Cisco Nexus 1000V Network Segmentation Manager Configuration Guide, Release 4.2(1)SV2(2.1)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- June 24, 2013
Chapter: Configuring Network Segmentation Manager
- Information About Network Segmentation Manager
- Prerequisites
- Guidelines and Limitations
- Default Settings
- Configuring NSM
- Verifying the NSM Configuration
- Configuration Examples for NSM
- Changing a Port Profile Associated with an NSM Policy
- Changing the Network Segmentation Policy Associated with a Network
- Feature History for Network Segmentation Manager
Configuring Network Segmentation Manager
This chapter contains the following sections:
- Information About Network Segmentation Manager
- Prerequisites
- Guidelines and Limitations
- Default Settings
- Configuring NSM
- Verifying the NSM Configuration
- Configuration Examples for NSM
- Changing a Port Profile Associated with an NSM Policy
- Changing the Network Segmentation Policy Associated with a Network
- Feature History for Network Segmentation Manager
Information About Network Segmentation Manager
Prerequisites
Network Segmentation Manager (NSM) has the following prerequisites:
- You have installed and configured the Cisco Nexus 1000V software using the Cisco Nexus 1000V Installation and Upgrade Guide.
- You have a vCenter Server configured in vCloud Director and vShield Manager. See the Cisco Nexus 1000V and VMware Compatibility Information for information about the version compatibility of the vCloud Director and vShield Manager for the Cisco Nexus 1000V.
- You have associated a vShield Manager with every vCenter Server.
- You have created an organization in vCloud Director.
- You have created a provider and organization virtual datacenter (vDC) in vCloud Director.
- Ensure that the Virtual Supervisor Module (VSM) has an active SVS connection.
- Ensure that the Virtual Supervisor Module (VSM) and Virtual Ethernet Module (VEM) connectivity is functioning.
- You have added hosts to the Cisco Nexus 1000V.
- Ensure that the user specified for NSM on vShield Manager is a network administrator.
Guidelines and Limitations
Network segmentation has the following configuration guidelines and limitations:
- You must enable the VLANs that are going to be used through NSM and add them to the uplink.
- Ensure that the infrastructure has port 443 open.
- You must enter the feature http-server command on the Cisco Nexus 1000V to allow web service communication.
- You must enable the segmentation feature to use NSM for a Virtual Extensible Local Area Network (VXLAN) through vCloud Director. In a network segmentation policy, VXLAN is used for a segmentation policy. See the Cisco Nexus 1000V VXLAN Configuration Guide.
Default Settings
| Parameters | Default |
|---|---|
VLAN policy (port-profile template) |
default_vlan_template |
segmentation policy (port-profile template) |
default_segmentation_template |
The default port-profiles default_vlan_template and default_segmentation_template are created automatically.
 Note |
If a network creation request comes with a tenant ID and backing type that does not match a network segmentation policy, the default_vlan_template or default_segmentation_template is used during network creation from vCloud Director. For more information, see the Cisco Nexus 1000V VXLAN Configuration Guide. See the Cisco Nexus 1000V and VMware Compatibility Information for information about the supported network pool in vCloud Director with the Cisco Nexus 1000V. |
Configuring NSM
This section guides you through the NSM configuration process that is shown in the following figure. After completing each procedure, return to this section to make sure that you have completed all required procedures in the correct sequence.
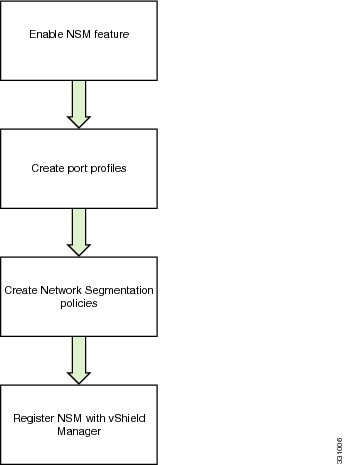
| Step 1 | Enable the NSM feature. See Enabling NSM. |
| Step 2 |
Create a port profile for network segmentation policies. See Creating a Port Profile for Network Segmentation Policies. When you enable the NSM feature, the default port profiles are created automatically. This step is not required if you use the default port profiles (default_vlan_template and default_segmentation_template). |
| Step 3 |
Create network segmentation policies. See Creating Network Segmentation Policies. When you enable the NSM feature, the default network segmentation policies are created automatically. This step is required only if the port profiles that you created in the previous step need to be inherited to the network segmentation policies for specific tenant IDs. |
| Step 4 | Register NSM with vShield Manager. See Registering vShield Manager with NSM. |
Enabling NSM
Log in to the CLI in EXEC mode.
This example shows how to enable the NSM feature and display the output:
switch# configure terminal Enter configuration commands, one per line. End with CNTL/Z. switch(config)# feature network-segmentation-manager switch(config)# show feature Feature Name Instance State -------------------- -------- -------- cts 1 disabled dhcp-snooping 1 disabled http-server 1 enabled lacp 1 disabled netflow 1 disabled network-segmentation 1 enabled port-profile-roles 1 disabled private-vlan 1 disabled segmentation 1 enabled sshServer 1 enabled tacacs 1 disabled telnetServer 1 disabled vtracker 1 disabled vxlan-gateway 1 disabled switch(config)#
Creating a Port Profile for Network Segmentation Policies
You can create a port profile to use features of the Cisco Nexus 1000V for network segmentation policies.
This example shows how to create a segmentation type port profile and display the output:
switch# configure terminal switch(config)# port-profile type vethernet ABC_profile_segmentation switch(config-port-prof)# no shutdown switch(config-port-prof)# state enabled switch(config-port-prof)# show running-config port-profile ABC_profile_segmentation !Command: show running-config port-profile ABC_profile_segmentation !Time: Thu Dec 1 19:58:44 2011 version 4.2(1)SV1(5.1) port-profile type vethernet ABC_profile_segmentation no shutdown state enabled switch(config-port-prof)#
Creating Network Segmentation Policies
Network segmentation policies are a set of policies that inherit customized port profiles. The policy type can be either VLAN or segmentation. This policy type corresponds to the network pool type in vCloud Director. VLAN network segmentation policies are used for networks that are created from VLAN-backed network pools. Segmentation network segmentation policies are used for networks that are created from network isolation-backed network pools in the vCloud Director 1.5 and VXLAN-backed network pools in the vCloud Director 5.1.
The network segmentation policies also contains a tenant ID and a reference to a port profile that may contain other policies for Cisco Nexus 1000V features. Each tenant ID is unique and can be associated with only one segmentation and one VLAN network segmentation policy. The tenant ID correlates to the Organization Universally Unique Identifier (UUID) in vCloud Director. For more information about retrieving the organization UUID from VMware vCloud Director, see 2012943.
 Note |
If a network segmentation policy with a tenant ID is not created, the default_vlan_template or default_segmentation_template is used during network creation from vCloud Director. For more information, see the Cisco Nexus 1000V VXLAN Configuration Guide. See the Cisco Nexus 1000V and VMware Compatibility Information for information about the supported network pool in vCloud Director with the Cisco Nexus 1000V. |
- Log in to the CLI in EXEC mode.
- Enable the NSM feature.
- Know the tenant IDs for tenants that require nondefault network segmentation policies. The tenant IDs for network segment policies can be found on vCloud Director. It is located in the address bar of the browser when viewing an organization. In the following example, https://[VCloud_director_IP]/cloud/#/vAppListPage?org=91e87e80-e18b-460f-a761-b978c0d28aea the tenant ID is 91e87e80-e18b-460f-a761-b978c0d28aea
- Create the port profiles with all the required feature port profiles before importing them to the network segmentation policy. To create a port profile, see Creating a Port Profile for Network Segmentation Policies.
- Know about port profile inheritance. See the Cisco Nexus 1000V Port Profile Configuration Guide.
This example shows how to create a NSM policy for ABC Inc. for VXLAN networks:
switch# configure terminal
switch(config)# network-segment policy abc-policy-vxlan
switch(config-network-segment-policy)# description network segmentation policy for ABC for
VXLAN networks
switch(config-network-segment-policy)# type segmentation
switch(config-network-segment-policy)# id f5dcf127-cdb0-4bdd-8df5-9515d6dc8170
switch(config-network-segment-policy)# import port-profile ABC_profile_segmentation
switch(config-network-segment-policy)# show running-config network-segment policy abc-policy-vxlan
!Command: show running-config network-segment policy abc-policy-vxlan
!Time: Fri Aug 26 18:34:50 2011
version 4.2(1)SV1(5.1)
feature network-segmentation-manager
network-segment policy abc-policy-vxlan
description network segmentation policy for ABC for VXLAN networks
id f5dcf127-cdb0-4bdd-8df5-9515d6dc8170
type segmentation
import port-profile port-profile ABC_profile_segmentation
switch(config-network-segment-policy)#
This example shows how to create a NSM policy for ABC Inc. for VLAN networks:
switch# configure terminal switch(config)# network-segment policy abc-policy-vlan switch(config-network-segment-policy)# description network segmentation policy for ABC for VLAN networks switch(config-network-segment-policy)# type vlan switch(config-network-segment-policy)# id f5dcf127-cdb0-4bdd-8df5-9515d6dc8170 switch(config-network-segment-policy)# import port-profile ABC_profile_vlan switch(config-network-segment-policy)#
 Note |
If a tenant specific policy is defined through network segmentation policies, you should define it for both segmentation and VLAN types. |
Registering vShield Manager with NSM
- Log in to vShield Manager.
- Verify that vShield Manager is connected to vCenter Server.
- Enable the NSM feature.
- Know the range of multicast addresses.
- Know the segment ID pool.
- Ensure that the segment ID range allocated to vShield Manager does not overlap with other instances in the network or VXLANs used on the Cisco Nexus 1000V.
- Ensure that the user specified for NSM on vShield Manager is a network administrator.
Unregistering vShield Manager with NSM
Verifying the NSM Configuration
Use the following commands to verify the NSM configuration:
| Command | Purpose |
|---|---|
show network-segment manager switch |
Displays the Cisco Nexus 1000V configured with NSM. |
show running-config port-profile |
Displays the port profile configuration. |
show vlan private-vlan [type] |
Displays the NSM policy configuration. |
Configuration Examples for NSM
Changing a Port Profile Associated with an NSM Policy
When you create a network in vCloud Director, network segmentation policies are created on the NSM and these network segmentation policies are inherited on a port profile. To associate a different port profile with the deployed network, you can change the port profile that is associated with the network segmentation policy.
| Step 1 | Identify all the networks that are associated with the network segmentation policy. See Identifying the Networks Associated with the Network Segmentation Policy. |
| Step 2 | Manually remove the inheritance for the existing port profile. See the "Removing Inherited Policies from a Port Profile" section in the Cisco Nexus 1000V Port Profile Configuration Guide for more information. |
| Step 3 | Manually inherit the new port profile that will be associated with the network segmentation policy. See the "Inheriting a Configuration from a Port Profile" section in the Cisco Nexus 1000V Port Profile Configuration Guide for more information. |
| Step 4 | Update the network segmentation policy. For more information, see Updating the Network Segmentation Policy. |
Identifying the Networks Associated with the Network Segmentation Policy
You can identify the networks associated with the network segmentation policy.
This example shows how to identify the networks that are associated with a network segmentation policy:
switch(config)# show network-segment policy usage network-segment policy default_segmentation_template dvs.VCDVSint-org-cn2-e46e9686-2327-49df-ad5c-a3f89c00cfb8 network-segment policy default_vlan_template network-segment policy abc-policy-vxlan dvs.VCDVSint-org-nexus-6141babd-bdc8-4e86-8f16-1ac786fb377f network-segment policy abc-policy-vlan switch(config)#
Updating the Network Segmentation Policy
You can update a network segmentation policy.
- Log in to the CLI in EXEC mode.
- Enable the NSM feature.
- Know the tenant IDs for the tenants that require nondefault network segmentation policies.
- Create the port profiles with all the required feature port profiles before importing them to the network segmentation policy.
- Know about port profile inheritance. See the Cisco Nexus 1000V Port Profile Configuration Guide.
This example shows how to update the network segmentation policy:
switch# configure terminal switch(config)# show running-config network-segment policy abc-policy-vxlan network-segment policy abc-policy-vxlan description network segmentation policy for ABC for VXLAN networks type segmentation id f5dcf127-cdb0-4bdd-8df5-9515d6dc8170 import port-profile ABC_profile_segmentation switch(config)# network-segment policy abc-policy-vxlan switch(config-network-segment-policy)# import port-profile ABC_profile_segmentation_new force switch(config)# show running-config network-segment policy abc-policy-vxlan network-segment policy abc-policy-vxlan description network segmentation policy for ABC for VXLAN networks type segmentation id f5dcf127-cdb0-4bdd-8df5-9515d6dc8170 import port-profile ABC_profile_segmentation_new switch#
Changing the Network Segmentation Policy Associated with a Network
When you create a network in vCloud Director, network segmentation policies are created on the NSM. To use other nondefault policies for any new or old networks associated with an organization vDC in vCloud Director, you must change the network segmentation policy that is associated with a network.
| Step 1 | Identify all the networks that need to be migrated. See Identifying the Networks. |
| Step 2 | Manually remove the inheritance of the port profile that is associated with the network segmentation policy from the network. See the "Removing Inherited Policies from a Port Profile" section in the Cisco Nexus 1000V Port Profile Configuration Guide for more information. |
| Step 3 | Manually inherit the new port profile that will be associated with the network segmentation policy on the network. See the "Inheriting a Configuration from a Port Profile" section in the Cisco Nexus 1000V Port Profile Configuration Guide for more information. |
| Step 4 | Migrate the networks from the default network segmentation policy to the nondefault network segmentation policy. See Migrating Networks to Non Default Network Segmentation Policy. |
Identifying the Networks
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# configure terminal | Enters global configuration mode. |
| Step 2 | switch(config)# show network-segment network | Displays the networks associated with a network segmentation policy. |
This example shows how to display the networks that are associated with a network segmentation policy:
switch(config)# show network-segment network network dvs.VCDVSint-org-cn2-e46e9686-2327-49df-ad5c-a3f89c00cfb8 tenant id: 2b4ca1b2-ba8e-456c-b772-a4730af16e2e network-segment policy: default_segmentation_template segment id: 4107 multicast ip: 225.0.0.1 network dvs.VCDVSint-org-nexus-6141babd-bdc8-4e86-8f16-1ac786fb377f tenant id: 91e87e80-e18b-460f-a761-b978c0d28aea network-segment policy: seg-template-nexus-org segment id: 4108 multicast ip: 225.0.0.2 switch(config)#
Migrating Networks to the Nondefault Network Segmentation Policy
You can migrate the networks from the default network segmentation policy to the nondefault network segmentation policy.
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | switch# configure terminal | Enters global configuration mode. |
||
| Step 2 | switch(config)# network-segment policy migrate id isolation_id type nw_type dest-policy policy | Migrates the networks from the default network segmentation policy to the nondefault destination network segmentation policy.
|
||
| Step 3 | switch(config)# show network-segment network | (Optional) Displays the networks that are associated with a network segmentation policy. |
This example shows how to migrate networks to the nondefault segmentation policy:
switch(config)# show network-segment network network dvs.VCDVStenantid_vlan-74e36255-e588-4357-8abe-15d2cc7feaec tenant id: da5c49a8-dd1b-4326-9da0-3c5e6a2c1b87 network-segment policy: default_segmentation_template segment id: 4107 multicast ip: 225.0.0.1 switch(config)# network-segment policy migrate id da5c49a8-dd1b-4326-9da0-3c5e6a2c1b87 type segmentation dest-policy org_seg switch(config)#
 Note |
If a warning appears, manually remove the inheritance of the port profile that is associated with the network segmentation policy from the network. Then, manually inherit the new port profile that will be associated with the network segmentation policy on the network. See the Cisco Nexus 1000V Port Profile Configuration Guide for more information. |
switch(config)# show network-segment network network dvs.VCDVStenantid_vlan-74e36255-e588-4357-8abe-15d2cc7feaec tenant id: da5c49a8-dd1b-4326-9da0-3c5e6a2c1b87 network-segment policy: org_seg segment id: 4107 multicast ip: 225.0.0.1 switch(config)#
Feature History for Network Segmentation Manager
This table includes only the updates for those releases that have resulted in additions or changes to the feature.
| Feature Name | Release | Feature Information |
|---|---|---|
Network Segmentation Manager |
4.2(1)SV1(5.1) |
Introduced the Network Segmentation Manager (NSM) feature. |
 Feedback
Feedback