NetFlow Configuration Guide, Cisco IOS XE Release 3S (ASR 1000)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 31, 2012
Chapter: Configuring NetFlow and NetFlow Data Export
- Finding Feature Information
- Prerequisites for Configuring NetFlow and NetFlow Data Export
- Restrictions for Configuring NetFlow and NetFlow Data Export
- Information About Configuring NetFlow and NetFlow Data Export
- NetFlow Data Capture
- NetFlow Flows Key Fields
- NetFlow Cache Management and Data Export
- NetFlow Export Format Versions 9 8 and 5
- Overview of NetFlow Export Format Versions 9 8 and 5
- NetFlow Export Version Formats
- NetFlow Export Packet Header Format
- NetFlow Flow Record and Export Format Content Information
- NetFlow Data Export Format Selection
- NetFlow Version 9 Data Export Format
- NetFlow Version 8 Data Export Format
- NetFlow Version 5 Data Export Format
- Egress NetFlow Accounting Benefits NetFlow Accounting Simplified
- NetFlow Subinterface Support Benefits Fine-Tuning Your Data Collection
- NetFlow Multiple Export Destinations Benefits
- How to Configure NetFlow and NetFlow Data Export
Configuring NetFlow and NetFlow Data Export
This module contains information about and instructions for configuring NetFlow to capture and export network traffic data. NetFlow capture and export are performed independently on each internetworking device on which NetFlow is enabled. NetFlow need not be operational on each router in the network. NetFlow is a Cisco IOS XE application that provides statistics on packets flowing through the router. NetFlow is emerging as a primary network accounting and security technology.
- Finding Feature Information
- Prerequisites for Configuring NetFlow and NetFlow Data Export
- Restrictions for Configuring NetFlow and NetFlow Data Export
- Information About Configuring NetFlow and NetFlow Data Export
- How to Configure NetFlow and NetFlow Data Export
- Configuration Examples for NetFlow and NetFlow Data Export
- Additional References
- Feature Information for Configuring NetFlow and NetFlow Data Export
- Glossary
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest caveats and feature information, see Bug Search Tool and the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the feature information table at the end of this module.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
Prerequisites for Configuring NetFlow and NetFlow Data Export
- Configure the router for IP routing.
- Ensure that either Cisco Express Forwarding or fast switching is enabled on your router and on the interfaces on which you want to configure NetFlow.
- Understand the resources required on your router because NetFlow consumes additional memory and CPU resources.
Restrictions for Configuring NetFlow and NetFlow Data Export
Preset Size of NetFlow Cache
NetFlow consumes additional memory. If you have memory constraints, you might want to preset the size of the NetFlow cache so that it contains a smaller number of entries. The default cache size depends on the platform.
Egress NetFlow Accounting in Cisco IOS XE Release 2.1 or Later Releases
The Egress NetFlow Accounting feature captures NetFlow statistics for IP traffic only. Multiprotocol Label Switching (MPLS) statistics are not captured. The Egress NetFlow Accounting feature can be used on a provider edge (PE) router to capture IP traffic flow information for egress IP packets that arrived at the router as MPLS packets and underwent label disposition.
Egress NetFlow accounting might adversely affect network performance because of the additional accounting-related computation that occurs in the traffic-forwarding path of the router.
Locally generated traffic (traffic that is generated by the router on which the Egress NetFlow Accounting feature is configured) is not counted as flow traffic for the Egress NetFlow Accounting feature.
 Note |
Egress NetFlow captures IPv4 packets as they leave the router. |
Restrictions for NetFlow Version 9 Data Export
- Backward compatibility--Version 9 is not backward-compatible with Version 5 or Version 8. If you need Version 5 or Version 8, you must configure it.
- Export bandwidth--Export bandwidth use increases for Version 9 (because of template flowsets) versus Version 5. The increase in bandwidth usage versus Version 5 varies with the frequency with which template flowsets are sent. The default is to resend templates every 20 packets, which has a bandwidth cost of about 4 percent. If necessary, you can lower the resend rate with the ip flow-export template refresh-rate packets command.
- Performance impact--Version 9 slightly decreases overall performance, because generating and maintaining valid template flowsets require additional processing.
Restrictions for NetFlow Version 8 Export Format
Version 8 export format is available only for aggregation caches, and it cannot be expanded to support new features.
Restrictions for NetFlow Version 5 Export Format
Version 5 export format is suitable only for the main cache, and it cannot be expanded to support new features.
Policy-Based Routing and NetFlow Data Export
If a local policy is configured, an Aggregation Services Router (ASR) checks the injected packet and applies policy-based routing (PBR) to the packet. When NetFlow Data Export (NDE) packets are injected in the data path during Cisco Express Forwarding lookup, the PBR local policy is not applied to the NDE packets. Therefore, NDE features on ASR cannot work with PBR.
Information About Configuring NetFlow and NetFlow Data Export
- NetFlow Data Capture
- NetFlow Flows Key Fields
- NetFlow Cache Management and Data Export
- NetFlow Export Format Versions 9 8 and 5
- Egress NetFlow Accounting Benefits NetFlow Accounting Simplified
- NetFlow Subinterface Support Benefits Fine-Tuning Your Data Collection
- NetFlow Multiple Export Destinations Benefits
NetFlow Data Capture
NetFlow captures data from ingress (incoming) and egress (outgoing) packets. NetFlow gathers statistics for the following ingress IP packets:
- IP-to-IP packets
- IP-to-MPLS packets
- Frame Relay-terminated packets
- ATM-terminated packets
NetFlow captures data for all egress (outgoing) packets through the use of the following feature:
- Egress NetFlow Accounting--NetFlow gathers statistics for all egress packets for IP traffic only.
NetFlow Flows Key Fields
A network flow is identified as a unidirectional stream of packets between a given source and destination--both are defined by a network-layer IP address and by transport-layer source and destination port numbers. Specifically, a flow is identified as the combination of the following key fields:
- Source IP address
- Destination IP address
- Source port number
- Destination port number
- Layer 3 protocol type
- Type of service (ToS)
- Input logical interface
These seven key fields define a unique flow. If a packet has one key field different from another packet, it is considered to belong to another flow. A flow might contain other accounting fields (such as the autonomous system (AS) number in the NetFlow export Version 5 flow format) that depend on the export record version that you configure. Flows are stored in the NetFlow cache.
NetFlow Cache Management and Data Export
The key components of NetFlow are the NetFlow cache or data source that stores IP flow information, and the NetFlow export or transport mechanism that sends NetFlow data to a network management collector, such as the NetFlow Collection Engine. NetFlow operates by creating a NetFlow cache entry (a flow record) for each active flow. A flow record is maintained within the NetFlow cache for each active flows. Each flow record in the NetFlow cache contains fields that can later be exported to a collection device, such as the NetFlow Collection Engine.
NetFlow is very efficient with the amount of export data being about 1.5 percent of the switched traffic in the router. NetFlow accounts for every packet (non-sampled mode) and provides a highly condensed and detailed view of all network traffic that entered the router or switch.
The key to NetFlow-enabled switching scalability and performance is highly intelligent flow cache management, especially for densely populated and busy edge routers handling large numbers of concurrent, short duration flows. The NetFlow cache management software contains a highly sophisticated set of algorithms for efficiently determining if a packet is part of an existing flow or should generate a new flow cache entry. The algorithms are also capable of dynamically updating the per-flow accounting measurements that reside in the NetFlow cache, and determining cache aging/flow expiration.
Rules for expiring NetFlow cache entries include:
- Flows which have been idle for a specified time are expired and removed from the cache.
- Long-lived flows are expired and removed from the cache. (Flows are not allowed to live more than 30 minutes by default; the underlying packet conversation remains undisturbed.)
- As the cache becomes full, a number of heuristics are applied to aggressively age groups of flows simultaneously.
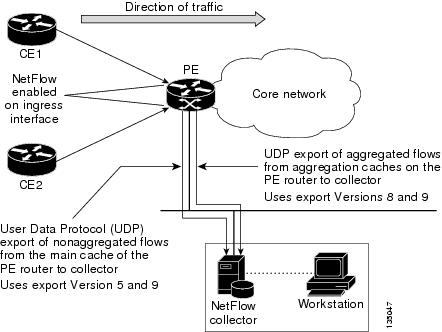
Expired flows are grouped together into "NetFlow export" datagrams for export from the NetFlow- enabled device. The NetFlow functionality is configured on a per-interface basis. To configure NetFlow export capabilities, you need to specify the IP address and application port number of the Cisco NetFlow or third-party flow collector. The flow collector is a device that provides NetFlow export data filtering and aggregation capabilities. The figure below shows an example of NetFlow data export from the main and aggregation caches to a collector.
| Figure 1 | NetFlow Data Export from the Main and Aggregation Caches |
NetFlow Export Format Versions 9 8 and 5
The following sections provide more detailed information on NetFlow Data Export Formats Versions 9, 8, and 5:
- Overview of NetFlow Export Format Versions 9 8 and 5
- NetFlow Export Version Formats
- NetFlow Export Packet Header Format
- NetFlow Flow Record and Export Format Content Information
- NetFlow Data Export Format Selection
- NetFlow Version 9 Data Export Format
- NetFlow Version 8 Data Export Format
- NetFlow Version 5 Data Export Format
Overview of NetFlow Export Format Versions 9 8 and 5
NetFlow exports data in UDP datagrams in one of the following formats: Version 9, Version 8, Version 7, or Version 5.
- Version 9--A flexible and extensible format, which provides the versatility needed for support of new fields and record types. The version 9 export format enables you to use the same version for main and aggregation caches, and the format is extendable, so you can use the same export format with future features.
- Version 8--A format added to support data export from aggregation caches. Export datagrams contain a subset of the usual Version 5 export data, which is valid for the particular aggregation cache scheme.
- Version 5--A later enhanced version that adds Border Gateway Protocol (BGP) AS information and flow sequence numbers. (Versions 2 through 4 were not released.) This is the most commonly used format.
NetFlow Export Version Formats
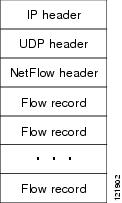
For all export versions, the NetFlow export datagram consists of a header and a sequence of flow records. The header contains information such as the sequence number, record count, and system uptime. The flow record contains flow information, for example, IP addresses, ports, and routing information.
The NetFlow Version 9 export format is the newest NetFlow export format. The distinguishing feature of the NetFlow Version 9 export format is that it is template based. Templates make the record format extensible. This feature allows future enhancements to NetFlow without requiring concurrent changes to the basic flow-record format.
The use of templates with the NetFlow Version 9 export format provides several other key benefits:
- You can export almost any information from a router or switch including Layer 2 through 7 information, routing information, IP Version 6 (IPv6), IP Version 4 (IPv4), and multicast information. This new information allows new applications for export data and new views of the network behavior.
- Third-party business partners who produce applications that provide collector or display services for NetFlow are not required to recompile their applications each time a new NetFlow export field is added. Instead, they might be able to use an external data file that documents the known template formats.
- New features can be added to NetFlow more quickly, without breaking current implementations.
The work of the IETF IP Information Export (IPFIX) Working Group (WG) and the IETF Pack Sampling (PSAMP) WG are based on the NetFlow Version 9 export format.
The Version 5 export format adds BGP autonomous system information and flow sequence numbers. the Version 8 export format is the NetFlow export format to use when you enable router-based NetFlow aggregation on Cisco IOS XE router platforms.
The figure below shows a typical datagram used for NetFlow fixed format export Versions 5, 7, and 8.
| Figure 2 | Typical Datagram for NetFlow Fixed Format Export Versions 5, 7, and 8 |
NetFlow Export Packet Header Format
In all five export versions, the datagram consists of a header and one or more flow records. The first field of the header contains the version number of the export datagram. Typically, a receiving application that accepts any of the format versions allocates a buffer large enough for the largest possible datagram from any of the format versions, and then uses the header to determine how to interpret the datagram. The second field in the header contains the number of records in the datagram (indicating the number of expired flows represented by this datagram). Datagram headers for NetFlow Export Versions 5, 8, and 9 also include a "sequence number" field used by NetFlow collectors to check for lost datagrams.
The NetFlow Version 9 export packet header format is shown in Figure 3 .
| Figure 3 | NetFlow Version 9 Export Packet Header Format |
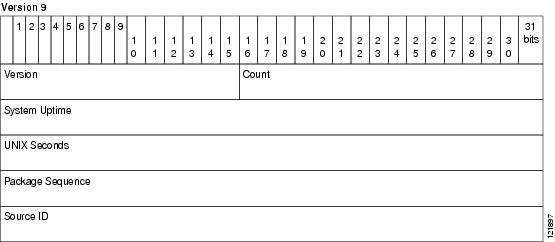
The table below lists the NetFlow Version 9 export packet header field names and descriptions.
| Table 1 | NetFlow Version 9 Export Packet Header Field Names and Descriptions |
| Field Name |
Description |
|---|---|
| Version |
The version of NetFlow records exported in this packet; for Version 9, this value is 0x0009. |
| Count |
Number of FlowSet records (both template and data) contained within this packet. |
| System Uptime |
Time in milliseconds since this device was first booted. |
| UNIX Seconds |
Seconds since 0000 Coordinated Universal Time (UTC) 1970. |
| Package Sequence |
Incremental sequence counter of all export packets sent by this export device; this value is cumulative, and it can be used to find out whether any export packets have been missed. This is a change from the NetFlow Version 5 and Version 8 headers, where this number represented "total flows." |
| Source ID |
The Source ID field is a 32-bit value that is used to guarantee uniqueness for each flow exported from a particular device. (The Source ID field is the equivalent of the engine type and engine ID fields found in the NetFlow Version 5 and Version 8 headers.) The format of this field is vendor-specific. In Cisco's implementation, the first two bytes are reserved for future expansion, and are always zero. Byte 3 provides uniqueness with respect to the routing engine on the exporting device. Byte 4 provides uniqueness with respect to the particular line card or Versatile Interface Processor on the exporting device. Collector devices should use the combination of the source IP address and the source ID field to associate an incoming NetFlow export packet with a unique instance of NetFlow on a particular device. |
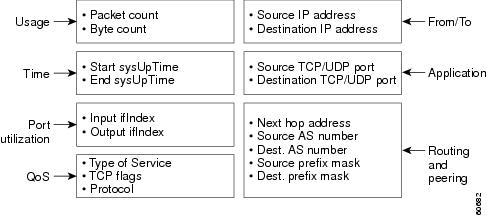
NetFlow Flow Record and Export Format Content Information
This section gives details about the Cisco export format flow record. The table below indicates which flow record format fields are available for Version 5, and 9. (Y indicates that the field is available. N indicates that the field is not available.)
| Table 2 | NetFlow Flow Record Format Fields for Format Versions 5 and 9 |
| Field |
Version 5 |
Version 9 |
|---|---|---|
| source IP address |
Y |
Y |
| destination IP address |
Y |
Y |
| source TCP/UDP application port |
Y |
Y |
| destination TCP/UDP application port |
Y |
Y |
| next hop router IP address |
Y |
Y |
| input physical interface index |
Y |
Y |
| output physical interface index |
Y |
Y |
| packet count for this flow |
Y |
Y |
| byte count for this flow |
Y |
Y |
| start of flow timestamp |
Y |
Y |
| end of flow timestamp |
Y |
Y |
| IP Protocol (for example, TCP=6; UDP=17) |
Y |
Y |
| Type of Service (ToS) byte |
Y |
Y |
| TCP Flags (cumulative OR of TCP flags) |
Y |
Y |
| source AS number |
Y |
Y |
| destination AS number |
Y |
Y |
| source subnet mask |
Y |
Y |
| destination subnet mask |
Y |
Y |
| flags (indicates, among other things, which flows are invalid) |
Y |
Y |
| Other flow fields1 |
N |
Y |
The figure below is an example of the NetFlow Version 5 export record format, including the contents and description of byte locations. The terms in bold indicate values that were added for the Version 5 format.
| Figure 4 | NetFlow Version 5 Export Record Format |
The table below shows the field names and descriptions for the NetFlow Version 5 export record format.
| Table 3 | NetFlow Version 5 Export Record Format Field Names and Descriptions |
| Content |
Bytes |
Descriptions |
|---|---|---|
| srcaddr |
0-3 |
Source IP address |
| dstaddr |
4-7 |
Destination IP address |
| nexthop |
8-11 |
Next hop router's IP address |
| input |
12-13 |
Ingress interface SNMP ifIndex |
| output |
14-15 |
Egress interface SNMP ifIndex |
| dPkts |
16-19 |
Packets in the flow |
| dOctets |
20-23 |
Octets (bytes) in the flow |
| first |
24-27 |
SysUptime at start of the flow |
| last |
28-31 |
SysUptime at the time the last packet of the flow was received |
| srcport |
32-33 |
Layer 4 source port number or equivalent |
| dstport |
34-35 |
Layer 4 destination port number or equivalent |
| pad1 |
36 |
Unused (zero) byte |
| tcp_flags |
37 |
Cumulative OR of TCP flags |
| prot |
38 |
Layer 4 protocol (for example, 6=TCP, 17=UDP) |
| tos |
39 |
IP type-of-service byte |
| src_as |
40-41 |
Autonomous system number of the source, either origin or peer |
| dst_as |
42-43 |
Autonomous system number of the destination, either origin or peer |
| src_mask |
44 |
Source address prefix mask bits |
| dst_mask |
45 |
Destination address prefix mask bits |
| pad2 |
46-47 |
Packet Assembler/Disassembler (PAD) 2 is unused (zero) bytes |
The figure below shows a typical flow record for the Version 9 export format. The NetFlow Version 9 export record format is different from the traditional NetFlow fixed format export record. In NetFlow Version 9, a template describes the NetFlow data and the flow set contains the actual data. This allows for flexible export. Detailed information about the fields currently in Version 9 and the export format architecture are available in the NetFlow Version 9 Flow-Record Format document.
| Figure 5 | NetFlow Version 9 Export Packet Example |
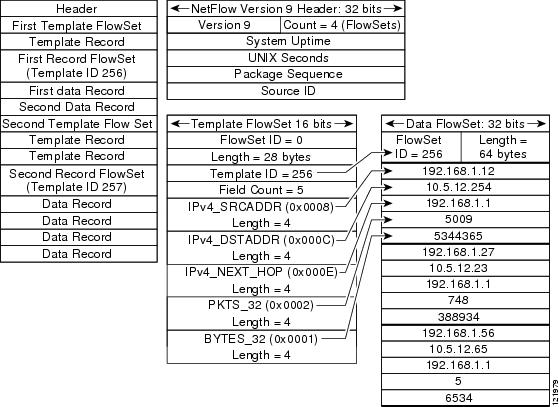
For all export versions, you specify a destination where NetFlow data export packets are sent, such as the workstation running NetFlow Collection Engine, either when the number of recently expired flows reaches a predetermined maximum, or every second--whichever occurs first. For a Version 5 datagram, up to 30 flows can be sent in a single UDP datagram of approximately 1500 bytes.
For detailed information on the flow record formats, data types, and export data fields for Version 9 and platform-specific information when applicable, see Appendix 2 in the NetFlow Solutions Service Guide.
NetFlow Data Export Format Selection
NetFlow exports data in UDP datagrams in export format Version 9, 8, or 5. The table below describes situations when you might select a particular NetFlow export format.
| Table 4 | When to Select a Particular NetFlow Export Format |
| Export Format |
Select When... |
|---|---|
| Version 9 |
You need to export data from various technologies, such as Multicast, DoS, IPv6 and so on. The Version 9 export format supports export from the main cache and from aggregation caches. |
| Version 8 |
You need to export data from aggregation caches. The Version 8 export format is available only for export from aggregation caches. |
| Version 5 |
You need to export data from the NetFlow main cache, and you are not planning to support new features. The Version 5 export format does not support export from aggregation caches. |
NetFlow Version 9 Data Export Format
NetFlow Version 9 data export supports Cisco Express Forwarding switching and fast switching.
NetFlow Version 9 is a flexible and extensible means for transferring NetFlow records from a network node to a collector. NetFlow Version 9 has definable record types and is self-describing for easier NetFlow Collection Engine configuration.
Using Version 9 export, you define new formats on the router that you can send to the NetFlow Collection Engine (formerly called NetFlow FlowCollector) at set intervals. You enable the features that you want, and the field values corresponding to those features are sent to the NetFlow Collection Engine.
Third-party business partners, who produce applications that provide NetFlow Collection Engine or display services for NetFlow need not recompile their applications each time a new NetFlow technology is added. Instead, with the NetFlow v9 Export Format feature, they can use an external data file that documents the known template formats and field types.
In NetFlow Version 9:
- Record formats are defined by templates.
- Template descriptions are communicated from the router to the NetFlow Collection Engine.
- Flow records are sent from the router to the NetFlow Collection Engine with minimal template information so that the NetFlow Collection Engine can relate the records to the appropriate template.
- Version 9 is independent of the underlying transport (UDP, TCP, Stream Control Transmission Protocol (SCTP), and so on).
NetFlow Version 9 Template-Based Flow Record Format
The main feature of the NetFlow Version 9 export format is that it is template based. A template describes a NetFlow record format and attributes of the fields (such as type and length) within the record. The router assigns each template an ID, which is communicated to the NetFlow Collection Engine, along with the template description. The template ID is used for all further communication from the router to the NetFlow Collection Engine.
NetFlow Version 9 Export Flow Records
The basic output of NetFlow is a flow record. In the NetFlow Version 9 export format, a flow record follows the same sequence of fields as found in the template definition. The template to which NetFlow flow records belong is determined by the prefixing of the template ID to the group of NetFlow flow records that belong to a template. For a complete discussion of existing NetFlow flow-record formats, see the NetFlow Services Solutions Guide.
NetFlow Version 9 Export Packet
In NetFlow Version 9, an export packet consists of the packet header and flowsets. The packet header identifies the new version and provides other NetFlow Version 9 Data Export Format Figure 3 for Version 9 export packet header details. Flowsets are of two types: template flowsets and data flowsets. The template flowset describes the fields that will be in the data flowsets (or flow records). Each data flowset contains the values or statistics of one or more flows with the same template ID. When the NetFlow Collection Engine receives a template flowset, it stores the flowset and export source address so that subsequent data flowsets that match the flowset ID and source combination are parsed according to the field definitions in the template flowset. Version 9 supports NetFlow Collection Engine Version 4.0. For an example of a Version 9 export packet, see NetFlow Version 9 Data Export Format.
NetFlow Version 8 Data Export Format
The Version 8 data export format is the NetFlow export format used when the router-based NetFlow aggregation feature is enabled on Cisco IOS XE router platforms. The Version 8 format allows for export datagrams to contain a subset of the Version 5 export data that is based on the configured aggregation cache scheme. For example, a certain subset of the Version 5 export data is exported for the destination prefix aggregation scheme, and a different subset is exported for the source-prefix aggregation scheme.
The Version 8 export format was introduced in the Cisco IOS NetFlow Aggregation feature. An additional six aggregation schemes that also use Version 8 format were defined for the NetFlow ToS-Based Router Aggregation feature. Refer to the Configuring NetFlow Aggregation Caches module for information about configuring Version 8 data export for aggregation caches.
The Version 8 datagram consists of a header with the version number (which is 8) and time stamp information, followed by one or more records corresponding to individual entries in the NetFlow cache.
The figure below displays the NetFlow Version 8 export packet header format.
| Figure 6 | NetFlow Version 8 Export Packet Header Format |

The table below lists the NetFlow Version 8 export packet header field names and definitions.
| Table 5 | NetFlow Version 8 Export Packet Header Field Names and Descriptions |
| Field Name |
Description |
|---|---|
| Version |
Flow export format version number. In this case 8. |
| Count |
Number of export records in the datagram. |
| System Uptime |
Number of milliseconds since the router last booted. |
| UNIX Seconds |
Number of seconds since 0000 UTC 1970. |
| UNIX NanoSeconds |
Number of residual nanoseconds since 0000 UTC 1970. |
| Flow Sequence Number |
Sequence counter of total flows sent for this export stream. |
| Engine Type |
The type of switching engine. Route Processor (RP) = 0 and linecard (LC) = 1. |
| Engine ID |
Slot number of the NetFlow engine. |
| Aggregation |
Type of aggregation scheme being used. |
| Agg Version |
Aggregation subformat version number. The current value is "2." |
| Sampling Interval |
Interval value used if Sampled NetFlow is configured. |
| Reserved |
Reserved. |
NetFlow Version 5 Data Export Format
The Version 5 data export format adds support for BGP autonomous system information and flow sequence numbers.
Because NetFlow uses UDP to send export datagrams, datagrams can be lost. The Version 5 header format contains a flow sequence number to find out whether flow export information has been lost. The sequence number is equal to the sequence number of the previous datagram plus the number of flows in the previous datagram. After receiving a new datagram, the receiving application can subtract the expected sequence number from the sequence number in the header to get the number of missed flows.
All fields in Version 5 export format are in network byte order. The figure below shows the NetFlow Version 5 export packet header format.
| Figure 7 | NetFlow Version 5 Export Packet Header Format |
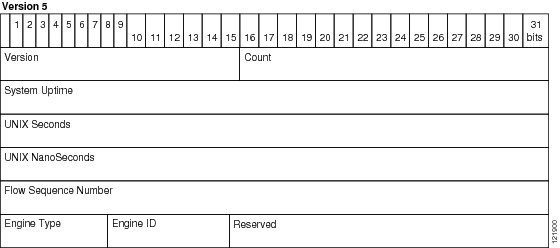
The table below lists the NetFlow Version 5 export packet header field names and descriptions.
| Table 6 | NetFlow Version 5 Export Packet Header Field Names and Descriptions |
| Bytes |
Field |
Description |
|---|---|---|
| 0 to 1 |
Version |
Flow export format version number. In this case 5. |
| 2 to 3 |
Count |
Number of export records in the datagram. |
| 4 to 7 |
System Uptime |
Number of milliseconds since the router last booted. |
| 8 to 11 |
UNIX Seconds |
Number of seconds since 0000 UTC 1970. |
| 12 to 15 |
UNIX NanoSeconds |
Number of residual nanoseconds since 0000 UTC 1970. |
| 16 to 19 |
Flow Sequence Number |
Sequence counter of total flows sent for this export stream. |
| 20 |
Engine Type |
The type of switching engine. RP = 0 and LC = 1. |
| 21 |
Engine ID |
Slot number of the NetFlow engine. |
| 22 to 23 |
Reserved |
Reserved. |
The table below lists the byte definitions for the Version 5 flow record format.
| Table 7 | Version 5 Flow Record Format |
| Bytes |
Content |
Description |
|---|---|---|
| 0 to 3 |
srcaddr |
Source IP address. |
| 4 to 7 |
dstaddr |
Destination IP address. |
| 8 to 11 |
nexthop |
IP address of the next hop router. |
| 12 to 15 |
input and output |
SNMP index of the input and output interfaces. |
| 16 to 19 |
dPkts |
Packets in the flow. |
| 20 to 23 |
dOctets |
Total number of Layer 3 bytes in the flow's packets. |
| 24 to 27 |
First |
SysUptime at start of flow. |
| 28 to 31 |
Last |
SysUptime at the time the last packet of flow was received. |
| 32 to 35 |
srcport and dstport |
TCP/UDP source and destination port number or equivalent. |
| 36 to 39 |
pad1, tcp_flags, prot, and tos |
Unused (zero) byte, cumulative OR of TCP flags, IP protocol (for example, 6 = TCP, 17 = UDP), and IP ToS. |
| 40 to 43 |
src_as and dst_as |
Autonomous system of the source and destination, either origin or peer. |
| 44 to 47 |
src_mask, dst_mask, and pad2 |
Source and destination address prefix mask bits. PAD 2 is unused (zero) bytes. |
Egress NetFlow Accounting Benefits NetFlow Accounting Simplified
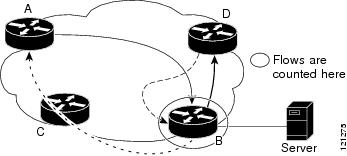
The Egress NetFlow Accounting feature can simplify NetFlow configuration, which is illustrated in the following example.
In the figures below, both incoming and outgoing (ingress and egress) flow statistics are required for the server. The server is attached to Router B. The "cloud" in the figure represents the core of the network and includes MPLS VPNs.
All traffic denoted by the arrows must be accounted for. The solid arrows represent IP traffic and the dotted arrows represent MPLS VPNs.
The first figure below shows how the flow traffic was tracked before the introduction of the Egress NetFlow Accounting feature. The second figure below shows how the flow traffic is tracked after the introduction of the Egress NetFlow Accounting feature. The Egress NetFlow Accounting feature simplifies configuration tasks and makes it easier for you to collect and track incoming and outgoing flow statistics for the server in this example.
Because only ingress flows could be tracked before the Egress NetFlow Accounting feature was introduced, the following NetFlow configurations had to be implemented for the tracking of ingress and egress flows from Router B:
- Enable NetFlow on an interface on Router B to track ingress IP traffic from Router A to Router B.
- Enable NetFlow on an interface on Router D to track ingress IP traffic from Router B to Router D.
- Enable NetFlow on an interface on Router A to track ingress traffic from the MPLS VPN from Router B to Router A.
- Enable NetFlow on an interface on Router B to track ingress traffic from the MPLS VPN from Router D to Router B.
| Figure 8 | Ingress-Only NetFlow Example |

A configuration such as the one used in the figure above requires that NetFlow statistics from three separate routers be added together to obtain the flow statistics for the server.
In comparison, the example in the figure below shows NetFlow, the Egress NetFlow Accounting feature, and the MPLS Egress NetFlow Accounting feature being used to capture ingress and egress flow statistics for Router B, thus obtaining the required flow statistics for the server.
In the figure below, the following NetFlow configurations are applied to Router B:
- Enable NetFlow on an interface on Router B to track ingress IP traffic from Router A to Router B.
- Enable the Egress NetFlow Accounting feature on an interface on Router B to track egress IP traffic from Router B to Router D.
- Enable NetFlow an interface on Router B to track ingress traffic from the MPLS VPN from Router B to Router D.
- Enable NetFlow on an interface on Router B to track ingress traffic from the MPLS VPN from Router B to Router A.
After NetFlow is configured on Router B, you can display all NetFlow statistics for the server by entering the show ip cache flow command or the show ip cache verbose flow command for Router B.
| Figure 9 | Egress NetFlow Accounting Example |
NetFlow Subinterface Support Benefits Fine-Tuning Your Data Collection
You can configure NetFlow on a per-subinterface basis. If your network contains thousands of subinterfaces and you want to collect export records from only a few subinterfaces, you can do that. The result is lower bandwidth requirements for NetFlow data export and reduced platform requirements for NetFlow data-collection devices.
The configuration of NetFlow on selected subinterfaces provides the following benefits:
- Reduced bandwidth requirement between routing devices and NetFlow management workstations.
- Reduced NetFlow workstation requirements; the number of flows sent to the workstation for processing is reduced.
NetFlow Multiple Export Destinations Benefits
The NetFlow Multiple Export Destinations feature enables configuration of multiple destinations for the NetFlow data. With this feature enabled, two identical streams of NetFlow data are sent to the destination host. Currently, the maximum number of export destinations allowed is two.
The NetFlow Multiple Export Destinations feature improves the chances of receiving complete NetFlow data because it provides redundant streams of data. Because the same export data is sent to more than one NetFlow collector, fewer packets are lost.
How to Configure NetFlow and NetFlow Data Export
- Configuring NetFlow
- Verifying That NetFlow Is Operational and Viewing NetFlow Statistics
- Configuring NetFlow Data Export Using the Version 9 Export Format
- Verifying That NetFlow Data Export Is Operational
- Clearing NetFlow Statistics on the Router
- Customizing the NetFlow Main Cache Parameters
Configuring NetFlow
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
|
|
Example: Router> enable |
(Required) Enables privileged EXEC mode.
|
||
|
|
Example: Router# configure terminal |
(Required) Enters global configuration mode. |
||
|
|
Example: Router(config)# interface fastethernet 0/0/0 |
(Required) Specifies the interface that you want to enable NetFlow on and enters interface configuration mode. |
||
|
|
Example: Router(config-if)# ip flow ingress |
(Required) Enables NetFlow on the interface.
This is the Egress NetFlow Accounting feature that is described in the Egress NetFlow Accounting Benefits NetFlow Accounting Simplified. |
||
|
|
Example: Router(config-if)# exit |
(Optional) Exits interface configuration mode and returns to global configuration mode.
|
||
|
|
|
(Optional) -- |
||
|
|
Example: Router(config-if)# end |
(Required) Exits the current configuration mode and returns to privileged EXEC mode. |
Verifying That NetFlow Is Operational and Viewing NetFlow Statistics
To verify that NetFlow is operational and to view the NetFlow statistics, perform the following steps.
DETAILED STEPS
| Step 1 | enable Use this command to enable privileged EXEC mode. Enter your password if prompted. Example:
Router> enable
Router# |
| Step 2 | show ip cache flow Use this command to verify that NetFlow is operational and to display a summary of the NetFlow statistics. The following is sample output from this command: Example:
Router# show ip cache flow
IP packet size distribution (1103746 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.249 .694 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.000 .000 .027 .000 .027 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
35 active, 4061 inactive, 980 added
2921778 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 21640 bytes
0 active, 1024 inactive, 0 added, 0 added to flow
0 alloc failures, 0 force free
1 chunk, 1 chunk added
last clearing of statistics never
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
-------- Flows /Sec /Flow /Pkt /Sec /Flow /Flow
TCP-FTP 108 0.0 1133 40 2.4 1799.6 0.9
TCP-FTPD 108 0.0 1133 40 2.4 1799.6 0.9
TCP-WWW 54 0.0 1133 40 1.2 1799.6 0.8
TCP-SMTP 54 0.0 1133 40 1.2 1799.6 0.8
TCP-BGP 27 0.0 1133 40 0.6 1799.6 0.7
TCP-NNTP 27 0.0 1133 40 0.6 1799.6 0.7
TCP-other 297 0.0 1133 40 6.8 1799.7 0.8
UDP-TFTP 27 0.0 1133 28 0.6 1799.6 1.0
UDP-other 108 0.0 1417 28 3.1 1799.6 0.9
ICMP 135 0.0 1133 427 3.1 1799.6 0.8
Total: 945 0.0 1166 91 22.4 1799.6 0.8
SrcIf SrcIPaddress DstIf DstIPaddress Pr SrcP DstP Pkts
FEt0/0/0 192.168.67.6 FEt1/0/0.1 172.16.10.200 01 0000 0C01 51
FEt0/0/0 10.10.18.1 Null 172.16.11.5 11 0043 0043 51
FEt0/0/0 10.10.18.1 Null 172.16.11.5 11 0045 0045 51
FEt0/0/0 10.234.53.1 FEt1/0/0.1 172.16.10.2 01 0000 0800 51
FEt0/0/0 10.10.19.1 Null 172.16.11.6 11 0044 0044 51
FEt0/0/0 10.10.19.1 Null 172.16.11.6 11 00A2 00A2 51
FEt0/0/0 192.168.87.200 FEt1/0/0.1 172.16.10.2 06 0014 0014 50
FEt0/0/0 192.168.87.200 FEt1/0/0.1 172.16.10.2 06 0015 0015 52
.
.
.
FEt0/0/0 172.16.1.84 FEt1/0.1 172.16.10.19 06 0087 0087 50
FEt0/0/0 172.16.1.84 FEt1/0.1 172.16.10.19 06 0050 0050 51
FEt0/0/0 172.16.1.85 FEt1/0.1 172.16.10.20 06 0089 0089 49
FEt0/0/0 172.16.1.85 FEt1/0.1 172.16.10.20 06 0050 0050 50
FEt0/0/0 10.251.10.1 FEt1/0.1 172.16.10.2 01 0000 0800 51
FEt0/0/0 10.162.37.71 Null 172.16.11.3 06 027C 027C 49
Router#
|
| Step 3 | show ip cache verbose flow Use this command to verify that NetFlow is operational and to display a detailed summary of the NetFlow statistics. The following is sample output from this command: Example:
Router# show ip cache verbose flow
ToS
IP packet size distribution (1130681 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.249 .694 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.000 .000 .027 .000 .027 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
35 active, 4061 inactive, 980 added
2992518 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 21640 bytes
0 active, 1024 inactive, 0 added, 0 added to flow
0 alloc failures, 0 force free
1 chunk, 1 chunk added
last clearing of statistics never
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
-------- Flows /Sec /Flow /Pkt /Sec /Flow /Flow
TCP-FTP 108 0.0 1133 40 2.4 1799.6 0.9
TCP-FTPD 108 0.0 1133 40 2.4 1799.6 0.9
TCP-WWW 54 0.0 1133 40 1.2 1799.6 0.8
TCP-SMTP 54 0.0 1133 40 1.2 1799.6 0.8
TCP-BGP 27 0.0 1133 40 0.6 1799.6 0.7
TCP-NNTP 27 0.0 1133 40 0.6 1799.6 0.7
TCP-other 297 0.0 1133 40 6.6 1799.7 0.8
UDP-TFTP 27 0.0 1133 28 0.6 1799.6 1.0
UDP-other 108 0.0 1417 28 3.0 1799.6 0.9
ICMP 135 0.0 1133 427 3.0 1799.6 0.8
Total: 945 0.0 1166 91 21.9 1799.6 0.8
SrcIf SrcIPaddress DstIf DstIPaddress Pr TOS Flgs Pkts
Port Msk AS Port Msk AS NextHop B/Pk Active
FEt0/0/0 192.168.67.6 FEt1/0.1 172.16.10.200 01 00 10 799
0000 /0 0 0C01 /0 0 0.0.0.0 28 1258.1
FEt0/0/0 10.10.18.1 Null 172.16.11.5 11 00 10 799
0043 /0 0 0043 /0 0 0.0.0.0 28 1258.0
FEt0/0/0 10.10.18.1 Null 172.16.11.5 11 00 10 799
0045 /0 0 0045 /0 0 0.0.0.0 28 1258.0
FEt0/0/0 10.234.53.1 FEt1/0.1 172.16.10.2 01 00 10 799
0000 /0 0 0800 /0 0 0.0.0.0 28 1258.1
FEt0/0/0 10.10.19.1 Null 172.16.11.6 11 00 10 799
0044 /0 0 0044 /0 0 0.0.0.0 28 1258.1
.
.
.
FEt0/0/0 172.16.1.84 FEt1/0/0.1 172.16.10.19 06 00 00 799
0087 /0 0 0087 /0 0 0.0.0.0 40 1258.1
FEt0/0/0 172.16.1.84 FEt1/0/0.1 172.16.10.19 06 00 00 799
0050 /0 0 0050 /0 0 0.0.0.0 40 1258.0
FEt0/0/0 172.16.1.85 FEt1/0/0.1 172.16.10.20 06 00 00 798
0089 /0 0 0089 /0 0 0.0.0.0 40 1256.5
FEt0/0/0 172.16.1.85 FEt1/0/0.1 172.16.10.20 06 00 00 799
0050 /0 0 0050 /0 0 0.0.0.0 40 1258.0
FEt0/0/0 10.251.10.1 FEt1/0/0.1 172.16.10.2 01 00 10 799
0000 /0 0 0800 /0 0 0.0.0.0 1500 1258.1
FEt0/0/0 10.162.37.71 Null 172.16.11.3 06 00 00 798
027C /0 0 027C /0 0 0.0.0.0 40 1256.4
Router#
|
| Step 4 | end Use this command to exit privileged EXEC mode. Example:
Router# end
|
Configuring NetFlow Data Export Using the Version 9 Export Format
This task does not include the steps for configuring NetFlow. You must configure NetFlow by enabling it on at least one interface in the router in order to export traffic data with NetFlow Data Export. Refer to the Configuring NetFlow for information about configuring NetFlow.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
|
|
Example: Router> enable |
(Required) Enters privileged EXEC mode.
|
||
|
|
Example: Router# configure terminal |
(Required) Enters global configuration mode. |
||
|
|
Example: Router(config)# ip flow-export destination 172.16.10.2 99 |
(Required) Specifies the IP address or hostname of the NetFlow collector, and the UDP port the NetFlow collector is listening on. |
||
|
|
|
(Optional) You can configure a maximum of two export destinations for NetFlow. This is the NetFlow Multiple Export Destinations feature that is described in the NetFlow Multiple Export Destinations Benefits. |
||
|
|
Example: Router(config)# ip flow-export source fastethernet 0/0/0 |
(Optional) The IP address of the interface specified is used as the source IP address for the UDP datagrams that are sent by NetFlow data export to the destination host.
|
||
|
|
Example: Router(config)# ip flow-export version 9 |
(Optional) Enables the export of information in NetFlow cache entries.
|
||
|
|
Example: Router(config)# ip flow-export template refresh-rate 15 |
(Optional) Enables the export of information in NetFlow cache entries.
|
||
|
|
Example: Router(config)# ip flow-export template timeout-rate 90 |
(Optional) Enables the export of information in NetFlow cache entries.
|
||
|
|
Example: Router(config)# ip flow-export template options export-stats |
(Optional) Enables the export of information in NetFlow cache entries.
|
||
|
|
Example: Router(config)# ip flow-export template options refresh-rate 25 |
(Optional) Enables the export of information in NetFlow cache entries.
|
||
|
|
Example: Router(config)# ip flow-export template options timeout-rate 120 |
(Optional) Enables the export of information in NetFlow cache entries.
|
||
|
|
Example: Router(config)# end |
(Required) Exits the current configuration mode and returns to privileged EXEC mode. |
Verifying That NetFlow Data Export Is Operational
To verify that NetFlow data export is operational and to view the statistics for NetFlow data export, perform the following task.
DETAILED STEPS
| Step 1 | enable Use this command to enable privileged EXEC mode. Enter your password if prompted. Example:
Router> enable
Router# |
| Step 2 | show ip flow export Use this command to display the statistics for the NetFlow data export, including statistics for the main cache and for all other enabled caches. The following is sample output from this command: Example:
Router# show ip flow export
Flow export v9 is enabled for main cache
Exporting flows to 172.16.10.2 (99)
Exporting using source interface FastEthernet0/0/0
Version 9 flow records
0 flows exported in 0 udp datagrams
0 flows failed due to lack of export packet
0 export packets were sent up to process level
0 export packets were dropped due to no fib
0 export packets were dropped due to adjacency issues
0 export packets were dropped due to fragmentation failures
0 export packets were dropped due to encapsulation fixup failures
Router#
|
| Step 3 | show ip flow export template Use this command to display the statistics for the NetFlow data export (such as the template timeout rate and the refresh rate) for the template-specific configurations. The following is sample output from this command: Example:
Router# show ip flow export template
Template Options Flag = 1
Total number of Templates added = 1
Total active Templates = 1
Flow Templates active = 0
Flow Templates added = 0
Option Templates active = 1
Option Templates added = 1
Template ager polls = 0
Option Template ager polls = 140
Main cache version 9 export is enabled
Template export information
Template timeout = 90
Template refresh rate = 15
Option export information
Option timeout = 120
Option refresh rate = 25
Router#
|
| Step 4 | end Use this command to exit privileged EXEC mode. Example:
Router# end
|
Clearing NetFlow Statistics on the Router
To clear NetFlow statistics on the router, perform the following task.
DETAILED STEPS
| Step 1 | enable Use this command to enable privileged EXEC mode. Enter your password if prompted. Example:
Router> enable
Router#
|
| Step 2 | clear ip flow stats Use this command to clear the NetFlow statistics on the router. For example: Example:
Router# clear ip flow stats
|
| Step 3 | end Use this command to exit privileged EXEC mode. Example:
Router# end
|
Customizing the NetFlow Main Cache Parameters
NetFlow operates by creating a NetFlow cache entry (a flow record) for each active flow. A flow record is maintained within the NetFlow cache for all active flows. Each flow record in the NetFlow cache contains fields that can later be exported to a collection device, such as the NetFlow Collection Engine. NetFlow enables the accumulation of data on flows. Each flow is identified by unique characteristics such as IP address, interface, application, and ToS.
To customize the parameters for the main NetFlow cache, perform the following steps.
NetFlow Cache Entry Management on a Routing Device
The routing device checks the NetFlow cache once per second and causes the flow to expire in the following instances:
- The flow cache has become full.
- A flow becomes inactive. By default, a flow unaltered in the last 15 seconds is classified as inactive.
- An active flow has been monitored for a specified number of minutes. By default, active flows are flushed from the cache when they have been monitored for 30 minutes.
Routing device default timer settings are 15 seconds for the inactive timer and 30 minutes for the active timer. You can configure your own time interval for the inactive timer between 10 and 600 seconds. You can configure the time interval for the active timer between 1 and 60 minutes.
NetFlow Cache Size
After you enable NetFlow on an interface, NetFlow reserves memory to accommodate a number of entries in the NetFlow cache. Normally, the size of the NetFlow cache meets the needs of your NetFlow traffic rates. The cache default size is 64K flow cache entries. Each cache entry requires 64 bytes of storage. About 4 MB of DRAM are required for a cache with the default number of entries. You can increase or decrease the number of entries maintained in the cache, if required. For environments with a large amount of flow traffic (such as an Internet core router), we recommend a larger value such as 131072 (128K). To obtain information on your flow traffic, use the show ip cache flow command.
Using the ip flow-cache entries command, you can configure the size of your NetFlow cache between 1024 entries and 524,288 entries. Using the cache entries command (after you configure NetFlow aggregation), you can configure the size of the NetFlow aggregation cache from 1024 entries to 2,000,000 entries.
 Caution |
We recommend that you not change the values for NetFlow cache entries. Improper use of this feature could cause network problems. To return to the default value for NetFlow cache entries, use the no ip flow-cache entries global configuration command. |
 Note |
If you modify any parameters for the NetFlow main cache after you enable NetFlow, the changes will not take effect until you reboot the router or disable NetFlow on every interface it is enabled on, and then re-enable NetFlow on the interfaces. |
DETAILED STEPS
Configuration Examples for NetFlow and NetFlow Data Export
- Example Configuring Egress NetFlow Accounting
- Example Configuring NetFlow Subinterface Support
- Example Configuring NetFlow Multiple Export Destinations
- Example Configuring NetFlow Version 5 Data Export
Example Configuring Egress NetFlow Accounting
The following example shows how to configure Egress NetFlow Accounting:
configure terminal ! interface fastethernet 0/0/0 ip flow egress !
Example Configuring NetFlow Subinterface Support
This section contains examples for configuring NetFlow Subinterface Support, and contains the following examples:
- Example NetFlow Subinterface Support for Ingress (Received) Traffic on a Subinterface
- Example NetFlow SubInterface Support for Egress (Transmitted) Traffic on a Subinterface
Example NetFlow Subinterface Support for Ingress (Received) Traffic on a Subinterface
configure terminal ! interface fastethernet 0/0/0.1 ip flow ingress !
Example NetFlow SubInterface Support for Egress (Transmitted) Traffic on a Subinterface
configure terminal ! interface fastethernet 1/0/0.1 ip flow egress !
 Note |
NetFlow performs additional checks for the status of each subinterface that requires more CPU processing time and bandwidth. If you have several subinterfaces configured and you want to configure NetFlow data capture on all of them, we recommend that you configure NetFlow on the main interface instead of on the individual subinterfaces. |
Example Configuring NetFlow Multiple Export Destinations
The following example shows how to configure the NetFlow Multiple Export Destinations feature:
configure terminal ! ip flow-export destination 10.10.10.10 9991 ip flow-export destination 172.16.10.2 9991 !
 Note |
You can configure a maximum of two export destinations for the main cache and for each aggregation cache. |
Example Configuring NetFlow Version 5 Data Export
The following example shows how to configure the NetFlow data export using the Version 5 export format with the peer AS information.
configure terminal
!
ip flow-export version 5 peer-as ip flow-export destination 172.16.10.2 99 exit Router# show ip flow export Flow export v5 is enabled for main cache Exporting flows to 172.16.10.2 (99) Exporting using source IP address 172.16.6.1 Version 5 flow records, peer-as 0 flows exported in 0 udp datagrams 0 flows failed due to lack of export packet 0 export packets were sent up to process level 0 export packets were dropped due to no fib 0 export packets were dropped due to adjacency issues 0 export packets were dropped due to fragmentation failures 0 export packets were dropped due to encapsulation fixup failures Router#
Additional References
Related Documents
| Related Topic |
Document Title |
|---|---|
| Cisco IOS commands |
|
| NetFlow commands: complete command syntax, command modes, command history, defaults, usage guidelines, and examples |
Cisco IOS NetFlow Command Reference |
| Tasks for configuring NetFlow input filters |
Using NetFlow Filtering or Sampling to Select the Network Traffic to Track |
| Tasks for configuring Random Sampled NetFlow |
Using NetFlow Filtering or Sampling to Select the Network Traffic to Track |
| Tasks for configuring NetFlow aggregation caches |
Configuring NetFlow Aggregation Caches |
| Information for installing, starting, and configuring the CNS NetFlow Collection Engine |
|
| Discussion of NetFlow flow-record formats |
NetFlow Services Solutions Guide |
Standards
| Standards |
Title |
|---|---|
| No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature. |
-- |
MIBs
| MIBs |
MIBs Link |
|---|---|
| No new or modified MIBs are supported by this feature, and support for existing MIBs has not been modified by this feature. |
To locate and download MIBs for selected platforms, Cisco software releases, and feature sets, use Cisco MIB Locator found at the following URL: |
RFCs
| RFCs |
Title |
|---|---|
| No new or modified RFCs are supported by this feature, and support for existing RFCs has not been modified by this feature. |
-- |
Technical Assistance
| Description |
Link |
|---|---|
| The Cisco Support and Documentation website provides online resources to download documentation, software, and tools. Use these resources to install and configure the software and to troubleshoot and resolve technical issues with Cisco products and technologies. Access to most tools on the Cisco Support and Documentation website requires a Cisco.com user ID and password. |
Feature Information for Configuring NetFlow and NetFlow Data Export
The following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
| Table 8 | Feature Information for Configuring NetFlow and NetFlow Data Export |
| Feature Name |
Releases |
Feature Configuration Information |
|---|---|---|
| Egress NetFlow Accounting |
Cisco IOS XE Release 2.1 |
The Egress NetFlow Accounting feature allows NetFlow statistics to be gathered on egress traffic that is exiting the router. Previous versions of NetFlow allow statistics to be gathered only on ingress traffic that enters the router. In Cisco IOS XE Release 2.1, this feature was introduced on Cisco ASR 1000 Series Routers. The following commands were modified by this feature: flow-sampler, ip flow egress, ip flow-egress input-interface, match, show ip cache flow, show ip cache verbose flow, show ip flow interface. |
| NetFlow |
Cisco IOS XE Release 2.1 |
NetFlow is a Cisco IOS XE application used to capture network traffic data. It provides statistics on packets flowing through the router, and is emerging as a primary network accounting and security technology. In Cisco IOS XE Release 2.1, this feature was introduced on Cisco ASR 1000 Series Aggregation Services Routers. The following commands were modified by this feature: flow-sampler, ip flow egress, ip flow-egress input-interface, match, show ip cache flow, show ip cache verbose flow, show ip flow interface. |
| NetFlow Multiple Export Destinations |
Cisco IOS XE Release 2.1 |
The NetFlow Multiple Export Destinations feature enables configuration of multiple destinations of the NetFlow data. In Cisco IOS XE Release 2.1, this feature was introduced on Cisco ASR 1000 Series Routers. The following commands were modified by this feature: ip flow-aggregation cache, ip flow-export destination, show ip flow export. |
| NetFlow Subinterface Support |
Cisco IOS XE Release 2.1 |
The NetFlow Subinterface Support feature provides the ability to enable NetFlow on a per-subinterface basis. In Cisco IOS XE Release 2.1, this feature was introduced on Cisco ASR 1000 Series Routers. The following commands were introduced or modified by this feature: ip flow ingress, show ip interface. |
| NetFlow v9 Export Format (Netflow Data Export [NDE] Version 5) (Netflow Data Export [NDE] Version 8) |
Cisco IOS XE Release 2.1 |
The NetFlow v9 Export Format is flexible and extensible, which provides the versatility needed to support new fields and record types. This format accommodates new NetFlow-supported technologies such as Multicast and Network Address Translation (NAT). In Cisco IOS XE Release 2.1, this feature was introduced on Cisco ASR 1000 Series Routers. The following commands were modified by this feature: debug ip flow export, export, ip flow-export, show ip flow export. |
Glossary
AS --autonomous system. A collection of networks under a common administration sharing a common routing strategy. Autonomous systems are subdivided by areas. An autonomous system must be assigned a unique 16-bit number by the Internet Assigned Numbers Authority (IANA).
Cisco Express Forwarding --Layer 3 IP switching technology that optimizes network performance and scalability for networks with large and dynamic traffic patterns.
BGP --Border Gateway Protocol. An interdomain routing protocol that replaces Exterior Gateway Protocol (EGP). A BGP system exchanges reachability information with other BGP systems. BGP is defined by RFC 1163.
BGP next hop --IP address of the next hop to be used by a router to reach a certain destination.
export packet --Type of packet built by a device (for example, a router) with NetFlow services enabled that is addressed to another device (for example, the NetFlow Collection Engine). The packet contains NetFlow statistics. The other device processes the packet (parses, aggregates, and stores information on IP flows).
fast switching --Cisco feature in which a route cache is used to expedite packet switching through a router.
flow --A set of packets with the same source IP address, destination IP address, protocol, source/destination ports, and type-of-service, and the same interface on which the flow is monitored. Ingress flows are associated with the input interface, and egress flows are associated with the output interface.
NetFlow --A Cisco IOS XE application that provides statistics on packets flowing through the router. It is emerging as a primary network accounting and security technology.
NetFlow Aggregation --A NetFlow feature that lets you summarize NetFlow export data on an Cisco IOS router before the data is exported to a NetFlow data collection system such as the NetFlow Collection Engine. This feature lowers bandwidth requirements for NetFlow export data and reduces platform requirements for NetFlow data collection devices.
NetFlow v9 --NetFlow export format Version 9. A flexible and extensible means for carrying NetFlow records from a network node to a collector. NetFlow Version 9 has definable record types and is self-describing for easier NetFlow Collection Engine configuration.
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.
 Feedback
Feedback