N+1 High Availability Deployment Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- September 17, 2014
Chapter: N+1 High Availability Overview
N+1 High Availability Overview
N+1 HA Overview
- The N+1 HA architecture provides redundancy for controllers across geographically separate data centers with low cost of deployment.
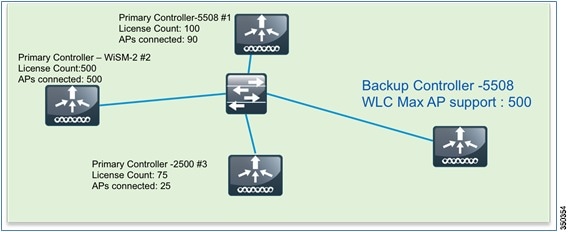
- A single backup controller can be used in order to provide backup for multiple primary WLCs, with consideration for appropriate compatibility in terms of AP mode. (See Figure 2-1)
- These WLCs are independent of each other and do not share configuration or IP addresses on any of their interfaces. Each WLC needs to be managed separately by Cisco Prime, can run a different hardware and a different software version, and can be deployed in different datacenters across the WAN link.
- Access Point Stateful Switch Over (AP SSO) functionality is not supported for N+1 HA. The AP Control and Provisioning of Wireless Access Points (CAPWAP) state machine is restarted when the primary controller fails.
- When a primary WLC resumes operation, the APs fall back from the backup WLC to the primary WLC automatically if the AP fallback option is enabled.
- APs with high priority on the primary controller always connect first to the backup controller, even if they have to push out low priority APs.
- When using a permanent AP count license for the backup controller, the 90-day timer does not start when the APs join the backup controller.
- With Release 7.4, an HA-SKU secondary controller can be configured as a backup controller for N+1 HA. For example, the following can be used as an HA-SKU controller:
–![]() 5508 Series Standalone controller with 50 AP license
5508 Series Standalone controller with 50 AP license
–![]() WiSM-2 Wireless LAN controller
WiSM-2 Wireless LAN controller
–![]() 7500 Series Standalone controller
7500 Series Standalone controller
–![]() 8500 Series Standalone controller
8500 Series Standalone controller
–![]() 2504 Wireless LAN controller, Release 7.5,with a minimum of 5 Permanent AP licenses
2504 Wireless LAN controller, Release 7.5,with a minimum of 5 Permanent AP licenses
- As soon as an AP joins the HA-SKU secondary controller, the 90-day timer starts, and the user sees a warning message after 90 days. In other words, an HA-SKU controller can be used as a secondary controller for 90 days without a warning message.
- The HA-SKU Unique Device Identifier (UDI) provides the capability of the maximum number of APs supported on that hardware. For instance, a 5508 HA- SKU controller provides support for 500 APs.
- The N+1 Secondary HA-SKU cannot be configured in combination with AP SSO. They are mutually exclusive.
Supported Hardware
N+1 HA with HA-SKU is supported on the 2504, 5500, 7500, and 8500 Series of standalone controllers as well as the WiSM-2 WLCs.
Configuration of N+1 HA with HA-SKU with the CLI
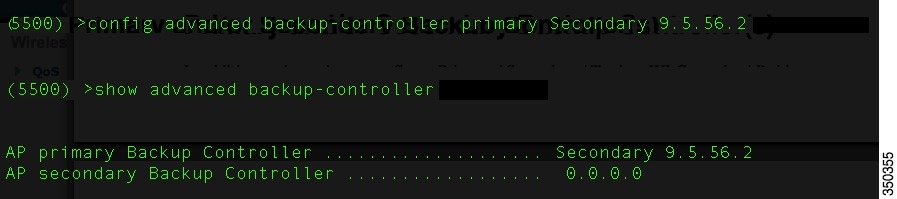
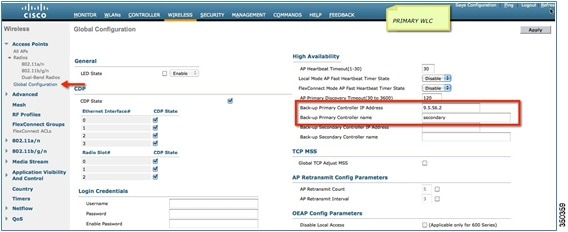
From the primary controller, configure the backup controller on the primary to point to the secondary controller. Use the config advanced backup-controller primary backup_controller_name backup_controller_IP_address command. (See Figure 2-2.)
Configuration of HA-SKU UDI as HA-SKU Secondary Controller
On the HA-SKU UDI controller, execute the config redundancy unit secondary command to obtain support for Max AP count licenses on a given hardware. Evaluation license does not need to be enabled for this purpose.
The section below depicts the process of converting a permanent AP count WLC to a HA-SKU secondary controller.
Configuration of Permanent AP Count WLC as HA-SKU Secondary Controller
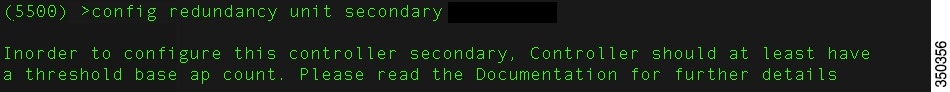
On the permanent AP count WLC, use the config redundancy unit secondary command to convert the controller into an HA-SKU secondary controller. In order to convert a permanent AP count controller to an HA-SKU secondary controller, it should have a minimum number of base AP count licenses; if that minimum is not met, an error message appears. (See Figure 2-3).
Figure 2-3 Secondary WLC (CLI)
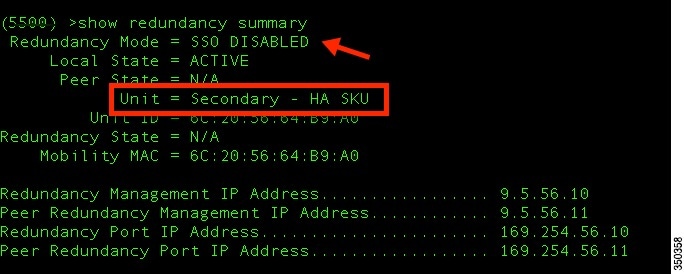
On the CLI, use the show redundancy summary command to view the status of the primary and secondary controllers. (See Figure 2-4 and Figure 2-5.)

Note![]() With release 7.5 and 7.6, the HA SKU WLC has to be rebooted after issuing the command "config redundancy unit secondary" to make APs join it.
With release 7.5 and 7.6, the HA SKU WLC has to be rebooted after issuing the command "config redundancy unit secondary" to make APs join it.
Figure 2-4 Status of Primary WLC (CLI)
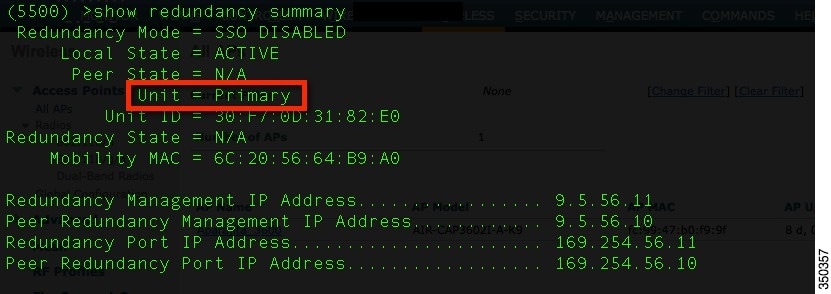
Figure 2-5 Status of HA-SKU Secondary WLC (CLI)
Configuration of N+1 HA with HA-SKU with the GUI
From the primary controller, navigate to Access Points > Global Configuration, then configure the backup controller on the primary to point to the secondary controller. (See Figure 2-6.)
On the secondary controller, navigate to Redundancy > Global Configuration, then configure the secondary controller to convert it to an HA-SKU secondary controller. (SeeFigure 2-7)
Figure 2-7 HA-SKU Secondary WLC (GUI)
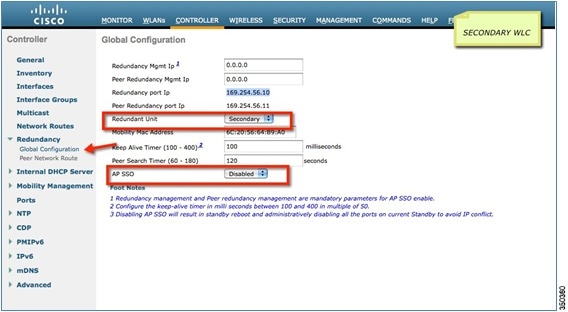

Note![]() AP SSO must be disabled to configure the controller to be an N+1 HA-SKU secondary controller.
AP SSO must be disabled to configure the controller to be an N+1 HA-SKU secondary controller.
Primary, Secondary, and Tertiary Redundancy with HA-SKU
An HA-SKU secondary controller can also be used as a primary, secondary, or tertiary controller. This can be configured under the AP specific configuration. (See Figure 2-8.)
Figure 2-8 Primary, Secondary, and Tertiary Configuration (GUI)

The configuration on HA-SKU secondary controller is the same as shown previously.
 Feedback
Feedback