK.
- You can run CiscoWorks on the same PC as DCNM-SAN, even though the Java requirements are different. When installing the later Java version for DCNM-SAN, make sure it does not overwrite the earlier Java version required for CiscoWorks. Both versions of Java can coexist on your PC.

Note![]() When launching the DCNM-SAN installer, the console command option is not supported.
When launching the DCNM-SAN installer, the console command option is not supported.

Note![]() Using the Cisco DCNM-SAN installer in GUI mode requires that you must login to the remote server using VNC or XWindows. Using telnet or SSH to install Cisco DCNM-SAN in GUI mode is not possible.
Using the Cisco DCNM-SAN installer in GUI mode requires that you must login to the remote server using VNC or XWindows. Using telnet or SSH to install Cisco DCNM-SAN in GUI mode is not possible.
Before you can access the Cisco DCNM-SAN, you must complete the following tasks:
- Install a supervisor module on each switch that you want to manage.
- Configure the supervisor module with the following values using the setup routine or the CLI:
–![]() IP address assigned to the mgmt0 interface
IP address assigned to the mgmt0 interface
–![]() SNMP credentials (v3 user name and password or v1/v2 communities), maintaining the same user name and password for all the switches in the fabric
SNMP credentials (v3 user name and password or v1/v2 communities), maintaining the same user name and password for all the switches in the fabric
- Ensure you disable the default firewall on a Microsoft Windows 2008 64-bit machine before you install Cisco DCNM. To disable the firewall, use the following command:
Cisco MDS SAN-OS Release 2.x, 3.x, and NX-OS Release 4.2(0) and later supports AAA authentication using RADIUS, TACACS, or local SNMP users.
The Cisco Device Manager software executable files reside on each supervisor module of each Cisco MDS 9000 Family switch running Cisco MDS SAN-OS or NX-OS software in your network. The supervisor module provides an HTTP server that responds to browser requests and distributes the software to Windows or UNIX network management stations. You can also find Cisco DCNM-SAN software on Cisco.com at the following website:
Supported Software

Note![]() For the latest information on supported software, refer to the Cisco DCNM Release Notes, Release 5.2.
For the latest information on supported software, refer to the Cisco DCNM Release Notes, Release 5.2.
Cisco DCNM-SAN and Cisco Device Manager have been tested with the following software:
–![]() Windows Vista SP1 (Enterprise edition), Windows 2008 (32 bit and 64 bit), Windows 7
Windows Vista SP1 (Enterprise edition), Windows 2008 (32 bit and 64 bit), Windows 7
–![]() Red Hat Enterprise Linux Server Release 5.4 or later
Red Hat Enterprise Linux Server Release 5.4 or later

Note![]() You cannot install Cisco DCNM-SAN and DCNM-LAN Server on Windows 7 (32 bit and 64 bit) platform.
You cannot install Cisco DCNM-SAN and DCNM-LAN Server on Windows 7 (32 bit and 64 bit) platform.
–![]() Sun JRE and JDK 1.6(x) is supported
Sun JRE and JDK 1.6(x) is supported

Note![]() Do not use Java 1.6 Update 13
Do not use Java 1.6 Update 13
The following common web browsers that support Adobe Flash 10 are qualified to use with Cisco DCNM-LAN and DCN-SAN.
–![]() Oracle Database 10g Express, Oracle Enterprise Edition 10g, Oracle Enterprise Edition 11g and 11g2 Enterprise Edition (Cisco recommends Oracle 11g2 Enterprise Edition for customers with large fabrics.)
Oracle Database 10g Express, Oracle Enterprise Edition 10g, Oracle Enterprise Edition 11g and 11g2 Enterprise Edition (Cisco recommends Oracle 11g2 Enterprise Edition for customers with large fabrics.)
–![]() PostgreSQL 8.1, 8.4 (Windows and Red Hat Enterprise Linux Server Release 5.4 or later)
PostgreSQL 8.1, 8.4 (Windows and Red Hat Enterprise Linux Server Release 5.4 or later)
–![]() PostgreSQL 8.1 (Solaris 9 and 10)
PostgreSQL 8.1 (Solaris 9 and 10)
Java Database Connectivity
Java database connectivity (JDBC) is the JavaSoft specification of a standard application programming interface (API) that allows Java programs to access database management systems.
A JDBC driver is a software component enabling a Java application to interact with a database. DCNM-SAN uses Oracle JDBC drivers ojdbc14.jar and ojdbc14.jar to access the Oracle database and store data.
You can download the recommended version (10.2.0.1.0) of the ojdbc14.jar file, from the following link:
http://www.oracle.com/technology/software/tech/java/sqlj_jdbc/htdocs/jdbc_10201.html
Alternatively, if you have access to the system where Oracle is installed in your environment, you can find the jar file in the Oracle installation directory under ORACLE_HOME\jdbc\lib\.
Minimum Hardware Requirements
For a PC running DCNM-SAN Server on large fabrics (1000 or more end devices), we recommend you use a Dual Core/Dual CPU high-speed system with 2 GB of RAM and 10 GB of free disk space.
Installing DCNM-SAN on Solaris
To install DCNM-SAN on Solaris, follow these steps:
Step 1![]() Copy the DCNM-SAN jar file dcnm-installer-k9.5.2.0.252.S2-solaris.bin from Cisco.com to a folder on the Solaris workstation.
Copy the DCNM-SAN jar file dcnm-installer-k9.5.2.0.252.S2-solaris.bin from Cisco.com to a folder on the Solaris workstation.
Step 2![]() Change the filepermissions using the following command:
Change the filepermissions using the following command:
Step 3![]() Launch the installer using the following command:
Launch the installer using the following command:
Step 4![]() Follow the on-screen instructions provided in the DCNM-SAN management software setup wizard.
Follow the on-screen instructions provided in the DCNM-SAN management software setup wizard.
Installing DCNM-SAN on Windows
Starting from MDS NX-OS Release 4.1(3a) and later, DCNM-SAN has an express installation option. When you select this option, DCNM-SAN will be installed on your computer with a set of default user credentials. If the PostgreSQL database is not present on your computer, the installer will install PostgreSQL. If the PostgreSQL database is present, the installer will upgrade it to latest version. You may change the default credentials after the installation is complete.
Express Installation
To install (Express) DCNM-SAN on Windows, follow these steps:
Step 1![]() Click the Install Management Software link.
Click the Install Management Software link.
Step 2![]() Choose Management Software > Cisco DCNM-SAN.
Choose Management Software > Cisco DCNM-SAN.
Step 3![]() Click the Installing DCNM link.
Click the Installing DCNM link.
Step 4![]() Click the DCNM Installer link.
Click the DCNM Installer link.
You see the welcome message in the Cisco DCNM-SAN Installer window.
Figure 1-1 Management Software Setup Wizard

Step 5![]() Click DCNM-SAN and then click Standalone.
Click DCNM-SAN and then click Standalone.
Step 6![]() Check the Express (with Default Options) check box, and then click Next to begin express installation.
Check the Express (with Default Options) check box, and then click Next to begin express installation.

Note![]() DCNM-SAN express installation option uses admin as the user name and password as the user password. The user may change the password after the installation is complete.
DCNM-SAN express installation option uses admin as the user name and password as the user password. The user may change the password after the installation is complete.

Note![]() DCNM-SAN express installation option installs the PostgreSQL database with dcnmuser as the user name and password_1_2_3 as the user password. The user may change the password after the installation is complete.
DCNM-SAN express installation option installs the PostgreSQL database with dcnmuser as the user name and password_1_2_3 as the user password. The user may change the password after the installation is complete.
You see the default credentials in the Cisco DCNM-SAN Installer window shown in Figure 1-2.
Figure 1-2 Default User Credentials

Once the installation is finished, you see an installation completed message in the Cisco DCNM-SAN Installer window shown in Figure 1-3.


Note![]() You can choose to launch DCNM-SAN or Device Manager by checking the Launch DCNM-SAN or Launch Device Manager check boxes. Icons for DCNM-SAN and Device Manager are automatically created on the desktop.
You can choose to launch DCNM-SAN or Device Manager by checking the Launch DCNM-SAN or Launch Device Manager check boxes. Icons for DCNM-SAN and Device Manager are automatically created on the desktop.
Step 8![]() Click Finish to close the Cisco DCNM-SAN Installer window.
Click Finish to close the Cisco DCNM-SAN Installer window.
Custom Installation
To install (Custom) DCNM-SAN on Windows, follow these steps:
Step 1![]() Click the Install Management Software link.
Click the Install Management Software link.
Step 2![]() Choose Management Software > Cisco DCNM-SAN.
Choose Management Software > Cisco DCNM-SAN.
Step 3![]() Click the Installing DCNM link.
Click the Installing DCNM link.
Step 4![]() Click the DCNM Installer link.
Click the DCNM Installer link.
You see the introduction message in the Cisco DCNM-SAN Installer window shown in Figure 1-4.
Figure 1-4 Introduction Screen

Step 5![]() Click the Next to begin the installation.
Click the Next to begin the installation.
You see the Installation Help window as shown in Figure 1-5.
You see the Choose Installation Settings window as shown in Figure 1-6
Figure 1-6 Choose Installation Settings

Step 7![]() Check the DCNM-SAN checkbox and then click the radio button for either:
Check the DCNM-SAN checkbox and then click the radio button for either:
a.![]() DCNM-SAN Server (Licensed) to install the server components for DCNM-SAN Server.
DCNM-SAN Server (Licensed) to install the server components for DCNM-SAN Server.
Add Server to an existing server federation to add the server to an already existing server federation.
SMIS to enable the SMIS option for the server.
b.![]() DCNM-SAN Standalone to install the standalone version of DCNM-SAN.
DCNM-SAN Standalone to install the standalone version of DCNM-SAN.

Note![]() You should verify that the DCNM-SAN Server hostname entry exists on the DNS server, unless the DCNM-SAN Server is configured to bind to a specific interface during installation.
You should verify that the DCNM-SAN Server hostname entry exists on the DNS server, unless the DCNM-SAN Server is configured to bind to a specific interface during installation.

Note![]() DCNM-SAN Standalone is a single application containing DCNM-SAN Client and a local version of DCNM-SAN Server bundled together. DCNM-SAN Standalone allows you to discover and monitor the immediate fabric.
DCNM-SAN Standalone is a single application containing DCNM-SAN Client and a local version of DCNM-SAN Server bundled together. DCNM-SAN Standalone allows you to discover and monitor the immediate fabric.
Step 8![]() Select an installation folder on your workstation for DCNM-SAN.
Select an installation folder on your workstation for DCNM-SAN.
On Windows, the default location is C:\Program Files\Cisco Systems. On a UNIX (Solaris or Linux) machine, the installation path name is /usr/local/cisco/dcm or $HOME/dcm, depending on the permissions of the user doing the installation.
You see the Database Options dialog box shown in Figure 1-7.
Figure 1-7 Database Options Dialog Box

Step 10![]() Click the radio button for either Install PostgreSQL or Use existing DB to specify which database you want to use.
Click the radio button for either Install PostgreSQL or Use existing DB to specify which database you want to use.
If you choose Install PostgreSQL, accept the defaults and enter a password. The PostgreSQL database will be installed.

Note![]() If you choose to install PostgreSQL, you must disable any security software you are running, because PostgreSQL may not install certain folders or users.
If you choose to install PostgreSQL, you must disable any security software you are running, because PostgreSQL may not install certain folders or users.

Note![]() Before you install PostgreSQL, remove the cygwin/bin from your environment variable path if Cygwin is running on your system.
Before you install PostgreSQL, remove the cygwin/bin from your environment variable path if Cygwin is running on your system.
Step 11![]() If you select Use existing DB, click the radio button for either PostgreSQL 8.1/8.2 or Oracle10/11g.
If you select Use existing DB, click the radio button for either PostgreSQL 8.1/8.2 or Oracle10/11g.
Step 12![]() Click Next in the Database Options dialog box.
Click Next in the Database Options dialog box.
You see the Local User Credentials dialog box shown in Figure 1-8.
Figure 1-8 Local User Credentials Dialog Box

Step 13![]() Enter a user name and password and click Next.
Enter a user name and password and click Next.
You see the Authentication Options dialog box shown in Figure 1-9.
Figure 1-9 Authentication Options Dialog Box

Step 14![]() Choose an authentication mode (Local, RADIUS or TACACS) and click Next.
Choose an authentication mode (Local, RADIUS or TACACS) and click Next.
Step 15![]() Click Verify to test your login.
Click Verify to test your login.
You see the Configuration Options dialog box for DCNM-SAN Standalone shown in Figure 1-10.
Figure 1-10 Configuration Options Dialog Box for DCNM-SAN Standalone

Step 16![]() Check the Use HTTPS Web Server check box as desired.
Check the Use HTTPS Web Server check box as desired.
Step 17![]() Click Advanced Settings to configure security settings.
Click Advanced Settings to configure security settings.

Note![]() You can change the DCNM-SAN Server port number to a port that is not used by any other application.
You can change the DCNM-SAN Server port number to a port that is not used by any other application.

Note![]() You should verify that the DCNM-SAN Server hostname entry exists on the DNS server, unless the DCNM-SAN Server is configured to bind to a specific interface during installation.
You should verify that the DCNM-SAN Server hostname entry exists on the DNS server, unless the DCNM-SAN Server is configured to bind to a specific interface during installation.

Note![]() If you check the Use HTTPS Web Server check box, the Web Server Port field is grayed out and the default port is 443.
If you check the Use HTTPS Web Server check box, the Web Server Port field is grayed out and the default port is 443.

Note![]() If you select a specific IP address during installation and change the server host IP address, you must modify the following two files that are all located in the $INSTALL/conf directory. Change server.bindaddrs to the new IP address in the server.properties file and change wrapper.app.parameter.4 to the new IP address in the FMServer.conf file.
If you select a specific IP address during installation and change the server host IP address, you must modify the following two files that are all located in the $INSTALL/conf directory. Change server.bindaddrs to the new IP address in the server.properties file and change wrapper.app.parameter.4 to the new IP address in the FMServer.conf file.
Step 18![]() Check the Require SNMPv3 and Disable SNMPv2c check box for enhanced security and then click OK.
Check the Require SNMPv3 and Disable SNMPv2c check box for enhanced security and then click OK.
Step 19![]() Click Next in the Configuration Options dialog box.
Click Next in the Configuration Options dialog box.
You see the Pre-Installation Summary window as shown in Figure 1-11.
Figure 1-11 Pre-Installation Summary

Once the installation is completed, you see an installation completed message in the Cisco DCNM-SAN Installer window shown in Figure 1-12.


Step 21![]() Click Done to close the Cisco DCNM-SAN Installer window.
Click Done to close the Cisco DCNM-SAN Installer window.
On a UNIX (Solaris or Linux) machine, shell scripts are created in the install directory. The shell scripts that run the programs equivalent to the Windows services are FMServer.sh, all the server-side data and Performance Manager data are stored in the install directory.
DCNM-SAN Client cannot run without DCNM-SAN Server. The server component is downloaded and installed when you download and install DCNM-SAN. On a Windows machine you install the DCNM-SAN Server as a service. This service can then be administered using Services in the Microsoft Windows Control Panel. The default setting for the DCNM-SAN Server service is that the server is automatically started when the machine is rebooted. You can change this behavior by modifying the properties in Services.
Importing PM Statitics Data to DCNM-SAN
To manually import existing Performance Manager statistics data to DCNM-SAN, follow these steps:
Step 1![]() Stop the DCNM-SAN Server.
Stop the DCNM-SAN Server.
Step 2![]() Copy the existing RRD file (from a prior installation) to $INSTALLDIR/pm/db.
Copy the existing RRD file (from a prior installation) to $INSTALLDIR/pm/db.
Step 3![]() Run the $INSTALLDIR/bin/pm.bat s.
Run the $INSTALLDIR/bin/pm.bat s.
Step 4![]() Restart the DCNM-SAN Server.
Restart the DCNM-SAN Server.
Step 5![]() Add the fabric to the Performance Manager collection using WebClient.
Add the fabric to the Performance Manager collection using WebClient.
Creating DCNM-SAN Shortcut Manually
The DCNM-SAN shortcut on the desktop is available only when launching the application for the first time. The shortcut is not offered when you lauch DCNM-SAN from the DCNM download page.
To create DCNM-SAN shortcut on the desktop, follow these steps:
Step 1![]() Navigate to Control Panel > Java.
Navigate to Control Panel > Java.
The Java Control Panel displays as shown in the Figure 1-14.
Figure 1-14 Java Control Panel Dialog Box

Step 2![]() In the Temporary Internet Files area, click View.
In the Temporary Internet Files area, click View.
The Java Cache Viewer dialog box displays as shown in Figure 1-15.
Figure 1-15 Java Cache Viewer Dialog Box
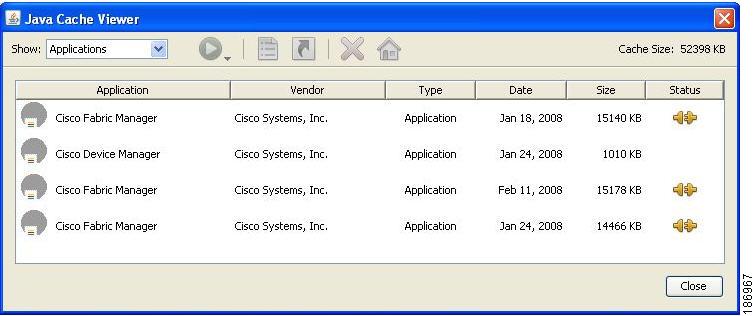
Step 3![]() To recreate the shortcut, right-click on the application, and select Install Shortcuts from the shortcut menu, as shown in Figure 1-16.
To recreate the shortcut, right-click on the application, and select Install Shortcuts from the shortcut menu, as shown in Figure 1-16.

Upgrading DCNM-SAN
This section includes the following topics:
- Upgrading Fabric Manager in Cisco SAN-OS Releases Prior to 3.1(2b)
- Upgrading Fabric Manager in Cisco SAN-OS Releases 3.1(2b) and Later to 3.2(1)
- Upgrading Fabric Manager Server and Fabric Manager Standalone Version Using the Fabric Manager Update Installer
Upgrading Fabric Manager in Cisco SAN-OS Releases Prior to 3.1(2b)
When you install Cisco Fabric Manager 3.2(1), data is migrated from the Hypersonic HSQL database to either the PostgreSQL database or Oracle Database 10g Express during the installation. To install the PostgreSQL database on Windows, click the FM Installer link on the CD.

Note![]() If you are upgrading a previous installation of DCNM-SAN Server, be sure the previous installation of the database is running. Do not uninstall the previous version. If the previous version is uninstalled, the database will not be migrated and your server settings will not be preserved. After you ensure that the previous installation is running, follow the steps listed in the “Installing the Management Software” section. Before beginning the upgrade, you must close DCNM-SAN and Device Manager.
If you are upgrading a previous installation of DCNM-SAN Server, be sure the previous installation of the database is running. Do not uninstall the previous version. If the previous version is uninstalled, the database will not be migrated and your server settings will not be preserved. After you ensure that the previous installation is running, follow the steps listed in the “Installing the Management Software” section. Before beginning the upgrade, you must close DCNM-SAN and Device Manager.
Upgrading Fabric Manager in Cisco SAN-OS Releases 3.1(2b) and Later to 3.2(1)
When you install Cisco SAN-OS 3.2(1), data is migrated from the Hypersonic HSQL database to either the PostgreSQL database or Oracle Database 10g Express during the installation. Data is also migrated from Oracle to Oracle.

Note![]() If you migrate the database from Oracle to Oracle, the schema is updated as required by Cisco SAN-OS 3.2(1).
If you migrate the database from Oracle to Oracle, the schema is updated as required by Cisco SAN-OS 3.2(1).
To install the PostgreSQL database on Windows, click the FM Installer link on the CD. To install Oracle Database 10g Express, follow the instructions in the “Installing Oracle” section.
Upgrading the Management Software
If you log into a switch running Cisco MDS SAN-OS with Device Manager and that switch has a later version of the management software, you are prompted to install the later version. To upgrade the Cisco MDS DCNM-SAN software, follow the instructions described in the “Installing the Management Software” section. You can also upgrade Device Manager at any time by entering the IP address or host name of the supervisor module with the later version of software in the Address field of your browser. You will need a new CD to upgrade DCNM-SAN.

Note![]() As of Cisco MDS SAN-OS Release 3.x, downgrades are not supported through the installer. To downgrade DCNM-SAN or Device Manager to an earlier release, you need to manually uninstall first and then reinstall the previous version of DCNM-SAN or Device Manager.
As of Cisco MDS SAN-OS Release 3.x, downgrades are not supported through the installer. To downgrade DCNM-SAN or Device Manager to an earlier release, you need to manually uninstall first and then reinstall the previous version of DCNM-SAN or Device Manager.
Upgrading DCNM-SAN Federated Server
To upgrade DCNM-SAN federated server on Linux and Solaris machines, follow these steps:
Step 1![]() Log on to the server node in the federation.
Log on to the server node in the federation.
Step 2![]() Run $INSTALLDIR/FMServer.sh stop to stop the server node.
Run $INSTALLDIR/FMServer.sh stop to stop the server node.
Step 3![]() Run the dcnm-installer-k9.5.2.0.252.S2.exe (java -Xmx512m -jar dcnm-installer-k9.5.2.0.252.S2.jar) on the first server node to upgrade the first server in the federation.
Run the dcnm-installer-k9.5.2.0.252.S2.exe (java -Xmx512m -jar dcnm-installer-k9.5.2.0.252.S2.jar) on the first server node to upgrade the first server in the federation.
Step 4![]() Repeat steps 1 through step 3 on all the other servers nodes.
Repeat steps 1 through step 3 on all the other servers nodes.
To upgrade DCNM-SAN federated server on a Windows machine, follow these steps:
Step 1![]() Log on to the server node in the federation.
Log on to the server node in the federation.
Step 2![]() Stop the DCNM-SAN Server service. To stop the DCNM-SAN Server service, click Start > Control Panel > Administrative Tools > Services.
Stop the DCNM-SAN Server service. To stop the DCNM-SAN Server service, click Start > Control Panel > Administrative Tools > Services.
Step 3![]() Right-click Cisco DCNM-SAN Server services in the services window, and then click Stop to stop the services.
Right-click Cisco DCNM-SAN Server services in the services window, and then click Stop to stop the services.
Step 4![]() Repeat step 1 through step 3 on all the server nodes.
Repeat step 1 through step 3 on all the server nodes.
Step 5![]() Run the dcnm-installer-k9.5.2.0.252.S2.jar (java -Xmx512m -dcnm-installer-k9.5.2.0.252.S2.jar) on the first server node to upgrade the first server.
Run the dcnm-installer-k9.5.2.0.252.S2.jar (java -Xmx512m -dcnm-installer-k9.5.2.0.252.S2.jar) on the first server node to upgrade the first server.
Step 6![]() Repeat step 5 on all the other server nodes.
Repeat step 5 on all the other server nodes.
Upgrading Fabric Manager Server and Fabric Manager Standalone Version Using the Fabric Manager Update Installer
As of Release 3.3(1a), you can use the Cisco MDS 9000 Fabric Manager Update Installer to upgrade:
The Fabric Manager Update Installer is smaller in size than the Fabric Manager installer which makes it easier to download. The update Installer has limited capability to upgrade Fabric Manager Server or the Fabric Manager Standalone version and it does not have the capability to install a database or the Fabric Manager Server infrastructure (JBoss). Table 1-1 shows the recommended Fabric Manager upgrade paths.
|
|
|
|
|---|---|---|
3.0(x)1 |
3. 
Note |
|
| 2. 
Note |
||
1. 
Note |
||
1. 
Note |
Integrating Cisco DCNM-SAN with Other Management Tools
You can use DCNM-SAN, Device Manager, and Performance Manager with these management tools:
- Cisco Traffic Analyzer —Allows you to break down traffic by VSANs and protocols and to examine SCSI traffic at a logical unit number (LUN) level.
- Cisco Protocol Analyzer —Enables you to examine actual sequences of Fibre Channel frames easily using the Fibre Channel and SCSI decoders Cisco developed for Ethereal.
- Cisco Port Analyzer Adapter 2 —Encapsulates SPAN traffic (both Fibre Channel control and data plane traffic) in an Ethernet header for transport to a Windows PC or workstation for analysis. Both the Cisco Traffic Analyzer and Cisco Protocol Analyzer require the PAA to transport MDS SPAN traffic to a Windows PC or workstation.
For more information on these tools and how they work together with the Cisco DCNM-SAN management applications, see Cisco MDS 9000 Family NX-OS Troubleshooting Guide.
Running DCNM-SAN Behind a Firewall
For Windows PCs running DCNM-SAN, Device Manager, and Performance Manager behind a firewall, certain ports need to be available.
By default, DCNM-SAN Client and Device Manager use the first available UDP port for sending and receiving SNMP responses. The UDP SNMP trap local ports are 1162 for DCNM-SAN, and 1163 or 1164 for Device Manager. DCNM-SAN Server also opens TCP RMI port 9099.
In Fabric Manager Release 2.1(2) or later, you can select the UDP port that Fabric Manager Client or Device Manager uses for SNMP responses by uncommenting the following statement:
- On a Windows desktop, uncomment the following in the FabricManager.bat or DeviceManager.bat file in the C:\Program Files\Cisco Systems\MDS9000\bin directory:
- On a UNIX desktop, uncomment the following in the FabricManager.sh or DeviceManager.sh file in the $HOME/.cisco_mds9000/bin directory:
In Fabric Manager Release 3.2(1) or later, Fabric Manager Client initiates communication with Fabric Manager Server on the port 9099 for Java Naming Directory and Interface (JNDI) lookup. Fabric Manager Server redirects the client to 1098 and JBoss directs the request to the appropriate service.
Fabric Manager Server proxy services uses a configurable TCP port (9198 by default) for SNMP communications between the Fabric Manager Client or Device Manager and Fabric Manager Server.
The Fabric Manager Server component requires two predictable TCP ports to be opened on the firewall for an incoming connection:
As long as these two ports are open, Fabric Manager Client can connect to the server. Other TCP ports connected to Fabric Manager Client are initiated by the server, which is behind the firewall.
The following table lists all ports used by DCNM-SAN applications:
DCNM-SAN Server Proxy Services
The DCNM-SAN Client and Device Manager use SNMP to communicate with the DCNM-SAN Server. In typical configurations, the DCNM-SAN Server may be installed behind a firewall. The SNMP proxy service available in Cisco Fabric Manager Release 2.1(1a) or later provides a TCP-based transport proxy for these SNMP requests. The SNMP proxy service allows you to block all UDP traffic at the firewall and configure DCNM-SAN Client to communicate over a configured TCP port.
DCNM-SAN uses the CLI for managing some features on the switches. These management tasks are used by DCNM-SAN and do not use the proxy services. Your firewall must remain open for CLI access for the following features:
- External and internal loopback test
- Flash files
- Create CLI user
- Security - ISCSI users
- Show image version
- Show tech
- Switch resident reports (syslog, accounting)
- Zone migration
- Show cores
If you are using the SNMP proxy service and another application on your server is using port 9198, you need to modify your workstation settings.

Note![]() The MDS switch always checks the local SNMP users before the remote AAA users, unlike the CLI.
The MDS switch always checks the local SNMP users before the remote AAA users, unlike the CLI.
To modify a Windows workstation, follow these steps:
Step 1![]() Open Internet Explorer and select Tools > Internet Options.
Open Internet Explorer and select Tools > Internet Options.
You see the Internet Options dialog box.
Step 2![]() Select the Connections tab and click LAN Settings.
Select the Connections tab and click LAN Settings.
You see the LAN Settings dialog box.
Step 3![]() Check the Use a Proxy Server for your LAN check box and click Advanced.
Check the Use a Proxy Server for your LAN check box and click Advanced.
Step 4![]() Add your server IP Address or local host under the Exceptions section.
Add your server IP Address or local host under the Exceptions section.
Step 5![]() Click OK to save your changes.
Click OK to save your changes.

 Feedback
Feedback