Cisco IOS WAP Gateway
Available Languages
Table Of Contents
Related Features and Technologies
Supported Standards, MIBs, and RFCs
Configuring a WAP Gateway Interface
Configuring Customer-Supplied User Authentication on the WAP Gateway
Configuring a Proxy List on the WAP Gateway
Configuring Security Features on the WAP Gateway
Configuring a WAP Gateway on a Multifunction Access Server
Specifying How the WAP Gateway Locates Content Servers
Verifying the Cisco IOS WAP Gateway
Monitoring and Maintaining the Cisco IOS WAP Gateway
WAP Gateway Interface Configuration Example
Customer-Supplied User Authentication Configuration Example
Proxy List Configuration Example
WAP Security Features Configuration Example
Content Server Location Configuration Example
wap http maximum header-length
Cisco IOS WAP Gateway
Feature History
This document describes the Cisco IOS WAP Gateway feature in Cisco IOS Release 12.2(2)XR. It includes the following sections:
•
Supported Standards, MIBs, and RFCs
•
Monitoring and Maintaining the Cisco IOS WAP Gateway
Feature Overview
The Cisco IOS WAP Gateway is a software feature developed in compliance with Wireless Application Protocol (WAP) version 1.2. The software runs on the Cisco 3640 and 3660 routers. A Cisco router can be configured either as a dedicated gateway server, or as a multifunction box in conjunction with other Cisco IOS features.
The Cisco IOS WAP Gateway feature is an implementation of the gateway component of the WAP architecture. Companies can deploy the gateway to offer mobile employees and partners access to company-specific WAP content that resides on internal web servers. In the WAP architecture, WAP security exists from the client device to the gateway but not through to the WAP content server. The Cisco IOS WAP Gateway feature can be implemented on a trusted server behind the company firewall, at which point it can access secure web content servers.
WAP is a standard for the presentation and delivery of wireless information and telephony services on wireless devices. Using an architecture based on the established WWW model, WAP defines a set of protocols designed for use with mobile telephone technology and wireless devices.
WAP was developed and is promoted by the WAP Forum. Mobile wireless devices containing WAP browsers are available from most mobile device manufacturers.
WAP is designed to be independent of both the bearer technology and the device. WAP protocols can operate with many bearer technologies such as code division multiple access (CDMA), which is currently prevalent in the United States; global system for mobile communications (GSM), which is popular in Europe; and the GSM feature known as general packet radio service (GPRS), which is starting to be deployed and provides higher-speed data services. The major bearer technologies are all supported by WAP.
Figure 1 shows how the WAP gateway functions with the various protocols used to request and deliver data between a client wireless device, the Cisco IOS WAP Gateway, and a web content server. The client wireless device—a mobile phone in Figure 1—contains a WAP browser that can display Wireless Markup Language (WML) and execute Wireless Markup Language Scripts (WMLS). WML is derived from eXtensible Markup Language (XML) but is functionally equivalent to HTML, and it is designed to display WAP content on the small screens of mobile devices that can display only four or five lines of text plus some icons or basic graphics. Wireless mobile devices typically have memory limitations compared to the average PC.
Figure 1 Functionality of the Cisco IOS WAP Gateway
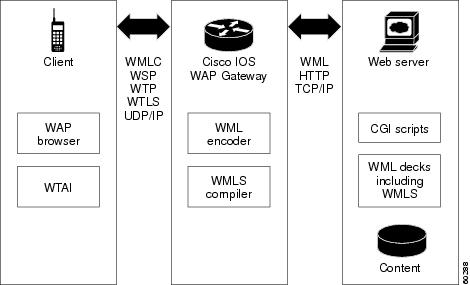
The mobile phone in Figure 1 also operates the Wireless Telephony Application Interface (WTAI), which gives access to the usual telephone capabilities such as phone books and dialing. WTAI allows telephone functionality to be controlled by WMLS. One use of this feature is to make the handset place a call to a telephone number that a WAP directory application has just retrieved and displayed on the screen.
When the client wireless device in Figure 1 initiates a request for WAP content, the request is forwarded to the WAP gateway via the wireless network provider that the client is using. Protocols used in the communication between the client and the gateway may include Wireless Session Protocol (WSP), Wireless Transaction Protocol (WTP), and Wireless Transport Layer Security (WTLS). All these protocols are optimized for use with wireless devices.
The WAP gateway in Figure 1 receives the request for WAP content from the wireless device and creates or reuses a session to the web server and requests content using Hypertext Transfer Protocol (HTTP). When the content is supplied to the gateway, it uses the WML encoder to compress the information and, if required, the gateway uses the WMLS compiler to compile the request before sending the WAP content back to the client device. Compression is achieved using a process called tokenisation.
The web content server in Figure 1 can be an existing web content server using standard URLs and Common Gateway Interface (CGI) scripts, but the content destined for client wireless devices must be in WML format. The WAP browser in the wireless device cannot display content written in HTML. Communication between the gateway and the web server occurs through conventional protocols such as HTTP and the TCP/IP protocol stack.
Benefits
Leverage Existing Equipment and Expertise
You can integrate WAP services into your existing IP network infrastructure using existing equipment because the WAP gateway can run on the Cisco 3640 and 3660 routers and will even run as part of a multifunction router. The WAP gateway software uses new and modified commands at the Cisco IOS command-line interface (CLI), but the existing commands for configuring an interface or verifying the configuration should be familiar to Cisco customers.
Secure WAP Access to Internal Web Content
Companies can make intranet services available to employees and partners via the WAP gateway without compromising security. The Cisco IOS WAP Gateway feature can run on a trusted router within the firewall and access WAP content held on an internal server.
The WAP gateway uses WTLS Class 1 security, which provides encryption between the wireless device and the gateway, and is widely supported by the wireless devices currently on the market.
Customers can implement their own user authentication methods by configuring the wap authentication service and associated optional commands.
Support for Microbrowsers
The Cisco IOS WAP Gateway feature implements the version 1.2 standards from the WAP Forum and will support all WAP microbrowsers that also implement these standards. Current and future WAP-enabled wireless devices will work with the gateway if they implement the WAP Forum version 1.2 standards.
Related Features and Technologies
•
V.110/WAP Access Solution
•
Cisco IOS Server Load Balancing (SLB)
Related Documents
•
Cisco IOS IP Command Reference, Volume 1 of 3: Addressing and Services, Release 12.2
•
Cisco IOS IP Command Reference, Volume 2 of 3: Routing Protocols, Release 12.2
•
Cisco IOS IP Command Reference, Volume 3 of 3: Multicast, Release 12.2
•
Cisco IOS IP Configuration Guide, Release 12.2
Supported Platforms
•
Cisco 3640
•
Cisco 3660
Platform Support Through Feature Navigator
Cisco IOS software is packaged in feature sets that support specific platforms. To get updated information regarding platform support for this feature, access Feature Navigator. Feature Navigator dynamically updates the list of supported platforms as new platform support is added for the feature.
Feature Navigator is a web-based tool that enables you to quickly determine which Cisco IOS software images support a specific set of features and which features are supported in a specific Cisco IOS image.
To access Feature Navigator, you must have an account on Cisco.com. If you have forgotten or lost your account information, send a blank e-mail to cco-locksmith@cisco.com. An automatic check will verify that your e-mail address is registered with Cisco.com. If the check is successful, account details with a new random password will be e-mailed to you. Qualified users can establish an account on Cisco.com by following the directions at http://www.cisco.com/register.
Feature Navigator is updated when major Cisco IOS software releases and technology releases occur. As of May 2001, Feature Navigator supports M, T, E, S, and ST releases. You can access Feature Navigator at the following URL:
http://www.cisco.com/go/fn
Supported Standards, MIBs, and RFCs
Standards
The Cisco IOS WAP Gateway feature conforms to all the mandatory standards requirements set out in the WAP 1.2 specifications created by the WAP Forum. All mandatory and certain optional features have been implemented. Your Cisco sales representative can provide a product bulletin containing the WAP Server Implementation Conformance Statement (WICS) for the Cisco IOS WAP Gateway feature.
MIBs
No new or modified MIBs are supported by this feature.
To obtain lists of supported MIBs by platform and Cisco IOS release, and to download MIB modules, go to the Cisco MIB website on Cisco.com at the following URL:
http://www.cisco.com/public/sw-center/netmgmt/cmtk/mibs.shtml
RFCs
•
RFC 2068, Hypertext Transfer Protocol—HTTP 1.1
•
RFC 1738, Uniform Resource Locators (URL)
Prerequisites
WML Content Access
You must ensure that you have access to a web content server that contains WML and WMLS files that will be displayed on the WAP-enabled wireless devices. The software running the web server must be configured with WAP Multipurpose Internet Mail Extension (MIME) types to handle the various types of WAP files. We recommend that you configure the web server software to return an index.wml page when a URL is requested without specifying a page, because it can save the user some keystrokes on a WAP phone.
Client Software
The Cisco IOS WAP Gateway feature implements the version 1.2 standards from the WAP Forum and will support all WAP microbrowsers that also implement these standards. You must confirm that all your client wireless devices implement the 1.2 standards and are configured to access the WAP gateway.
WAP-enabled wireless devices have many different menu configurations but two parameters must be configured on each device that will access the Cisco IOS WAP Gateway. The IP address that must be entered in the WAP browser is the primary IP address of the interface on which the WAP gateway is configured. The User Datagram Protocol (UDP) port number being used by the wireless device must correspond to the protocol stack configured on the WAP gateway.
Configuration Tasks
See the following sections for configuration tasks for the Cisco IOS WAP Gateway feature. Each task in the list is identified as either required or optional:
•
Configuring a WAP Gateway Interface (required)
•
Configuring Customer-Supplied User Authentication on the WAP Gateway (optional)
•
Configuring a Proxy List on the WAP Gateway (optional)
•
Configuring Security Features on the WAP Gateway (optional)
•
Configuring a WAP Gateway on a Multifunction Access Server (optional)
•
Specifying How the WAP Gateway Locates Content Servers (optional)
•
Verifying the Cisco IOS WAP Gateway (optional)
Configuring a WAP Gateway Interface
The Cisco IOS WAP Gateway feature is configured on only one interface but it operates over all physical interfaces to take advantage of any redundancy and to maximize availability. The interface on which the WAP gateway is configured can be a physical or loopback (virtual) interface. The gateway uses the primary IP address of this interface as the IP address for all WAP traffic, regardless of the actual physical interface over which the packets arrive or depart. To reduce the dependence on a physical interface that may be subject to physical connection issues or network failures, we recommend that the WAP gateway be configured on a loopback interface.
To enable the Cisco IOS WAP Gateway feature on a router, use the following commands beginning in global configuration mode:
Configuring Customer-Supplied User Authentication on the WAP Gateway
The Cisco IOS WAP Gateway feature contains a feature and associated commands that allow the device browser to be redirected to a URL where customer-supplied user authentication can occur before the gateway will display any requested web content.
The user authentication feature can be used to supplement the static WAP username and password provided by most browsers. Static passwords may not provide the required level of security for an enterprise where all network access is controlled using one-time passwords. In this environment, the user must change the password on the WAP-enabled device before establishing each WAP session. The navigation on the device is tedious and may discourage use of the service. Using some form of initial group ID and password on the WAP-enabled device, and implementing a customer-supplied user authentication on the gateway, could allow the one-time password to be verified using WAP itself. A filtering mechanism may be employed on the firewall to ensure that the group ID initial requests access only the WAP gateway.
To configure this optional task, use the following commands in global configuration mode as needed. The authentication is activated when a new session begins.
Configuring a Proxy List on the WAP Gateway
Using a proxy list allows the WAP gateway to determine which URL requests should be handled directly and which should be forwarded to a specified HTTP proxy server. The gateway searches through the proxy list in the order in which each filter request is entered when processing a request for a page. The gateway tests a page request against each line until a match is found. If no match is found the page request is serviced directly. An asterisk (*) wildcard can be used in the proxy filter entries.
Proxy servers are servers that will process information for another server and are sometimes used for security reasons to keep external requests from reaching internal servers. Proxy servers can also help ease performance issues because they take some of the load off other servers.
To create a proxy list, use the following command in global configuration mode. The proxy list records are searched in the order in which they are entered.
Configuring Security Features on the WAP Gateway
The Cisco IOS WAP Gateway feature uses WTLS Class 1 security. Several commands have been implemented in the software to allow the customer to configure the behavior of the gateway.
The gateway implements a number of different encryption, hash, and key-exchange algorithms. The use of each algorithm can be explicitly enabled or disabled. Deciding which algorithm to enable may depend on your company policy or the set of algorithms supported by the wireless devices with which the WAP gateway must communicate. Many wireless devices only support a subset of the available algorithms. While a WAP session is being established, the WAP-enabled device proposes the use of an algorithm and the gateway agrees to the proposal if it supports the proposed algorithm. That algorithm is then enabled. Unless you have a specific security requirement, the default configurations of both the wireless devices and the Cisco IOS WAP Gateway will usually work for all wireless devices.
For each type of algorithm you can select different strengths of security. A shorter key length is easier to compute and will impose less overhead on the processor than a longer key length, but a shorter key length can compromise security. The level of security you need to configure will be determined by the type of information that can be accessed through the gateway. Confidential corporate information requires a higher level of security than information about the weather, for example, although having current access to such information may be invaluable.
Timeout intervals for idle WTLS sessions or connections can also be configured. A balance must be found between configuring a shorter interval in the interests of security and allowing a reasonable interval that stops the user from constantly needing to reauthenticate or reconnect when the interval expires.
To configure security options, use any or all the following optional commands in global configuration mode as needed:
Configuring a WAP Gateway on a Multifunction Access Server
The WAP gateway can run either on a dedicated router or on a multifunction router. One example of a multifunction router would be to run the Cisco IOS WAP Gateway software on an access server. The ability to enable other Cisco IOS features will depend on the CPU and memory in the router. Feature enablement will affect the performance of the router. To run the WAP gateway on a multifunction access server, note the following configuration tips:
•
Refer to the Cisco IOS Dial Technologies Configuration Guide, Release 12.2 for configuration scenarios.
•
Configure the gateway on a loopback (virtual) interface for enhanced availability.
Specifying How the WAP Gateway Locates Content Servers
When a wireless device requests a web page via the WAP gateway, the Cisco IOS software must determine where to find the requested web page. A number of Cisco IOS commands can be configured to help reduce the time required to access the requested web page.
To specify multiple DNS servers and associated features, use any or all of the following commands in global configuration mode:
Verifying the Cisco IOS WAP Gateway
Verifying that the WAP gateway is working involves checking the configuration of the wireless devices and web servers. Those tasks may not be possible at the same location as the router that is acting as the WAP gateway. Some Cisco IOS commands, however, can be run on the router to determine if the correct WAP parameters are configured and running. Depending on the level of security required, one or more of the WAP protocol stacks are configured. Each WAP protocol stack is assigned a specific port number from 9200 through 9203. When the router is listening on a port number, use the show ip sockets EXEC command to display the port number information.
To verify that the Cisco IOS WAP Gateway feature is running, perform the following steps:
Step 1
Enter the show wap EXEC command to display the settings of all the WAP parameters. The values of all the WAP parameters, even those set to their default settings, are displayed.
Router# show wapCisco IOS Wireless Application Protocol Gateway parametersWAP Gateway is enabled on interface Loopback0WAP services available are: secure-cl secure-coUP browser-specific settings:'device:home' is substituted with : 'http://www.company-name.com/wapserver/i''device:base' is substituted with : 'http://www.company-name.com/wapserver''x-up-subno' header is appended with 'gateway.company-name.com'HTTP headers are wrapped after 80 bytesUser authentication service is 'http://www.company-name.com/auth/login.wml'User authentication completed is 'http://www.company-name.com/auth/scripts/validate.cgi'User authentication prefix is 'http://www.company-name.com/auth/scripts'User authentication timeout is set to 20 minutesWSP maximum sessions is set to 1000WSP session timeout is set to 5 minutesWTLS master key timeout is set to 1 dayWTLS session timeout is set to 1 hour 30 minutesWTLS connection timeout is set to 1 hour 30 minutesWTLS handshake timeout is set to 5 minutesWTLS Encryption Algorithms:RC5-CBC-128 - enabledRC5-CBC-56 - enabledRC5-CBC-40 - enabledWTLS Hash Algorithms:MD5-128 - disabledMD5-80 - disabledMD5-40 - disabledSHA-160 - enabledSHA-80 - enabledSHA-40 - enabledSHA-XOR-40 - disabledSHA-0 - disabledWTLS Key Exchange Algorithms:DH-ANON-UNRESTRICTED - enabledDH-ANON-768 - enabledDH-ANON-512 - enabledRSA-ANON-UNRESTRICTED - enabledRSA-ANON-768 - enabledRSA-ANON-512 - enabledProxy list is:*.company-name.com*.company-name.com:**.*->proxy.company-name.comStep 2
Enter the show ip sockets EXEC command to display the ports that are being used. Ports 9202 and 9203 are in use, confirming the configuration of the wap command.
Router# show ip socketsProto Remote Port Local Port In Out Stat TTY OutputIF17 0.0.0.0 0 172.20.1.1 67 0 0 489 017 10.1.0.2 49998 172.20.1.1 9203 0 0 B1 017 0.0.0.0 0 172.20.1.1 9202 0 0 B1 0Step 3
Enter the show wap statistics EXEC command to show that traffic is being generated. A wireless phone or phone-emulator software on a PC, configured to access the WAP gateway, will generate traffic. Run this command several times while generating the traffic to ensure that the counters are being updated.
Router# show wap statisticserrors requests responses sessions sessions-HWM rx-udp tx-udp0 2614 2614 0 2 5151 2894timers: 0number of memory pools: 17
Troubleshooting Tips
WAP Gateway
The Cisco IOS WAP Gateway feature introduces a new EXEC mode command, debug wap, to enable diagnostic output concerning various events relating to the operation of the WAP gateway to be displayed on a console. The debug wap command is intended only for troubleshooting purposes because the volume of output generated by the software can result in severe performance degradation on the router. To minimize the impact of using the debug wap commands, perform the following steps:
Step 1
Attach a console directly to the router running the WAP gateway.
Step 2
Enter the no logging console command in global configuration mode to disable all logging to the console terminal. To reenable logging to the console, use the logging console command in global configuration mode.
Step 3
Use Telnet to access a router port. Enter the enable command in EXEC configuration mode.
Step 4
Enter the terminal monitor command in global configuration mode and enter the necessary debug wap commands. Try to enter only specific debug wap commands to isolate the output to a certain subcomponent and minimize the load on the processor. Use the detailed keyword to generate more detailed debug information on specified subcomponents. To disable logging on the virtual terminal, enter the no terminal monitor command.
Step 5
Enter the specific no debug wap command when you are finished.
This procedure will minimize the load on the router created by the debug wap commands because the console port is no longer generating character-by-character processor interrupts. If you cannot connect to a console directly, you can run this procedure via a terminal server. If you must break the Telnet connection, however, you may not be able to reconnect because the router may be unable to respond due to the processor load of generating the debug wap output.
WAP Wireless Devices
Ensure that your WAP-enabled wireless device is configured with the appropriate WAP parameters. The IP address that is entered in the WAP browser in the wireless device is the primary IP address of the interface on which the WAP gateway is configured. The UDP port number being used by the wireless device must correspond to the protocol stack configured on the WAP gateway.
Web Content Servers
Ensure that the content server contains the relevant WML files and scripts and can be accessed by the router running the Cisco IOS WAP Gateway feature. The content server software must be configured to register the various WAP MIME types.
Monitoring and Maintaining the Cisco IOS WAP Gateway
To monitor and maintain the Cisco IOS WAP Gateway feature, use the following commands in EXEC mode:
Configuration Examples
This section provides the following configuration examples:
•
WAP Gateway Interface Configuration Example
•
Customer-Supplied User Authentication Configuration Example
•
Proxy List Configuration Example
•
WAP Security Features Configuration Example
•
Content Server Location Configuration Example
WAP Gateway Interface Configuration Example
In the following example, the WAP gateway is enabled on a loopback (virtual) interface, the secure connectionless protocol stack is configured, and the secure connection-oriented protocol stack is configured:
interface Loopback0ip address 172.20.1.1 255.255.0.0wap secure-cl secure-coCustomer-Supplied User Authentication Configuration Example
In the following example, customer-supplied user authentication is enabled, a file called login.wml prompts the user for a username and password, and a CGI script called validate.cgi validates the username and password and displays a page with an HTTP status indicating success or failure:
wap authentication service http://www.company-name.com/auth/login.wmlwap authentication completed http://www.company-name.com/auth/scripts/validate.cgiwap authentication prefix http://www.company-name.com/auth/scripts/The first command causes the gateway to run the customer-supplied authentication procedure in login.wml whenever a new session is started. Instead of serving the first page request on the session, the browser will be re-directed to the file called login.wml. This file contains WML, which prompts the user for a username and a password. The username and password parameters that are entered by the user are sent to the CGI script called validate.cgi.
The second command registers that validate.cgi is the file that must be successfully retrieved to indicate to the gateway that the authentication process was successful. This CGI script validates the username and password using a user-specified mechanism. The CGI script returns WML, which displays the first customer-supplied authentication screen, along with a message to indicate whether authentication was successful.
The third command permits pages in the specified directory to be accessed during the authentication process. The specified prefix can be used, for example, to allow the authentication procedure to display a corporate logo on the screen or to operate a more complex authentication procedure using multiple files.
Proxy List Configuration Example
In the following example, a sequence of proxy list records is created. The first record captures all the local domain requests and services them directly. The second record captures local domain requests with a specified port number and services them directly. The third record specifies both an HTTP server and a name of a proxy server to which the requests matching the HTTP server are forwarded. Note that the first two filter records will capture all the local page requests except those requests that do not specify a company-name host. The third filter record captures all other requests containing a dot in the domain name and forwards the requests to the specified proxy server. If the gateway does not find a match in the list, the page request is serviced directly:
wap proxy-list *.company-name.comwap proxy-list *.company-name.com:*wap proxy-list *.* proxy.company-name.comWAP Security Features Configuration Example
In the following example, the gateway is being configured to operate all the encryption and key-exchange algorithms, but only a selection of the hash algorithms. WTLS timeout parameters are all set to an interval in seconds that is different from their default values.
wap wtls encryption allwap wtls hash sha-40 sha-80 sha-160wap wtls key-exchange allwap wtls timeout key 86400wap wtls timeout session 5400wap wtls timeout connection 5400wap wtls timeout handshake 300Content Server Location Configuration Example
In the following example, a default domain name, some host names, and two DNS servers are configured:
ip domain-name company-name.comip host web.company-name.com 10.1.1.10ip host wapauth.company-name.com 172.21.1.10ip name-server 172.21.1.100ip name-server 10.3.1.100Command Reference
This section documents new commands. All other commands used with this feature are documented in the Cisco IOS Release 12.2 command reference publications.
•
wap
•
wap http maximum header-length
clear wap statistics
To reset the Wireless Application Protocol (WAP) gateway counters, use the clear wap statistics command in EXEC mode.
clear wap statistics
Syntax Description
This command has no arguments or keywords.
Command Modes
EXEC
Command History
Usage Guidelines
WAP gateway counters accumulate during operation and can be useful for monitoring. To establish baseline statistics, use the clear wap statistics command at the start of the monitoring period to ensure that the counters are reset.
Examples
The following example shows all the WAP gateway counters being reset:
Router# clear wap statisticsdebug wap
To display debug messages for the Wireless Application Protocol (WAP) gateway, use the debug wap command in EXEC mode. To turn off debugging, use the no form of this command.
debug wap {dns | gateway | html-to-wml | http | udp | wml | wsp | wtls | wtp} [detailed]
no debug wap {dns | gateway | html-to-wml | http | udp | wml | wsp | wtls | wtp} [detailed]
Syntax Description
Command Modes
EXEC
Command History
Usage Guidelines
To minimize the load on the processor, use specific debug wap commands. Use the show debugging EXEC command to keep track of which debug commands are currently operational. Use the undebug EXEC command to turn off all debugging options.

CautionThe debug wap command is intended for troubleshooting and should not be used during normal operation. The output generated may create severe performance degradation.
Examples
The following is sample output from the following debug wap commands:
Router# debug wap allJun 26 09:49:56.683: WAP wtls: rx checksum 68 41 3D CAJun 26 09:49:56.683: WAP wtls: Proposed cipher suite 3, 3Jun 26 09:49:56.683: WAP wtls: requested cipher suite. bulk=3, mac=3Jun 26 09:49:56.683: WAP wtls: Proposed cipher suite 3, 2Jun 26 09:49:56.683: WAP wtls: requested cipher suite. bulk=3, mac=2Jun 26 09:49:56.683: WAP wtls: Proposed cipher suite 3, 1Jun 26 09:49:56.683: WAP wtls: requested cipher suite. bulk=3, mac=1Jun 26 09:49:56.683: WAP wtls: Proposed cipher suite 2, 3Jun 26 09:49:56.683: WAP wtls: requested cipher suite. bulk=2, mac=3Jun 26 09:49:56.683: WAP wtls: Proposed cipher suite 2, 2Jun 26 09:49:56.683: WAP wtls: requested cipher suite. bulk=2, mac=2Jun 26 09:49:56.683: WAP wtls: Proposed cipher suite 1, 3Jun 26 09:49:56.683: WAP wtls: requested cipher suite. bulk=1, mac=3Jun 26 09:49:56.683: WAP wtls: Proposed cipher suite 1, 2Jun 26 09:49:56.683: WAP wtls: requested cipher suite. bulk=1, mac=2Jun 26 09:49:56.683: WAP wtls: Proposed Key Exchange 8 (0)Jun 26 09:49:56.683: WAP wtls: Unsupported Key Exchange algorithm 8 was proposedJun 26 09:49:56.683: WAP wtls: Proposed Key Exchange 10 (0)Jun 26 09:49:56.683: WAP wtls: Unsupported Key Exchange algorithm 10 was proposedJun 26 09:49:56.683: WAP wtls: Proposed Key Exchange 9 (0)Jun 26 09:49:56.683: WAP wtls: Unsupported Key Exchange algorithm 9 was proposedJun 26 09:49:56.683: WAP wtls: Proposed Key Exchange 5 (0)Jun 26 09:49:56.683: WAP wtls: Proposed Key Exchange 7 (0)Jun 26 09:49:56.683: WAP wtls: Proposed Key Exchange 6 (0)Jun 26 09:49:56.683: WAP wtls: Selected algorithms bulk cipher algorithm 3Selected mac algorithm 3Selected compression mode 0Selected key exchange 5(0)Jun 26 09:50:03.431: WAP wtls: rx checksum 96 2C 37 2CJun 26 09:50:03.631: WAP wtls: Computing master secretJun 26 09:50:03.631: WAP wtls: rx checksum C0 01 02 00Jun 26 09:50:03.631: WAP wtls: rx checksum 78 CA EA 87Jun 26 09:50:03.631: WAP wtls: Verify finish succeededJun 26 09:50:03.635: WAP wtls: Going to Opening state...Jun 26 09:50:04.679: WAP wtls: rx checksum 89 90 CF 20Jun 26 09:50:04.679: WAP wtp: tr_invoke_res calledJun 26 09:50:05.679: WAP wtls: rx checksum C7 DF EC A5Jun 26 09:50:05.803: WAP wtls: rx checksum 4D 02 07 3BJun 26 09:50:05.807: WAP wtp: tr_invoke_res calledJun 26 09:50:05.827: WAP wml: squished 610 into 540The following is sample output from the debug wap all detailed command:
Router# debug wap all detailedJun 26 09:56:43.415: WAP udp: < udp:9203 75 1.1.0.2:49998C3 00 00 00 46 01 00 43 01 3B 38 6A 58 4E 27 48C6 B0 BF 29 18 EF 41 3E 4D 08 A3 92 DD 1D 92 9330 4C 00 12 08 00 00 0A 00 00 09 00 00 05 00 0007 00 00 06 00 00 00 00 0E 03 03 03 02 03 01 0203 02 02 01 03 01 02 01 00 02 03Jun 26 09:56:43.415: WAP wtls: rx checksum A1 76 D8 68Jun 26 09:56:43.415: WAP wtls: Client Hello received 0Jun 26 09:56:43.415: WAP wtls: SEC_Create.ind receivedJun 26 09:56:43.415: WAP wtls: Proposed cipher suite 3, 3Jun 26 09:56:43.415: WAP wtls: requested cipher suite. bulk=3, mac=3Jun 26 09:56:43.415: WAP wtls: Proposed cipher suite 3, 2Jun 26 09:56:43.415: WAP wtls: requested cipher suite. bulk=3, mac=2Jun 26 09:56:43.415: WAP wtls: Proposed cipher suite 3, 1Jun 26 09:56:43.415: WAP wtls: requested cipher suite. bulk=3, mac=1Jun 26 09:56:43.415: WAP wtls: Proposed cipher suite 2, 3Jun 26 09:56:43.415: WAP wtls: requested cipher suite. bulk=2, mac=3Jun 26 09:56:43.415: WAP wtls: Proposed cipher suite 2, 2Jun 26 09:56:43.415: WAP wtls: requested cipher suite. bulk=2, mac=2Jun 26 09:56:43.415: WAP wtls: Proposed cipher suite 1, 3Jun 26 09:56:43.415: WAP wtls: Proposed Key Exchange 9 (0)Jun 26 09:56:43.415: WAP wtls: Unsupported Key Exchange algorithm 9 was proposedJun 26 09:56:43.415: WAP wtls: Proposed Key Exchange 5 (0)Jun 26 09:56:43.415: WAP wtls: Proposed Key Exchange 7 (0)Jun 26 09:56:43.415: WAP wtls: Proposed Key Exchange 6 (0)Jun 26 09:56:43.415: WAP wtls: Selected algorithms bulk cipher algorithm 3Selected mac algorithm 3Selected compression mode 0Selected key exchange 5(0)Jun 26 09:56:49.611: WAP wtls: Computing master secretJun 26 09:56:49.611: WAP wtls: master secret D7 63 E2 E4 17 A4 30 2C 6E 99 27 42DF 70 74 D5 08 74 61 9CJun 26 09:56:49.611: WAP wtls: New receiving hmac key 8B AD 55 F2 1A 19 1A FD DDF9 E7 17 51 AF 9D 92 B7 50 FD 8AJun 26 09:56:49.615: WAP wtls: New receiving key B8 98 91 B9 28 6A F7 D1 18 1115 E4 F5 C1 C9 BAJun 26 09:56:49.615: WAP wtls: New receiving iv EB 99 F6 0A AF ED BA 1CJun 26 09:56:49.615: WAP wtls: decrypting with iv EB 99 F6 0A AF ED BA 1CJun 26 09:56:49.615: WAP wtls: decrypting with secret B8 98 91 B9 28 6A F7 D1 1811 15 E4 F5 C1 C9 BAJun 26 09:56:49.615: WAP wtls: Finished receivedJun 26 09:56:49.615: WAP wtls: Creating finished on 378 bytes of handshakeJun 26 09:56:49.615: WAP wtls: HandshakeJun 26 09:56:51.663: WAP wtp: Rcv Invoke 32770Jun 26 09:56:51.663: WAP wtp: StateJun 26 09:56:51.663: WAP wsp: Supplier invoke 2Jun 26 09:56:51.663: WAP dns: Looking up 172.20.1.1Jun 26 09:56:51.663: WAP dns: Translated 172.20.1.1 to 172.20.1.1:0Jun 26 09:56:51.663: WAP http: processing send in state 0Jun 26 09:56:51.663: WAP http: connecting to 172.20.1.1:80Jun 26 09:56:51.663: WAP http: waiting to connect...Jun 26 09:56:51.667: WAP http: HTTP Request:GET /a.wml HTTP/1.1user-agent: Nokia7110/1.0 (04.84)accept-charset: iso-8859-1,utf-8,iso-10646-ucs-2accept-language: enaccept:text/vnd.wap.wml,application/vnd.wap.wmlc,text/vnd.wap.wmlscript,application/vnd.wap.wmlscriptcaccept: image/vnd.wap.wbmp,application/vnd.wap.wtls-ca-certificate,text/plain,text/html; q=0.1if-modified-since: Jul 08 2006 09:34:02X-Network-Info: 10.1.0.2:49998host: 172.20.1.1"http://www.wapforum.org/DTD/wml_1.1.xml"><wml><card id="card1" title="Currency" newcontext="true"><p>Amount: <input format="*N" name="amount" title="Amount:"/>From: <select name="from" value="USD" title="From:"><option value="DEM">German Mark</option><option value="FRF">French Franc</option>...Jun 26 09:56:51.675: WAP http: ...Jun 26 09:56:51.683: WAP wml: substituting for "amount"Jun 26 09:56:51.683: WAP wml: substituting for "German Mark"Jun 26 09:56:51.683: WAP wml: substituting for "French Franc"Jun 26 09:56:51.683: WAP wml: substituting for "Finnish Markka"Jun 26 09:56:51.683: WAP wml: substituting for "US Dollar"Jun 26 09:56:51.687: WAP wml: substituting for "currency.wmls#"Jun 26 09:56:51.687: WAP wml: substituting for "conversion"Jun 26 09:56:51.687: WAP wml: substituting for "card1_help"Jun 26 09:56:51.687: WAP wml: substituting for "currency.wmls#"Jun 26 09:56:51.687: WAP wml: squished 610 into 540Related CommandsJ
show debugging
Displays the state of each debugging option.
undebug
Turns off debugging displays.
show wap
To display the values of all the Wireless Application Protocol (WAP) gateway parameters, use the show wap command in EXEC mode.
show wap [statistics]
Syntax Description
Defaults
By default, all WAP gateway parameter values are displayed.
Command Modes
EXEC
Command History
Usage Guidelines
If no arguments or keywords are specified, the gateway displays the values of all the WAP parameters, even those that are set to their default. Use the show running-config EXEC command to display WAP gateway parameters that have been changed from their default values in the current configuration running on the router.
Examples
The following is sample output from the show wap command:
Router# show wapCisco IOS Wireless Application Protocol Gateway parametersWAP Gateway is enabled on interface Loopback0WAP services available are: secure-cl secure-coUP browser-specific settings:'device:home' is substituted with : 'http://www.company-name.com/wapserver/index.wml''device:base' is substituted with : 'http://www.company-name.com/wapserver''x-up-subno' header is appended with 'gateway.company-name.com'HTTP headers are wrapped after 80 bytesUser authentication service is 'http://www.company-name.com/wapserver/authen_service.wml'User authentication completed is 'http://www.company-name.com/wapserver/authen_completed.wml'User authentication prefix is 'http://www.company-name.com/wapserver/pages'User authentication timeout is set to 20 minutesWSP maximum sessions is set to 1000WSP session timeout is set to 5 minutesWTLS master key timeout is set to 1 dayWTLS session timeout is set to 1 hour 30 minutesWTLS connection timeout is set to 1 hour 30 minutesWTLS handshake timeout is set to 3 minutesWTLS Encryption Algorithms:RC5-CBC-128 - enabledRC5-CBC-56 - enabledRC5-CBC-40 - enabledWTLS Hash Algorithms:MD5-128 - disabledMD5-80 - disabledMD5-40 - disabledSHA-160 - enabledSHA-80 - enabledSHA-40 - enabledSHA-XOR-40 - disabledSHA-0 - disabledWTLS Key Exchange Algorithms:DH-ANON-UNRESTRICTED - enabledDH-ANON-768 - enabledDH-ANON-512 - enabledRSA-ANON-UNRESTRICTED - enabledRSA-ANON-768 - enabledRSA-ANON-512 - enabledProxy list is:*.company-name.com*.company-name.com:**.*->proxy.company-name.comTable 1 describes the significant fields shown in the display.
The following is sample output from the show wap statistics command:
Router# show wap statisticserrors requests responses sessions sessions-HWM rx-udp tx-udp0 2614 2614 0 2 5151 2894timers: 0number of memory pools: 17Table 2 describes the significant fields shown in the display.
Related Commands
clear wap statistics
Resets the WAP gateway counters.
show running-config
Displays the current configuration.
wap
To enable the Wireless Application Protocol (WAP) gateway on an interface, use the wap command in interface configuration mode. To disable the WAP gateway, use the no form of this command.
wap {all | [cl] [co] [secure-cl] [secure-co]}
no wap {all | [cl] [co] [secure-cl] [secure-co]}
Syntax Description
Defaults
By default, the WAP gateway is not enabled.
Command Modes
Interface configuration
Command History
Usage Guidelines
The WAP gateway is configured only on one interface, but it operates over all physical interfaces to take advantage of any redundancy and to maximize availability. The interface on which the WAP gateway is configured can be a physical or loopback (virtual) interface. The gateway uses the primary IP address of this interface as the IP address for all WAP traffic regardless of the actual physical interface over which the packets arrive or depart. Use of a single IP address ensures that the WAP gateway will communicate correctly with WAP browsers, even when return traffic is routed over a different path and leaves the router via a different physical interface.
To reduce the dependence on a physical interface, which may be subject to physical connection issues or network failures, we recommend that the WAP gateway be configured on a loopback interface created for this purpose.
When the WAP gateway is disabled, it stops operating over all the interfaces on the router.
The WAP gateway can be configured to operate all the WAP protocol stacks or a list specifying one or more of the options. Determining which of the possible protocol stacks the WAP gateway will operate depends on the type of service or information that is being accessed via the WAP gateway. Information that is not confidential need not operate with the overhead of the secure protocol stacks. Confidential corporate information and credit card services require the secure protocol stacks. Each protocol stack operates over a different port.
Use the show wap EXEC command to display the interface on which WAP is enabled and to display which WAP services are available.

Note
WAP-enabled wireless devices must be configured in advance to use a protocol stack that is being operated by the WAP gateway because there is no method to negotiate between protocol stacks when a session is established. Not all WAP-enabled wireless devices support all the possible WAP protocol stacks.
Examples
The following example shows the WAP gateway being enabled on a loopback interface and configured to operate both types of secure WAP protocol stacks:
interface Loopback 0ip address 172.20.1.1 255.255.0.0wap secure-cl secure-coThe following example shows the WAP gateway being disabled:
interface Loopback 0no wap allRelated Commands
wap authentication completed
To specify the URL that must be successfully accessed to indicate to the Wireless Application Protocol (WAP) gateway that authentication was successful, use the wap authentication completed command in global configuration mode. To restore this parameter to its default value, use the no form of this command.
wap authentication completed url
no wap authentication completed
Syntax Description
Defaults
By default, the URL specified by the wap authentication service command is used.
Command Modes
Global configuration
Command History
Usage Guidelines
The wap authentication completed command is used with other authentication commands to enable a customer-supplied user authentication scheme to work with the WAP gateway.
If the wap authentication service command is configured, the WAP gateway will redirect the browser to the page configured by the wap authentication service command whenever a new session starts. The customer-supplied authentication process will then proceed and a page, specified by the wap authentication completed command, will be displayed if the authentication process is successful. Until the authentication process is successful, the WAP gateway will service only URLs specified by the wap authentication service, wap authentication completed, and wap authentication prefix commands, and all other page requests within that session will be denied.

Note
The authentication scheme cannot be run when the WAP gateway is operating the connectionless WSP protocol to communicate between the wireless device and the WAP gateway.
Examples
The following example shows the URL http://www.company-name.com/auth/scripts/validate.cgi being configured as the URL to be accessed to indicate to the WAP gateway that authentication was successful:
wap authentication completed http://www.company-name.com/auth/scripts/validate.cgiRelated Commands
wap authentication prefix
To specify a URL prefix that permits access to pages during the Wireless Application Protocol (WAP) customer-supplied user authentication process, use the wap authentication prefix command in global configuration mode. To disable use of the prefix, use the no form of this command.
wap authentication prefix url
no wap authentication prefix
Syntax Description
url
URL prefix used to permit access to pages during the WAP customer-supplied user authentication process. The URL prefix will usually be a directory but can be any valid URL.
Defaults
By default no prefix is defined.
Command Modes
Global configuration
Command History
Usage Guidelines
The wap authentication prefix command is used with other authentication commands to enable a customer-supplied user authentication scheme to work with the WAP gateway. The prefix URL is normally used to point to a directory from which other pages can be displayed during the authentication process.
If the wap authentication service command is configured, the WAP gateway will redirect the browser to the page configured by the wap authentication service command whenever a new session starts. The customer-supplied authentication process will then proceed and a page, specified by the wap authentication completed command, will be displayed if the authentication process is successful. Until the authentication process is successful, the WAP gateway will service only URLs specified by the wap authentication service, wap authentication completed, and wap authentication prefix commands, and all other page requests within that session will be denied.

Note
The authentication scheme cannot be run when the WAP gateway is operating the connectionless WSP protocol to communicate between the wireless device and the WAP gateway.
Examples
The following example shows the directory named scripts being configured as the authentication prefix URL:
wap authentication prefix http://www.company-name.com/auth/scripts/Related Commands
wap authentication service
To initiate customer-supplied user authentication, use the wap authentication service command in global configuration mode. To disable the customer-supplied user authentication, use the no form of this command.
wap authentication service url
no wap authentication service
Syntax Description
Defaults
By default, no URL is defined and no redirection is performed.
Command Modes
Global configuration
Command History
Usage Guidelines
The wap authentication service command is used to enable a customer-supplied user authentication scheme to work with the Wireless Application Protocol (WAP) gateway.
If the wap authentication service command is configured, the WAP gateway will redirect the browser to the page configured by the wap authentication service command whenever a new session starts. The customer-supplied authentication process will then proceed and a page, specified by the wap authentication completed command, will be displayed if the authentication process is successful. Until the authentication process is successful, the WAP gateway will service only URLs specified by the wap authentication service, wap authentication completed, and wap authentication prefix commands, and all other page requests within that session will be denied.

Note
The authentication scheme cannot be run when the WAP gateway is operating the connectionless WSP protocol to communicate between the wireless device and the WAP gateway.
Examples
The following example shows the URL http://www.company-name.com/auth/login.wml being configured as the URL to be accessed to initiate customer-supplied user authentication for the WAP gateway:
wap authentication service http://www.company-name.com/auth/login.wmlRelated Commands
wap authentication timeout
To specify an interval after which the user must reauthenticate, use the wap authentication timeout command in global configuration mode. To disable the timeout interval, use the no form of this command.
wap authentication timeout seconds
no wap authentication timeout
Syntax Description
Defaults
By default, no timeout interval is set.
Command Modes
Global configuration
Command History
Usage Guidelines
The wap authentication timeout command is used with other authentication commands to enable a customer-supplied user authentication scheme to work with the Wireless Application Protocol (WAP) gateway.
If the wap authentication service command is configured, the WAP gateway will redirect the browser to the page configured by the wap authentication service command whenever a new session starts. The customer-supplied authentication process will then proceed and a page, specified by the wap authentication completed command, will be displayed if the authentication process is successful. Until the authentication process is successful, the WAP gateway will service only URLs specified by the wap authentication service, wap authentication completed, and wap authentication prefix commands, and all other page requests within that session will be denied.

Note
The authentication scheme cannot be run when the WAP gateway is operating the connectionless WSP protocol to communicate between the wireless device and the WAP gateway.
Examples
The following example shows an authentication timeout interval of 1200 seconds (20 minutes) being set:
wap authentication timeout 1200Related Commands
wap http maximum header-length
To specify how the gateway splits individual Hypertext Transfer Protocol (HTTP) headers into multiple lines, use the wap http maximum header-length command in global configuration mode. To restore the maximum header length to the default value, use the no form of this command.
wap http maximum header-length max-characters
no wap http maximum header-length
Syntax Description
max-characters
Maximum number of characters allowed before the gateway splits a line of HTTP headers at the end of the next comma-separated value.
Defaults
By default, the maximum HTTP header length is set to 100 characters.
Command Modes
Global configuration
Command History
Usage Guidelines
The wap http maximum header-length command controls how the gateway splits individual HTTP headers into multiple lines. As the gateway builds the HTTP header, if the addition of a comma-separated value causes the line to exceed this value, the header is continued on a new line. Some web content servers cannot handle long lines of text, and the use of line wrapping avoids this problem.
Examples
The following example shows the maximum HTTP header length set to 80 characters:
wap http maximum header-length 80wap proxy-list
To specify a list of filter records that the Wireless Application Protocol (WAP) gateway can use to filter out requests that must be routed to a proxy server and not forwarded directly to the server specified in the URL, use the wap proxy-list command in global configuration mode. To reset the filter list to the default of a null string, use the no form of this command.
wap proxy-list http-server [proxy-server]
no wap proxy-list
Syntax Description
Defaults
By default, the filter list is a null string.
Command Modes
Global configuration
Command History
Usage Guidelines
When the WAP gateway receives a page request it searches through the configured proxy list records in the order in which they were entered until it finds a match. If the gateway finds a match, the request is forwarded to the specified proxy server. If no proxy server is specified, or no match is found, the request is serviced directly. Requests to be forwarded to the local domain are configured first, then any other requests that contain a dot in the domain name can be sent to a proxy server.
Examples
The following example shows a list of proxy list records that will enable the WAP gateway to forward page requests that are within the company-name company network directly to its server, while a proxy server will be used for all page requests outside the network:
First Record
wap proxy-list *.company-name.comThis record shows all requests to the company-name company host being serviced directly and not sent to a proxy server.
Second Record
wap proxy-list *.company-name.com:*This record shows all requests to any explicitly specified port number on a company-name host being serviced directly and not passed to a proxy server.
Third Record
wap proxy-list *.* proxy.company-name.com:9090This record shows all other requests including a dot in the page request being serviced by the specified company-name proxy server. The first two records capture all the local page requests except those requests that do not specify a company-name host. Requests are usually sent to the default port of 8080, but in this record, a different port number has been specified in the proxy-server argument.
Fourth Record
wap proxy-list *This record shows all requests without a domain specification being serviced directly. This is the default action.
wap up-browser device-base
To specify a URL prefix to be used as a substitute for the string of characters (known as "device:base") received in a request from an Unwired Planet (UP) browser, use the wap up-browser device-base command in global configuration mode. To restore the URL prefix to its default setting of a null string, use the no form of this command.
wap up-browser device-base url
no wap up-browser device-base
Syntax Description
url
URL prefix used by the Wireless Application Protocol (WAP) gateway as a substitute for "device:base" when received in requests from a UP browser.
Defaults
By default, the URL is a null string.
Command Modes
Global configuration
Command History
Usage Guidelines
This command works with the wap up-browser device-home global configuration command to provide support for UP v4.0 browsers that cannot be configured directly with a conventional URL. When a UP browser on the wireless device starts, it requests "device:home" instead of a URL. The WAP gateway translates the "device:home" request into the URL configured by the wap up-browser device-home command before forwarding the request to the content server. Subsequent page requests from the UP browser may specify the "device:base" string followed by a path and filename. The WAP gateway substitutes the URL prefix configured with the wap up-browser device-base command for the "device:base" string and then sends the request to the content server.
Examples
The following example shows the URL prefix of http://www.company-name.com/wapserver being set as the substitute URL for the "device:base" request sent by a UP browser:
wap up-browser device-base http://www.company-name.com/wapserverRelated Commands
Specifies a URL to be used when a request containing the string of characters (known as "device:home") is received from a UP browser.
wap up-browser device-home
To specify a URL to be used when a request containing the string of characters (known as "device:home") is received from an Unwired Planet (UP) browser, use the wap up-browser device-home command in global configuration mode. To restore the URL prefix to its default setting of a null string, use the no form of this command.
wap up-browser device-home url
no wap up-browser device-home
Syntax Description
Defaults
By default, the URL is a null string.
Command Modes
Global configuration
Command History
Usage Guidelines
This command works with the wap up-browser device-base global configuration command to provide support for UP v4.0 browsers that cannot be configured directly with a conventional URL. When a UP browser on the wireless device starts, it requests the string of characters (known as "device:home") instead of a URL. The Wireless Application Protocol (WAP) gateway translates the "device:home" request into the URL configured by the wap up-browser device-home command before forwarding the request to the content server. Subsequent page requests from the UP browser may specify the "device:base" string followed by a path and filename. The WAP gateway substitutes the URL prefix configured with the wap up-browser device-base command for the "device:base" string and then sends the request to the content server.
The wireless client device does not know the actual web page as the WAP gateway translates the request for the home page to the actual URL that is downloaded. Relative URLs that may point to a particular place on a page should be avoided.
Examples
The following example shows the URL http://www.company-name.com/wapserver/index.wml being set as the substitute URL for the "device:home" request sent by a UP browser:
wap up-browser device-home http://www.company-name.com/wapserver/index.wmlRelated Commands
Specifies a URL prefix to be used as a substitute for the string of characters (known as "device:base") received in a request from a UP browser.
wap up-browser subno-suffix
To specify a value to be appended to the header field (known as "X-UP-subno") to identify the Wireless Application Protocol (WAP) gateway before transmission to a Wireless Markup Language (WML) content server, use the wap up-browser subno-suffix command in global configuration mode. To disable appending a value to the header field, use the no form of this command.
wap up-browser subno-suffix value
no wap up-browser subno-suffix
Syntax Description
Defaults
By default, no value is appended and the header is unchanged as it passes through the WAP gateway.
Command Modes
Global configuration
Command History
Usage Guidelines
The wap up-browser subno-suffix command has been implemented to support compatibility with Unwired Planet (UP) browsers.
When a header field (known as "X-UP-subno") is received from UP browsers, it contains user identification information supplied by the browser. The WAP gateway forwards this header to the content server. Where several WAP gateways exist, a value can be appended to the header field to identify each individual WAP gateway to the content server.
Examples
The following example shows the value of gateway.company-name.com being added to the "X-UP-subno" header field:
wap up-browser subno-suffix gateway.company-name.comwap wsp maximum sessions
To specify the maximum number of concurrent Wireless Session Protocol (WSP) sessions, use the wap wsp maximum sessions command in global configuration mode. To disable the restriction on the number of WSP sessions, use the no form of this command.
wap wsp maximum sessions number
no wap wsp maximum sessions
Syntax Description
Defaults
By default, there is no limit to the number of WSP sessions.
Command Modes
Global configuration
Command History
Usage Guidelines
Use the wap wsp maximum sessions command to specify a limit to the number of concurrent WSP sessions that the Wireless Application Protocol (WAP) gateway will create. When the maximum number of sessions is reached, a request to create a new WSP session will result in the deletion of the oldest existing session by the gateway, to ensure that the maximum number of WSP sessions is not exceeded. The oldest WSP session is usually in an idle state. A timeout interval can be set for idle WSP sessions by using the wap wsp timeout session global configuration command.

Note
The practical limit for the maximum number of WSP sessions depends on the type of CPU in the router and the amount of memory.
Examples
The following example shows the maximum number of WSP sessions set to 1000:
wap wsp maximum sessions 1000Related Commands
Specifies the number of seconds that a WSP session will continue to exist when there is no traffic for that session.
wap wsp timeout session
To specify the number of seconds that a Wireless Session Protocol (WSP) session will continue to exist when there is no traffic for that session, use the wap wsp timeout session command in global configuration mode. To restore the default timeout interval to 1 hour, use the no form of this command.
wap wsp timeout session seconds
no wsp timeout session
Syntax Description
Defaults
By default, the number of seconds before the session times out is set to 3600 (1 hour).
Command Modes
Global configuration
Command History
Usage Guidelines
Use the wap wsp timeout session command to manage the timeout intervals for WSP sessions with no traffic. Keeping the WSP session timeout interval short may improve software performance because terminating an idle WSP session frees the associated memory resources. A short timeout interval, however, may result in the gateway dropping existing sessions sooner than expected.
Examples
The following example shows the WSP session timeout set to 300 seconds (5 minutes):
wap wsp timeout session 300Related Commands
wap wtls encryption
To specify the encryption algorithms that the Wireless Application Protocol (WAP) gateway will operate, use the wap wtls encryption command in global configuration mode. To disable the use of an encryption algorithm, use the no form of this command.
wap wtls encryption {all | [rc5-cbc-40] [rc5-cbc-56] [rc5-cbc-128]}
no wap wtls encryption {all | [rc5-cbc-40] [rc5-cbc-56] [rc5-cbc-128]}
Syntax Description
Defaults
By default, all the RC5-based algorithms are enabled.
Command Modes
Global configuration
Command History
Usage Guidelines
Block cipher encryption techniques are designed to disguise plain text patterns that otherwise might generate patterns of encrypted cipher text. Any repeated sequences can facilitate cracking of the algorithm.
The WAP gateway can be configured to operate all the encryption algorithms or a list specifying one or more of the options. To decide which encryption algorithms to configure, you must consider several factors. A shorter key length is easier to compute and will impose less overhead on the processor than a longer key length, but a shorter key length can compromise security. The level of security you need to configure will also be determined by the type of information that can be accessed through the gateway. Confidential corporate information often requires a high level of security.
Use the wap wtls encryption command in conjunction with the wap wtls hash and wap wtls key-exchange global configuration commands to help establish and operate a secure WAP session.

Note
Many wireless devices support only a subset of the available algorithms. Configuring the gateway to operate only one or two algorithms may prevent some wireless devices from accessing the gateway.
Examples
The following example shows the WAP gateway being configured to disable the use of the RC5 cipher block chaining encryption algorithm with an effective key length of 128 bits. All the RC5-based algorithms are enabled by default.
no wap wtls encryption rc5-cbc-128Related Commands
Specifies the hash algorithms operated by the WAP gateway.
Specifies the key-exchange algorithms operated by the WAP gateway.
wap wtls hash
To specify the hash algorithms that the Wireless Application Protocol (WAP) gateway will operate, use the wap wtls hash command in global configuration mode. To disable the use of a hash algorithm, use the no form of this command.
wap wtls hash {all | [md5-40] [md5-80] [md5-128] [sha-0] [sha-40] [sha-80] [sha-160] [sha-xor-40]}
no wap wtls hash {all | [md5-40] [md5-80] [md5-128] [sha-0] [sha-40] [sha-80] [sha-160] [sha-xor-40]}
Syntax Description
Defaults
By default, the WAP gateway operates the sha-40, sha-80, and sha-160 hash algorithms.
Command Modes
Global configuration
Command History
Usage Guidelines
Hash algorithms are used to construct a digital signature for encrypted text to prevent attempts to modify the original encrypted text.
The WAP gateway can be configured to operate all the hash algorithms or a list specifying one or more of the options. The level of security you need to configure will be determined by the type of information that can be accessed through the gateway. Confidential corporate information often requires a high level of security.
Use the wap wtls hash command in conjunction with the wap wtls encryption and wap wtls key-exchange global configuration commands to help establish and operate a secure WAP session.

Note
Many wireless devices support only a subset of the available algorithms. Configuring the gateway to operate only one or two algorithms may prevent some wireless devices from accessing the gateway.
Examples
The following example shows the WAP gateway being configured to disable the use of the SHA-1 hash algorithm where the complete output is used:
no wap wtls hash sha-160Related Commands
Specifies the encryption algorithms operated by the WAP gateway.
Specifies the key-exchange algorithms operated by the WAP gateway.
wap wtls key-exchange
To specify a key-exchange algorithm that the Wireless Application Protocol (WAP) gateway will operate, use the wap wtls key-exchange command in global configuration mode. To disable the use of a key-exchange algorithm, use the no form of this command.
wap wtls key-exchange {all | [dh-anon-512] [dh-anon-768] [dh-anon-unrestricted] [rsa-anon-512] [rsa-anon-768] [rsa-anon-unrestricted]}
no wap wtls key-exchange {all | [dh-anon-512] [dh-anon-768] [dh-anon-unrestricted] [rsa-anon-512] [rsa-anon-768] [rsa-anon-unrestricted]}
Syntax Description
Defaults
By default, the WAP gateway operates all the available key-exchange algorithms.
Command Modes
Global configuration
Command History
Usage Guidelines
Key-exchange algorithms allow cryptographic keys to be securely generated and exchanged between devices over an unsecure connection.
The WAP gateway can be configured to operate all the key-exchange algorithms or a list specifying one or more of the options. To decide which key-exchange algorithms to configure, you must consider several factors. A shorter key length is easier to compute and will impose less overhead on the processor than a longer key length, but a shorter key length can compromise security. The level of security you need to configure will also be determined by the type of information that can be accessed through the gateway. Confidential corporate information often requires a high level of security.
Use the wap wtls key-exchange command in conjunction with the wap wtls encryption and wap wtls hash global configuration commands to help establish and operate a secure WAP session.

Note
Many wireless devices support only a subset of the available algorithms. Configuring the gateway to operate only one or two algorithms may prevent some wireless devices from accessing the gateway.
Examples
The following example shows the WAP gateway being configured to disable use of the DH key-exchange encryption algorithm without authentication and with the key length limited to 512 bits:
no wap wtls key-exchange dh-anon-512Related Commands
Specifies the encryption algorithms operated by the WAP gateway.
Specifies the hash algorithms operated by the WAP gateway.
wap wtls timeout connection
To specify an interval after which an inactive Wireless Transport Layer Security (WTLS) connection will be closed by the gateway, use the wap wtls timeout connection command in global configuration mode. To restore the connection timeout interval to its default setting, use the no form of this command.
wap wtls timeout connection seconds
no wap wtls timeout connection
Syntax Description
Defaults
By default, the WTLS connection timeout interval is 1800 seconds (30 minutes).
Command Modes
Global configuration
Command History
Usage Guidelines
The Wireless Application Protocol (WAP) gateway has no reliable method for determining when a user is finished with a session if the session is not explicitly closed by the browser. Use the wap wtls timeout connection command to ensure a balance between closing an inactive WTLS connection before the user is finished with the connection and using router memory with a series of inactive connections.
Other global configuration commands that you can use to control the behavior of the WTLS layer are wap wtls timeout handshake, wap wtls timeout key, and wap wtls timeout session.
Examples
The following example shows the WTLS connection timeout interval set to 20 minutes:
wap wtls timeout connection 1200Related Commands
wap wtls timeout handshake
To specify the interval that the gateway allows for the Wireless Transport Layer Security (WTLS) handshake to complete, use the wap wtls timeout handshake command in global configuration mode. To restore the handshake timeout interval to its default setting, use the no form of this command.
wap wtls timeout handshake seconds
no wap wtls timeout handshake
Syntax Description
Defaults
By default, the WTLS handshake timeout interval is 120 seconds (2 minutes).
Command Modes
Global configuration
Command History
Usage Guidelines
Use the wap wtls timeout handshake command to ensure that an incomplete WTLS handshake process is terminated after an appropriate interval. The WTLS handshake process may fail for a variety of reasons but if the client does not respond during the timeout interval, the process is terminated.
Other global configuration commands that you can use to control the behavior of the WTLS layer are wap wtls timeout connection, wap wtls timeout key, and wap wtls timeout session.
Examples
The following example shows the WTLS handshake timeout set to 3 minutes:
wap wtls timeout handshake 180Related Commands
wap wtls timeout key
To specify an interval during which the gateway will retain a Wireless Transport Layer Security (WTLS) master key when the session is unused, use the wap wtls timeout key command in global configuration mode. To restore the master key timeout interval to its default setting, use the no form of this command.
wap wtls timeout key seconds
no wap wtls timeout key
Syntax Description
Defaults
By default, the WTLS session key timeout interval is 2,678,400 seconds (31 days).
Command Modes
Global configuration
Command History
Usage Guidelines
After the timeout interval, the wireless device will need to renegotiate a new key when it contacts the Wireless Application Protocol (WAP) gateway.

Note
The WTLS master key is not maintained across router reboots. After the router is rebooted, a new master key must be established when the wireless device connects to the WAP gateway.
Other global configuration commands that you can use to control the behavior of the WTLS layer are wap wtls timeout connection, wap wtls timeout handshake, and wap wtls timeout session.
Examples
The following example shows the timeout interval for an unused WTLS master key set to 1 day:
wap wtls timeout key 86400Related Commands
wap wtls timeout session
To specify an interval after which an inactive Wireless Transport Layer Security (WTLS) session will be closed by the gateway, use the wap wtls timeout session command in global configuration mode. To restore the session timeout interval to its default setting, use the no form of this command.
wap wtls timeout session seconds
no wap wtls timeout session
Syntax Description
Defaults
By default, the WTLS session timeout interval is 3600 seconds (1 hour).
Command Modes
Global configuration
Command History
Usage Guidelines
An inactive WTLS session is defined as a session that has no associated WTLS connections.
The Wireless Application Protocol (WAP) gateway has no reliable method for determining when a user is finished with a session if the session is not explicitly closed by the browser. Use the wap wtls timeout session command to ensure a balance between closing an inactive WTLS session before the user is finished with the session and using router memory with a series of inactive sessions.
Other global configuration commands that you can use to control the behavior of the WTLS layer are wap wtls timeout connection, wap wtls timeout handshake, and wap wtls timeout key commands.
Examples
The following example shows the WTLS session timeout interval set to 90 minutes:
wap wtls timeout session 5400Related Commands
Glossary
2G—second generation. Generic name for second-generation digital mobile networks such as GSM. See GSM.
CDMA—code division multiple access. A technology for digital transmission used in North America, Japan, and Korea.
GPRS—general packet radio service. An upgrade to the existing GSM digital mobile networks to provide higher-speed data services.
GSM—global system for mobile communication. Popular 2G digital cellular mobile network standard, widely deployed in Europe.
UDP—User Datagram Protocol. Connectionless transport layer protocol in the IP protocol stack. UDP is a simple protocol that exchanges datagrams without acknowledgments or guaranteed delivery, requiring that error processing and retransmission be handled by other protocols.
UP browser—WAP browser developed by Unwired Planet (now Openwave).
WAP—Wireless Application Protocol. Protocol suite to enable the delivery and presentation of data on mobile phones and other wireless devices.
WDP—Wireless Datagram Protocol. Protocol that is similar to UDP but has segmentation and reassembly capabilities. Used where bearers can support only small packet sizes.
WML—Wireless Markup Language. An XML-based markup language used to describe content for delivery to WAP devices. WML is optimized for mobile wireless devices and uses the concept of a deck of cards where a series of related cards (often screens) are downloaded from the server at the same time. The downloaded deck is navigated locally, saving many separate, and potentially expensive, requests to the remote server.
WMLC—Wireless Markup Language Compressed. Compressed WML content is WML content received from a web server and compressed by a WAP gateway, using a process called tokenisation. WMLC content is then forwarded to the WAP-enabled device.
WMLS—Wireless Markup Language Script. A scripting language derived from ECMAscript and used with WML.
WSP—Wireless Session Protocol. WAP protocol that is broadly equivalent to HTTP.
WTAI—Wireless Telephony Application Interface. An API to the telephony capabilities in a mobile phone.
WTLS—Wireless Transport Layer Security. A protocol to ensure data integrity, privacy, and authentication to transactions on a wireless device using WAP. WTLS is derived from the Transport Layer Security (TLS) protocol but has been optimized for use over narrowband communication channels.
WTP—Wireless Transaction Protocol. A lightweight protocol that provides reliable transport for WSP. See also WSP.
 Feedback
Feedback