Cisco Unified Border Element Fundamentals and Basic Setup, Cisco IOS Release 15M&T
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- April 7, 2014
Chapter: Overview of Cisco Unified Border Element
Overview of Cisco Unified Border Element
Cisco Unified Border Element (CUBE) is a unified communications border element, providing voice and video connectivity between the enterprise IP network and service provider network. It is similar to a voice gateway, except for the replacement of physical voice trunks with an IP connection.
Information about Cisco Unified Border Element
Cisco Unified Border Element (CUBE) is network border element that can terminate and originate signaling (H.323 and Session Initiation Protocol [SIP]), media streams (Real-Time Transport Protocol [RTP] and RTP Control Protocol [RTCP]).
Session Border controller (SBC) was used by service providers (SP) to enable full billing capabilities within VoIP networks. CUBE provides the extended functionality of interconnecting VoIP networks, especially on the enterprise side.
CUBE functionality is implemented on devices using a special IOS feature set, which allows CUBE to route a call from one VoIP dial peer to another. As VoIP dial peers can be handled by either SIP or H.323, CUBE can be used to interconnect VoIP networks of different signaling protocols. VoIP internetworking is achieved by connecting an inbound dial peer with an outbound dial peer. A standard Cisco IOS gateway without CUBE functionality cannot allow VoIP-to-VoIP connections.
Protocol internetworking is possible for the following combinations:
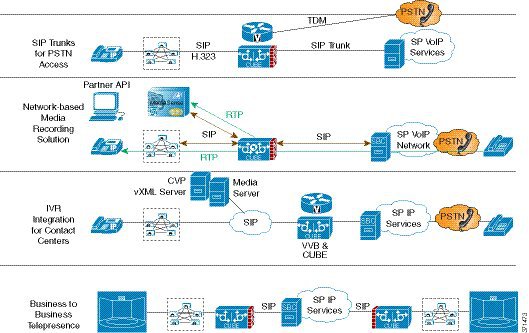
CUBE is used by enterprise and small and medium-sized organizations to interconnect SIP PSTN access with SIP and H.323 enterprise unified communications networks.
A CUBE interoperates with several different network elements including voice gateways, IP phones, and call-control servers in many different application environments, from advanced enterprise voice and/or video services with Cisco Unified Communications Manager or Cisco Unified Communications Manager Express, as well as simpler toll bypass and voice over IP (VoIP) transport applications. The CUBE provides organizations with all the border controller functions integrated into the network layer to interconnect unified communications voice and video enterprise-to-service-provider architectures.
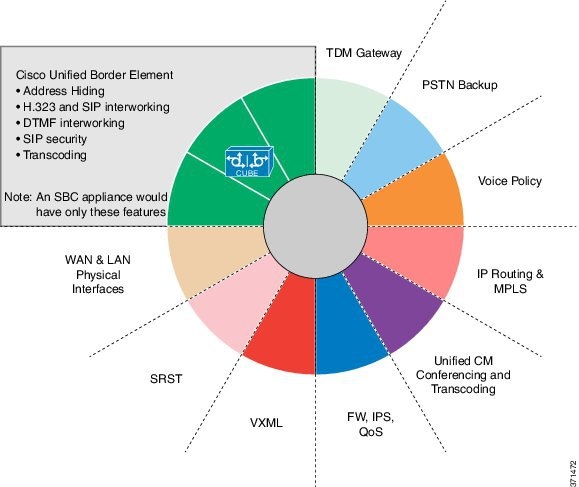
- Signaling interworking—H.323 and SIP.
- Media interworking—dual-tone multifrequency (DTMF), fax, modem, and codec transcoding.
- Address and port translations—privacy and topology hiding.
- Billing and call detail record (CDR) normalization.
- Quality-of-service (QoS) and bandwidth management—QoS marking using differentiated services code point (DSCP) or type of service (ToS), bandwidth enforcement using Resource Reservation Protocol (RSVP), and codec filtering.

SIP/H.323 Trunking
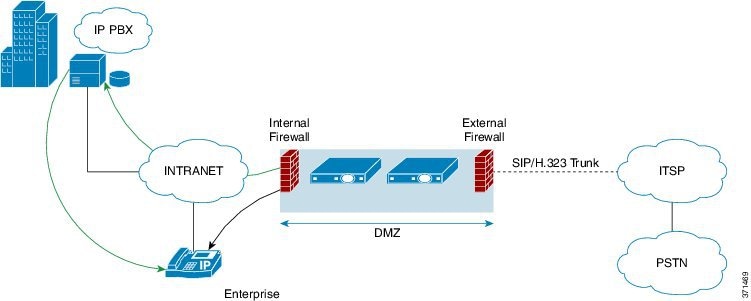
The Session Initiation Protocol (SIP) is a signaling communications protocol, widely used for controlling multimedia communication sessions such as voice and video calls over Internet Protocol (IP) networks. SIP (or H.323) trunking is the use of VoIP to facilitate the connection of a private branch exchange (PBX) to the Internet. To use SIP trunking, an enterprise must have a PBX that connects to all internal end users, an Internet telephony service provider (ITSP) and a gateway that serves as the interface between the PBX and the ITSP. One of the most significant advantages of SIP trunking is its ability to combine data, voice, and video in a single line, eliminating the need for separate physical media for each mode.
SIP trunking overcomes TDM barriers, in that it:

Typical Deployment Scenarios for CUBE
CUBE in an enterprise environments serve two main purposes:
- External Connections-CUBE is the demarcation point within a unified communications network and provides interconnectivity with external networks. This includes H.323 voice and video connections and SIP VoIP connections.
- Internal Connections-When used within a VoIP network, CUBE increases flexibility and interoperability between devices.

CUBE Deployment Modes
- Media flow-through—CUBE acts as a back-to-back user agent. In a media flow-through mode, between two endpoints, both signaling
and media flows through the IP-to-IP Gateway (IPIP GW). The IPIP GW
performs both signaling and media interworking between H.323/SIP
IPv4 and SIP IPv6 networks.
Media-flow-through mode is recommended when CUBE is used as an SBC for PSTN connectivity.
Figure 6. Media flow-through 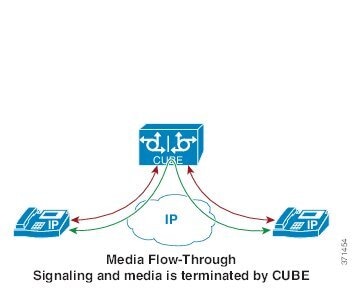
- Media flow-around—Only signaling is
terminated at CUBE. Media bypasses CUBE and flows directly between the endpoints. This mode is recommended to be used only if CUBE is deployed within an enterprise network.
Figure 7. Media flow-around 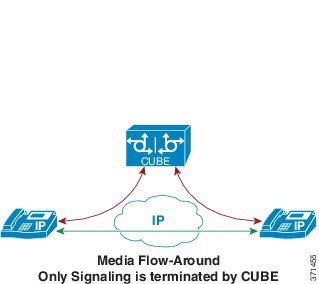
How to Configure Basic CUBE Tasks
Enabling the CUBE application on a Router
1.
enable
2.
configure
terminal
3.
voice
service
voip
4.
mode border-element license capacity sessions
5.
allow-connections from-type to to-type
6.
end
DETAILED STEPS
Configuring a Trusted IP Address List for Toll-Fraud Prevention
1.
enable
2.
configure terminal
3.
voice service voip
4.
ip address trusted list
5.
ipv4 ipv4-address [network-mask]
6.
ipv6 ipv6-address
7.
end
DETAILED STEPS
 Feedback
Feedback