Release Notes for the Cisco NetFlow Generation Appliance 1.0 (2)
Available Languages
Table Of Contents
Release Notes for the Cisco NetFlow Generation Appliance
Visibility into Switch Interface Data for Managed Device Flows
Single Source of Flow Visibility for Multiple Management Applications
Fabric Path Domain Flow Visibility in the Data Center
Collect Data Using Various Export Formats to Support Multiple Management Applications
Open Bugs in Cisco NGA 1.0 (2)
Resolved Bugs in Cisco NGA 1.0 (2)
Front Panel for Cisco NGA 3240
Configure Your Traffic Sources
Cisco NGA 3240 Technical Specifications
Overview of Cisco NGA Flow Components
Examples of Deployment Scenarios
Field Replaceable Units (FRU) Components
Using Virtual Media to Install or Recover Cisco NGA
Obtaining Documentation and Submitting a Service Request
Release Notes for the Cisco NetFlow Generation Appliance
Release 1.0 (2)
November 21, 2012, OL-26941-01
This release note includes important information about Cisco NetFlow Generation Appliance (Cisco NGA) Software Release 1.0 (2) and contains the following sections:
•
Obtaining Documentation and Submitting a Service Request
You can access the most current Cisco NGA documentation, including these release notes, online at the Cisco NetFlow Generation Appliance page on Cisco.com.
New and Changed Information
The following sections describe release information that is pertinent to Cisco NetFlow Generation Appliance Software Release 1.0 (2).
Cisco NGA New Features
Cisco NetFlow Generation Appliance (NGA) provides network visibility and establishes a new standard for cross-device flow visibility. It empowers network operations, engineering, and security teams with actionable insight into network traffic for the purpose of resource optimization, application performance improvement, traffic accounting, and security needs.
Cisco NGA 3240 is preinstalled with the Cisco NetFlow Generation Appliance Software Release 1.0 (2). Cisco NGA 3140 users can upgrade to this Cisco NGA software release. For upgrade instructions, see Using Virtual Media to Install or Recover Cisco NGA and the Quick Start Guide for the Cisco NetFlow Generation Appliance.
The following topics describe new features and enhancements in Cisco NGA 1.0 (2):
•
Visibility into Switch Interface Data for Managed Device Flows
For detailed feature descriptions see the "Key Features" section in the User Guide for Cisco NetFlow Generation Appliance.
For the most up-to-date support information and documentation updates, see the online release notes on Cisco.com.
New Device Support
Cisco NGA 1.0 (2) adds support for the Cisco Nexus 3000 Switch device as a Cisco managed device. For details, see Configure Your Traffic Sources. For version support information, see the Cisco NetFlow Generation Appliance Compatibility Matrix.
Visibility into Switch Interface Data for Managed Device Flows
You can now access switch interface information for Cisco Nexus 3000, 5000, and 7000 Series switch flows using the managed device feature. The following switch MIB-2 and IF-MIB objects are mirrored in the Cisco NGA ifTable for the configured managed devices: ifName, ifDescr, ifAlias, ifType, ifMtu, ifSpeed, and ifHighSpeed. This enhancement provides accurate NetFlow interface information without impairing switch performance.
For version support information, see the Cisco NetFlow Generation Appliance Compatibility Matrix.
TCP Flags Enhancement
In Cisco NGA 1.0 (1), the bits in the TCP flag field collected were cumulative over the life of a particular flow. To improve security, TCP flag bits are now reset after each flow export so that only the flags that have been observed since the last export are reported. The reporting period is the active timeout interval. This enhancement helps collector applications that are interested in security-oriented data. By clearing the flags after each export, collectors that use NetfFlow to search for network attacks can detect SYN-flood attacks more readily.
Increase Flow Cache Size
The active flow cache size has been increased to 80 million flows.
Session Timeout for TCP
The TCP flows are now reported instantly when they are closed instead of using a fixed delay. This enhancement optimizes the TCP flows to provide more efficient cache management.
Virtual Media Support
The Cisco NGA 3240 hardware release no longer supports a CD/DVD and requires you to use virtual media for installations and upgrades. For instructions on how to use the Cisco NGA built-in management tool to perform various tasks, see Using Virtual Media to Install or Recover Cisco NGA.
CIMC virtual media support on the Cisco NetFlow Generation Appliance 3140 (as well as the 3240). For details on how to use the CIMC and the specific helper options you should choose, see Using the CIMC.

Note
This software is preinstalled on a UCS C-Series server. Where applicable, documentation may reference the UCS C-Series guides for hardware-specific tasks such as rack mounting and technical specifications. Because Cisco NGA is the only application running on this appliance, it does not require you to perform any maintenance or configuration tasks that may be associated with the UCS C-Series server. We recommend you do not attempt to open the appliance unless directed by a customer support representative.
Device Support
Managed device support now includes the Nexus 3000 Series switches. For details on the list of supported Cisco managed devices and their software versions, see the Cisco NetFlow Generation Appliance Compatibility Matrix.
Common Deployment Scenarios
This release note includes the following examples to help illustrate several configuration scenarios for your Cisco NGA.
•
Single Source of Flow Visibility for Multiple Management Applications
•
Fabric Path Domain Flow Visibility in the Data Center
•
Collect Data Using Various Export Formats to Support Multiple Management Applications
Single Source of Flow Visibility for Multiple Management Applications
Figure 1 shows a configuration example of the Cisco NGA flow components that use the same traffic flows but allow you to filter flow data about specific applications; for example, if you want to verify application specific flows that enable you to charge a customer for usage, use this type of configuration. The numbered list below the figure corresponds to the callouts in Figure 1 and describes each component in this configuration example.
The quickest way to configure this type of scenario is to use the Quick Setup, then add the second flow collector using the Advanced Setup. For instructions, see the Quick Start Guide for the Cisco NetFlow Generation Appliance.
Figure 1 Deployment for Single or Multiple Device Traffic Flows for Multiple Application Data
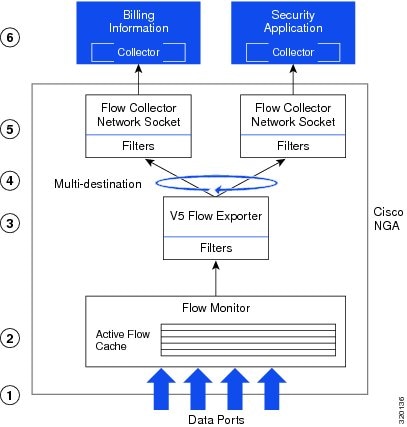
Configure traffic from one or more network devices to Cisco NGA using SPAN or a passive network tap. For details on how to configure SPAN or a tap device, see your device documentation.
Configure a flow monitor with all four interfaces from your switch (which could be an access or aggregation switch).
Configure a single v5 flow exporter to receive traffic on all four data ports. The flow exporter manages the flows with the same filters to support one format; in Figure 1 the exporter supports v5 format.
Configure multi-destination policies to replicate the flows across multiple collectors. This enables you to use the same traffic flows across all collectors for the purpose of separate management tasks.
Configure a filter for billing purposes by selecting the source IP address and source port number in the Advanced Setup Filter configuration window. Alternately, if you have a v9 flow exporter use the application ID defined in the record, you may filter on the application instead of the port number.
For details on configuring the Advanced Setup filters, see the User Guide for Cisco NetFlow Generation Appliance.
Use your NetFlow collectors to produce reports, graphs, and analysis of the data.
Fabric Path Domain Flow Visibility in the Data Center
Figure 2 shows a configuration example of the Cisco NGA flow components that help you to analyze Layer 2 traffic flows from two or more switches within the data center using load balancing policies; for example, to filter specific flows across all collectors, use this type of configuration. The numbered list below the figure corresponds to the callouts in Figure 2 and describes each component in this configuration example.
Figure 2 Deployment for Fabric Path Domain Flow Visibility in the Data Center
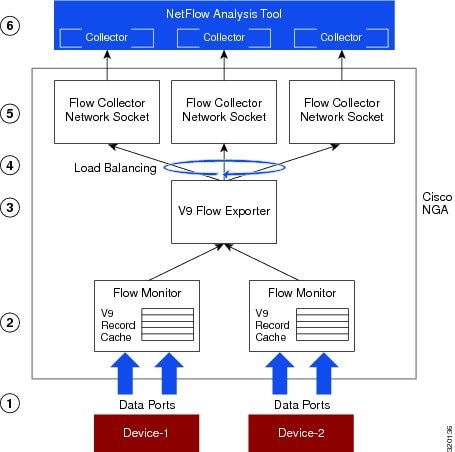
Configure traffic from two (or more) network devices in the Fabric Path domain to Cisco NGA using SPAN or a passive network tap. This enables you to analyze Layer 2 traffic flows within the data center. For details on how to configure SPAN or a tap device, see your device documentation.
Configure your flow monitors with two interfaces from each device (which could be an access or aggregation switch). For details on configuring the Advanced Setup flow monitors, see the User Guide for Cisco NetFlow Generation Appliance.
Configure multiple flow exporters to receive traffic from different devices on all four data ports. The flow exporter manages the flows with the same filters to support one format; in Figure 2 the exporter supports v9 format.
In this mode, only one level of filters are allowed; the filters that are associated with the flow exporter. Having only a single set of filters applied at the exporter level allows the appliance to accurately honor the round-robin weight assignments.
Configure load balancing policies to spread the flows across multiple collectors. This enables you to avoid high traffic flows on any one collector and improve scalability.
For details on configuring the Advanced Setup filters, see the User Guide for Cisco NetFlow Generation Appliance.
When collectors are configured in load-balancing mode you can apply filters at the exporter level only.
Use your NetFlow collectors to produce reports, graphs, and analysis of the data.
Collect Data Using Various Export Formats to Support Multiple Management Applications
Figure 3 shows a configuration example of the Cisco NGA flow components that help to gather flow data using different export formats. This scenario supports flow visibility into multiple management applications such as billing (using NetFlow v5 format) and security (using IPFIX format). The numbered list below the figure corresponds to the callouts in Figure 3 and describes each component in this configuration example.
Figure 3 Deployment with Different Export Formats Collecting Multi-Application Data
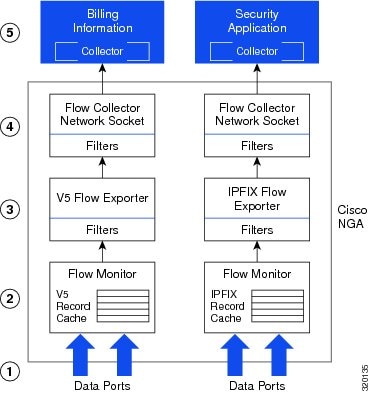
Configure traffic to Cisco NGA using SPAN or a passive network tap. A flow monitor can be configured to listen to up to four data ports. For details on how to configure SPAN or a tap device, see your device documentation.
Configure one or more flow monitors to export multiple export formats. Figure 3 depicts v5 and IPFIX exporters. Each exporter can work independently using different traffic input based on the requirements of your management application.
Configure multiple flow export filters to funnel application traffic based on specific management applications. For details on configuring the Advanced Setup flow filters, see the User Guide for Cisco NetFlow Generation Appliance.
Given that filtering has been configured at the flow exporter, no extra filtering is required at the flow collector.
Use your NetFlow collectors to produce reports, graphs, and analysis of the data.
Cisco NGA 1.0 (2) Bugs
This section provides information about open and resolved bugs in the Cisco NGA Software Release 1.0 (2) software release.
•
Open Bugs in Cisco NGA 1.0 (2)
•
Resolved Bugs in Cisco NGA 1.0 (2)
To obtain more information about known problems, access the Cisco Software Bug Toolkit at the following URL:
http://www.cisco.com/cgi-bin/Support/Bugtool/home.pl
Open Bugs in Cisco NGA 1.0 (2)
Table 1 provides a list of open bugs in Cisco NGA Software Release 1.0 (2).
Click on the identifier to view the impact and workaround for the bug. This information is displayed in the Using the Bug Tool Kit. You can track the status of the open bugs, using the Bug Toolkit.
Resolved Bugs in Cisco NGA 1.0 (2)
Table 2 provides a list of resolved bugs in Cisco NGA Software Release 1.0 (2).
Using the Bug Tool Kit
This section explains how to use the Bug Toolkit to search for a specific bug or to search for all bugs in a release.
Step 1
Go to http://tools.cisco.com/Support/BugToolKit.
Step 2
At the Log In screen, enter your registered Cisco.com username and password; then, click Log In. The Bug Toolkit page opens.

Note
If you do not have a Cisco.com username and password, you can register for them at http://tools.cisco.com/RPF/register/register.do.
Step 3
To search for a specific bug, click the Search Bugs tab, enter the bug ID in the Search for Bug ID field, and click Go.
Step 4
To search for bugs in the current release, click the Search Bugs tab and specify the following criteria:
•
Select Product Category—Network Management and Automation.
•
Select Products—[Product Name].
•
Software Version—[Product Version].
•
Search for Keyword(s)—Separate search phrases with boolean expressions (AND, NOT, OR) to search within the bug title and details.
•
Advanced Options—You can either perform a search using the default search criteria or define custom criteria for an advanced search. To customize the advanced search, click Use custom settings for severity, status, and others and specify the following information:
–
Severity—Choose the severity level.
–
Status—Choose Terminated, Open, or Fixed.
Choose Terminated to view terminated bugs. To filter terminated bugs, uncheck the Terminated check box and select the appropriate suboption (Closed, Junked, or Unreproducible) that appears below the Terminated check box. Select multiple options as required.
Choose Open to view all open bugs. To filter the open bugs, uncheck the Open check box and select the appropriate suboptions that appear below the Open check box. For example, if you want to view only new bugs in Prime Optical 9.5, choose only New.
Choose Fixed to view fixed bugs. To filter fixed bugs, uncheck the Fixed check box and select the appropriate suboption (Resolved or Verified) that appears below the Fixed check box.
–
Advanced—Check the Show only bugs containing bug details check box to view only those bugs that contain detailed information, such as symptoms and workarounds.
–
Modified Date—Choose this option to filter bugs based on the date when the bugs were last modified.
–
Results Displayed Per Page—Specify the number of bugs to display per page.
Step 5
Click Search. The Bug Toolkit displays the list of bugs based on the specified search criteria.
Step 6
To export the results to a spreadsheet:
a.
In the Search Bugs tab, click Export All to Spreadsheet.
b.
Specify the filename and location at which to save the spreadsheet.
c.
Click Save. All bugs retrieved by the search are exported.
If you cannot export the spreadsheet, log into the Technical Support website at http://www.cisco.com or contact the Cisco Technical Assistance Center (TAC).
Documentation Updates
This section contains information about errors, omissions, and changes for Cisco NetFlow Generation Appliance 1.0 documentation and online help.
The following information is more recent than the existing Cisco.com documentation and online help:
•
Updates for Quick Start Guide
Updates for Quick Start Guide
The following sections in the Quick Start Guide for the Cisco NetFlow Generation Appliance are updated below for release 1.0 (2) as follows:
•
Requirements and Restrictions
•
Rear Panel for Cisco NGA 3240
•
Front Panel for Cisco NGA 3240
•
Configure Your Traffic Sources
•
Field Replaceable Units (FRU) Components
•
Cisco NGA 3240 Technical Specifications
We recommend you review the Quick Start Guide for the Cisco NetFlow Generation Appliance 3240 and refer back to the release notes for recently updated details.
Requirements and Restrictions
Browser support includes the following tested browsers:
•
Mozilla Firefox ESR 10
•
Microsoft Internet Explorer 9
For additional compatibility information, see the Cisco NetFlow Generation Appliance Compatibility Matrix.
Rear Panel for Cisco NGA 3240
The rear panel for the Cisco NGA 3240 is described in Figure 4. Cisco NGA software comes preinstalled on the UCS 220 M3 server and is referred to in the product documentation as the Cisco NetFlow Generation Appliance, or the appliance.

Note
Rear panel port numbers mirror the location numbers in Figure 4. They are unlike standard port numbers, so take special note.
Figure 4 Cisco NGA 3240 Rear Panel
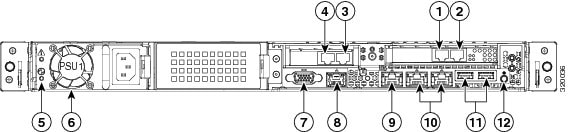
Table 3 Rear Panel Location Numbers
Data port #1
VGA video connector
Data port #2
Serial port (RJ-45 connector)1
Data port #3
CIMC Ethernet port (RJ45)2
Data port #4
Dual 1-Gb Ethernet ports
(LAN1 and LAN2)3Power supply LED
USB ports
Power supply
Rear Identification button/LED
1 Connect to local terminal server
2 Required only if you plan to use the UCS management center software
3 Only one port is used as a management port for Cisco NGA (LAN1); additional port is reserved for future use
Front Panel for Cisco NGA 3240
The front panel for the Cisco NGA 3240 is described in Figure 5. Cisco NGA software comes preinstalled on the UCS 220 M3 server.
Figure 5 Cisco NGA Front Panel
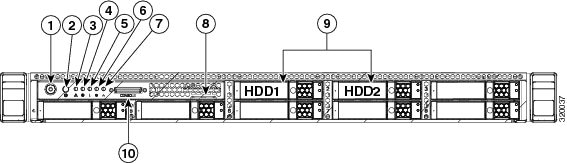
Table 4 Cisco NGA 3240 Front Panel
Power button/Power status LED1
Power supply status LED
Identification locator button/Locator LED
Network link activity LED
System status LED
Pull-out asset tag
Fan status LED
Hard disk drives (2)
Temperature status LED
KVM console port2
1 Use only when a forced shutdown is necessary. Hold down for several seconds until light is no longer lit with a green color.
2 Use with KVM cable that provides two USB, one VGA, and one serial connector. You can connect to an optional keyboard and VGA monitor.
Supported Upgrade Path
Table 5 provides details on the commands to use for Cisco NGA backup, upgrade, and restore tasks.
Configure Your Traffic Sources
This section includes updates to the existing product documentation which now includes the Cisco Nexus 3000 Series switch as a managed device.
Cisco NGA supports network devices that can direct traffic to Cisco NGA using standard SPAN. For traffic sources that are supported Cisco managed devices, you can also collect interface information for the traffic sources. For specific Cisco managed device support versions, see the marketing documentation on Cisco.com.
There are two tasks to configuring your traffic sources. The traffic source in Cisco NetFlow Generation Appliance can be either a switch or router. The first task is required; the second task is optional.
Perform these tasks to set up your traffic sources; for example, a Nexus 3000, Nexus 5000, or Nexus 7000 Series switch. For a list of supported platforms, see the Cisco NetFlow Generation Appliance Compatibility Matrix.
1.
(Required) Create a Switched Port Analyzer (SPAN) session (also known as port mirroring) on your switch or router using the command line interface, or use a tap device to forward traffic to your Cisco NGA. Port mirroring selects network traffic for analysis by a network analyzer.
Ensure that your traffic sources are connected to the data ports on the appliance with the appropriate 10-Gb Ethernet cable. This document does not provide details on how to create SPAN sessions or to use a network tap device. For details on how to set up these configurations, see your device documentation.
2.
(Optional) Configure the IP address of your traffic source in Cisco NGA as a managed device.
If your traffic source is one of the supported Cisco switches or routers and you want the appliance to export flow records with the input and output interface of the device rather than data port interface index on the appliance, you need to configure the IP address and login credentials of your traffic source as a managed device. For details, see Configure the IP Address of Your Traffic Source.
One of the benefits of configuring a managed device on the Cisco NGA allows the appliance to gather the interface index from the device. Cisco NGA populates exported NetFlow records with the interface (ifIndex) values from the device that is being monitored, rather than the interface values from the appliance itself.
For example, in a scenario when a flow enters a Cisco Nexus switch on interface 50 and leaves on interface 60, and it is also being replicated (through SPAN) to interface 2 of the appliance, if the Cisco Nexus switch is configured as the managed device, Cisco NGA can report input interface 50 and output interface 60 for the flow. Otherwise, it will report interface 2 for both input and output, as this is the Cisco NGA interface on which a copy of the flow is received. Note that the managed device feature support is limited to platforms indicated in the Cisco NetFlow Generation Appliance Compatibility Matrix.

Note
SSH must be enabled on the remote Nexus device in order for Cisco NGA to access interface information. For details on how to enable SSH on the Nexus OS, see the device documentation.
Configure the IP Address of Your Traffic Source
One of the benefits of configuring the IP address of your supported Nexus Series switches is that when your switch is configured as a managed device, Cisco NetFlow Generation Appliance uses the switch's interface index values when exporting records. This allows you more visibility into the collected data. This is an optional task.
Ensure that your traffic sources are connected to the data ports on the Cisco NGA with the appropriate 10Gb Ethernet cable.
To add, edit, or delete managed devices:
Step 1
To configure up to four Nexus Series switch devices as managed devices in Cisco NGA, choose Setup > NetFlow > Managed Devices.
Step 2
Choose one of the following tasks:
•
To add managed devices, click Create and enter the required information in the Create Managed Device window. See Table 1-6 for field descriptions.
•
To edit an existing managed device, select the row, click Edit then enter the device information.
•
To delete a managed device, select the row and click Delete.
You can configure up to four managed devices. For each managed device, you can specify which set of data ports are attached to it. Once a data port is assigned to one managed device, you cannot assign it to another managed device.
Step 3
Once you configure the managed device or devices, to configure your Cisco NGA flow components choose Setup > NetFlow > Quick Setup or Setup > NetFlow > Advanced Setup.
We recommend using the Quick Setup to configure your initial NetFlow monitor instance. A NetFlow monitor instance consists of a flow monitor, collector, and exporter for v5 and a flow monitor, collector, exporter, and record name for v9. Then use Advanced Setup if you require additional flow components or filters.
Cisco NGA 3240 Technical Specifications
The following table contains links to the technical specifications for the Cisco NetFlow Generation Appliance 3240. Cisco NGA is an integrated hardware platform that is preinstalled with the Cisco NetFlow Generation Appliance Software Release 1.0 (2) on the UCS C220 M3 server.
Physical
The Physical Specifications section in the Cisco UCS C220 Server Installation and Service Guide.
Environmental
The Environmental Specifications section in the Cisco UCS C220 Server Installation and Service Guide.
Power
The Power Specifications section in the Cisco UCS C220 Server Installation and Service Guide. Cisco NGA ships with a 650W power supply.
For more information about the Cisco UCS C220 server, see the Cisco UCS C220 Server Installation and Service Guide.
Updates for User Guide
Several updates did not make it into to the User Guide for Cisco NetFlow Generation Appliance after the release was published. To view the latest product information, review the updates in this section. For the product documentation set, see Cisco.com.
The following sections are new or replace existing content in the user guide for release 1.0 (2):
•
Overview of Cisco NGA Flow Components
•
Examples of Deployment Scenarios
•
Using Virtual Media to Install or Recover Cisco NGA
Overview of Cisco NGA Flow Components
Cisco NGA uses flow components, or standard NetFlow configurations, to customize the traffic analysis parameters for your specific requirements. You can quickly set up a single NetFlow monitoring instance which is the minimum set of flow components required using the Quick Start workflow.
For advanced configurations where multiple NetFlow monitoring instances are desired or advanced features such as filters and customizing v9 and IPFIX record parameters are needed, you can use the Advanced Setup workflow.
Figure 6 depicts the simplest deployment scenario. It is an example of a Cisco NGA monitoring instance. Each monitoring instance contains a variable set of flow components based on your configuration. This is the minimum set of flow components that you must configure in the appliance to export NetFlow v5 data. For NetFlow v9 data export, the monitoring instance may contain any combination of the following: a flow monitor, exporter, collector, and record name. Configure this setup using the Advanced Setup menu. For definitions of Cisco NGA flow components, see Table 7.
Figure 6 Quick Setup Diagram of Cisco NGA Flow Components
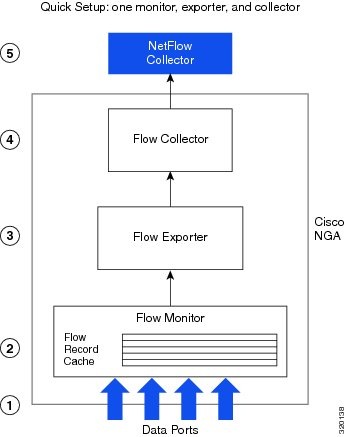
You can connect up to four routers or switches to the appliance using the four data ports configured with SPAN sessions as described in Examples of Deployment Scenarios. Other configurations are also possible using a network tap device. For additional scenarios, see Common Deployment Scenarios. For an installation and configuration overview, see the Quick Start Guide for Cisco NetFlow Generation Appliance.
Table 7 defines each flow component and provides examples of how to configure them. Flow components can be combined to create various monitoring instances to address specific deployment needs. For details on the deployment methods you can choose for device support, see Examples of Deployment Scenarios.
Table 7 Cisco NGA Flow Components and Terms
Flow monitor
A flow monitor is required to export flow cache data. You must create and activate at least one flow monitor for the system to begin exporting flows.
You can create more than one flow monitor to monitor different sets of data ports and use different cache parameters.
One data port can be used by one active monitor at any given time.
The flow monitor designates which data ports are monitored by the the appliance and specifies parameters for the flow cache operation. You can custom the following parameters:
•
The size of the cache
•
Timeout values and behavior
•
Which flow records are to be associated with the flow monitor
When you use multiple flow monitors you can associate different data ports with each monitor. You can also associate different exporters with each monitor, and by doing so associate different collectors with each monitor.
For example, you can attach four different switches to the appliance, so that you send the data from each switch to a different collector. In this case, you must create four distinct flow monitors, each one configured with the data port that is connected to the corresponding switch. Each flow monitor has its own flow exporter (so you can vary them to use either v5 or v9), and each of those exporters can be associated with a different collector.
Flow collector
Each flow collector within the Cisco NGA represents a construct (which may have associated filters). That internal construct, represented in the figure as a flow collector socket, is what you must explicitly configure.
The NetFlow collector is an external device, separate from the Cisco NGA, to which the appliance can export flow records. Most collectors will store the flow data in a database and then produce reports, graphs, and analysis of the data. Use the Cisco NGA's flow collector configuration to specify the IP address and UDP port of your collectors.
A collector may specialize in traffic accounting, billing, monitoring traffic patterns on your network, or detecting potential security threats. Flow records exported by the Cisco NGA provide the necessary data to produce these reports.
You may configure multiple collectors and the Cisco NGA exports data to each of them, either alternating between them in a round robin fashion, or replicating the same flow data to each collector. In this way you can deploy multiple collectors for different purposes. You can also spread the load across multiple collectors if one collector cannot keep up with the data rate exported by the Cisco NGA.
Flow exporter
The flow exporter specifies which version of NetFlow Data Export format should be exported by the Cisco NGA.
The flow exporter is also used to designate other parameters such as how often the Cisco NGA sends out NetFlow template updates, and which policy should be used if there are multiple collectors (replicate the same to data to each, or load balance among them).
You may define filters in the flow exporter to specify exactly which flows are to be sent to each collector.
Ensure you choose a NetFlow Data Export format that is supported by your collectors.

Note
Cisco NGA is capable of generating a large amount of data. If necessary, use filters to reduce the load on your collector, or use multiple collectors in round robin load balancing mode.
Flow Filters (optional)
There are two configurable filter levels in Cisco NGA: one filter that defines which device record data to collect (collector) and one that defines what data to export to the NetFlow collectors (exporter).
You can use filters to match specific fields within each flow record before it is exported.
You can also reduce the demand on your collector by applying filters to reduce the number of flows that are actually exported by the appliance.
You may apply specific filters to individual collectors, or you may apply filters globally in the flow exporter definition and they will apply to all collectors in that exporter.
The primary use of filters is to lighten the load on collectors that may not be able to keep up with a high export rate.
Alternately, you may only be interested in flow data for a particular host, or set of hosts, or a particular application, and so on. In these cases, you can use filters to limit the data to only those flows that are of interest.
Filters are not applicable for round robin export policy.
Flow Record (configurable in v9 and IPFIX)
A flow record is a basic unit of information exported by the Cisco NGA to collectors.
Use the record configuration to specify which fields are used to uniquely identify a flow, and to specify which counters and information elements are to be exported for each flow.
The Match fields are treated as keys and are used to uniquely identify each flow. For example, you may want a particular flow to be identified by five parameters such as source IP address, destination IP address, source port number, destination port number, and IP protocol value.
Or to effectively aggregate several flows together you can select fewer Match fields. For example by selecting only the source and destination IP address. In that case, several connections which use different port numbers are aggregated into a single flow record for export.
The Collect fields collect additional data in the flow that you can specify; such as packet count, byte count, TCP flags, and so on.
Managed Device
A supported Cisco switch or router that is configured so that the Cisco NGA can gather NetFlow data such as interface details.
For specific Cisco switch and router platform support, see the Cisco NetFlow Generation Appliance Compatibility Matrix.
One of the benefits of configuring a managed device on the Cisco NGA is that it allows the appliance to gather the interface index from the device as well as the interface name. Cisco NGA populates exported NetFlow records with the interface (ifIndex) values (ifName, ifDescr, ifAlias, ifType, ifMtu, ifSpeed, and ifHighSpeed) from the device that is being monitored, rather than the interface values from the appliance itself.
1 For details on how to configure these components, see the Quick Start Guide for Cisco NetFlow Generation Appliance or the User Guide for Cisco NetFlow Generation Appliance.
Examples of Deployment Scenarios
The following content clarifies the deployment methods, or scenarios, that Cisco NGAsupports.
You can direct packets to the Cisco NGA using either or both of the following deployment scenarios:
•
A Switched Port Analyzer (SPAN) session (also known as port mirroring) from the network device that supports this method. Port mirroring selects network traffic for analysis by a network analyzer. This is a low-cost alternative to network taps.
You can choose to use SPAN, remote SPAN (RSPAN), or SPAN with port channels to monitor your traffic. To configure one of these SPAN methods on your Cisco Nexus or Catalyst devices to send traffic to the Cisco NGA, use the Nexus supervisor or the Catalyst IOS CLI. Using local SPAN uses four data ports, thus four routers or switches.
•
A network tap. A network tap is a hardware device which provides a copy of the data that flows across a network link. By setting up a network tap using remote SPAN or Remote (RSPAN), you are able to monitor more than the four routers or switches you are limited to using local SPAN.
To understand how SPAN, RSPAN, and port channelling work on Cisco routers and switches and how to configure your network devices using standard SPAN, see your router and switch software configuration documentation.
Field Replaceable Units (FRU) Components
This section details links to manage the Cisco NGA Field Replaceable Units (FRUs):
•
Removing and Replacing a Hard Disk Drive
For information about replacing hard disk drives in the appliance, see the Replacing Hard Drives or Solid State Drives section in the Cisco UCS C220 Server Installation and Service Guide.
•
Installing or Replacing a Power Supply
For information about replacing power supplies, see the Replacing Power Supplies section in the Cisco UCS C220 Server Installation and Service Guide.
Miscellaneous Updates
The following details will be added to the user guide during the next release update:
•
You must define a NetFlow v9 record counter field (such as packets or bytes) or no NetFlow data generates (since there is no data to collect).
•
The v9 record name of an existing flow monitor may still be displayed after the particular flow monitor being edited and changed to exported NetFlow v5 type. The workaround is, while in flow monitor editing mode, use the backspace key to delete the Exporter name then un-select the v9 Record Name when this field becomes editable. Reselect the Exporter then save.
•
When you use the CLI, if you have multiple existing filters and attempt to add another filter you must reenter all the filter names in order to add any new filters. We recommend you use commas with no spaces to separate the filters.
•
Cisco NGA is now recovered using virtual media if necessary. The CD/DVD is no longer shipped. See Using Virtual Media to Install or Recover Cisco NGA for instructions.
•
Table 8 lists the ports used by the Cisco NGA for network communication.
Using the CIMC
The CIMC is a built-in management service provided with the Cisco NGA. CIMC provides a web-based GUI that enables you to perform tasks including:
•
Manage remote presence with KVM console. The console is an interface accessible from CIMC and emulates a direct keyboard, video, and mouse (KVM) connection to the appliance. The KVM console allows you to connect to the appliance from a remote location. It also provides the "Virtual Media" feature used for recovery/ISO install. (See Using the KVM Console.)
•
Power on, power off, power cycle, reset and shut down the appliance
•
Toggle the locator LED to locate the appliance with blinking blue LED
For instructions on how to use the Cisco NGA built-in management tool to perform various tasks, see Using Virtual Media to Install or Recover Cisco NGA.
Using the KVM Console
The KVM console is an interface accessible from the Cisco NGA that emulates a direct KVM connection. The KVM console allows you to view the serial console remotely without any connection to a terminal server. It also provides the Virtual Media feature used for recovery/ISO install.
If you want to use the KVM console to access the appliance, you must ensure that either the appliance or the service profile associated with the appliance is configured with a CIMC IP address. The KVM console uses the CIMC IP address assigned to an appliance or a service profile to identify and connect with the correct appliance.
•
If the management subnet you are connected to has a DHCP server deployed, the CIMC will automatically receive an IP address. This address will be displayed during initial bootup and can be seen from a serial console connection or a VGA screen.
•
If the management subnet you are connected to does not have a DHCP server, you must enter a static IP address by entering the CIMC configuration setup during bootup. To do this, press <F8> during initial bootup. After the address is set, the CIMC GUI and ssh connections will be available.
For more information about the KVM console, see the "Starting the KVM Console" section in the Cisco UCS Manager GUI Configuration Guide.
Using Virtual Media to Install or Recover Cisco NGA
To upgrade or recover Cisco NGA you can use the Cisco Image Management Controller to map the Cisco NGA ISO file to the virtual media CD. No CD/DVD is shipped with the product. You must log in with user or admin privileges to perform this task.
Step 1
Download the ISO file from Cisco.com (where the Cisco NGA images are located).
Step 2
Log into web interface (default: admin/password) using your web browser.
For more information about configuring virtual media using the CIMC, see Set up CIMC for the UCS C-Series Server.
Step 3
Click Launch KVM Console (requires Java).
Step 4
In the Java applet, click the Virtual Media tab.
Step 5
Click Add Image and select the ISO file.
Step 6
Check Mapped in Client View for the newly created drive.
Step 7
Log into web interface, click Power Cycle Server.
The appliance will boot up from the mapped ISO image and will stop at the Helper Utility menu.
Step 8
Click the KVM tab in the Java applet.
Step 9
Choose one of these options:
For details on how to set up virtual media for this product (which is preinstalled on a UCS server), see "Configuring Virtual Media" in Cisco UCS C-Series Servers Integrated Management Controller GUI Configuration Guide at http://www.cisco.com/en/US/docs/unified_computing/ucs/c/sw/gui/config/guide/1.4.1/b_Cisco_UCS_C-Series_GUI_Configuration_Guide_141_chapter_0110.html#topic_04C1A0A98E0841D797DBD5D4149607F9.
Reference Appendix Updates
The Cisco NGA does not have support for certain NetFlow v5 fields. It will export a value of zero for these fields. In Table B-3, Configure Records Window Fields, the following routing features are not supported in Cisco NGA:
–
SRC_AS, DST_AS
–
BGP_NEXT_HOP
–
SRC_MASK, DST_MASK
Product Documentation
The Cisco NetFlow Generation Appliance product documentation supports Hardware Releases 3140 and 3240.

Note
We sometimes update the documentation after original publication. Therefore, you should review the documentation on Cisco.com for any updates.
You can view the marketing and user documents for Cisco NGA 1.0 (2) at: http://www.cisco.com/go/nga
The following document lists the documents available for Cisco NGA 1.0 (2):
http://www.cisco.com/en/US/products/ps12508/products_documentation_roadmaps_list.htmlRelated Documentation
This section provides information about other documentation related to the Cisco NetFlow Generation Appliance.
Cisco Nexus 7000 Series Switch
•
Cisco Nexus 7000 Series NX-OS System Management Configuration Guide, Release 5.x
•
SPAN Configuration on a Nexus 7000 Series Switches
Cisco Nexus 5000 Series Switch
•
Cisco Nexus 5000 Series NX-OS Software Configuration Guide
Cisco Nexus 3000 Series Switch
•
Cisco Nexus 3000 Series NX-OS Fundamentals Configuration Guide (for SPAN configuration details)
Obtaining Documentation and Submitting a Service Request
For information on obtaining documentation, submitting a service request, and gathering additional information, see the monthly What's New in Cisco Product Documentation, which also lists all new and revised Cisco technical documentation, at the following URL:
http://www.cisco.com/en/US/docs/general/whatsnew/whatsnew.html
Subscribe to the What's New in Cisco Product Documentation as a Really Simple Syndication (RSS) feed and set content to be delivered directly to your desktop using a reader application. The RSS feeds are a free service and Cisco currently supports RSS Version 2.0.
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback