Cisco Video Surveillance Deployment Guide for the UCS Express Platform
Available Languages
Table Of Contents
Video Surveillance Deployment Guide for the UCS Express Platform
EtherSwitch Router Configuration
Onboard Ethernet Router Configuration
External Interface Router Configuration
Installing and Configuring the ISR Router and SRE
Verifying the IOS Image of the ISR
Verifying and Configuring the SRE Hypervisor
Deploying the VSM 6.3.2 Template
Configuring Network Switches for the VSM VM
Video Surveillance Deployment Guide for the UCS Express Platform
November 2012This guide describes the key requirements and instructions for deploying a virtualized Cisco® Video Surveillance Manager (VSM) on the Cisco Unified Computing System™ (UCS) Express platform.
Contents
This document includes the following sections:
Installing and Configuring the ISR Router and SRE
Deploying the VSM 6.3.2 Template
Configuring Network Switches for the VSM VM
Introduction
This guide describes the key requirements and instructions for deploying a virtualized Cisco VSM on the Cisco UCS Express platform. This guide describes installation and configuration guidelines for the Service Ready Engine (SRE) blade server, VMware vSphere Hypervisor, Integrated Service Router Generation 2 (ISR G2), and the VSM virtual machine (VM), as well as best practice recommendations.
Audience
This guide is intended for use by Cisco System Engineers, Physical Security Advanced Technology Provider (ATP) partners, and technical field staff who develop and implement Cisco Video Surveillance and UCS Express for branch office solutions.
A successful implementation also requires additional knowledge in the following areas:
•
Cisco ISR-G2 (29xx/39xx Series) Internetwork Operating System (IOS) router configuration
•
Cisco Video Surveillance Manager (Version 6.3.2) installation and configuration
Scope
This guide contains detailed instructions on the installation of the VSM on UCS Express on the ISR G2 (Figure 1).
Figure 1 Deployment Guide Scope


Note
This guides assumes that the ESXi Hypervisor is installed on the SRE 910 service module.

Note
This guide does not describe the configuration and operation of these products. For a full description of these products, see the "More Information" section.
System Overview
The Cisco UCS Express product is an SRE blade on an ISR G2 branch office router running the SRE-V (ESXi) virtualization software. The 2900 and 3900 series routers have various Gigabit Ethernet interfaces onboard, wide-area network (WAN) interface card (WIC) interface slots, and multiple service module slots, depending on the model (Figure 2).
Figure 2 Cisco Integrated Service Routers and Service Ready Engine

The SRE 910 blade is inserted into one of the service module slots. Figure 3 displays that there are two Gigabit Ethernet internal interfaces on the router: one connected to the router and the second connected to MultiGigabit Fabric (MGF). There is also one external Gigabit Ethernet interface on the front panel of the SRE. The SRE blade has two 500 GB hard drives and 4 GB of random-access memory (RAM).
Figure 3 SRE Hardware Architecture

EtherSwitch Router Configuration
The specific router configuration depends on which interface is being used to connect to the external switch. In the first recommended deployment configuration (Figure 4), the EtherSwitch Enhanced High-speed WAN interface card (EHWIC) or EtherSwitch Service Module is used to connect to the external switch (Figure 5).
Figure 4 Host Router Connected to External Switch via MGF and EtherSwitch
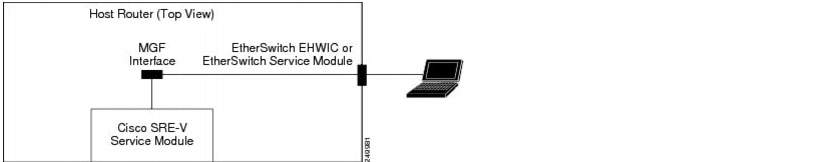
Figure 5 Router Configuration Sample and Topology for External Switch via MGF and EtherSwitch
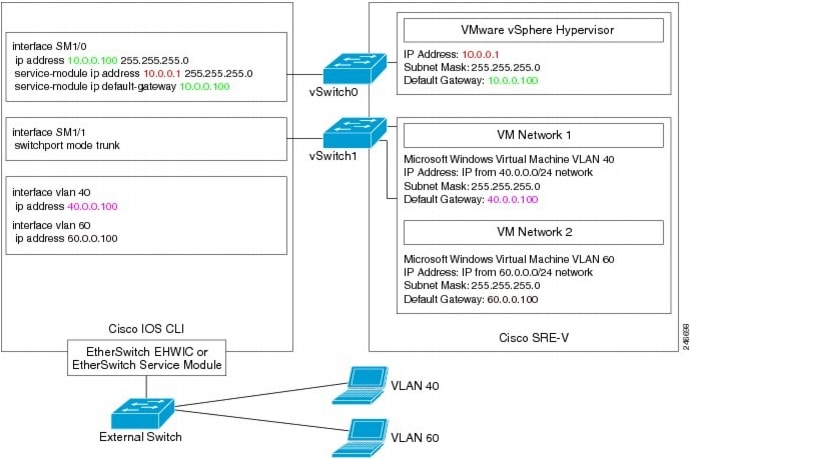

Note
For this configuration, the Cisco EtherSwitch EHWIC/EtherSwitch service module is required. A list of supported EtherSwitch modules can be found in the Installation and Configuration Guide for Cisco Services Ready Engine Virtualization, Release 2.0 at http://www.cisco.com/en/US/docs/interfaces_modules/services_modules/sre_v/2.0/user/guide/overview.html.
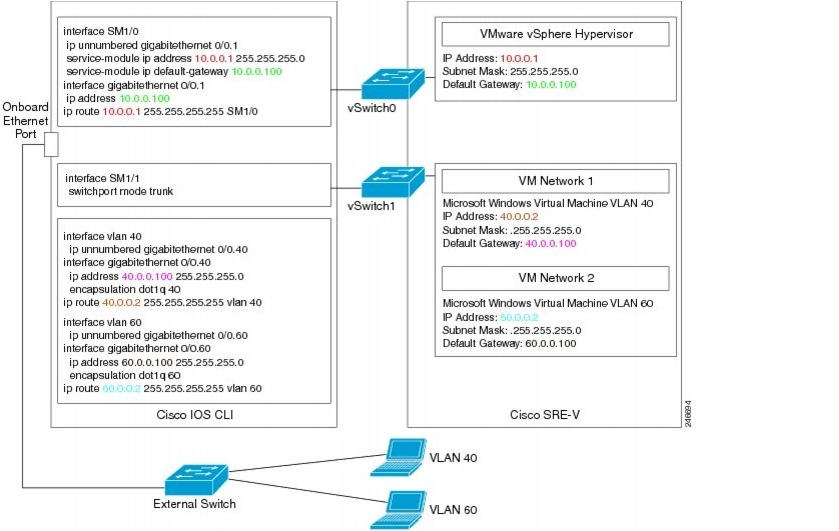
Onboard Ethernet Router Configuration
In the second possible deployment configuration (Figure 6), the router's onboard Ethernet port is used to connect to the external switch (Figure 7).
Figure 6 Host Router Connected to an External Switch via an Onboard Router Port
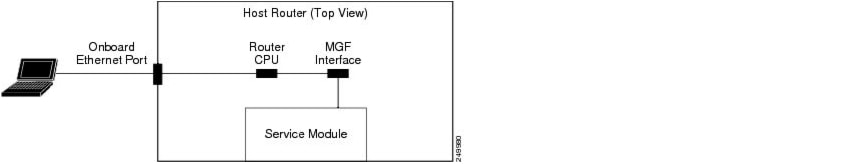
Figure 7 Router Configuration Sample and Topology for External Switch via Onboard Port
External Interface Router Configuration
In the third potential deployment configuration (Figure 8), the external interface on the front panel of the UCS Express Service Module is used to connect to the external switch.
Figure 8 Host Router for External Switch via Front Panel Service Module Interface
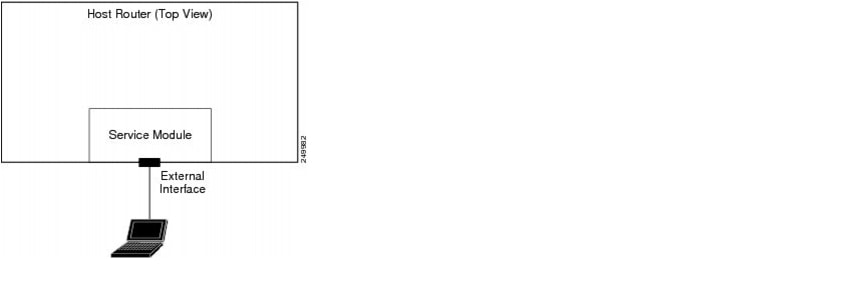
This option has some limitations:
•
It does not go through the router.
•
ISR Router features, such as Transmission Control Protocol (TCP) Internet Protocol (IP)/User Datagram Protocol (UDP) offload, is not supported on this interface.
More details can be found in the Installation and Configuration Guide for Cisco Services Ready Engine Virtualization, Release 2.0 at http://www.cisco.com/en/US/docs/interfaces_modules/services_modules/sre_v/2.0/user/guide/overview.html.
Logical Network Topology
Figure 9 illustrates the overall logical topology of the networking and video surveillance components, including a UCS Express containing the SRE-V running VSM, the Video Surveillance Operations Manager (VSOM), various IP cameras, an external switch, and the operator workstations running the VSOM client.
Figure 9 Logical Network Topology
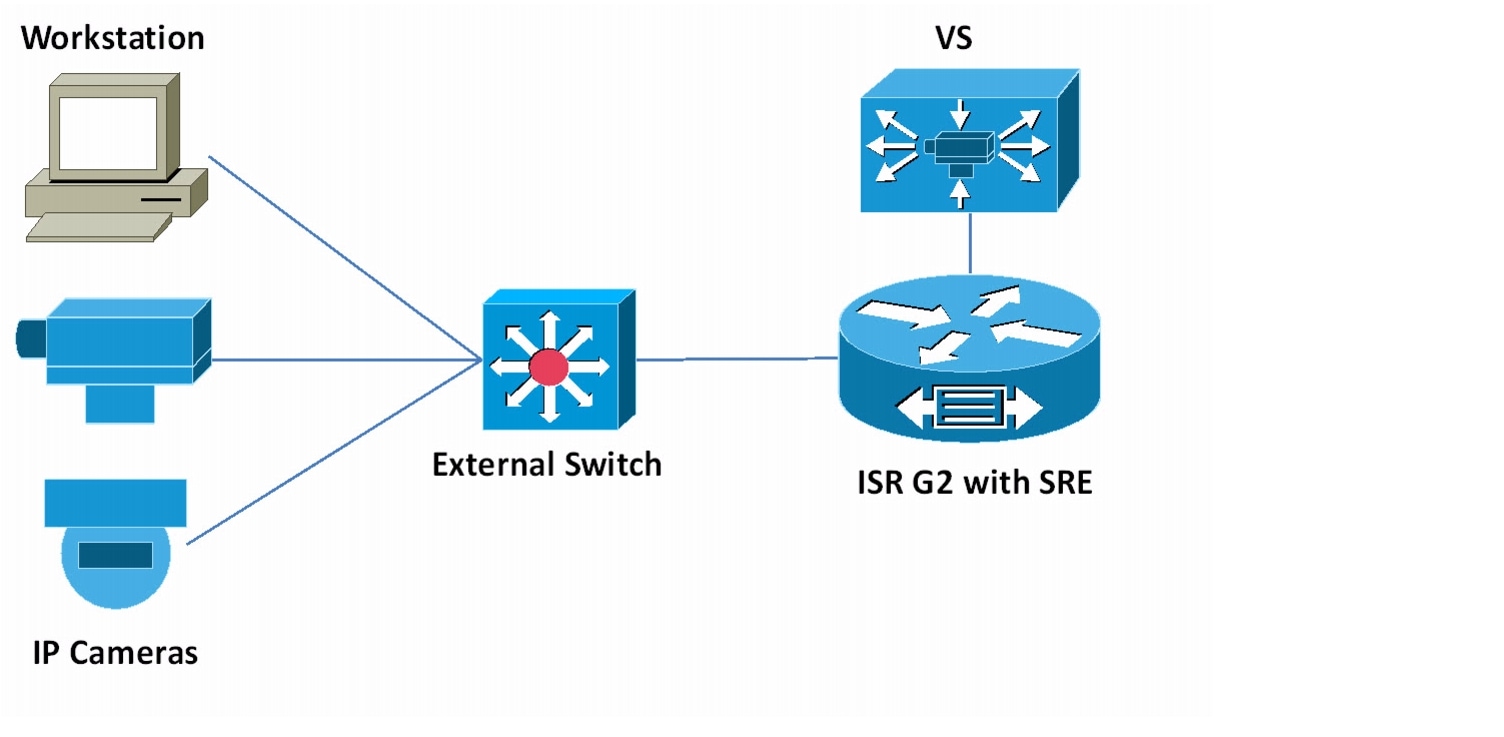

CautionThis deployment guide has been validated to operate within the specifications outlined in the Cisco Video Surveillance Manager for UCS Express Data Sheet ( http://www.cisco.com/en/US/prod/collateral/vpndevc/ps6918/ps9145/ps9152/data_sheet_c78-703863.html). See the data sheet on cisco.com for the latest guidelines, including maximum number of cameras, maximum I/O, and maximum raw storage.
Installing and Configuring the ISR Router and SRE
This guide describes the installation steps of configuring the ISR router and SRE, setting up the network interfaces, configuring hypervisor services and guest clients, and deploying and verifying the VSM VM.

Note
In the following configuration examples, it is assumed that:
•
SRE is inserted into Slot 1
•
10.10.1.0/24 is the management network
•
10.3.8.0/21 is the VSM network
•
VSM virtual LAN (VLAN) is 60
Verifying the IOS Image of the ISR
To verify the IOS image of the ISR:
Step 1
Log on to the router console and run the show version command to check the running version.
Step 2
Ensure that the ISR G2 is running 15.1(4)M, or a later version of IOS image.
If the router is running a version older than 15.1(4)M, then download and upgrade the IOS image to the correct version. To learn how to upgrade an IOS image, navigate to the Cisco web site at http://www.cisco.com/en/US/docs/net_mgmt/configuration_engine/3.0/administration/guide/upgrade.html.
Configuring the ISR Interface
To configure the ISR interface:
Step 1
Log on to the router console and view the running configuration with the show running-config command.
This command displays two interfaces, SM 1/0 and SM 1/1, assuming that the SRE blade is plugged into Service Module Slot 1. SM 1/0 is connected to the vSwitch0 vmKernel port of the Hypervisor, and SM 1/1 is connected to the vSwitch0 VM port group.
Step 2
Configure the router and hypervisor IP addresses by executing the following commands:
interface GigabitEthernet0/0description $ETH-LAN$$ETH-SW-LAUNCH$$INTF-INFO-GE 0/0$ip address 10.10.1.151 255.255.255.0interface SM1/0ip unnumbered GigabitEthernet0/0service-module ip address 10.10.1.152 255.255.255.0service-module ip default-gateway 10.10.1.151
Configuring the ISR VLANs
To configure the ISR VLANs:
Step 1
Configure the SM 1/1 connected to the Service Module as a trunk port:
interface SM1/1description Internal switch interface connected to Service Moduleswitchport mode trunkStep 2
Create sub-interfaces on the onboard router port to run 802.1q encapsulation for VLAN traffic, assign IP address for the sub-interfaces for VLAN routing, and create the VLANs:
interface GigabitEthernet0/1.60encapsulation dot1Q 60ip address 10.3.8.3 255.255.248.0vlan 60interface Vlan60description VSM VLANip unnumbered GigabitEthernet0/1.60Step 3
Create VLAN routes and a static route for the hypervisor:
ip route 10.10.1.152 255.255.255.255 SM1/0ip route 10.3.8.5 255.255.255.255 Vlan60
Verifying and Configuring the SRE Hypervisor
To verify and configure the SRE hypervisor:
Step 1
From the router console, session into the Service Module to verify that the hypervisor is running on the SRE blade.
Step 2
Assuming that the SRE is inserted into Slot 1 and the ESXi 5 hypervisor is installed and running on the blade, run the following command to session into the blade:
service-module sm 1/0 sessionStep 3
Verify that you are now logged on to the hypervisor user interface logon screen (Figure 10).
Figure 10 Hypervisor User Interface Screen
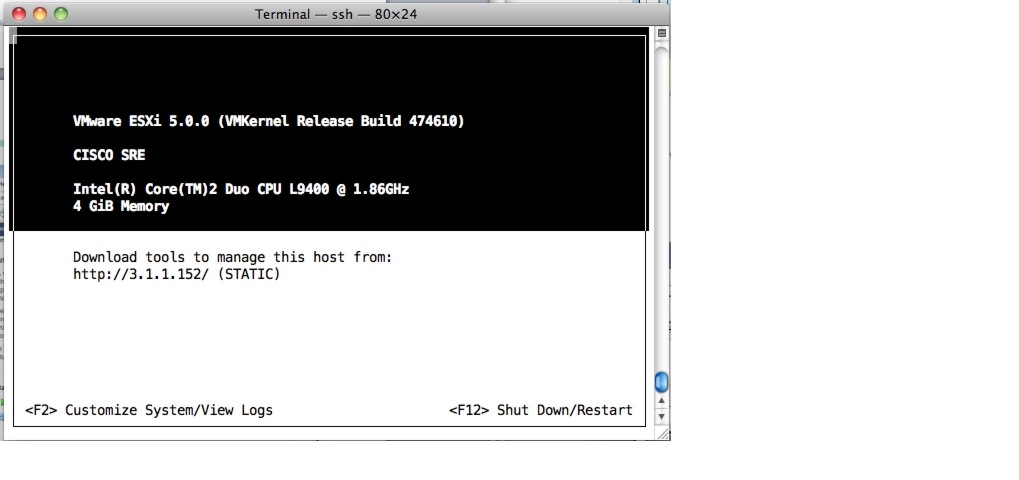
Step 4
Log on to the hypervisor with the root username and blank password.
Step 5
Press the F2 key to enter the Customize System mode and set the password.
Step 6
Navigate to Troubleshooting Options and enable SSH.
Step 7
Press the Esc key to save and exit this mode.
Step 8
Return to the IOS console or exit the session:
•
To return to the IOS console, press the Ctrl+Shift+6 sequence and then press x.
•
To exit the session, enter the following command:
service-module sm 1/0 session clear

Note
SRE-V comes with a 60-day trial license. A permanent license is required after 60 days. For details about licensing, see the Installation and Configuration Guide for Cisco Services Ready Engine Virtualization, Release 2.0 at http://www.cisco.com/en/US/docs/interfaces_modules/services_modules/sre_v/2.0/user/guide/license.html
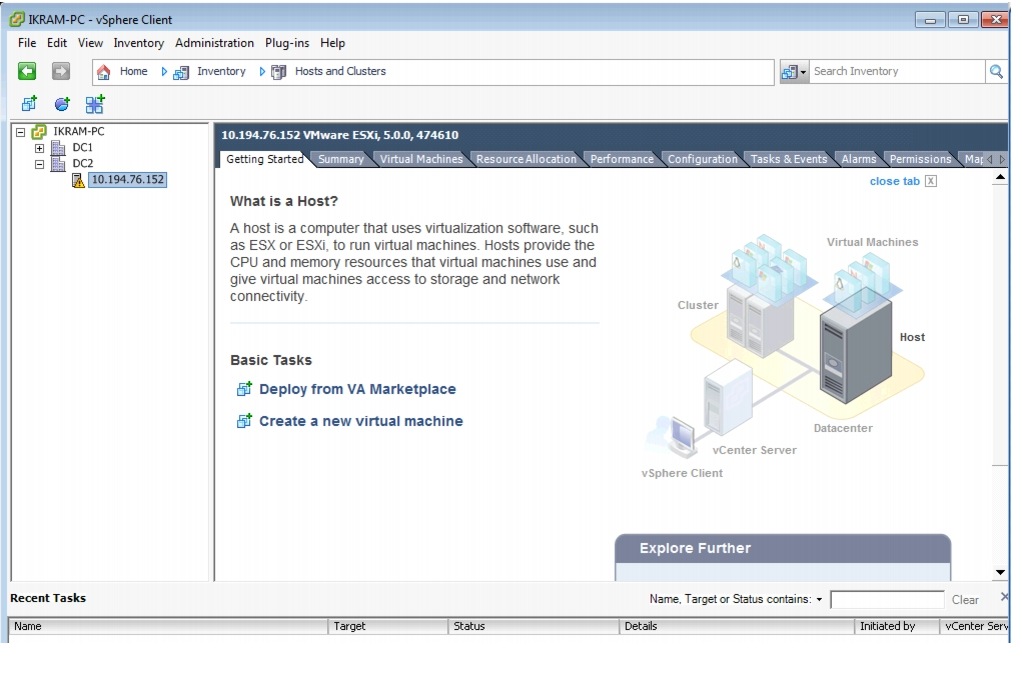
Installing the vSphere Client
To install the vSphere client:
Step 1
Open a web browser and enter the hypervisor URL (http://3.1.1.152/).
Step 2
Click the Download vSphere Client link to download the vSphere client to your computer.

Note
Internet connection is required to download the vSphere client. After the vSphere client is installed, launch the client (Figure 11) and enter the hypervisor's IP address and credentials to access the host.
Figure 11 vSphere Client Main Screen
Deploying the VSM 6.3.2 Template
To deploy the VSM 6.3.2 template:
Step 1
Download the VSM 6.3.2 template from the Cisco web page or insert a USB drive with the VSM template.
Step 2
Copy the template to the same computer on which the vSphere client was previously installed.

Note
The OVF Template is approximately 2.5 GB in size. Once deployed, the VM requires 20 GB of space (without including the space for the video partitions).
Step 3
Launch the vSphere client and connect to the hypervisor.
Step 4
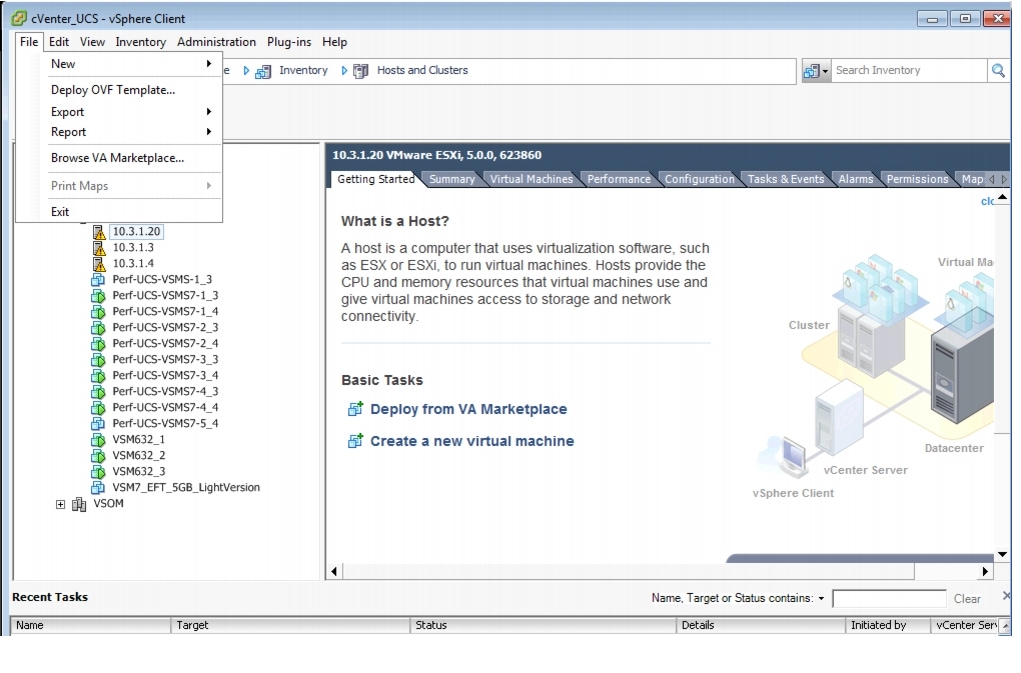
Click File > Deploy OVF Template to launch the OVF Deploy Template wizard (Figure 12).
Figure 12 Launching the Deploy OVF Template Wizard in the vSphere Client
Step 5
Follow the instructions in the wizard:
a.
Click Browse and either enter a URL to download, or specify a location and select the VSM template.
b.
Enter an appropriate name for this virtual machine.
c.
Complete the remaining steps by choosing all of the default options.
d.
Click Finish to begin deploying the VSM template.
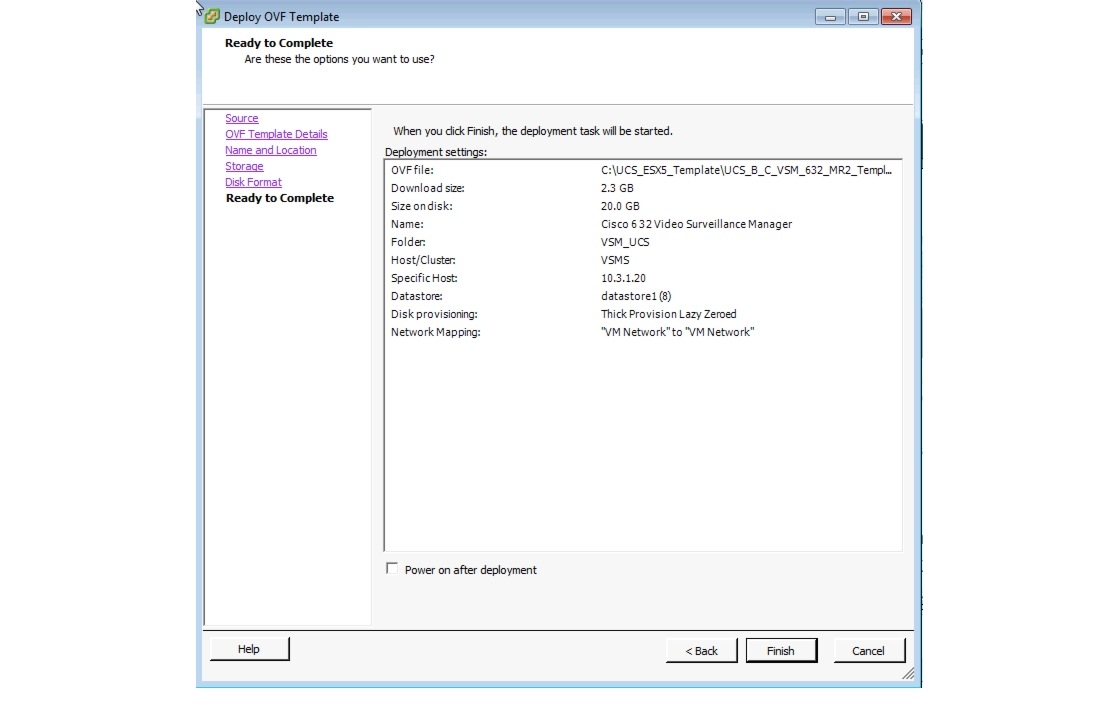
Figure 13 displays the result of those selected deployment settings.
Figure 13 Ready to Complete the OVF Wizard —VSM Template and Default Settings
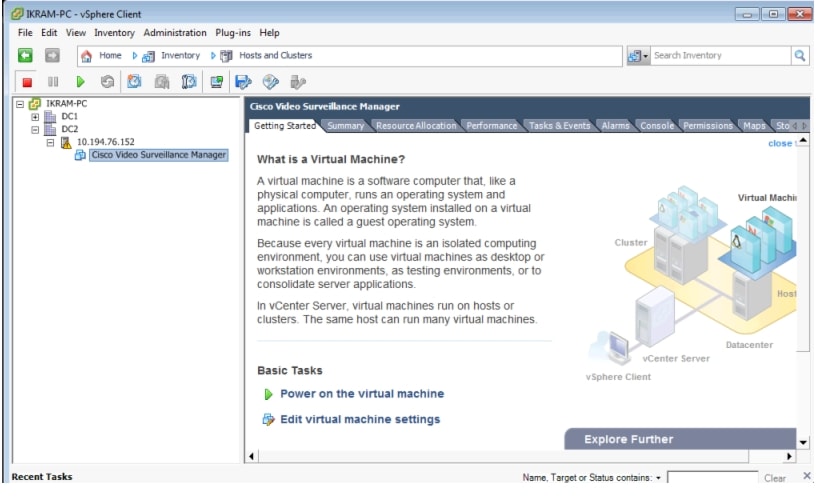
Once the VSM template is successfully deployed, the VSM VM displays under the hypervisor entry in the left-hand Inventory tree (Figure 14, left pane).
For more information about OVF Templates, see http://www.vmware.com/technical-resources/interfaces/ovf.html.

Note
The VSM VM size is 30 GB.
Figure 14 VSM VM Console in the vSphere Client
Creating New Media Hard Disks
The size of a new media hard disk is based on the redundant array of independent disks (RAID) configuration of the hypervisor. If the hypervisor is configured with a RAID 0 setting, then the usable disk size for the media partition is 860 GB; if using a RAID 1 setting, then the usable disk size is 400 GB. A RAID configuration is specified when the SRE module is ordered.

Note
Cisco assumes that the SRE comes with RAID configured. If it is not configured, or if the RAID configuration must be modified, then follow the instructions in the SRE configuration guide listed in the reference section.
To create a new media hard disk for the VSM VM:
Step 1
Launch the vSphere client and connect to the vCenter server (see Figure 11).
Step 2
In the left pane (Inventory tree), right-click the hypervisor's name and select Edit Settings (Figure 15) to launch the Virtual Machine Properties—Hardware Tab settings (Figure 16).
Figure 15 vCenter UCS, vSphere Client—Edit Settings
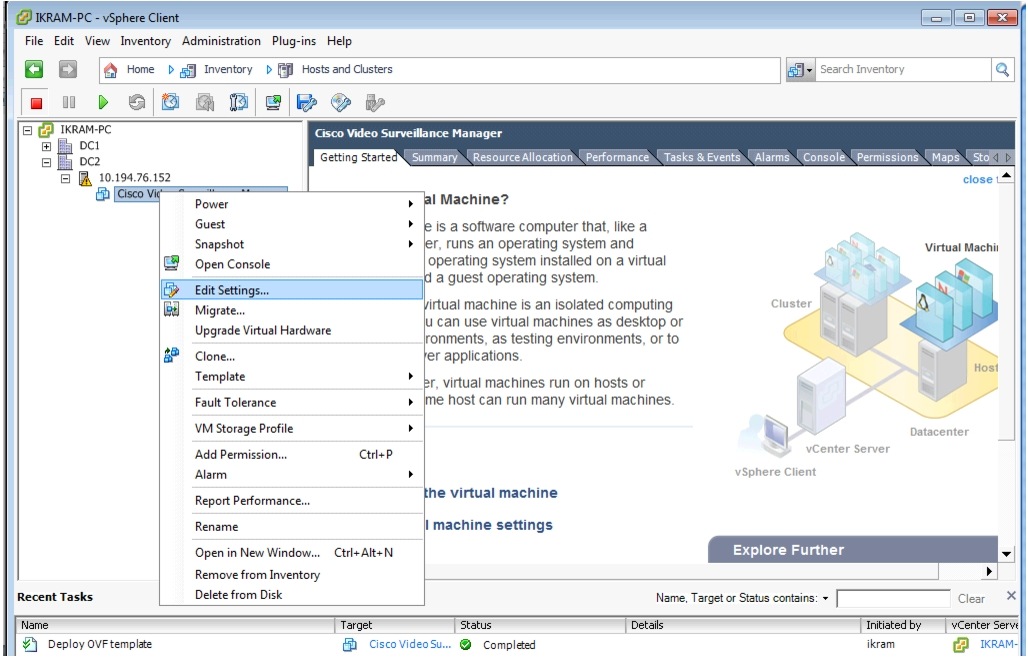
Figure 16 Virtual Machine Properties—Hardware Tab Settings
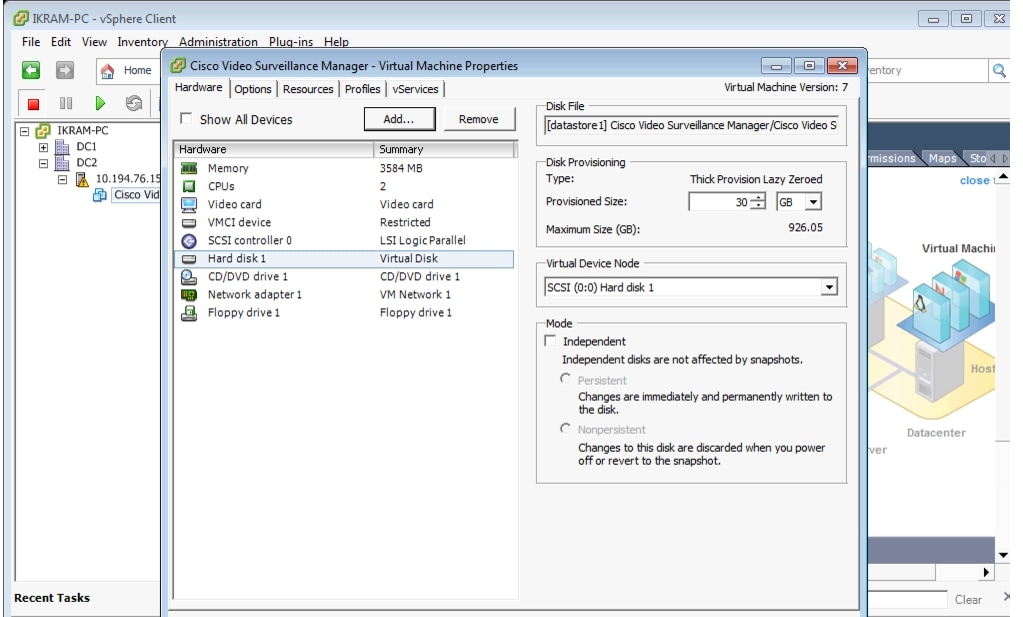
Step 3
Select Hard disk n and note the Disk Provisioning sizes (Maximum Size and Provisioned Size).
Step 4
Click Add to display the Add Hardware screen (Figure 17).
Figure 17 Selecting a Hard Disk
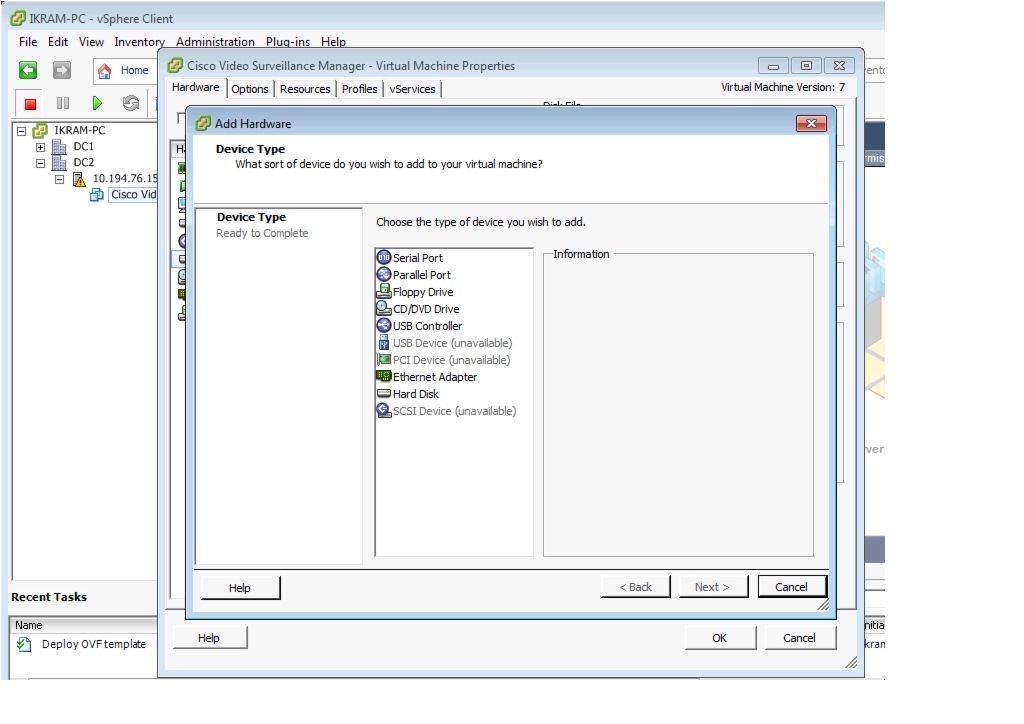
Step 5
From the device type list, select Hard Disk and click Next to display the next screen.
Step 6
Select the default options for adding the new hard disk and proceed to the final screen (Figure 18).
Figure 18 Summary of New Hard Disk Options
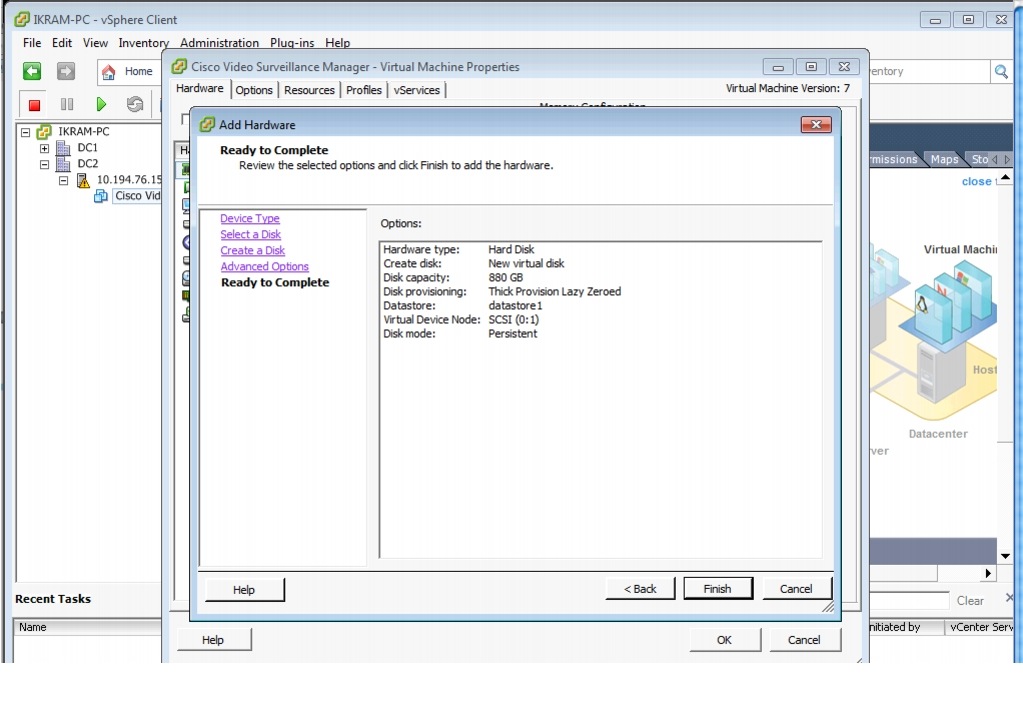
Step 7
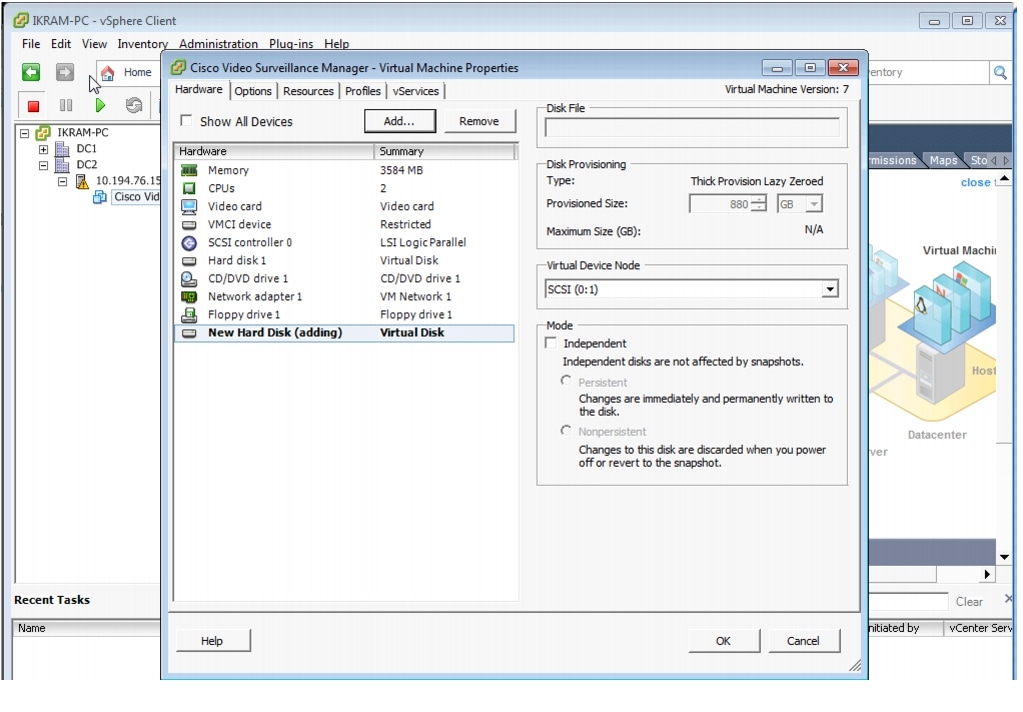
Click Finish to return to the Virtual Machine Properties (Figure 16) and view the newly created hard disk.
Step 8
Click OK (Figure 19) to accept the new hard disk and to complete the procedure.
Figure 19 Ready to Add New Hard Disk to VSM VM
Configuring Network Switches for the VSM VM
To set up the networking configuration for the VSM VM:
Step 1
Launch the vSphere client and connect to the vCenter server (see Figure 11).
Step 2
In the left pane (Inventory tree), click the hypervisor's name > click the Configuration tab.
Step 3
In the Hardware section, click Networking (Figure 20).
Figure 20 VM Switch Networking Properties—vSphere Client
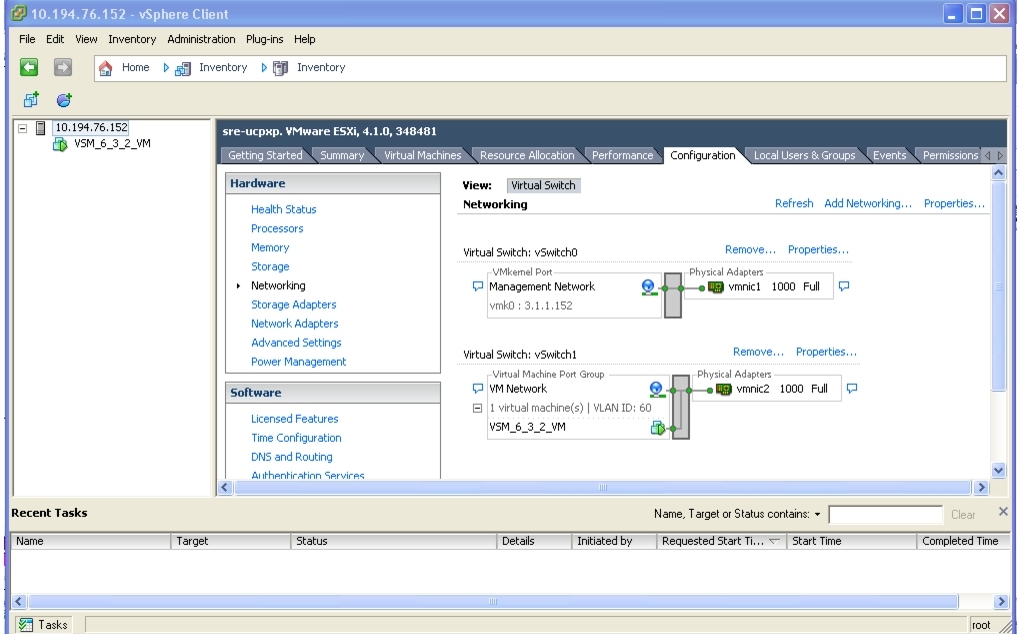
The defaults, Virtual Switch: vSwitch 0 and Virtual Switch: vSwitch1, display.
Step 4
Click Properties to configure the virtual switch's properties (Figure 21).
Figure 21 VM Switch1 Networking Properties—vSphere Client
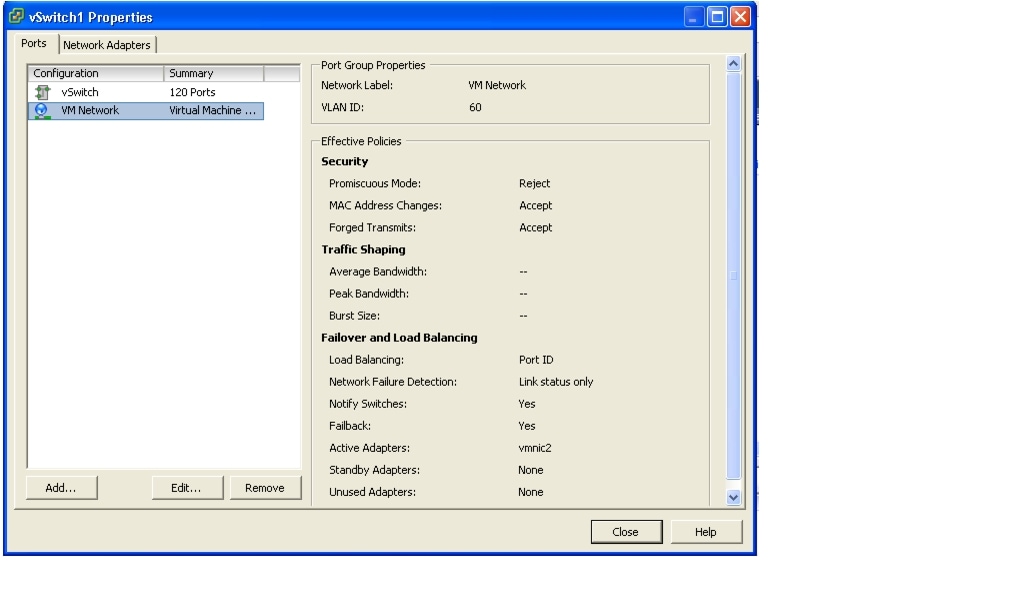
Step 5
Select VM Network and click Edit.
Step 6
Optional. Change the VLAN ID to the VSM VLAN (for example, 60) (Figure 22).
Figure 22 VM Networking Properties—vSphere Client
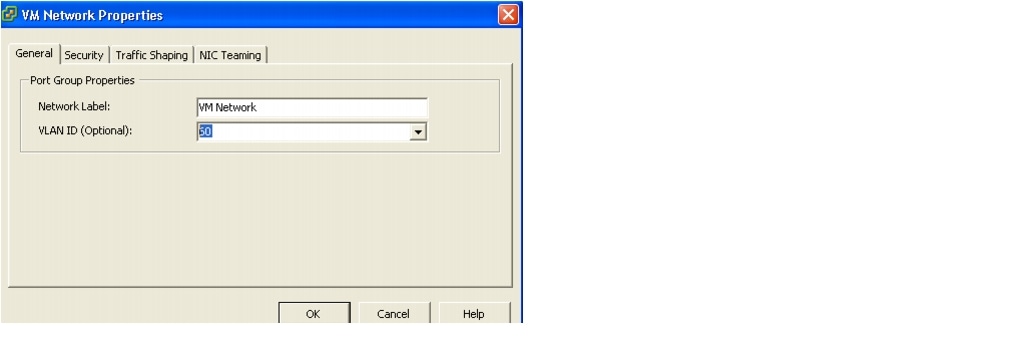
Step 7
Click OK to complete the network configuration.
Configuring NTP

Note
We recommend that you use the Network Time Protocol (NTP) source to maintain the correct time on the server. Configuring NTP should be done before configuring the video. The clock should be set to use Coordinated Universal Time (UTC) and the appropriate time zone for the server.
To set up the NTP configuration for the VSM VM:
Step 1
Launch the vSphere client and connect to the vCenter server.
Step 2
In the left pane (Inventory tree), click the hypervisor's name.
Step 3
Click the Configuration tab, and in the Software area (Figure 23), click Time Configuration.
Figure 23 Time Configuration Properties—NTP Settings
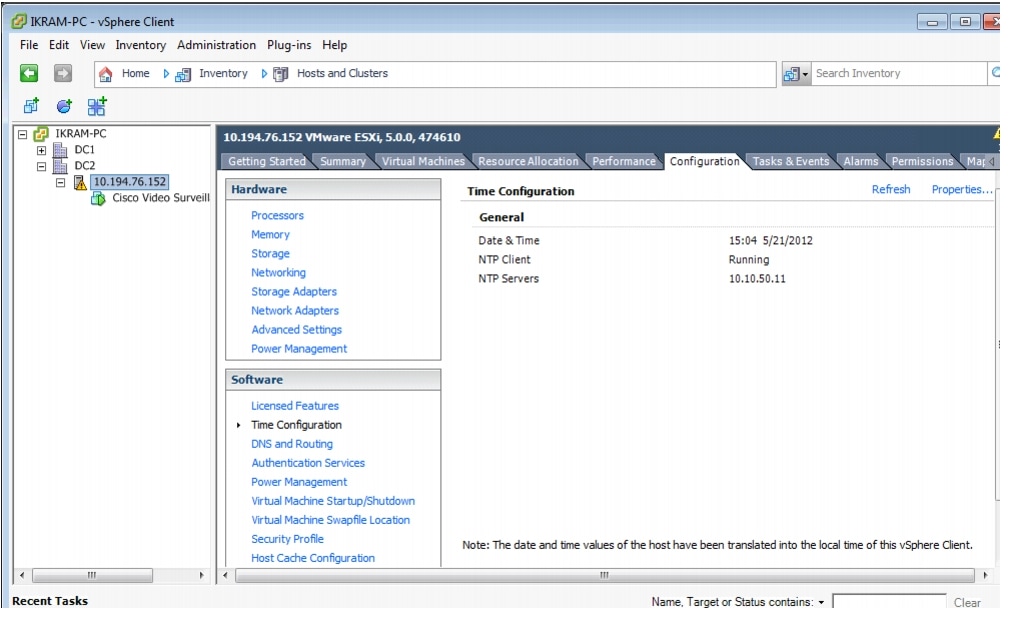
Step 4
Click Properties to configure the NTP settings.
Step 5
Check the NTP Client Enabled check box and click Options to add NTP server address (Figure 24 and Figure 25).
Figure 24 Time Configuration—General Properties
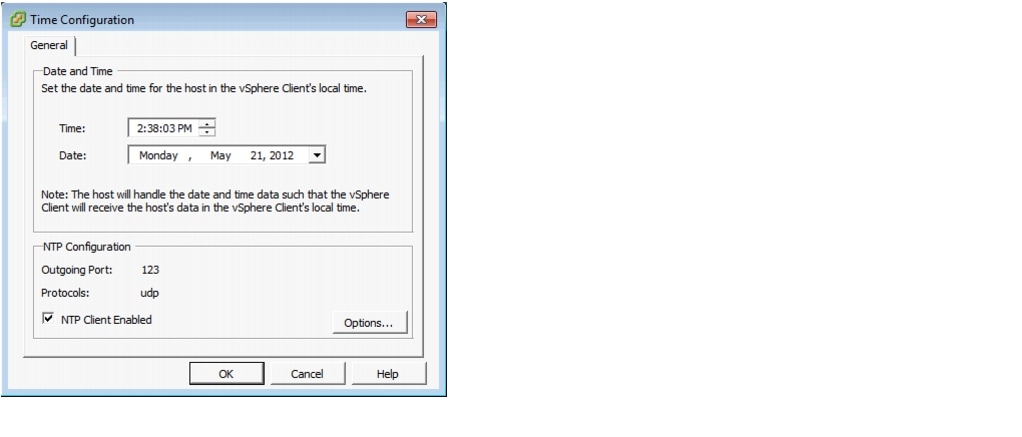
Figure 25 NTP Daemon Options
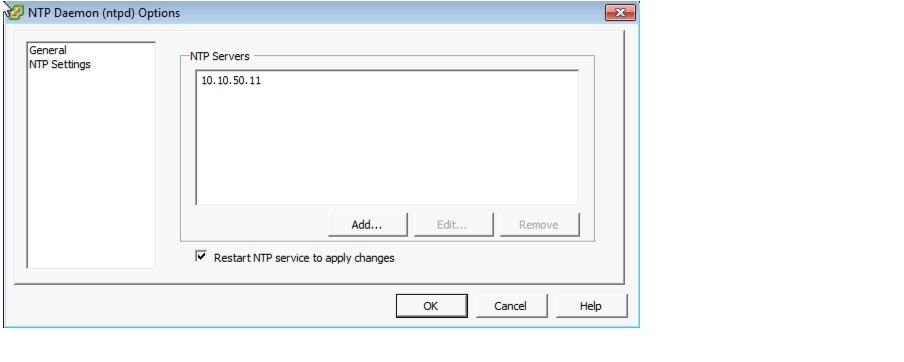
Step 6
Click OK to complete the NTP configuration for the hypervisor.

Note
To set up the NTP configuration on the VSM VM running SUSE, use Yet Another Setup Tool (YaST) to configure the NTP source and server time.
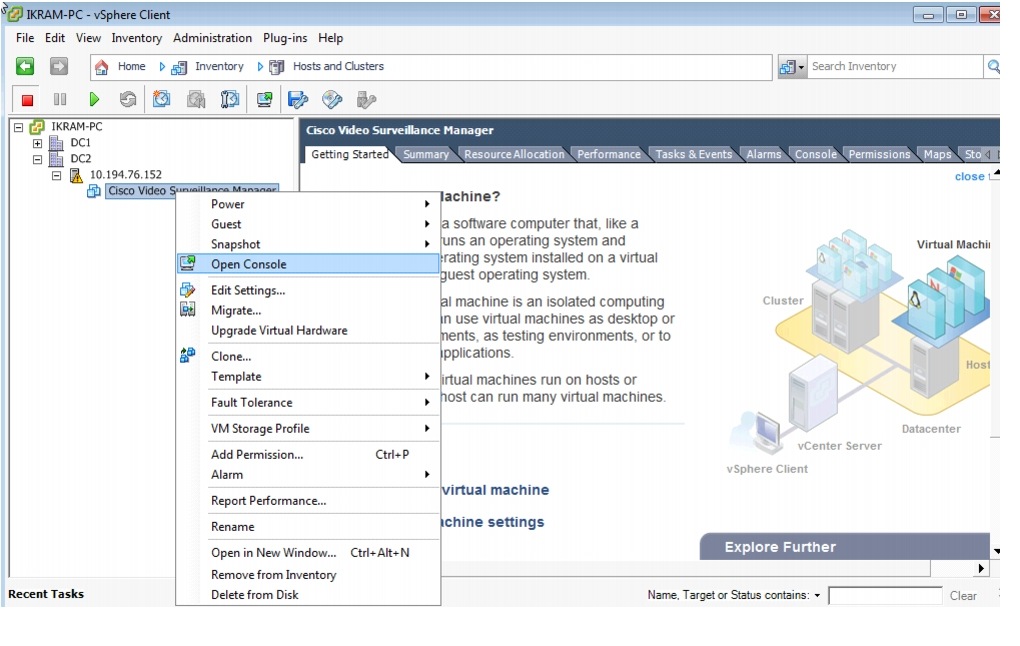
Launching the VSM VM
To launch the VSM VM:
Step 1
In the left pane (Inventory tree) of the vCenter_UCS-vSphere client, right-click the VSM VM name and select Open Console (Figure 26) to launch the VM console.
Figure 26 Opening the VSM VM Console
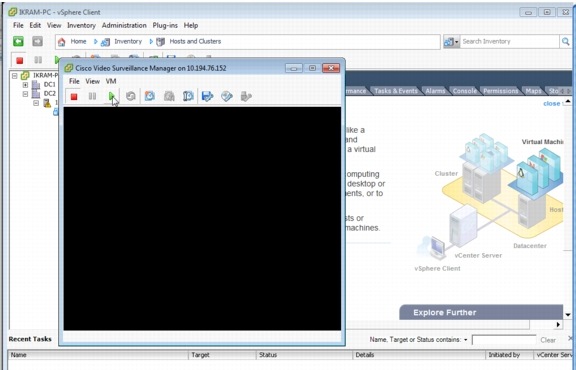
Step 2
On the console toolbar, click the green arrow (Figure 27).
Figure 27 Launching the VSM VM Console
Configuring the VSM VM
To configure the VSM VM:
Step 1
Open the VSM VM console and log on to VSM with either your specific authentication or the standard default username of root and the secur4u password.
Step 2
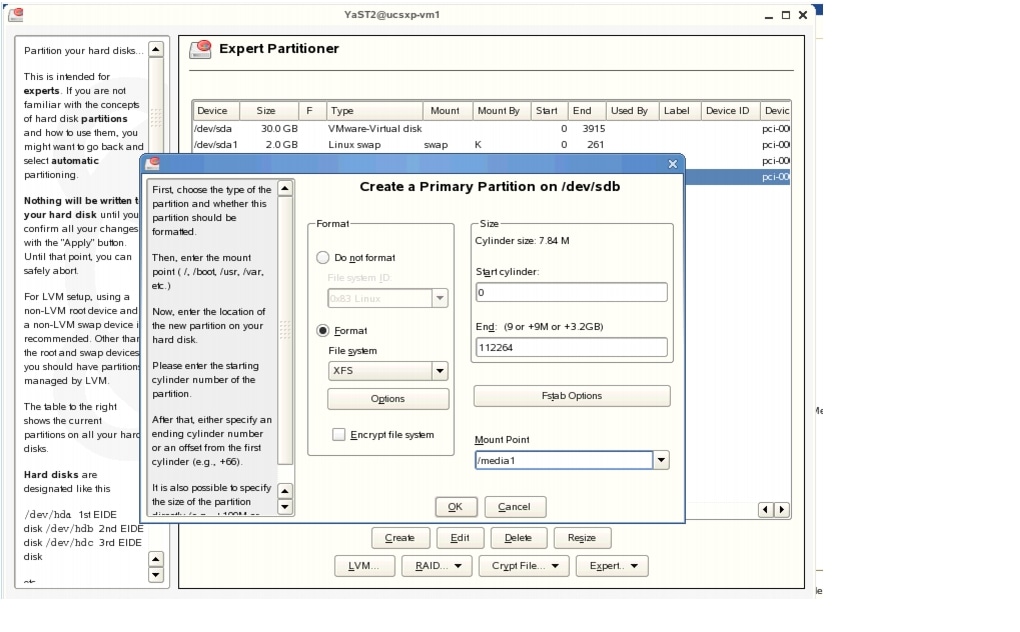
Launch the Yet another Software Tool (YaST) partitioner utility to add the new media partition (Figure 28, Figure 29, Figure 30, Figure 31).
Figure 28 Creating a New Media Partition in YaST
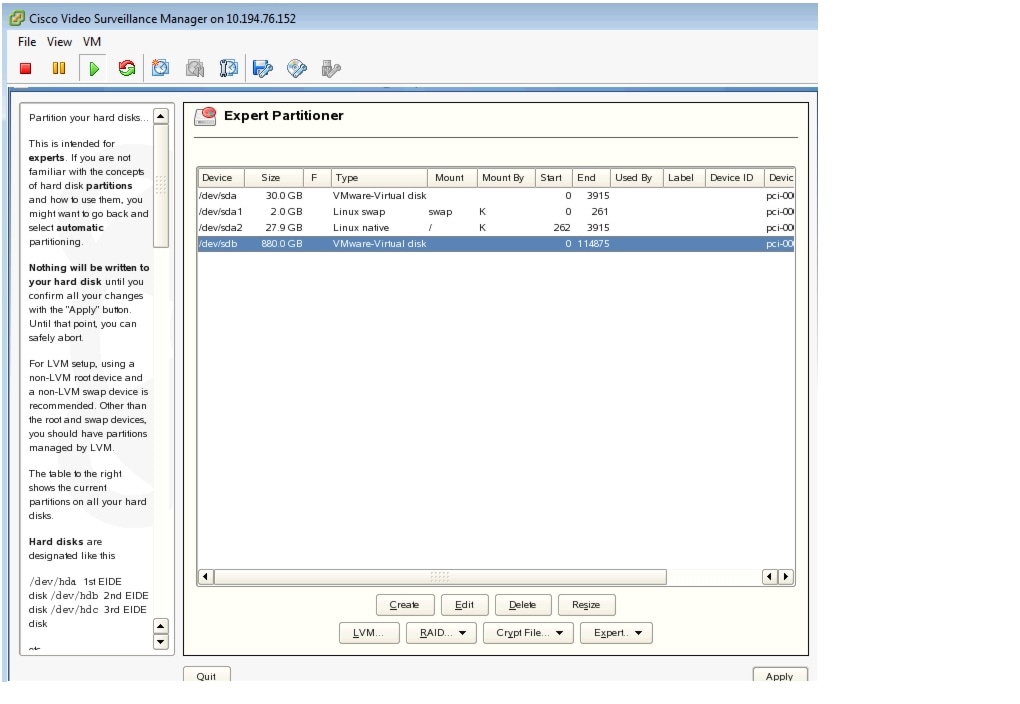
Figure 29 Selecting the Disk Device to Partition in YaST
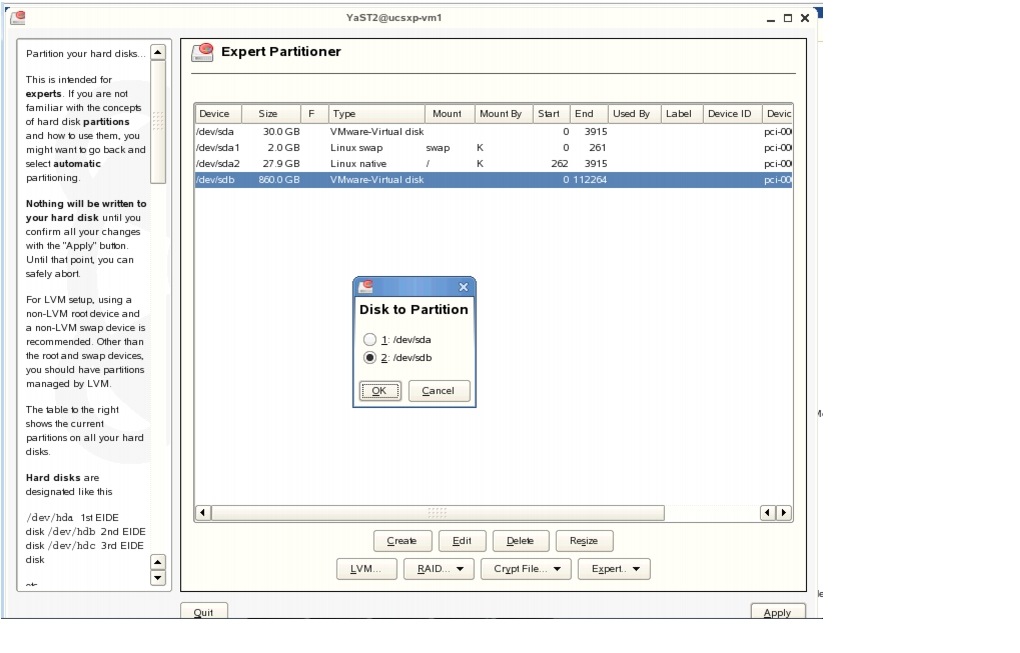
Figure 30 Selecting Partition Type in YaST
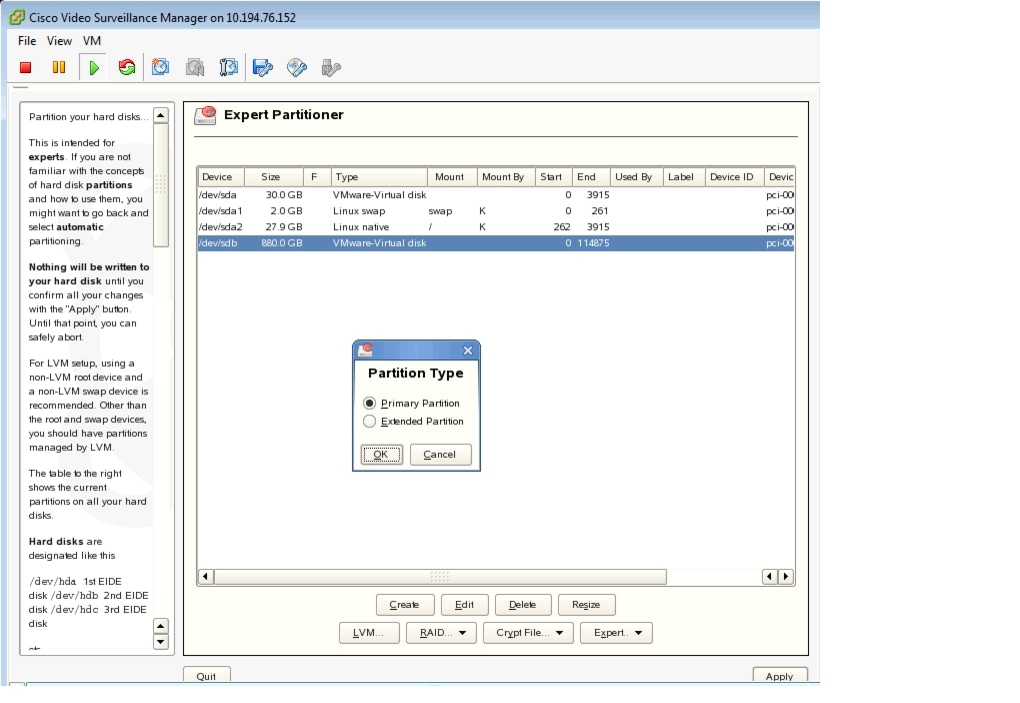
Figure 31 Using XFS Format—Choose Partition Size and Name the Mount Point in YaST
Step 3
After successfully creating the partition, change ownership of partition to the nobody account and group with the chown nobody:nobody /media1 command.
Step 4
Reboot the VSM VM: log off and select Reboot.
Step 5
After the VM reboots, open the Video Surveillance Management Console (VSMC) page from the browser and configure the Media Server options to set the /media1 partition for storing archives and video clip data.

Note
Remember to finish all of the remaining VSM administration and configuration tasks. For information about VSM Install and User Guides, refer to the "More Information" section.
Testing Network Connectivity
To verify that network connectivity is working properly between endpoints, including IP cameras and VSOM operator workstations:
Step 1
Log on to the VSM server and ensure that all Cisco services are running and operational.
Step 2
Navigate to the VSMC page and from the Status Console, verify the status of the Cisco services.
More Information
For more information about Cisco-related products, see the following resources:
•
Cisco Physical Security and Building Systems:
http://www.cisco.com/go/physec/•
Cisco UCS Express (SRE-V) Install and Upgrade Guides:
http://www.cisco.com/en/US/products/ps11273/prod_installation_guides_list.html•
Cisco Video Surveillance Media Server Software—Install and Upgrade Guides: http://www.cisco.com/en/US/products/ps9152/prod_installation_guides_list.html
•
Installing and Configuring VMware Tools: http://www.vmware.com/pdf/vmware-tools-installation-configuration.pdf
•
Cisco Configuration Engine Administration Guide—Upgrade or Downgrade an IOS Image
http://www.cisco.com/en/US/docs/net_mgmt/configuration_engine/3.0/administration/guide/upgrade.html•
Installation and Configuration Guide for Cisco Services Ready Engine Virtualization, Release 2.0
http://www.cisco.com/en/US/docs/interfaces_modules/services_modules/sre_v/2.0/user/guide/overview.html
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback