Authentication Types for Wireless Devices
Available Languages
Table Of Contents
Authentication Types for Wireless Devices
Understanding Authentication Types
Open Authentication to the Access Point
Shared Key Authentication to the Access Point
EAP Authentication to the Network
MAC Address Authentication to the Network
Combining MAC-Based, EAP, and Open Authentication
Using CCKM for Authenticated Clients
Configuring Authentication Types
Assigning Authentication Types to an SSID
Configuring WPA Migration Mode
Configuring Additional WPA Settings
Configuring MAC Authentication Caching
Configuring Authentication Holdoffs, Timeouts, and Intervals
Configuring the 802.1X Supplicant
Creating a Credentials Profile
Applying the Credentials to an Interface or SSID
Applying the Credentials Profile to the Wired Port
Applying the Credentials Profile to an SSID Used for the Uplink
Creating and Applying EAP Method Profiles for the 802.1X Supplicant
Creating an EAP Method Profile
Applying an EAP Profile to the Fast Ethernet Interface
Applying an EAP Profile to an Uplink SSID
Matching Access Point and Client Device Authentication Types
Authentication Types for Wireless Devices
This module describes how to configure authentication types for wireless devices in the following sections:
•
Understanding Authentication Types
•
Configuring Authentication Types
•
Matching Access Point and Client Device Authentication Types
Understanding Authentication Types
This section describes the authentication types that are configured on the access point. Authentication types are tied to the Service Set Identifiers (SSIDs) that are configured for the access point. If you want to serve different types of client devices with the same access point, configure multiple SSIDs..
Before a wireless client device can communicate on your network through the access point, it must authenticate to the access point by using open or shared-key authentication. For maximum security, client devices should also authenticate to your network using MAC-address or Extensible Authentication Protocol (EAP) authentication. Both of these authentication types rely on an authentication server on your network.

Note
By default, the access point sends reauthentication requests to the authentication server with the service-type attribute set to authenticate-only. However, some Microsoft IAS servers do not support the authenticate-only service-type attribute. Changing the service-type attribute to login-only ensures that Microsoft IAS servers recognize reauthentication requests from the access point. Use the dot11 aaa authentication attributes service-type login-only global configuration command to set the service-type attribute in reauthentication requests to login-only.
The access point uses several authentication mechanisms or types and can use more than one at the same time. These sections explain each authentication type:
•
Open Authentication to the Access Point
•
Shared Key Authentication to the Access Point
•
EAP Authentication to the Network
•
MAC Address Authentication to the Network
•
Combining MAC-Based, EAP, and Open Authentication
•
Using CCKM for Authenticated Clients
Open Authentication to the Access Point
Open authentication allows any device to authenticate and then attempt to communicate with the access point. Using open authentication, any wireless device can authenticate with the access point, but the device can communicate only if its Wired Equivalent Privacy (WEP) keys match the access point's WEP keys. Devices that are not using WEP do not attempt to authenticate with an access point that is using WEP. Open authentication does not rely on a RADIUS server on your network.
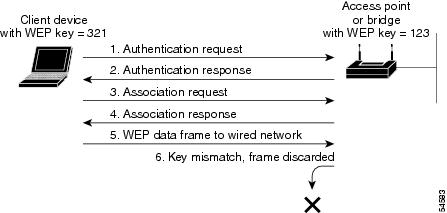
Figure 1 shows the authentication sequence between a device trying to authenticate and an access point using open authentication. In this example, the device's WEP key does not match the access point's key. Therefore, the device can authenticate but not pass data.
Figure 1 Sequence for Open Authentication
Shared Key Authentication to the Access Point
Cisco provides shared key authentication to comply with the IEEE 802.11b standard. However, because of shared key authentication's security flaws, we recommend that you avoid using it.
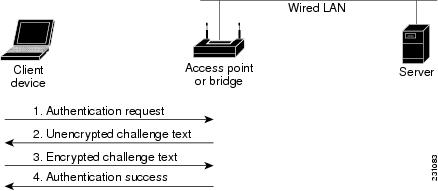
During shared key authentication, the access point sends an unencrypted challenge text string to any device that is attempting to communicate with the access point. The device that is requesting authentication encrypts the challenge text and sends it back to the access point. If the challenge text is encrypted correctly, the access point allows the requesting device to authenticate.
Both the unencrypted challenge and the encrypted challenge can be monitored, however, which leaves the access point open to attack from an intruder who calculates the WEP key by comparing the unencrypted and encrypted text strings. Because of this vulnerability to attack, shared key authentication can be less secure than open authentication. Like open authentication, shared key authentication does not rely on a RADIUS server on your network.
Figure 2 shows the authentication sequence between a device that is trying to authenticate and an access point that is using shared key authentication. In this example, the device's WEP key matches the access point's key, so the device can authenticate and communicate.
Figure 2 Sequence for Shared Key Authentication
EAP Authentication to the Network
This authentication type provides the highest level of security for your wireless network. By using the Extensible Authentication Protocol (EAP) to interact with an EAP-compatible RADIUS server, the access point helps a wireless client device and the RADIUS server to perform mutual authentication and derive a dynamic unicast WEP key. The RADIUS server sends the WEP key to the access point, which uses the key for all unicast data signals that the server sends to or receives from the client. The access point also encrypts its broadcast WEP key (which is entered in the access point's WEP key slot 1) with the client's unicast key and sends it to the client.
When you enable EAP on your access points and client devices, authentication to the network occurs in the sequence shown in Figure 3.
Figure 3 Sequence for EAP Authentication
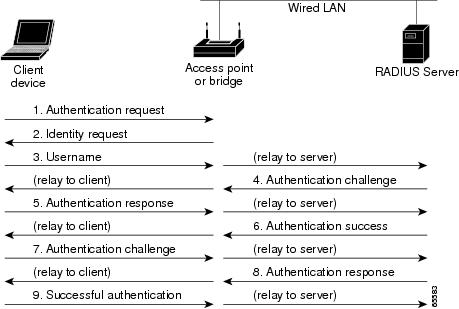
In Step 1 through Step 9 in Figure 3, a wireless client device and a RADIUS server on the wired LAN use 802.1x and EAP to perform a mutual authentication through the access point. The RADIUS server sends an authentication challenge to the client. The client uses a one-way encryption of the user-supplied password to generate a response to the challenge and sends that response to the RADIUS server. Using information from its user database, the RADIUS server creates its own response and compares that to the response from the client. When the RADIUS server authenticates the client, the process repeats in reverse, and the client authenticates the RADIUS server.
When mutual authentication is complete, the RADIUS server and the client determine a WEP key that is unique to the client and that provides the client with the appropriate level of network access, thereby approximating the level of security in a wired switched segment to an individual desktop. The client loads this key and prepares to use it for the logon session.
During the logon session, the RADIUS server encrypts and sends the WEP key, called a session key, over the wired LAN to the access point. The access point encrypts its broadcast key with the session key and sends the encrypted broadcast key to the client, which uses the session key to decrypt it. The client and access point activate WEP and use the session and broadcast WEP keys for all communications during the remainder of the session.
There is more than one type of EAP authentication, but the access point behaves the same way for each type: it relays authentication messages from the wireless client device to the RADIUS server and from the RADIUS server to the wireless client device. See the "Assigning Authentication Types to an SSID" section for instructions on setting up EAP on the access point.

Note
If you use EAP authentication, you can select open or shared key authentication, but you do not have to make a selection. EAP authentication controls authentication both to your access point and to your network.
MAC Address Authentication to the Network
The access point relays the wireless client device's MAC address to a RADIUS server on your network, and the server checks the address against a list of allowed MAC addresses. Because intruders can create counterfeit MAC addresses, MAC-based authentication is less secure than EAP authentication. However, MAC-based authentication provides an alternate authentication method for client devices that do not have EAP capability. See the "Assigning Authentication Types to an SSID" section for instructions on enabling MAC-based authentication.

Tip
If you don't have a RADIUS server on your network, you can create a list of allowed MAC addresses on the access point's Advanced Security: MAC Address Authentication page. Devices with MAC addresses not on the list are not allowed to authenticate.

Tip
If MAC-authenticated clients on your wireless LAN roam frequently, you can enable a MAC authentication cache on your access points. MAC authentication caching reduces overhead because the access point authenticates devices in its MAC-address cache without sending the request to your authentication server. See the "Configuring MAC Authentication Caching" section for instructions on enabling this feature.
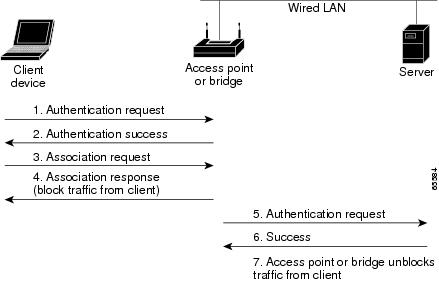
Figure 4 shows the authentication sequence for MAC-based authentication.
Figure 4 Sequence for MAC-Based Authentication
Combining MAC-Based, EAP, and Open Authentication
You can set up the access point to authenticate client devices that use a combination of MAC-based and EAP authentication. When you enable this feature, client devices that use 802.11 open authentication to associate to the access point first attempt MAC authentication. If MAC authentication succeeds, the client device joins the network.
If MAC authentication fails, EAP authentication takes place. See the "Assigning Authentication Types to an SSID" section for instructions on setting up this combination of authentications.
Using CCKM for Authenticated Clients
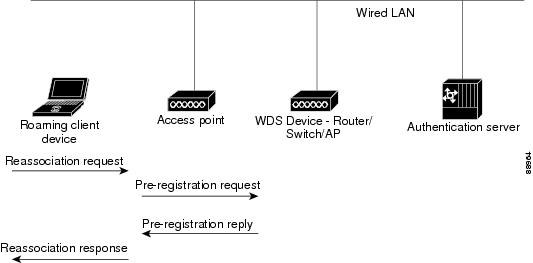
Using Cisco Centralized Key Management (CCKM), authenticated client devices can roam from one access point to another without any perceptible delay during reassociation. An access point on your network provides Wireless Domain Services (WDS) and creates a cache of security credentials for CCKM-enabled client devices on the subnet.
The WDS access point's cache of credentials dramatically reduces the time required for reassociation when a CCKM-enabled client device roams to a new access point. When a client device roams, the WDS access point forwards the client's security credentials to the new access point, and the reassociation process is reduced to a two-packet exchange between the roaming client and the new access point. Roaming clients reassociate so quickly that there is no perceptible delay in voice or other time-sensitive applications. See the "Assigning Authentication Types to an SSID" section for instructions on enabling CCKM on your access point. The RADIUS-assigned VLAN feature is not supported for client devices that associate using SSIDs with CCKM enabled.
Figure 5 shows the reassociation process using CCKM.
Figure 5 Client Reassociation Using CCKM
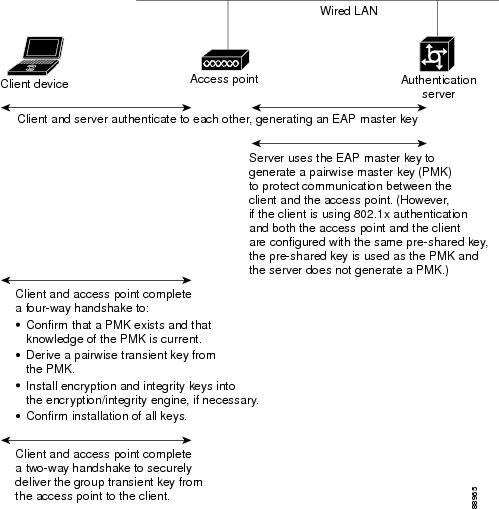
Using WPA Key Management
Wi-Fi Protected Access (WPA) is a standards-based, interoperable security enhancement that strongly increases the level of data protection and access control for existing and future wireless LAN systems. It is derived from and will be forward-compatible with the upcoming IEEE 802.11i standard. WPA leverages TKIP (Temporal Key Integrity Protocol) for data protection and 802.1X for authenticated key management.
WPA key management supports two mutually exclusive management types: WPA and WPA-Pre-shared key (WPA-PSK). Using WPA key management, clients and the authentication server authenticate to each other using an EAP authentication method, and the client and server generate a pairwise master key (PMK). Using WPA, the server generates the PMK dynamically and passes it to the access point. Using WPA-PSK, however, you configure a pre-shared key on both the client and the access point, and that pre-shared key is used as the PMK.

Note
Unicast and multicast cipher suites advertised in WPA information element (and negotiated during 802.11 association) may potentially mismatch with the cipher suite supported in an explicitly assigned VLAN. If the RADIUS server assigns a new VLAN ID which uses a cipher suite that is different from the previously negotiated cipher suite, there is no way for the access point and client to switch back to the new cipher suite. Currently, the WPA and CCKM protocols do not allow the cipher suite to be changed after the initial 802.11 cipher-negotiation phase. In this scenario, the client device is disassociated from the wireless LAN.
See the "Assigning Authentication Types to an SSID" section for instructions on configuring WPA key management on your access point.
Figure 6 shows the WPA key management process.
Figure 6 WPA Key Management Process
Configuring Authentication Types
This section describes how to configure authentication types. You attach configuration types to the Service Set Identifiers (SSIDs). This section contains these topics:
•
Assigning Authentication Types to an SSID
•
Configuring Authentication Holdoffs, Timeouts, and Intervals
•
Creating and Applying EAP Method Profiles for the 802.1X Supplicant

Note
There are no default authentication SSIDs for the wireless router.
Assigning Authentication Types to an SSID
To configure authentication types for SSIDs, follow these steps, beginning in privileged EXEC mode:
Step 1
configure terminal
Enters global configuration mode.
Step 2
dot11 ssid ssid-string
Creates an SSID and enters SSID configuration mode for the new SSID.
The SSID can consist of up to 32 alphanumeric characters. SSIDs are case sensitive.
The first character cannot contain the following characters:
•
Exclamation point (!)
•
Pound sign (#)
•
Semicolon (;)
The following characters are invalid and cannot be used in an SSID:
•
Plus sign (+)
•
Right bracket (])
•
Front slash (/)
•
Quotation mark (")
•
Tab
•
Trailing spaces
Step 3
authentication open
[mac-address list-name [alternate]]
[[optional] eap list-name](Optional) Sets the authentication type to open for this SSID. Open authentication allows any device to authenticate and then attempt to communicate with the access point.
•
(Optional) Set the SSID's authentication type to open with MAC address authentication. The access point forces all client devices to perform MAC-address authentication before they are allowed to join the network. For list-name, specify the authentication method list. Click this link for more information on method lists: http://www.cisco.com/en/US/docs/ios/12_2/security/configuration/guide/scfathen.html
Use the alternate keyword to allow client devices to join the network using either MAC or EAP authentication. Clients that successfully complete either type of authentication are allowed to join the network.
•
(Optional) Set the SSID's authentication type to open with EAP authentication. The access point forces all client devices to perform EAP authentication before they are allowed to join the network. For list-name, specify the authentication method list.
Use the optional keyword to allow client devices using either open or EAP authentication to associate and become authenticated. This setting is used mainly by service providers that require special client accessibility.
Note
An access point configured for EAP authentication forces all client devices that associate to perform EAP authentication. Client devices that do not use EAP cannot use the access point.
Step 4
authentication shared
[mac-address list-name]
[eap list-name](Optional) Sets the authentication type for the SSID to shared key.
Note
Because of shared key's security flaws, we recommend that you avoid using it.
Note
You can assign shared key authentication to only one SSID.
•
(Optional) Set the SSID's authentication type to shared key with MAC address authentication. For list-name, specify the authentication method list.
•
(Optional) Set the SSID's authentication type to shared key with EAP authentication. For list-name, specify the authentication method list.
Step 5
authentication network-eap list-name
[mac-address list-name](Optional) Sets the authentication type for the SSID to Network-EAP. Using the Extensible Authentication Protocol (EAP) to interact with an EAP-compatible RADIUS server, the access point helps a wireless client device and the RADIUS server to perform mutual authentication and derive a dynamic unicast WEP key. However, the access point does not force all client devices to perform EAP authentication.
•
(Optional) Set the SSID's authentication type to Network-EAP with MAC address authentication. All client devices that associate to the access point are required to perform MAC-address authentication. For list-name, specify the authentication method list.
Step 6
authentication key-management {[wpa] [cckm]} [optional]
(Optional) Sets the authentication type for the SSID to WPA, CCKM, or both. If you use the optional keyword, client devices other than WPA and CCKM clients can use this SSID. If you do not use the optional keyword, only WPA or CCKM client devices are allowed to use the SSID.
To enable CCKM for an SSID, you must also enable Network-EAP authentication. When CCKM and Network EAP are enabled for an SSID, client devices using LEAP1 , EAP-FAST2 , PEAP/GTC3 , MSPEAP4 , and EAP-TLS5 can authenticate using the SSID.
To enable WPA for an SSID, you must also enable Open authentication or Network-EAP or both.
Note
When you enable both WPA and CCKM for an SSID, you must enter wpa first and cckm second. Any WPA client can attempt to authenticate, but only CCKM voice clients can attempt to authenticate.
Note
Before you can enable CCKM or WPA, you must set the encryption mode for the SSID's VLAN to one of the cipher suite options. To enable both CCKM and WPA, you must set the encryption mode to a cipher suite that includes TKIP. See the Cipher Suites and WEP module module on Cisco.com for instructions on configuring the VLAN encryption mode.
Note
If you enable WPA for an SSID without a pre-shared key, the key management type is WPA. If you enable WPA with a pre-shared key, the key management type is WPA-PSK. See the "Configuring Additional WPA Settings" section for instructions on configuring a pre-shared key.
Step 7
end
Returns to privileged EXEC mode.
Step 8
copy running-config startup-config
(Optional) Saves your entries in the configuration file.
1 Light Extensible Authentication Protocol
2 EAP-Flexible Authentication via Secure Tunneling
3 Protected EAP/Generic Token Card
4 XX PEAP
5 EAP-Transport Layer Security
Use the no form of the SSID commands to disable the SSID or to disable SSID features.
This example sets the authentication type for the SSID batman to Network-EAP with CCKM authenticated key management. Client devices using the SSID batman authenticate using the adam server list. After they are authenticated, CCKM-enabled clients can perform fast reassociations using CCKM.
ap# configure terminalap(config-if)# ssid batmanap(config-ssid)# authentication network-eap adamap(config-ssid)# authentication key-management cckm optionalap(config)# interface dot11radio 0ap(config-if)# ssid batmanap(config-ssid)# endConfiguring WPA Migration Mode
WPA migration mode allows the following client device types to use the same SSID to associate to the access point:
•
WPA clients capable of TKIP and authenticated key management
•
802.1X-2001 clients (such as legacy LEAP clients and clients using TLS) capable of authenticated key management but not TKIP
•
Static-WEP clients not capable of TKIP or authenticated key management
If all three client types associate using the same SSID, the multicast cipher suite for the SSID must be WEP. If only the WPA and 802.1X-2001 clients use the same SSID, the multicast key can be dynamic, but if the static-WEP clients use the SSID, the key must be static. To accommodate associated client devices, the access point can switch automatically between a static group key and a dynamic group key. To support all three types of clients on the same SSID, you must configure the static key in key slot 2 or 3.
To set up an SSID for WPA migration mode, configure these settings:
•
WPA optional
•
A cipher suite containing TKIP and 40-bit or 128-bit WEP
•
A static WEP key in key slot 2 or 3
This example sets the SSID migrate for WPA migration mode:
ap# configure terminalap(config-if)# ssid migrateap(config-if)# encryption mode cipher tkip wep128ap(config-if)# encryption key 3 size 128 12345678901234567890123456 transmit-keyap(config-ssid)# authentication openap(config-ssid)# authentication network-eap adamap(config-ssid)# authentication key-management wpa optionalap(config-ssid)# wpa-psk ascii batmobile65ap(config)# interface dot11radio 0ap(config-if)# ssid migrateap(config-ssid)# endConfiguring Additional WPA Settings
Use two optional settings to configure a pre-shared key on the access point and to adjust the frequency of group key updates.
Setting a Pre-Shared Key
To support WPA on a wireless LAN where 802.1X-based authentication is not available, you must configure a pre-shared key on the access point. You can enter the pre-shared key in ASCII or hexadecimal characters. If you enter the key as ASCII characters, you enter between 8 and 63 characters, and the access point expands the key by using the process described in the Password-based Cryptography Standard (RFC 2898). If you enter the key as hexadecimal characters, you must enter 64 hexadecimal characters.
Configuring Group Key Updates
In the last step in the WPA process, the access point distributes a group key to the authenticated client device. You can use these optional settings to configure the access point to change and distribute the group key, based on client association and disassociation:
•
Membership termination—The access point generates and distributes a new group key when any authenticated device disassociates from the access point. This feature keeps the group key private for associated devices, but it might generate some overhead traffic if clients on your network roam frequently among access points.
•
Capability change—The access point generates and distributes a dynamic group key when the last non-key management (static WEP) client disassociates. The access point distributes the statically configured WEP key when the first non-key management (static WEP) client authenticates. In WPA migration mode, this feature significantly improves the security of key-management-capable clients when there are no static-WEP clients associated to the access point.
To configure a WPA pre-shared key and group key update options, follow these steps, beginning in privileged EXEC mode:
Step 1
configure terminal
Enters global configuration mode.
Step 2
ssid ssid-string
Enters SSID configuration mode for the SSID.
Step 3
wpa-psk {hex | ascii} [0 | 7] encryption-key
Enters a pre-shared key for client devices that are using WPA that also use static WEP keys.
Enter the key by using either hexadecimal or ASCII characters. If you use hexadecimal, you must enter 64 hexadecimal characters to complete the 256-bit key. If you use ASCII, you must enter a minimum of 8 letters, numbers, or symbols, and the access point expands the key for you. You can enter a maximum of 63 ASCII characters.
Step 4
interface dot11radio radio-interface
Enters interface configuration mode for the radio interface.
Step 5
ssid ssid-string
Enters the SSID defined in Step 2 to assign the SSID to the selected radio interface.
Step 6
exit
Returns to privileged EXEC mode.
Step 7
broadcast-key [vlan vlan-id]
{change seconds}
[membership-termination]
[capability-change]Uses the broadcast key rotation command to configure additional updates of the WPA group key.
This example shows how to configure a pre-shared key for clients using WPA and static WEP, with group key update options:
ap# configure terminalap(config-if)# ssid batmanap(config-ssid)# wpa-psk ascii batmobile65ap(config)# interface dot11radio 0ap(config-ssid)# ssid batmanap(config-if)# exitap(config)# broadcast-key vlan 87 membership-termination capability-changeConfiguring MAC Authentication Caching
If MAC-authenticated clients on your wireless LAN roam frequently, you can enable a MAC authentication cache on your access points. MAC authentication caching reduces overhead because the access point authenticates devices in its MAC address cache without sending the request to your authentication server. When a client device completes MAC authentication to your authentication server, the access point adds the client's MAC address to the cache.
To enable MAC authentication caching, follow these steps, beginning in privileged EXEC mode:
Use the no form of the dot11 aaa mac-authen filter-cache command to disable MAC authentication caching.
The following example shows how to enable MAC authentication caching with a one-hour timeout:
ap# configure terminalap(config)# dot11 aaa mac-authen filter-cache timeout 3600ap(config)# endConfiguring Authentication Holdoffs, Timeouts, and Intervals
To configure holdoff times, reauthentication periods, and authentication timeouts for client devices that authenticate through your access point, follow these steps, beginning in privileged EXEC mode:
Use the no form of these commands to reset the values to default settings.
Configuring the 802.1X Supplicant
Traditionally, the dot1x authenticator and client have been a network device and a PC client, the supplicant, respectively, as it was the PC user that had to authenticate to gain access to the network. However, wireless networks introduce unique challenges to the traditional authenticator/client relationship. Access points can be placed in public places, inviting the possibility that they could be unplugged and their network connection used by an outsider.
The supplicant is configured in two phases:
•
Create and configure a credentials profile
•
Apply the credentials to an interface or SSID
You can complete the phases in any order, but they must be completed before the supplicant becomes operational.
Creating a Credentials Profile
To create an 802.1X credentials profile, follow these steps, beginning in privileged EXEC mode:
Use the no form of the dot1x credentials command to negate a parameter.
The following example creates a credentials profile named test with the username user and a the unencrypted password password:
ap>enablePassword:xxxxxxxap# config terminalEnter configuration commands, one per line. End with CTRL-Z.ap(config)# dot1x credentials testap(config-dot1x-creden)# username userap(config-dot1x-creden)# password passwordap(config-dot1x-creden)# exitap(config)#Applying the Credentials to an Interface or SSID
Credential profiles are applied to an interface or an SSID in identical ways.
Applying the Credentials Profile to the Wired Port
To apply the credentials to the access point's wired port, follow these steps, beginning in privileged EXEC mode:
The following example applies the credentials profile test to the access point's Fast Ethernet port:
ap>enablePassword:xxxxxxxap# config terminalEnter configuration commands, one per line. End with CTRL-Z.ap(config)# interface fa0ap(config-if)# dot1x credentials testap(config-if)# endap#Applying the Credentials Profile to an SSID Used for the Uplink
If you have a repeater access point in your wireless network and are using the 802.1X supplicant on the root access point, you must apply the 802.1X supplicant credentials to the SSID that the repeater uses to associate with and authenticate to the root access point.
To apply the credentials to an SSID used for the uplink, follow these steps, beginning in privileged EXEC mode:
The following example applies the credentials profile test to the ssid testap1 on a repeater access point.
repeater-ap>enablePassword:xxxxxxxrepeater-ap# config terminalEnter configuration commands, one per line. End with CTRL-Z.repeater-ap(config-if)# dot11 ssid testap1repeater-ap(config-ssid)# dot1x credentials testrepeater-ap(config-ssid)# endrepeater-ap(config)Creating and Applying EAP Method Profiles for the 802.1X Supplicant
This section describes the optional configuration of an EAP method list for the 802.1X supplicant. Configuring EAP method profiles enables the supplicant to not acknowledge some EAP methods, even though they are available on the supplicant. For example, if a RADIUS server supports EAP-FAST and LEAP, under certain configurations, the server might initially employ LEAP instead of a more secure method. If no preferred EAP method list is defined, the supplicant supports LEAP, but it may be advantageous to force the supplicant to use a more secure method such as EAP-FAST.
Creating an EAP Method Profile
To define a new EAP profile, follow these steps, beginning in privileged EXEC mode:
Step 1
configure terminal
Enters global configuration mode.
Step 2
eap profile profile name
Enters a name for the profile
Step 3
description
(Optional)—Enters a description for the EAP profile
Step 4
method fast
Enters an allowed EAP method or methods.
Note
Although they appear as sub-parameters, EAP-GTC, EAP-MD51 , and EAP-MSCHAPV22 are intended as inner methods for tunneled EAP authentication and should not be used as the primary authentication method.
Step 5
end
Returns to privileged EXEC mode.
1 EAP-Message Digest 5
2 EAP-Microsoft Challenge Handshake Authentication Protocol Version 2
Use the no command to negate a command or to set its defaults.
Use the show eap registrations method command to view the currently available (registered) EAP methods.
Use the show eap sessions command to view existing EAP sessions.
Applying an EAP Profile to the Fast Ethernet Interface
This operation normally applies to root access points. To apply an EAP profile to the Fast Ethernet interface, follow these steps, beginning in privileged EXEC mode:
Applying an EAP Profile to an Uplink SSID
This operation typically applies to repeater access points. To apply an EAP profile to the uplink SSID, follow these steps, beginning in the privileged EXEC mode.

Note
The repeater mode is not supported on Cisco 860 and Cisco 880 series embedded-wireless devices.
Matching Access Point and Client Device Authentication Types
To use the authentication types described in this section, the access point authentication settings must match the authentication settings on the client adapters that associate to the access point. See the Cisco Aironet Wireless LAN Client Adapters Installation and Configuration Guide for Windows for instructions on setting authentication types on wireless client adapters. See the Cipher Suites and WEP documentation documentation on Cisco.com for instructions on configuring cipher suites and WEP on the access point.
Table 1 lists the client and access point settings required for each authentication type.

Note
Some non-Cisco Aironet client adapters do not perform 802.1X authentication to the access point unless you configure Open authentication with EAP. To allow both Cisco Aironet clients using LEAP and non-Cisco Aironet clients using LEAP to associate using the same SSID, you might need to configure the SSID for both Network EAP authentication and Open authentication with EAP.
Likewise, to allow both Cisco Aironet 802.11a/b/g client adapters (CB21AG and PI21AG) running EAP-FAST and non-Cisco Aironet clients using EAP-FAST or LEAP to associate using the same SSID, you might need to configure the SSID for both Network EAP authentication and Open authentication with EAP.

Note
If you are running an 802.11n access point, for best results be sure to get the latest driver from the 802.11n Wi-Fi card vendor for the card that you are using.
f
Table 1 Client and Access Point Security Settings
Static WEP with open authentication
Create a WEP key, and enable Use Static WEP Keys and Open Authentication.
Set up and enable WEP, and enable open authentication for the SSID.
Static WEP with shared key authentication
Create a WEP key, and enable Use Static WEP Keys and Shared Key Authentication.
Set up and enable WEP, and enable Shared Key Authentication for the SSID.
LEAP authentication
Enable LEAP.
Set up and enable WEP, and enable Network-EAP for the SSID1 .
EAP-FAST authentication
Enable EAP-FAST, and enable automatic provisioning or import a Protected Access Credential (PAC) file.
Set up and enable WEP, and enable Network-EAP for the SSID1.
If radio clients are configured to authenticate using EAP-FAST, open authentication with EAP should also be configured. If you do not configure open authentication with EAP, the following warning message appears:
SSID CONFIG WARNING: [SSID]: If radio clients are using EAP-FAST, AUTH OPEN with EAP should also be configured.
EAP-FAST authentication with WPA
Enable EAP-FAST and Wi-Fi Protected Access (WPA), and enable automatic provisioning or import a PAC file.
To allow the client to associate to both WPA and non-WPA access points, enable Allow Association to both WPA and non-WPA authenticators.
Select a cipher suite that includes TKIP, set up and enable WEP, and enable Network-EAP and WPA for the SSID.
Note
To allow both WPA and non-WPA clients to use the SSID, enable optional WPA.
802.1X authentication and CCKM
Enable LEAP.
Select a cipher suite, and enable Network-EAP and CCKM for the SSID.
Note
To allow both 802.1X clients and non-802.1X clients to use the SSID, enable optional CCKM.
802.1X authentication and WPA
Enable any 802.1X authentication method.
Select a cipher suite, and enable open authentication and WPA for the SSID (you can also enable Network-EAP authentication in addition to or instead of open authentication).
Note
To allow both WPA clients and non-WPA clients to use the SSID, enable optional WPA.
802.1X authentication and WPA-PSK
Enable any 802.1X authentication method.
Select a cipher suite, and enable open authentication and WPA for the SSID (you can also enable Network-EAP authentication in addition to or instead of open authentication). Enter a WPA pre-shared key.
Note
To allow both WPA clients and non-WPA clients to use the SSID, enable optional WPA.
EAP-TLS authentication
If using automatic calling unit (ACU) to configure card
Enable Host Based EAP and Use Dynamic WEP Keys in ACU, and select Enable network access control using IEEE 802.1X and Smart Card or Other Certificate as the EAP Type in Windows 2000 (with Service Pack 3) or Windows XP.
Set up and enable WEP, and enable EAP and open authentication for the SSID.
If using Windows XP to configure card
Select Enable network access control using IEEE 802.1X and Smart Card or other Certificate as the EAP Type.
Set up and enable WEP, and enable EAP and open authentication for the SSID.
EAP-MD5 authentication
If using ACU to configure card
Create a WEP key, enable Host Based EAP, and enable Use Static WEP Keys in ACU, and select Enable network access control using IEEE 802.1X and MD5-Challenge as the EAP Type in Windows 2000 (with Service Pack 3) or Windows XP.
Set up and enable WEP, and enable EAP and open authentication for the SSID.
If using Windows XP to configure card
Select Enable network access control using IEEE 802.1X and MD5-Challenge as the EAP Type.
Set up and enable WEP, and enable EAP and open authentication for the SSID.
PEAP authentication
If using ACU to configure card
Enable Host Based EAP and Use Dynamic WEP Keys in ACU, and select Enable network access control using IEEE 802.1X and PEAP as the EAP Type in Windows 2000 (with Service Pack 3) or Windows XP.
Set up and enable WEP, and enable EAP and open authentication for the SSID.
If using Windows XP to configure card
Select Enable network access control using IEEE 802.1X and PEAP as the EAP Type.
Set up and enable WEP, and enable Require EAP and open authentication for the SSID.
EAP-SIM authentication
If using ACU to configure card
Enable Host Based EAP and Use Dynamic WEP Keys in ACU, and select Enable network access control using IEEE 802.1X and subscriber identity module (SIM) authentication as the EAP Type in Windows 2000 (with Service Pack 3) or Windows XP.
Set up and enable WEP with full encryption, and enable EAP and open authentication for the SSID.
If using Windows XP to configure card
Select Enable network access control using IEEE 802.1X and SIM authentication as the EAP Type.
Set up and enable WEP with full encryption, and enable EAP and open authentication for the SSID.
1 Some non-Cisco Aironet client adapters do not perform 802.1X authentication to the access point unless you configure open authentication with EAP. To allow both Cisco Aironet clients using LEAP and non-Cisco Aironet clients using LEAP to associate using the same SSID, you might need to configure the SSID for both Network EAP authentication and open authentication with EAP. Likewise, to allow both Cisco Aironet 802.11a/b/g client adapters (CB21AG and PI21AG) running EAP-FAST and non-Cisco Aironet clients using EAP-FAST or LEAP to associate using the same SSID, you might need to configure the SSID for both Network EAP authentication and open authentication with EAP.
 Feedback
Feedback