- Preface
- Troubleshooting Overview
- Troubleshooting FCoE Issues
- Troubleshooting Layer 2 Switching Issues
- Troubleshooting QoS Issues
- Troubleshooting SAN Switching Issues
- Troubleshooting Security Issues
- Troubleshooting System Management Issues
- Troubleshooting Virtual Port Channel Issues
- Troubleshooting Config-Sync Issues
- Index
Cisco Nexus 5500 Troubleshooting Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- June 18, 2015
Chapter: Troubleshooting Overview
Troubleshooting Overview
This chapter introduces the basic concepts, methodology, and general troubleshooting guidelines for problems that may occur when configuring and using the Cisco Nexus 5000 Series switch.
Troubleshooting Basics
The following are the basic steps for troubleshooting:
Step 1![]() Gather information that defines the specific symptoms.
Gather information that defines the specific symptoms.
Step 2![]() Identify all potential problems that could be causing the symptoms.
Identify all potential problems that could be causing the symptoms.
Step 3![]() Systematically eliminate each potential problem (from most likely to least likely) until the symptoms disappear.
Systematically eliminate each potential problem (from most likely to least likely) until the symptoms disappear.
To identify the possible problems, you need to use a variety of tools and understand the overall configuration.The following chapters in this guide describe many approaches and specific solutions to potential problems.
Troubleshooting a Switch Crash
When a switch crashes, the cause might be from the failure of a process, and results in a reload of the switch.
A crash is usually recorded with a core file on the switch and includes the reason for the crash, such as a failed process. The following can help you determine the cause of the crash:
- Use the show cores command to determine if a core file was recorded. You also can use the show process log command to display the processes and if a core was created.
- Use the show processes log details command to provide useful information about the reason for the crash:
- Note the module-number and the PID number in the output of the show cores command for the process that crashed. (Usually the module number is 1 for a Nexus 5000 switch.)
- Use the copy core :// module-id / PID ftp : command to export the file and contact the TAC to obtain an analysis of the file.
- Obtain the timestamp of the crash with the show version, show system reset-reason, or show cores commands. With the show logging command, review the events that happened just before the crash.
Best Practices
Best practices are the recommended steps you should take to ensure the proper operation of your switch.
- Maintain a consistent Cisco NX-OS release across all your Cisco Nexus 5000 switches.
- Refer to the release notes for your Cisco SAN-OS release for the latest features, limitations, and caveats.
- Enable system message logging.
- Troubleshoot any new configuration changes after implementing the change.
- Use the Device Manager to manage your configuration and detect possible problems before they become critical.
Common Terms
|
|
|
|---|---|
Fabric Manager Tools and CLI Commands
This section highlights the tools and CLI commands that are commonly used to troubleshoot problems. These tools and commands are a portion of what you may use to troubleshoot your specific problem.
The following chapters in this guide may describe additional tools and commands specific to the symptoms and possible problems covered in that chapter.
NX-OS Tips
Displaying what is required from the configuration
Displaying within Config Mode
With NX-OS, you can display required data from within the configuration mode, so there is no need to back out to the switch prompt.
Pipe command
Using the pipe command to only display required keyword
Copy command
Redirecting output
NX-OS allows you to redirect outputs to files and flash areas in the switch.
Redirecting output of the show tech-support details command
Use the tac-pac filename command to redirect the output of the show tech-support details command to a file and then gzip the file.
The file is stored on bootflash:// filename provided that there is enough memory available. If you do not specify a filename, NX-OS creates the file as volatile:show_tech_out.gz. Copy the file from the device using the procedure in the copy command section.
From volatile, copy the file to the bootflash, FTP, or TFTP server.
NX-OS command listing
Narrowing scope of keywords
You can use many commands like grep and include to narrow the scope of a keyword.
Logging
You can use logging through the CLI or Device Manager. In the following examples, the logging command and the Device Manager display severity information:
Viewing Severity Information with the CLI
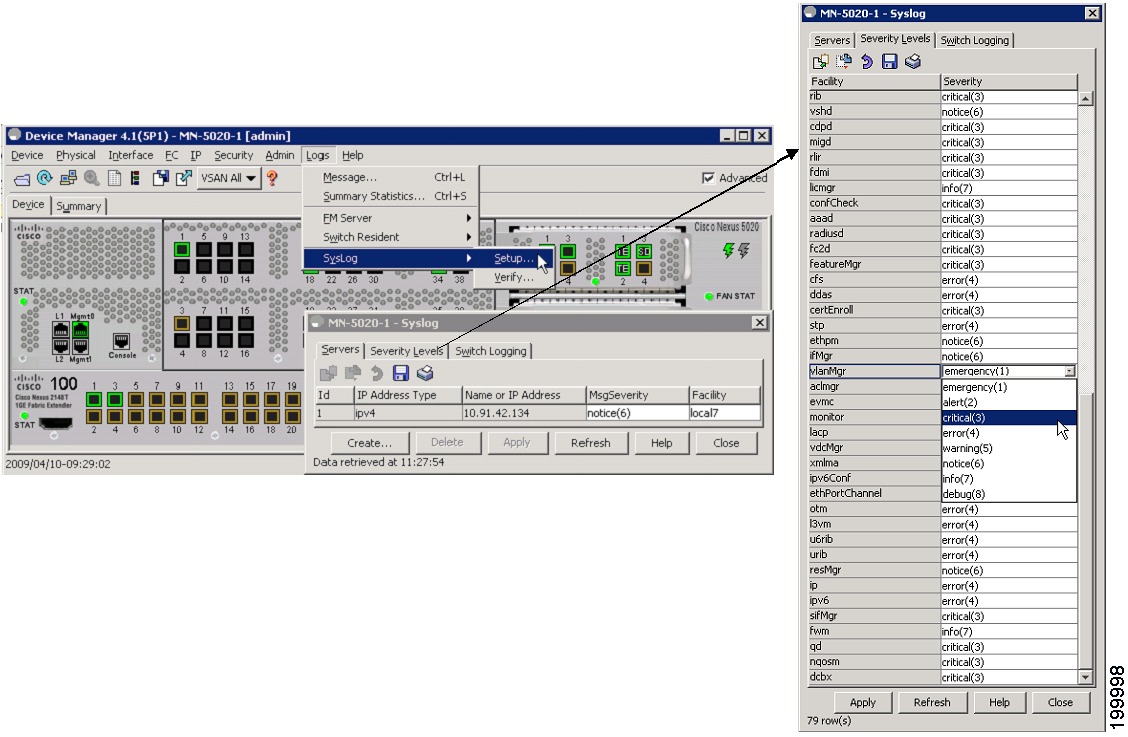
Viewing Severity Levels in the Device Manager
Ethanalyzer and SPAN
Ethanalyzer is a tool that collects frames that are destined to, or originate from, the Nexus 5000 control plane. Node to switch or switch to switch traffic can be seen with this tool.
SPAN is a feature whereby frames that are transient to the switch are copied to a second port for analysis. Node to switch or node to node traffic can be seen via this method.
Ethanalyzer
Ethanalyzer is a Cisco NX-OS protocol analyzer tool based on the Wireshark open source code. This tool is a command-line version of Wireshark that captures and decodes packets. You can use Ethanalyzer to troubleshoot your network and analyze the control-plane traffic.
The following example is for viewing the Spanning Tree Protocol (STP) and Fibre Channel: Using 0 in the command captures output until you press Ctrl-C. The FCID is a well-known name for switch domain controller.
SPAN
The Switched Port Analyzer (SPAN) feature—sometimes called port mirroring or port monitoring—selects network traffic for analysis by a network analyzer. The network analyzer can be a Cisco SwitchProbe, a Fibre Channel Analyzer, or other Remote Monitoring (RMON) probes.
SPAN sources refer to the interfaces from which traffic can be monitored. The Cisco Nexus 5000 Series switch supports Ethernet, virtual Ethernet, Fibre Channel, virtual Fibre Channel, port channels, SAN port channels, VLANs, and VSANs as SPAN sources. With VLANs or VSANs, all supported interfaces in the specified VLAN or VSAN are included as SPAN sources. You can choose the SPAN traffic in the ingress direction, the egress direction, or both directions for Ethernet, virtual Ethernet, Fibre Channel, and virtual Fibre Channel source interfaces:
- Ingress source (Rx)—Traffic entering the switch through this source port is copied to the SPAN destination port.
- Egress source (Tx)—Traffic exiting the switch through this source port is copied to the SPAN destination port.

Note![]() For the Cisco Nexus 5548 Switch, Fibre Channel ports cannot be configured as ingress source ports in a SPAN session.
For the Cisco Nexus 5548 Switch, Fibre Channel ports cannot be configured as ingress source ports in a SPAN session.
Source Ports
A source port, also called a monitored port, is a switched interface that you monitor for network traffic analysis. The switch supports any number of ingress source ports (up to the maximum number of available ports on the switch) and any number of source VLANs or VSANs.
A source port has these characteristics:
- Can be of any port type: Ethernet, virtual Ethernet, Fibre Channel, virtual Fibre Channel, port channel, SAN port channel, VLAN, and VSAN.
- Cannot be monitored in multiple SPAN sessions.
- Cannot be a destination port.
- Each source port can be configured with a direction (ingress, egress, or both) to monitor. For VLAN, VSAN, port channel, and SAN port channel sources, the monitored direction can only be ingress and applies to all physical ports in the group. The rx/tx option is not available for VLAN or VSAN SPAN sessions.
- Beginning with Cisco NX-OS Release 5.0(2)N1(1). Port channel and SAN port channel interfaces can be configured as ingress or egress source ports.
- Source ports can be in the same or different VLANs or VSANs.
- For VLAN or VSAN SPAN sources, all active ports in the source VLAN or VSAN are included as source ports.
- The Cisco Nexus 5010 switch supports a maximum of two egress SPAN source ports. This limit does not apply to the Cisco Nexus 5020 Switch and the Cisco Nexus 5548 switch.
SPAN Destinations
SPAN destinations refer to the interfaces that monitors source ports. The Cisco Nexus 5000 Series switch supports Ethernet and Fibre Channel interfaces as SPAN destinations.
|
|
|
|---|---|
Characteristics of Destination Ports
Each local SPAN session must have a destination port (also called a monitoring port) that receives a copy of traffic from the source ports, VLANs, or VSANs. A destination port has these characteristics:
- Can be any physical port, Ethernet, Ethernet (FCoE), or Fibre Channel. Virtual Ethernet and virtual Fibre Channel ports cannot be destination ports.
- Cannot be a source port.
- Cannot be a port channel or SAN port channel group.
- Does not participate in spanning tree while the SPAN session is active.
- Is excluded from the source list and is not monitored if it belongs to a source VLAN of any SPAN session.
- Receives copies of sent and received traffic for all monitored source ports. If a destination port is oversubscribed, it can become congested. This congestion can affect traffic forwarding on one or more of the source ports.
Monitor Caveats
Limitations of Nexus 5000 SPAN CoS values are not preserved at the monitor (span) destination.
- Packets coming in on the monitor source with an unknown VLAN tag are spanned ouf with a 0 VLAN tag (priority tag).
- For Ethernet destination, the monitor session is up only if the destination port is configured as switch port monitor.
- Out of 18 configurable sessions, only two are active (up state). The rest are in down state (hardware resource unavailable).
Configuration limitations: VLAN or port-channel cannot be configured as egress source
SPAN Configuration

Verifying the SPAN Session
Suspending the SPAN Session
Debugging
Command-Line Debugging
Available debugs depend on features enabled in NX-OS. There are many different options to select when turning on debugs.
Determine the destination of the output:
You must have administrator privileges to run debugs. Debugs can only be run from the CLI.
Debug Logging
Set the log file as CiscoLive_debugs, using the debug logfile command. Then, use the show debug command to see name of the debug file.
Display debugging to the screen with the following command:
Copy the debug file from MDS to a server with the copy command. When you enter the VRF, if none is specified then the default is used.
To delete the debug logfile, use one of the following commands:
If you do not use one of these commands, the debug logfile will be cleared and overwritten when the next debug logfile is created. The system only allows one debug logfile to exist.
Debugs to the Direct Telnet Window
Consistency Checker Commands
Starting with Cisco NX-OS Release 7.1(4)N1(1), the following Forwarding Manager (FWM) Persistent Storage Service (PSS) consistency checker commands are introduced. For earlier releases, you need to use a Linux binary to run the FWM PSS consistency checker. Contact the Cisco Technical Assistance Center (TAC) for assistance with the Linux binary option.
The Forwarding Manager (FWM) Persistent Storage Service (PSS) consistency checkers detects inconsistencies in the FWM PSS.

Note![]() Before you run the consistency checker, ensure the system is stable to avoid any false alarms. You might have to run the consistency checkers multiple times (five times) to get accurate results.
Before you run the consistency checker, ensure the system is stable to avoid any false alarms. You might have to run the consistency checkers multiple times (five times) to get accurate results.
- show platform fwm info pss runtime_consistency —Runs the consistency checker for the Forwarding Manager (FWM) Persistent Storage Service (PSS).
The following is a sample output for the show platform fwm info pss runtime_consistency command:
- show platform fwm info pss runtime_consistency_report —Displays the inconsistency report for the Forwarding Manager (FWM) Persistent Storage Service (PSS) consistency checker.
The following is a sample output for the show platform fwm info pss runtime_consistency_report command:
Starting with Cisco NX-OS Release 7.1(4)N1(1), the following FWM Layer 2 Multipathing (L2MP) consistency checker commands are introduced. For earlier releases, you need to use a python script to run the consistency checker. Contact the Cisco Technical Assistance Center (TAC) for assistance with the python script option.
The FWM Layer 2 Multipathing (L2MP) hardware and software consistency checker detects inconsistencies between the L2MP data structures and the corresponding hardware programmed entries. This tool is useful in troubleshooting issues in Fabricpath data forwarding.
- show consistency-checker l2mp —Runs the FWM Layer 2 Multipathing (L2MP) hardware and software consistency checker for all modules.
The following is a sample output for the show consistency-checker l2mp command:
- show consistency-checker l2mp module module-number —Runs the FWM Layer 2 Multipathing hardware and software consistency checker for a particular module.
The following is a sample output for the show consistency-checker l2mp module module-number command:
Cisco Discover Protocol
Cisco Discover Protocol (CDP) version 2 is applied to the physical Ethernet interface and only works when enabled at both ends of the link. LLDP standard is derived from CDP.
CDP is used to verify proper connectivity to correct network devices, very useful at switch deployment.
The following example shows the arguments that can be used with the show CDP command:
Failover
FCoE Traffic
When the Nexus 5000 experiences loss of fabric connectivity, it brings down all the affected vFC interfaces.
The following methods are used to signal the host of loss of connectivity to the FC fabric
- FIP Clear Link Virtual Link to the CNA will be signaled to indicate the ‘shut’ state of vFC. Throughout the ‘shut’ period FCF Advertisements indicate ‘not available for login’.
- In case the loss of connectivity is over the FCoE network, FIP keep-alives are used by the FCF and the CNA to timeout the login sessions. The keep-alive timers are configurable.
Non-FCoE traffic
Under certain failure scenarios where the access switch has lost all uplink connectivity to the aggregation layer, the CNA needs to be signaled of the loss of LAN connectivity. This helps the CNA failover the host traffic to the standby port. Traditionally, such a failure is signaled by bringing down the host facing link. Bringing down the link achieves two purposes:
- Host is signaled of loss of connectivity.
- The access switch stops forwarding traffic to and from the host-facing link.
However, in the converged network, even though the LAN connectivity is lost at the access switch, the SAN connectivity might still be intact. Bringing down the entire host-facing link is not desirable. Instead, the loss of connectivity is signaled over protocols. Loss of SAN connectivity is signaled using the FIP Clear Virtual Link message. Loss of LAN connectivity is signaled using logical link status TLVs defined in DCBX and VIC protocols.
LAN Traffic
When LAN connectivity is lost for a particular VLAN on the uplinks, the VLAN is also brought down on the host-facing link.
Dedicating a VLAN solely for FCoE traffic helps with shutting down non-FCoE traffic to and from the host-facing link without disrupting FCoE traffic from the same host.
 Feedback
Feedback