Nexus 1000v Quickstart with Hyper-V Server Configuration Example
Available Languages
Contents
Introduction
This document describes how to configure Microsoft (MS) Windows Hyper-V Server 2012, install drivers, and add it to System Center Virtual Machine Manager (SCVMM). It also describes how to install and configure the Cisco Nexus 1000v Series switch, and add Virtual Machines (VMs) to the Nexus 1000v.
Prerequisites
Requirements
This document introduces MS Windows Hyper-V Server 2012 and the Cisco Nexus 1000v Series switch. However, you should have some experience/knowledge with basic Windows features configuration and installation, such as Failover Clustering.
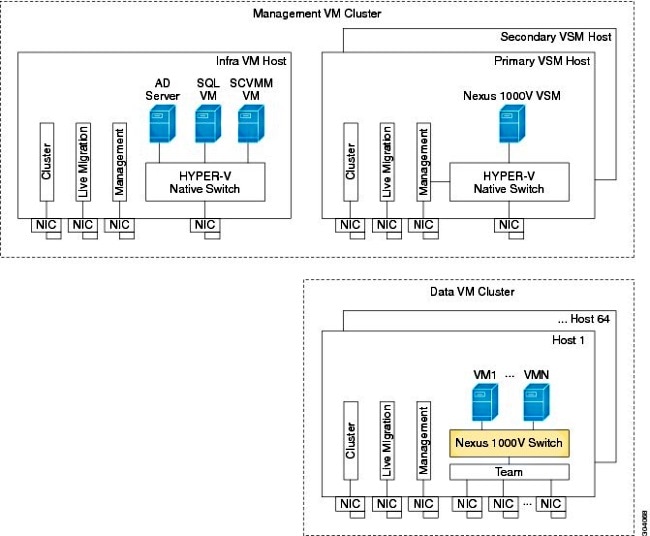
These are the requirements for this deployment:
- Active Directory
- Domain Name Server (DNS)
- Two Management/Infrastructure Hyper-V Hosts
- At Least One Data Hyper-V Host
- SCVMM Server
- Windows 2012 Jumpserver
This image is taken from the Cisco Nexus 1000v Series Switch Deployment Guide:
Components Used
This deployment uses Microsoft Hyper-V 2012 Server 2012, Nexus 1000v for Hyper-V, and SCVMM.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Background Information
Hyper-V core was released in parallel with Windows Server 2012. It only runs the Server Core installation of Server 2012 (which means no GUI, only CLI), and only runs Hyper-V and some related roles, such as Clustering. The advantage of this is that Hyper-V core is completely free, except for support.
Install Windows Hyper-V Server
The Hyper-V server installs like any other Windows installation, which means you have to complete these steps:
- Reduce paths to storage down to one if you use Storage Area Network (SAN) storage.
- Install the required drivers when you use the installation wizard.
The Hyper-V Server installation process is outside the scope of this document. However, it works like any other Windows installation.
Introduction to Windows Core
MS is promoting the Server Core, which was introduced in 2008. The free version of Hyper-V only comes with Windows Core. However, with full installations, you can move between the two with a reboot.
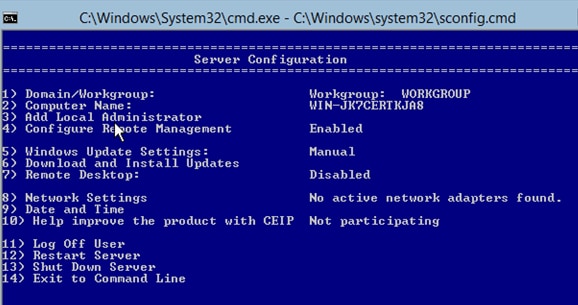
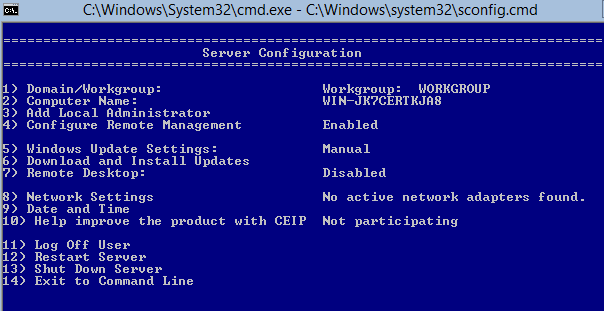
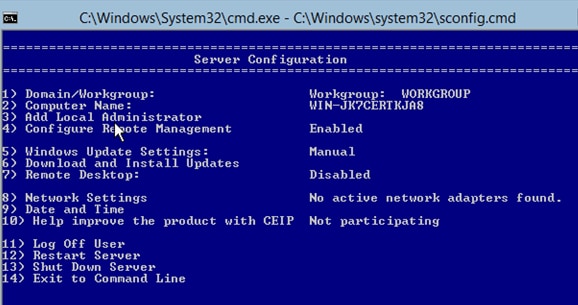
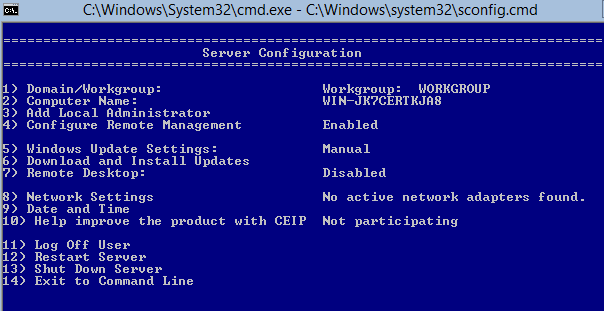
When you log into Windows Core, there are two windows ? a normal command prompt and the system configuration wizard.
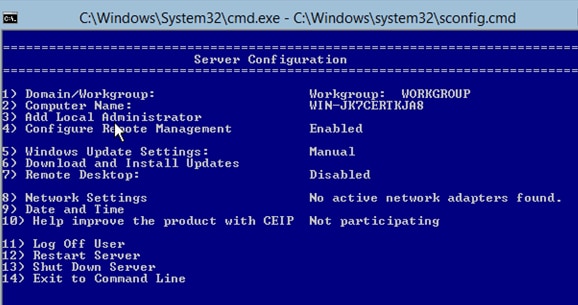
There are many options here that are used in order to perform basic installation/maintenance. The first step is to install the drivers for the Network Interface Controller (NIC) cards, which is covered in the next section.
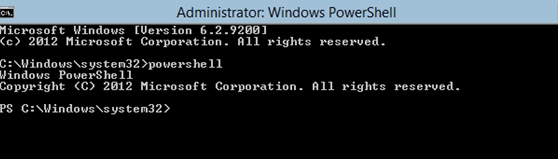
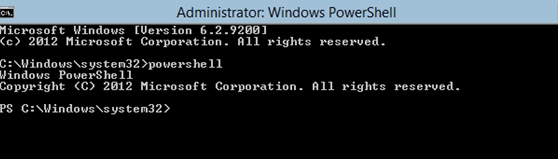
In order to get into PowerShell from the command prompt, type PowerShell.
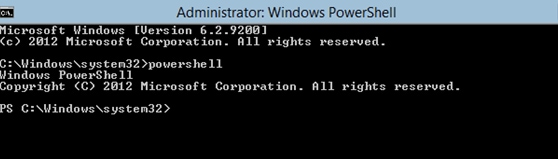
The PS before the command prompt indicates that you are in PowerShell rather than the normal CMD line.
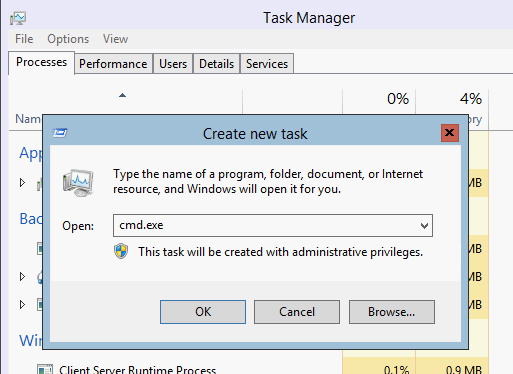
If you close your CLI Window accidentally, press ctrl+alt+del, and open the Task Manager in order to launch it again:
If you close the system configuration wizard window, type sconfig.cmd in order to open it again.
Install Drivers
Install the Ethernet Network Interface Controller (ENIC) drivers that are needed for network communication.
- Mount the Driver CD in the virtual media of the Keyboard/Video/Mouse (KVM) window.
- When you log into the console of the Windows host, you see the server configuration utility. Type 14 in order to get to a CLI prompt or use the other window that was opened.
- Enter the PowerShell command in order to get into PowerShell (before, you were simply in the Windows command prompt).
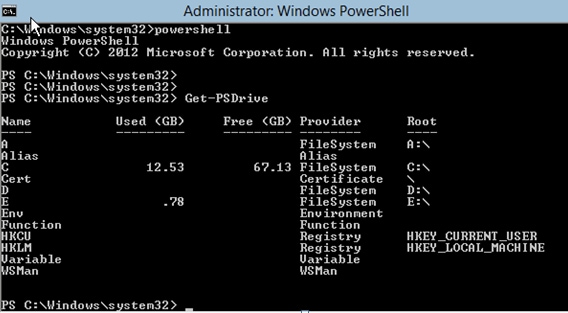
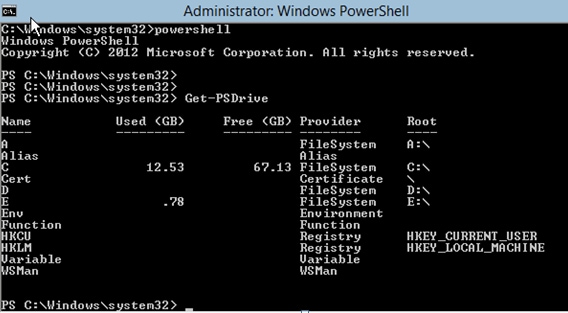
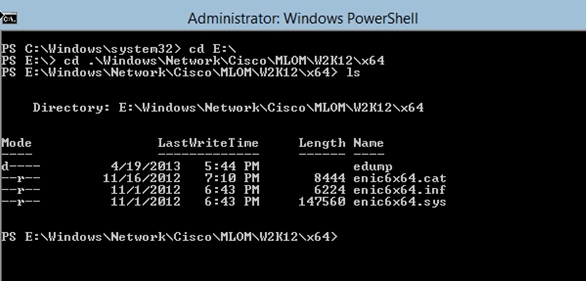
- Use the Get-PSDrive lightweight command (cmdlet) in order to list all available drives, which includes your CD drive. In this case, the CD drive is E:\.
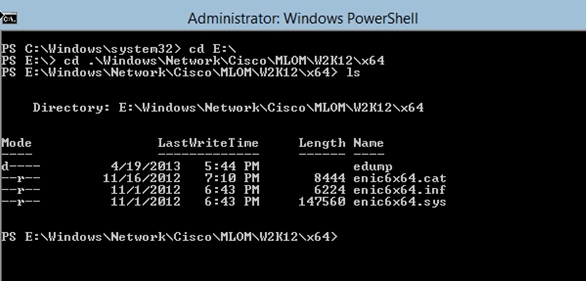
- Navigate to the driver folder you want to install.
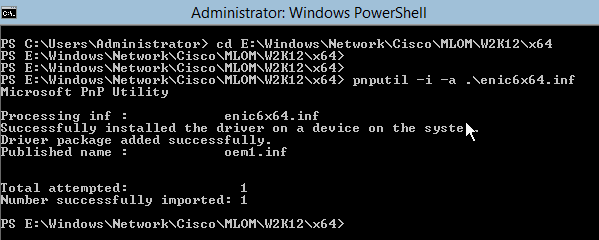
- Use the pnputil - i - a .\[driver].inf command in order to install the driver.
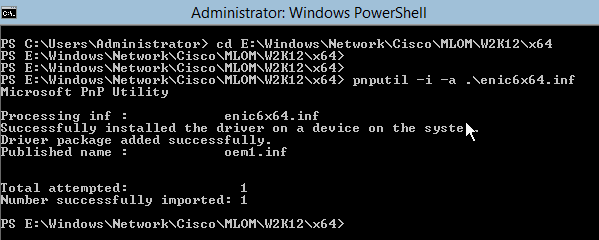
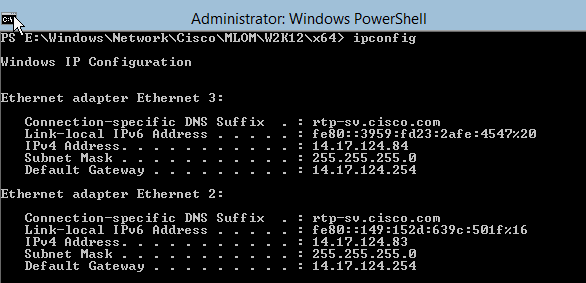
- Verify that the driver is installed. This command varies based on the driver; in the case of the ENIC, run the ipconfig command.
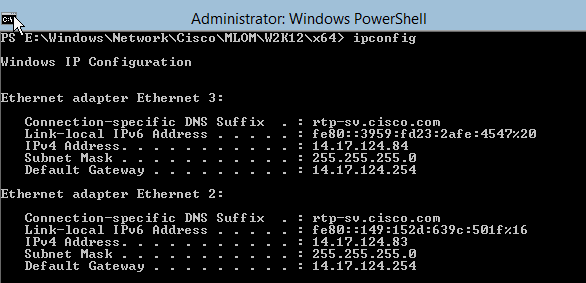
- If you use DHCP, the address should be ready. Otherwise, return to the server configuration wizard, and configure an IP address with the sconfig.cmd command.
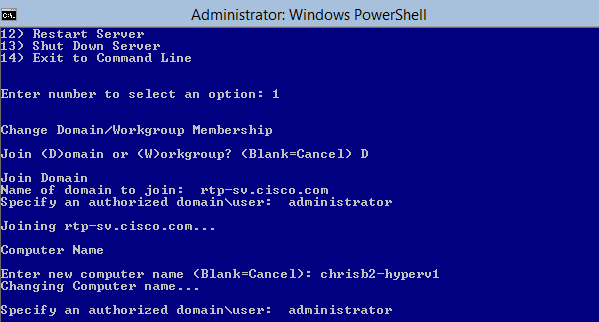
Add the Hyper-V Server to the Domain
Windows relies on a complex set of trust domains. In order to add your Hyper-V server to the SCVMM or to remotely manage your server, you must be a member of the same domain. There are other ways around this with the domain/workgroup trust, but they are outside the scope of this document.
- Enter the sconfig.cmd command in order to launch the server configuration wizard.
- Enter 1 in order to launch the domain wizard. This guides you through the process used in order to add the server to a domain.
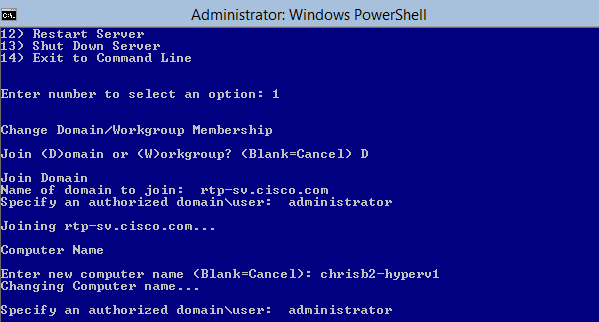
- Use your domain, and log in with the proper credentials.
- If a window does not appear that indicates that the settings have taken effect, reboot the computer with the shutdown - r command in order to have the new settings take effect.
- Add a DNS entry for your host with the DNS manager on the jumpserver.
Enable Remote Access
There are many ways in order to remotely access a server core. The best is the Microsoft Management Console (MMC).
MMC
- Run netsh advfirewall set allprofiles state off on your host.
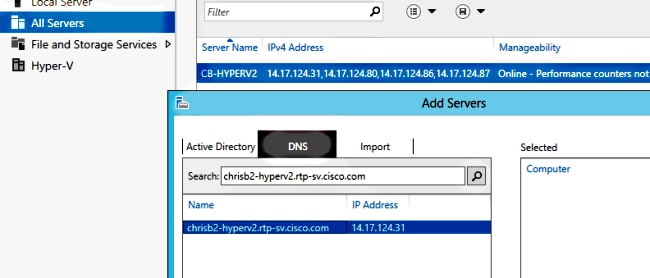
- In the Windows 2012 jumpserver, open Server Manager, and right-click All Servers.
- Search for your host, and add it to the server manager.
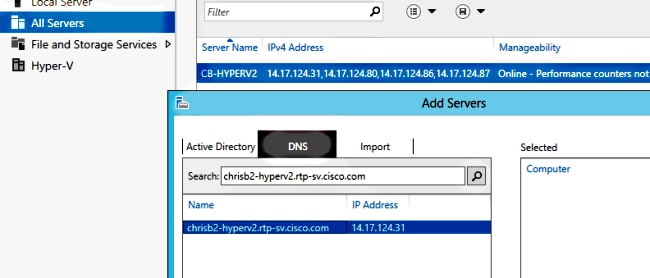
You can now use Server Manager like you were on a local machine.
Remote Desktop
Run the cscript C:\Windows\System32\Scregedit.wsf /ar 0 from the command prompt in order to enable remote desktop connections for administrators.
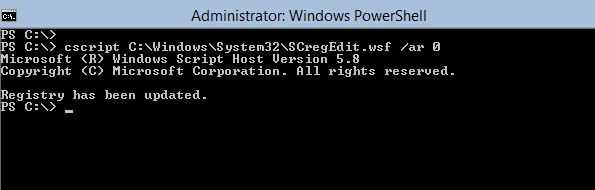
You are now able to Remote Desktop Protocol (RDP) with accounts that have Administrator access. You can also enable this from the configuration wizard with option 7.
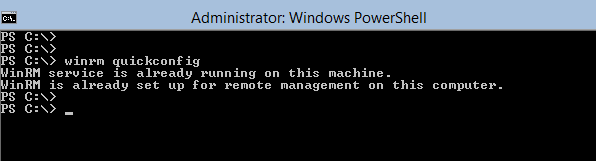
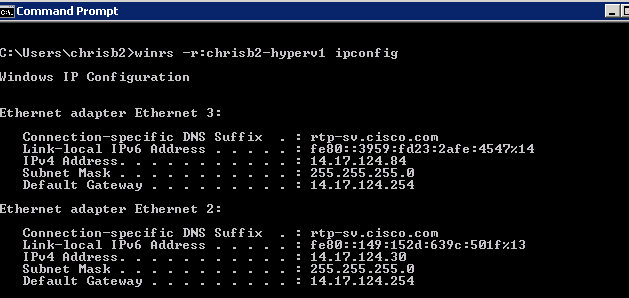
Windows Remote Shell
- Run WinRM quickconfig in order to enable remote command prompts.
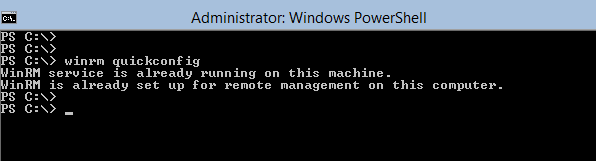
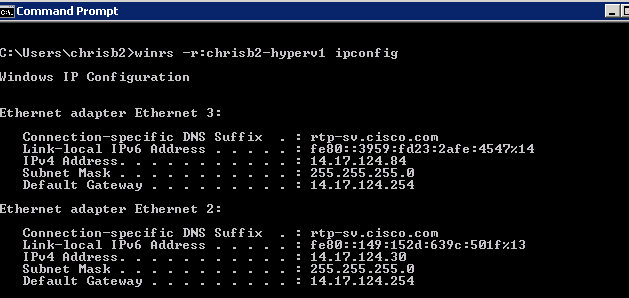
- From a machine on the same domain, run winrs - r:[serverName] [command] command.
Remote PowerShell
This is similar to the Remote Shell, but it gives you full PowerShell access, and allows you to connect to remote computers like Secure Shell (SSH).
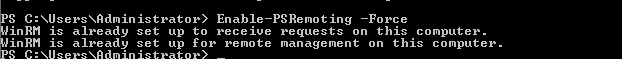
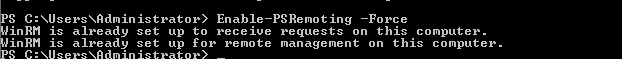
- On the remote host, run the Enable-PSRemoting - Force command.
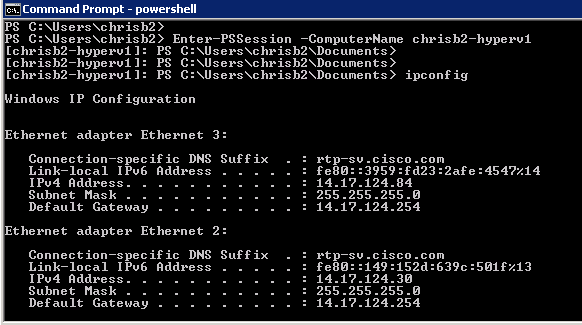
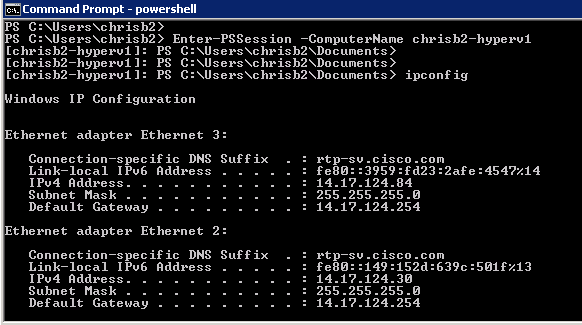
- On the remote machine run Enter-PSSession - ComputerName [computer_name].
Install Additional Roles
Once the server is added to the MMC of the jumpserver, you can run the add/remove roles and features wizard from the jumpserver, and add roles to the remote server like any other server. Do this now in order to install Multipath I/O (MPIO) if it is needed as well as the failover clustering features that are needed for Hyper-V clusters.
- Open the server configuration utility.
- Navigate to Manage > Add Roles and Features.
- Choose your Hyper-V server.
- Install MPIO, if you use Fibre Channel (FC), and Failover Clustering.
- Repeat for the second host.
Additional Configuration
- Use the mpiocpl command from the command prompt in order to launch the MPIO wizard once the feature is installed.
- In order to configure disks from the CLI, use these commands:
- Get-disk in order to list available disks
- Set-disk - number X - IsOffline $false in order to bring the disk online
- Initialize-Disk X in order to initialize the disk
- New-Partition [Disk_Number] - UseMaximumSize - MBRType - AssignDriveLetter in order to create the partition
- Format-Volume - DriveLetter [DriveLetter] in order to format the drive
- Launch the Clustering wizard from the jumpserver, and add your two hosts to a cluster.
Add the Hyper-V Host to SCVMM
Now you have a basic Windows installation - drivers are installed, IPs are configured, you are on the domain, and you can remotely manage the box. It is time to add the host to SCVMM, which is the equivalent of vCenter. If you have a host that runs Hyper-V manager, you can point that to your host in order to manage it. However, this is basic management, which is similar to logging into the ESXi host directly rather than vCenter.
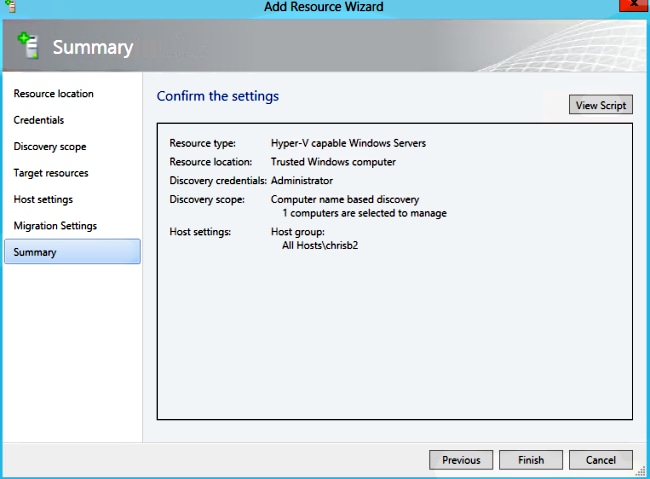
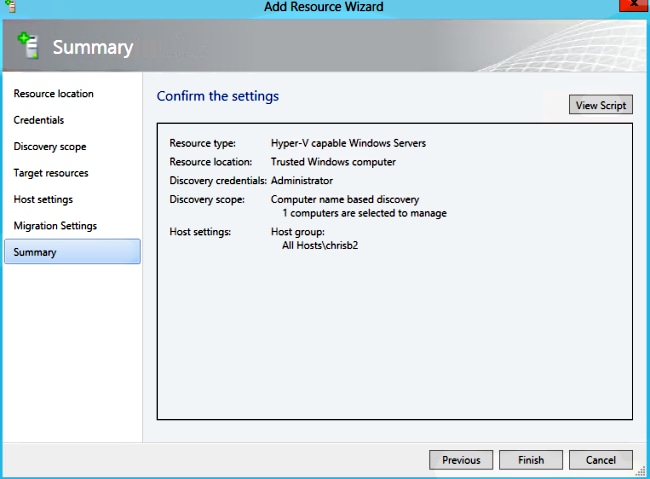
This section describes how to add the newly-provisioned Hyper-V host to SCVMM.
- RDP to your jumpserver, and log in with your domain account.
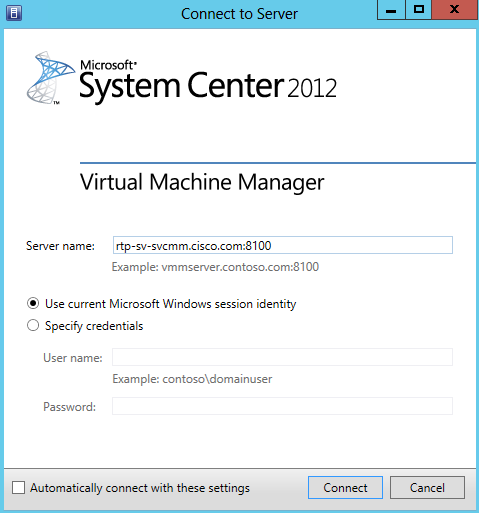
- Launch the Virtual Machine Manager Console from the desktop. If you do not have this installed, you can install it from the SCVMM ISO.
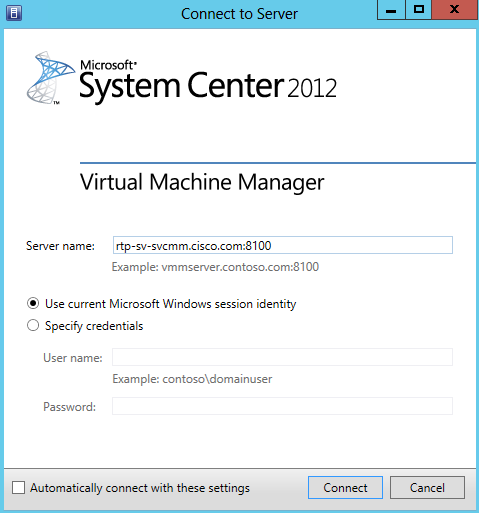
- Point the console towards your SCVMM server, and click the Use current Microsoft Windows Session identity radio button.
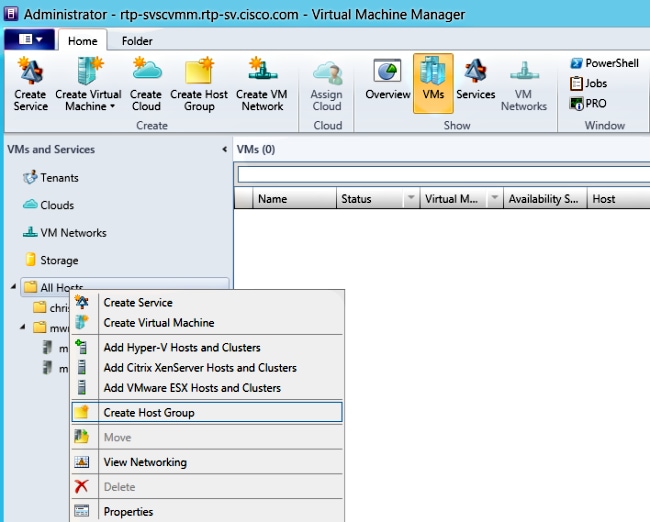
- You are now in SCVMM. Right-click the All Hosts folder, and choose Create Host Group. Name this with a descriptive title.
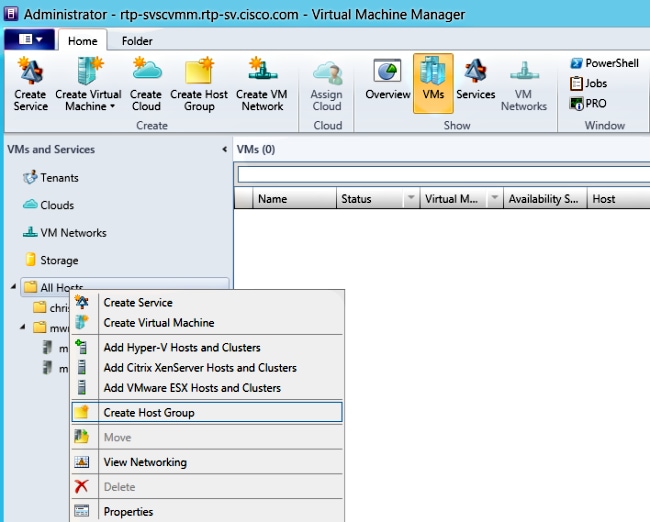
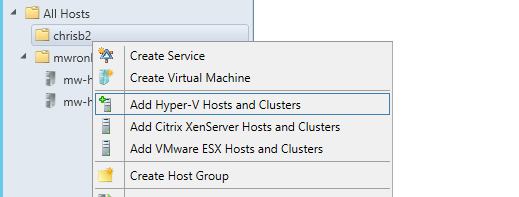
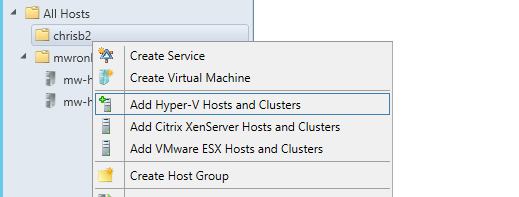
- Right-click the newly-created host group, and choose Add Hyper-V Hosts and Clusters.
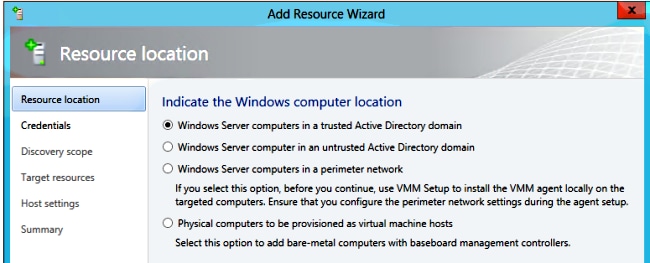
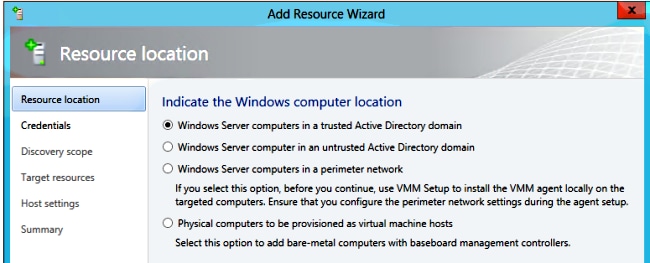
- Click the Windows Server computers in a trusted Active Directory domain radio button.
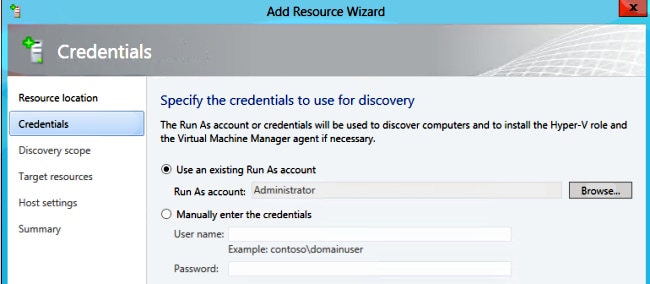
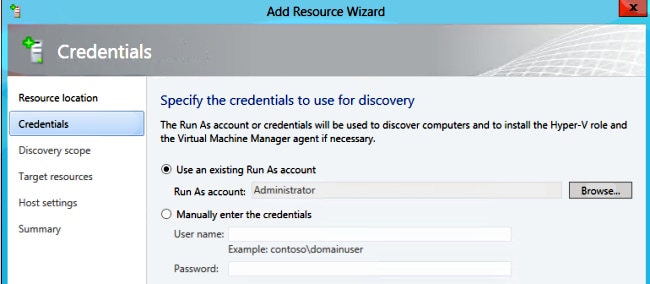
- Click the Use an existing Run As account radio button. This is the account that the wizard uses in order to log in to the hosts you add.
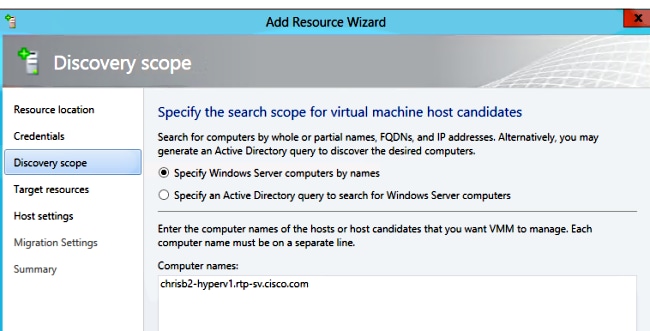
- Enter the DNS names of the servers you need to add.
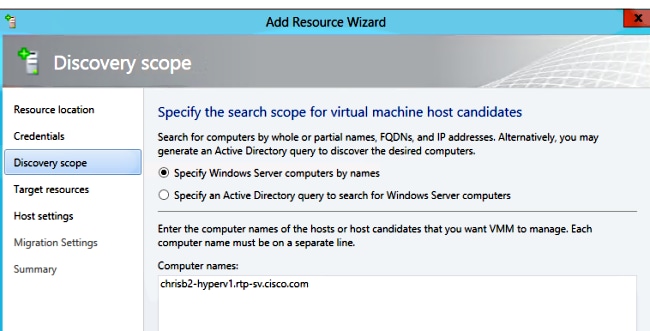
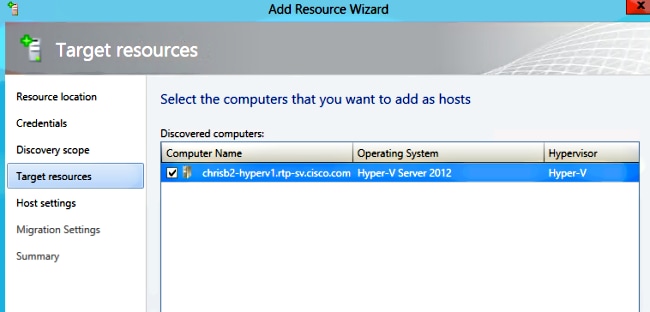
- On the next screen, choose the discovered servers that must be added. If you cannot see the servers on this screen, then go back and modify your search parameters.
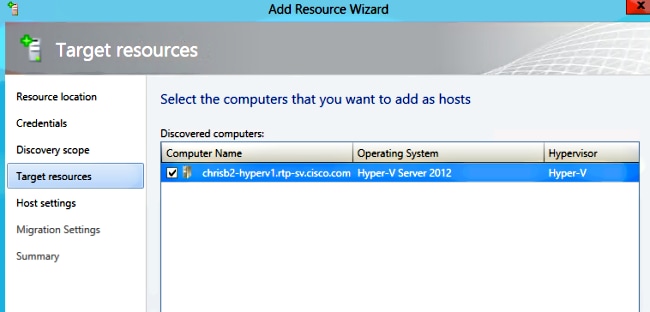
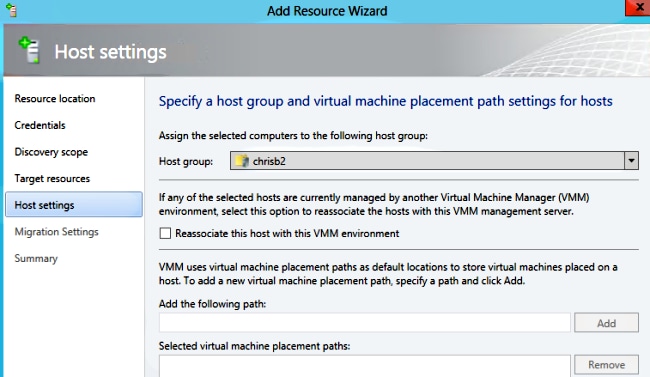
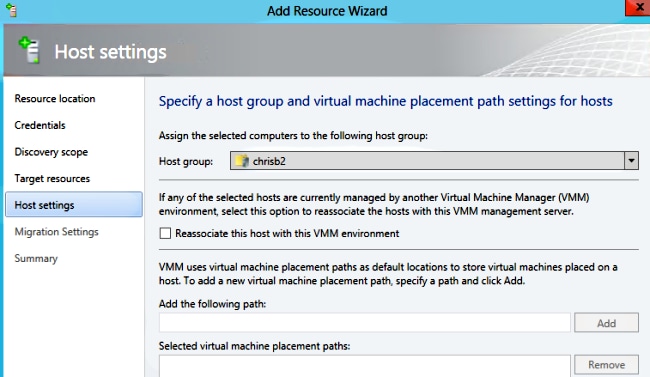
- Modify the settings as needed. For example, you can change the default path.
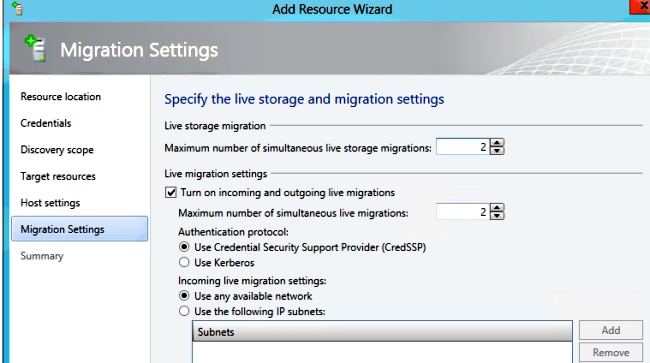
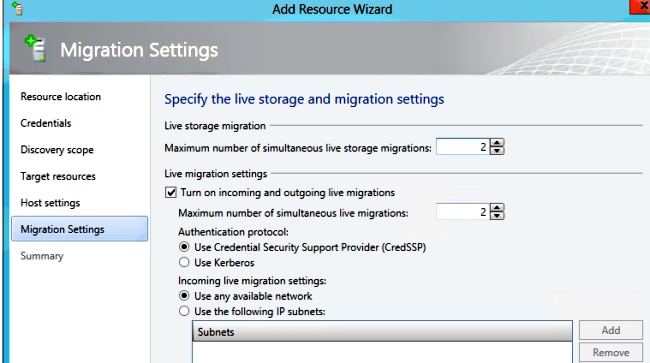
- Enable live migrations if desired. You can specifiy the network to use as well.
- Verify and accept the changes. Ensure that you fix any errors.
If you have trouble with your connection (for example, if it errors-out), complete these steps:
- Disable Windows firewall with the PowerShell netsh advfirewall set allprofiles state off command.
- Make sure you use the correct credentials and that the host is on the domain.
- Review the Windows error logs because they are often helpful in this case.
Nexus 1000v on Hyper-V
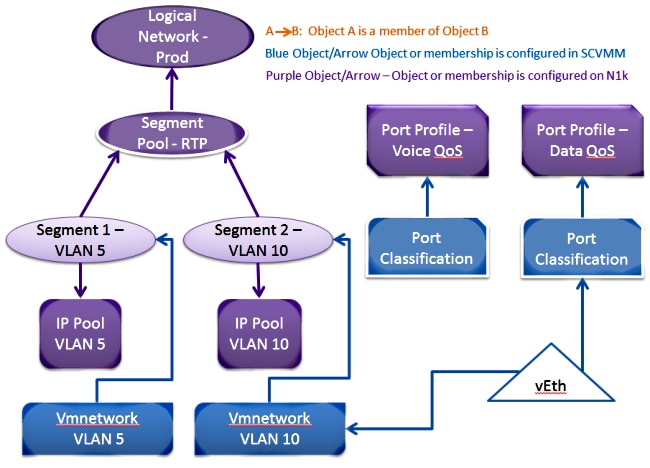
The Nexus 1000v on Hyper-V is configured very differently than the Nexus 1000v on VMware by default. This is because the Nexus 1000v on Hyper-V relies heavily on the network segmentation features due to the networking architecture of Hyper-V. Here is a quick overview of the different terminologies and how they interact:
- Logical Network - A logical network is a general bucket that contains a certain network. For example, DMZ would be a logical network and Production would be another.
- Segment Pool - A collection of segments that belongs to a logical network. For example, they might be for different sites, such as one pool for RTP, and one pool for SJ.
- Segment - This is where the access capabilities of a network are defined. This is where you assign VLANs.
- Port-Profiles - A collection of policies, not connectivity. Quality of Service (QoS), Access Control List (ACL) and others belong here.
- IP Pool - This gets assigned to a segment. In most cases it does not matter. But, when doing orchestration, SCVMM can automatically assign addresses from this pool.
- Ethernet - This is an uplink from the host. Each set of uplinks allows a certain segment pool.
- vEthernet - This is the interface of a VM. It inherits a port-profile for its policies and a segment for its VLAN.
- VMnetwork - This is the segment combined with the IP pool on the SCVMM side.
- Port-Classification - This refers to the port-profile policies in SCVMM.
Here is a diagram that explains the inheritance chain:
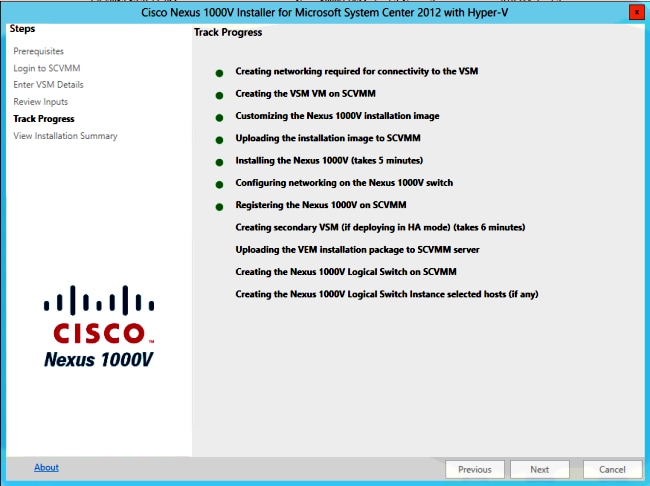
Use the Installer Application in Order to Install the Virtual Supervisor Modules (VSMs)
Use this method for a fresh install - the installer application only shows hosts that do not have a virtual switch. This installs the VSMs and provides some basic configuration. You should not use this to install because you understand the product better if you install it manually. However, it is included here for reference.
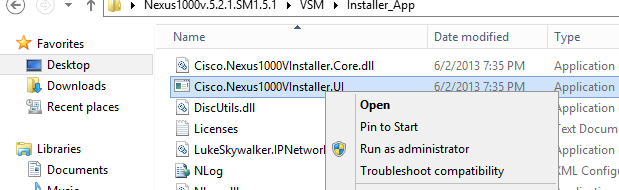
- Log in to the jumpserver with your domain credentials.
- Open a Windows Explorer window and navigate to [n1k bundle]\VSM\Installer_App.
- Right-click Cisco.Nexus1000VInstaller.UI.exe, and choose Run as administrator.
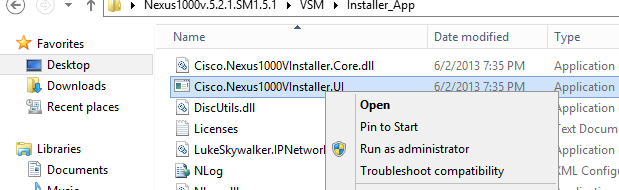
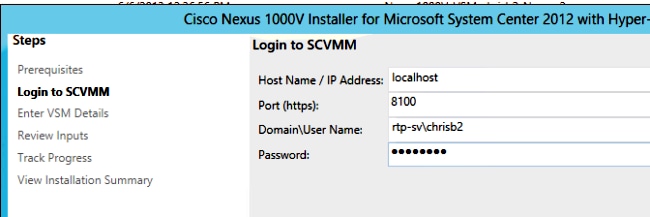
- Review the requirements. Click Next.
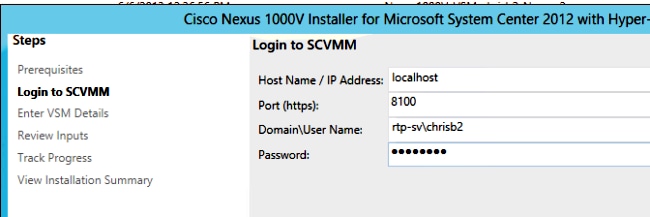
- Enter the SCVMM server details. Make sure you use an administrator account.
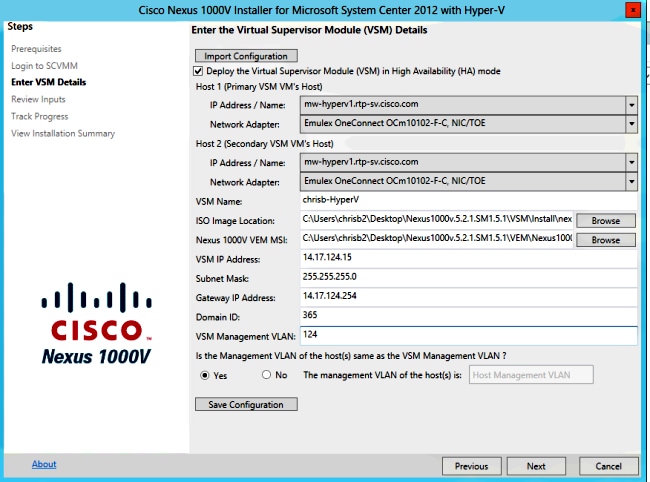
- On the next page, you are asked for the basic Nexus 1000v configuration. Fill this out based on your needs. The VSM ISO is in the VSM folder, and the VEM .msi is in the VEM folder. There is currently a bug, Cisco bug ID CSCuh36072, that prevents this wizard from seeing hosts with a virtual switch (vSwitch) already defined. The Hyper-V server comes with a vSwitch created already. Because of this bug, you need to delete the vSwitch. In order to delete it, right-click host, go to properties and then virtual switches.
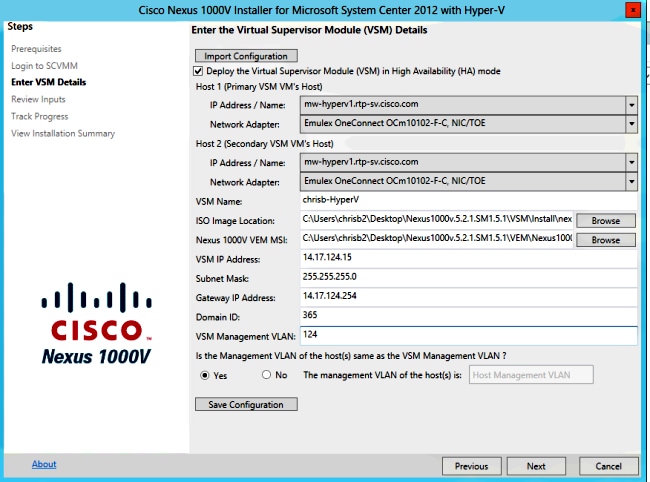
- Verify the settings, and click Next in order to begin the installation. The installation takes about ten to twenty minutes.
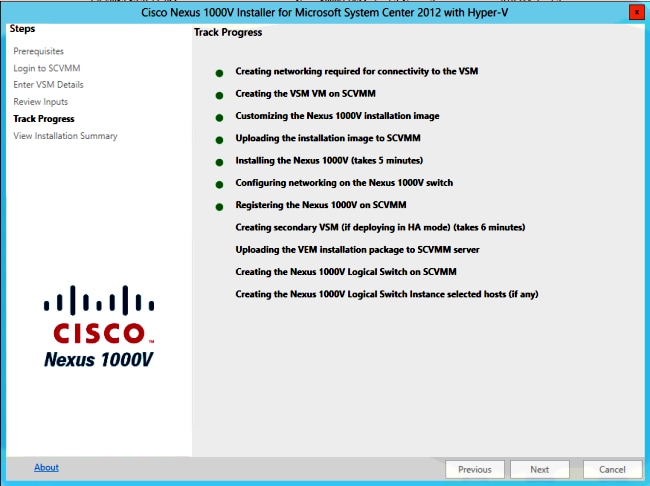
After this wizard is complete, you are able to log into your VSM. Admin/Admin is the default install.
Manually Install the Nexus 1000v
This section describes how to manually install the Nexus 1000v Series Switch, which is useful in a couple of cases:
- Integration with a system that already exists. The manual installation method is far more granular and allows you to control exactly how it integrates.
- Deeper knowledge of the product. This method allows you to better understand how everything integrates, which makes it easier to troubleshoot and expand.
- Problems with the installer. If you encounter any issues with the installer, you can use the manual method.
Install the VSMs Manually
Use this method if you need to install VSMs into an environment that already exists. This method allows you to use the infrastructure that already exists instead of building your own.
Part 1 - SCVMM Setup
This procedure only needs to be done once for each SCVMM server.
- Install the provider MSI on the SCVMM server.
- Import the VSM templates.
- On the SVCMM server, open PowerShell.
- Run the Register-Nexus1000vVsmTemplate.ps1 script.
- Copy the Virtual Ethernet Module (VEM) to the SVCMM repository ALLUSERSPROFILE%\Switch Extension Drivers.
- Create a logical network (Fabric > Logical Networks) and associate it with a standard switch (right-click the host, Properties, Virtual Switches in order to create the switch, and Hardware in order to assign the logical network to it). This allows you to put VMs on this network.
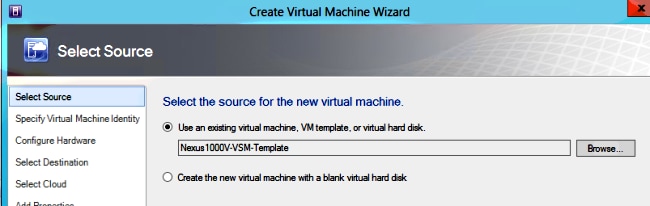
Part 2 - VSM Deployment
- Go to Library > Library Servers and upload the VSM .iso to the library server.
- Right-click Infra1, and choose New Virtual Machine.
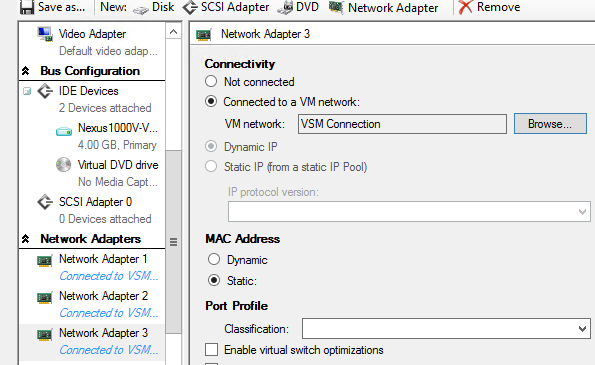
- Choose the Nexus1000v-VSM-Template. This was registered when the PowerShell script ran in part 1.
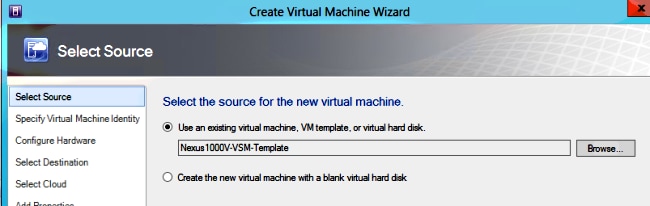
- Name the VSM.
- Connect the Network Adapters to the network created in Part 1.
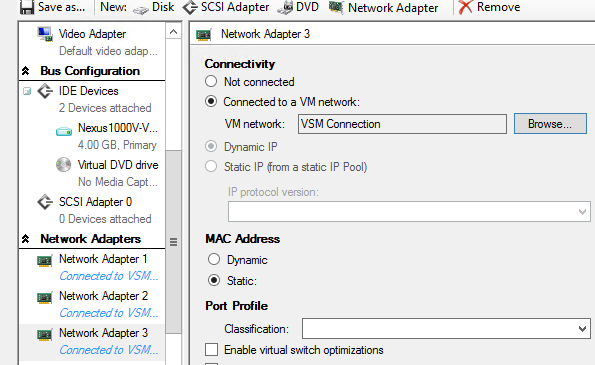
- Mount the CD in the CD drive.
- Scroll down and enable High Availability (HA) under Availability (this is only needed if you install the VSMs to a failover cluster).
- Place the VSM on the Infrastructure hosts.
- Once the VM is deployed, launch the KVM, and run through the initial configuration wizard.
Part 3 - VSM Basic Configuration
- Enable network-segmentation-manager and http-server
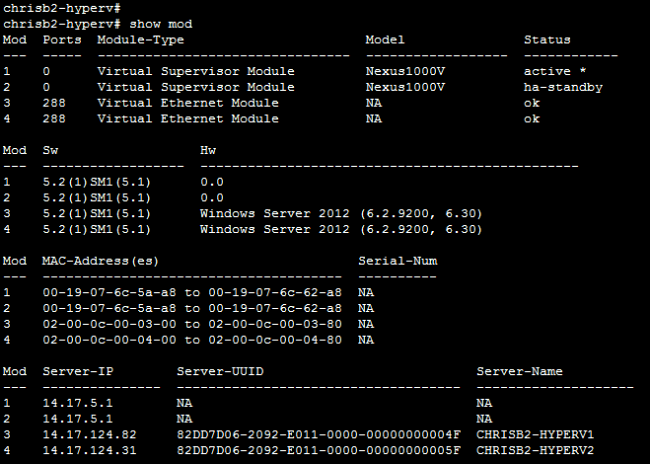
chrisb2-hyperv#
chrisb2-hyperv# configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
chrisb2-hyperv(config)# feature network-segmentation-manager
chrisb2-hyperv(config)# feature http-server
chrisb2-hyperv(config)# - Create an IP pool for your VLAN. These are the IPs that you assign to your VMs. They need to be defined, but they are only used if SCVMM provides automation.
nsm ip pool template VLAN124
ip address 14.17.124.80 14.17.124.250
network 14.17.124.0 255.255.255.0
default-router 14.17.124.254 - Create a logical network. You only need one logical network unless you have something like a DMZ.
nsm logical network chrisb2-CALO
- Create a network segment pool. Make it a member of the logical network.
nsm network segment pool chrisb2-RTP
member-of logical network chrisb2-CALO - Create multiple segments, one for each access VLAN.
nsm network segment chrisb2-124
member-of network segment pool chrisb2-RTP
switchport access vlan 124
ip pool import template ip_pool_124
publish network segment
switchport mode access - Create a port-profile for the VMs. There is no need to access a VLAN here. Remember that the port-profile is simply a collection of policies.
port-profile type vethernet defaultAccess
no shutdown
state enabled
publish port-profile - Create a Network Segmentation Manager (NSM) uplink. The allow network segment pool command tells SVCMM that these segments are allowed out this uplink. This is needed for the host in order to see your segments.
nsm network uplink UPLINK
switchport mode trunk
publish network uplink
allow network segment pool chrisb2-RTP - Modify the created port-profile with any needed policies, such as port-channels.
port-profile type Ethernet UPLINK
channel-group auto mode on mac-pinning
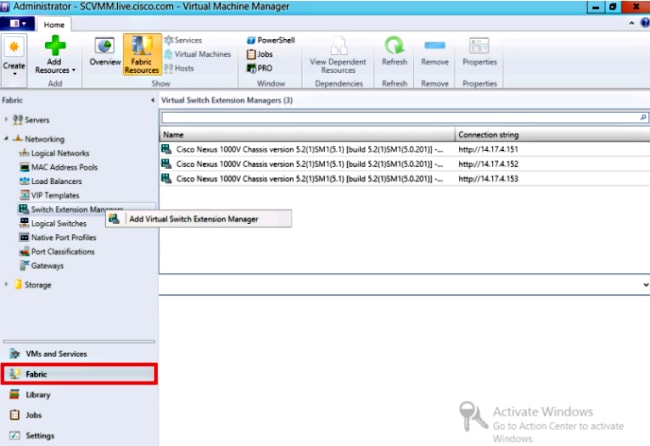
Part 4 - SVCMM Basic Configuration
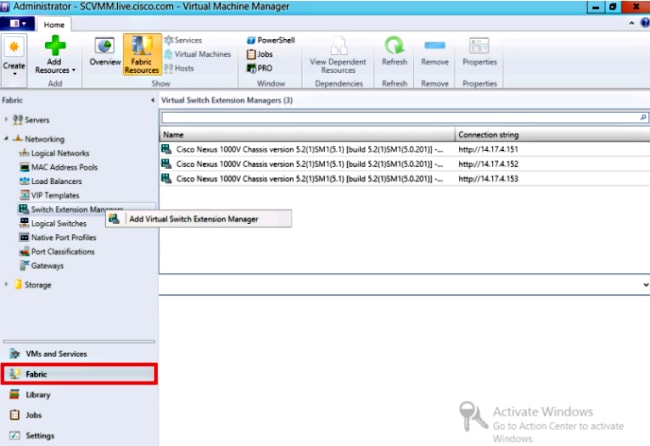
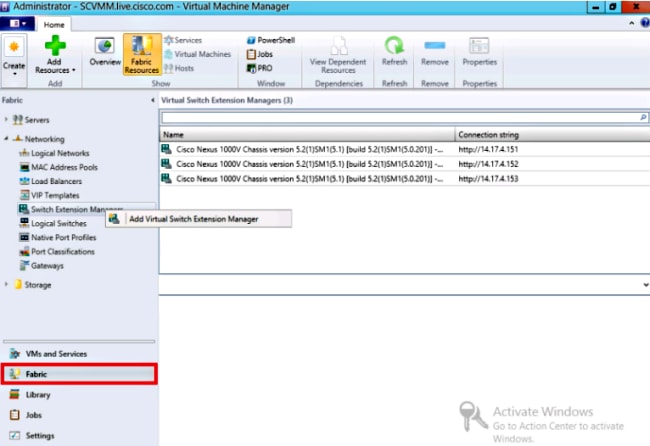
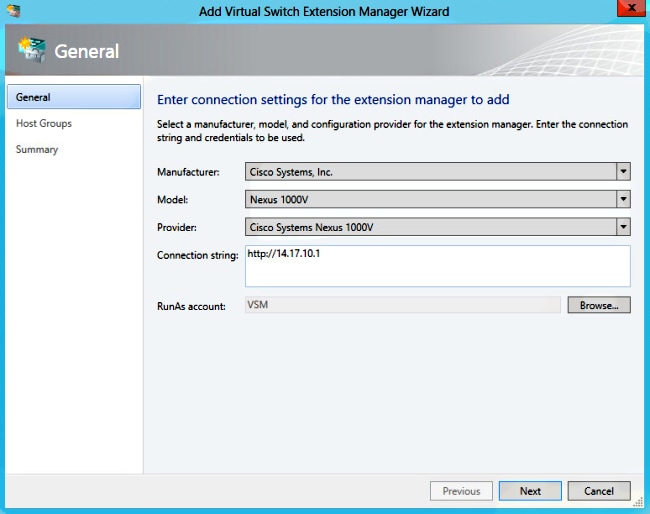
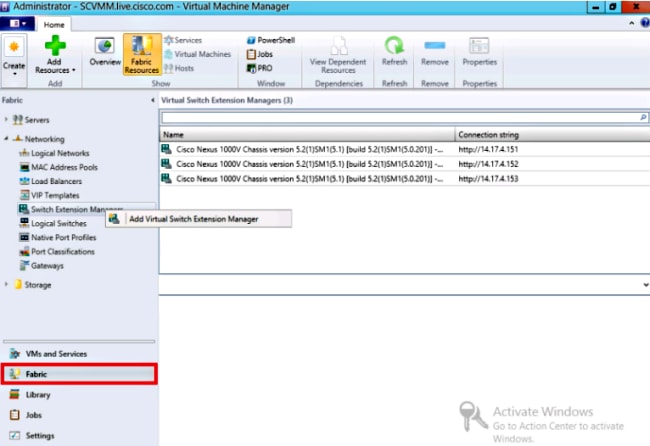
- Navigate to Fabric, and expand Networking. Right-click Switch Extension Manager, and click on Add Virtual Switch Extension Manager.
- Enter the Connection settings. The Connection String address is http://your_VSM_IP_address.
- Click Browse, and create a Run As account with credentials to log in to your Nexus 1000v.
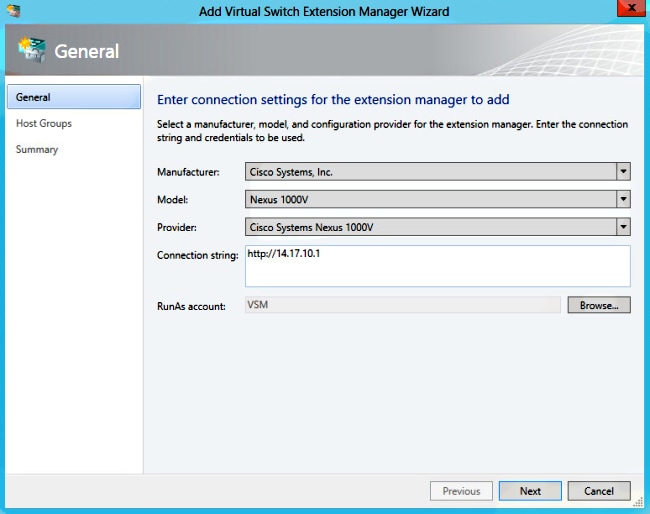
- Click Next.
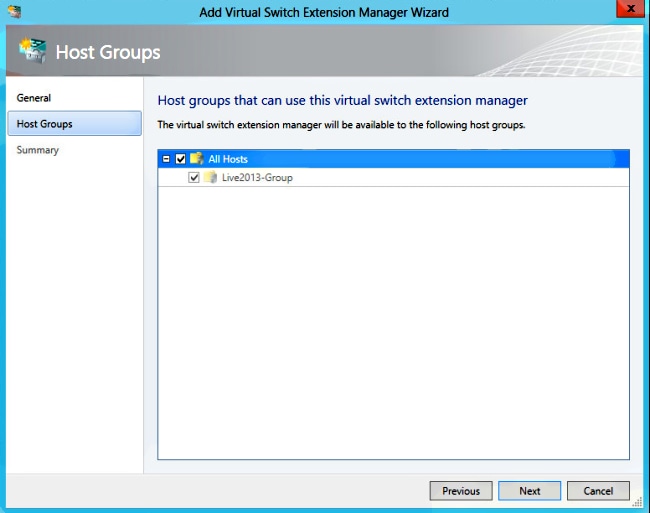
- In the Host Groups panel, select all the host groups that can use the virtual switch extension manager, and click Next.
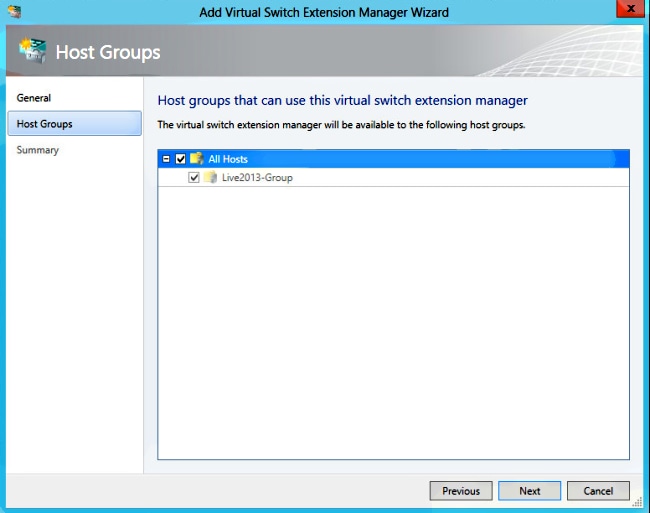
- In the Summary panel, confirm the settings, and click Finish. The switch extension should be created now.
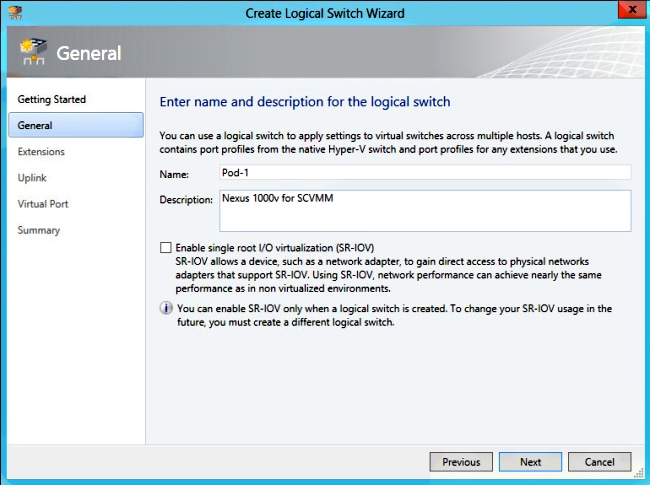
Part 5 - Create the Logical Switch
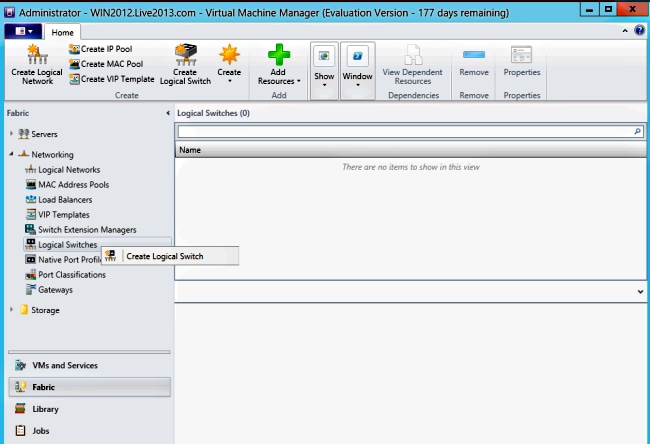
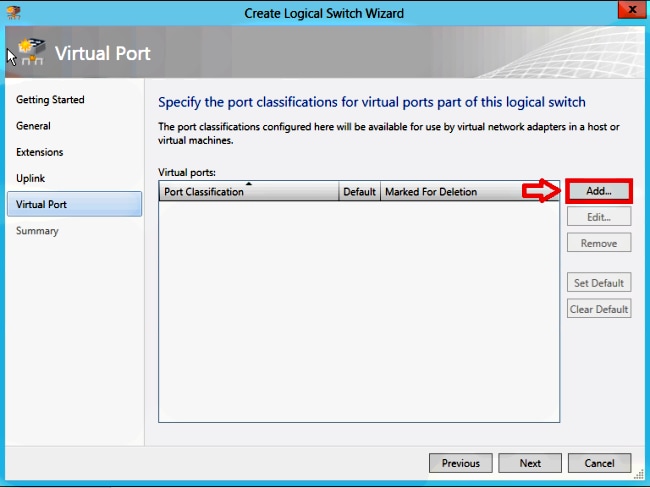
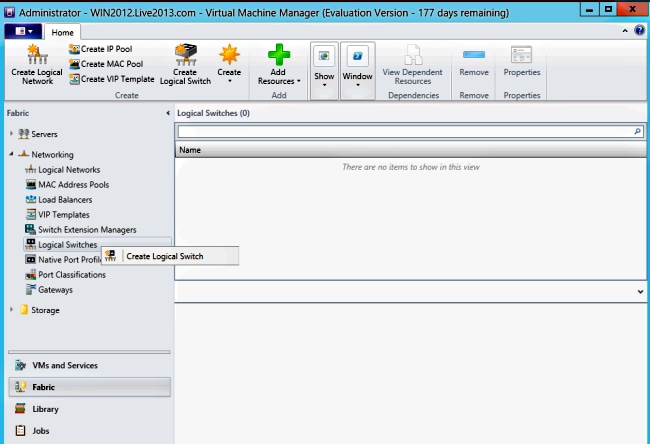
- In the SCVMM user interface, click Fabric, then Logical Switches under Networking in the left-navigation panel. Right-click Logical Switches and Create Logical Switch.
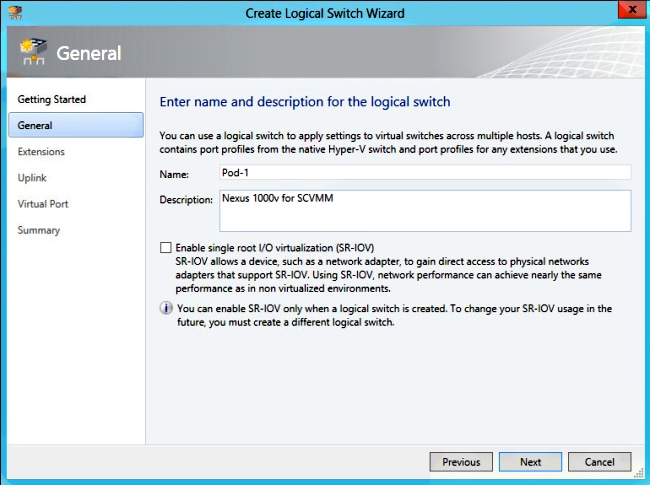
- Click Next on the Getting Started page. Review the instructions, and click Next.
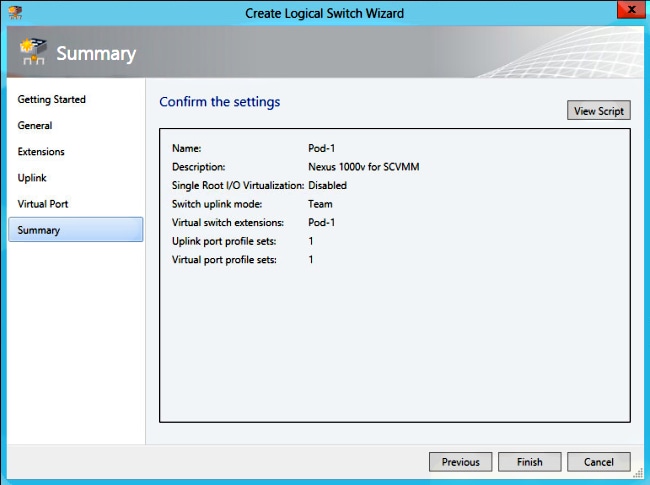
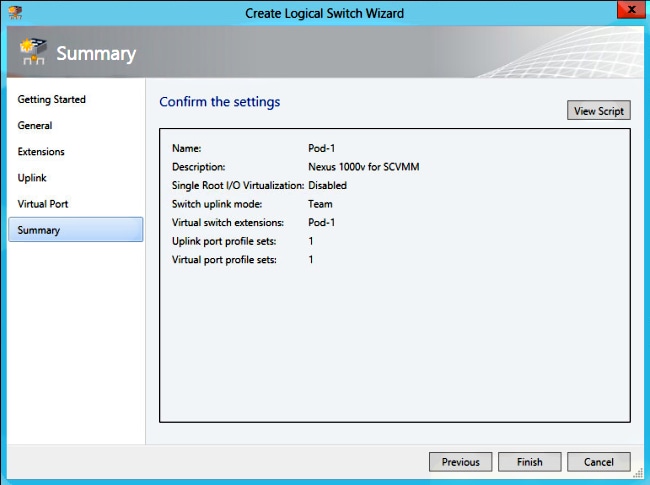
- Enter a name and a description for the logical switch.
- In the Extensions panel, the virtual switch extensions are listed. Select the VSM extension you created, and click Next.
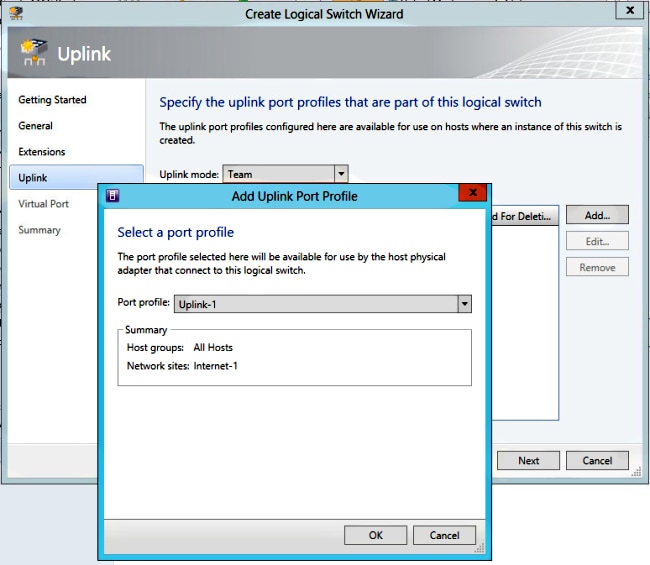
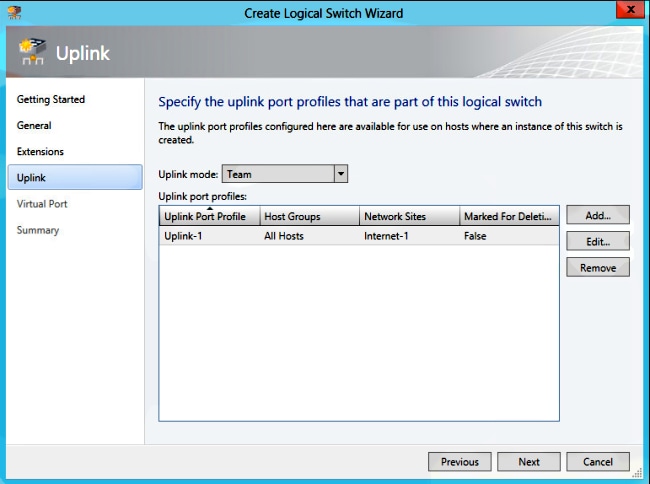
- In the Uplink panel, specify the uplink port-profiles that are part of this logical switch. The uplink port-profiles are available for use on the hosts where an instance of the logical switch is created. Set the Uplink mode to Team.
- In the Uplink port-profiles field, click Add. The Add Uplink Port Profile window opens.
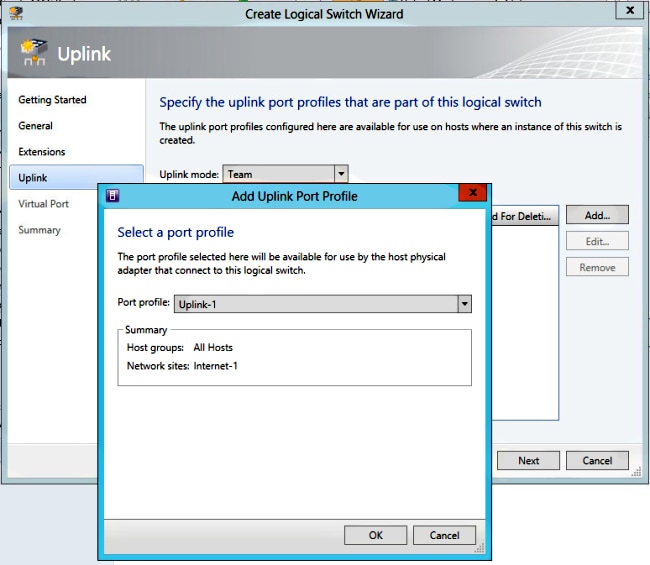
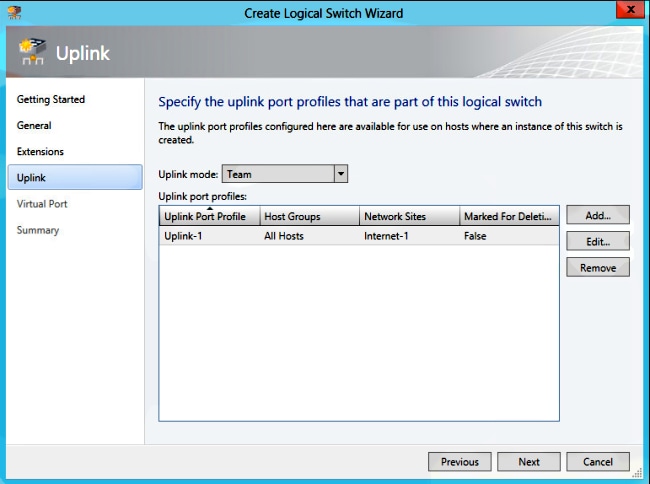
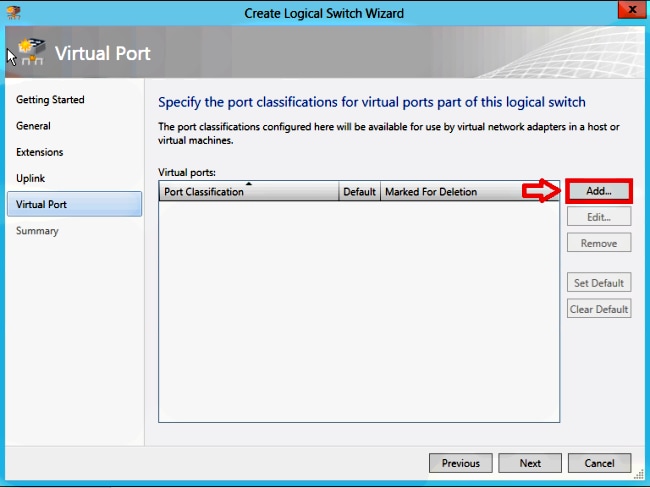
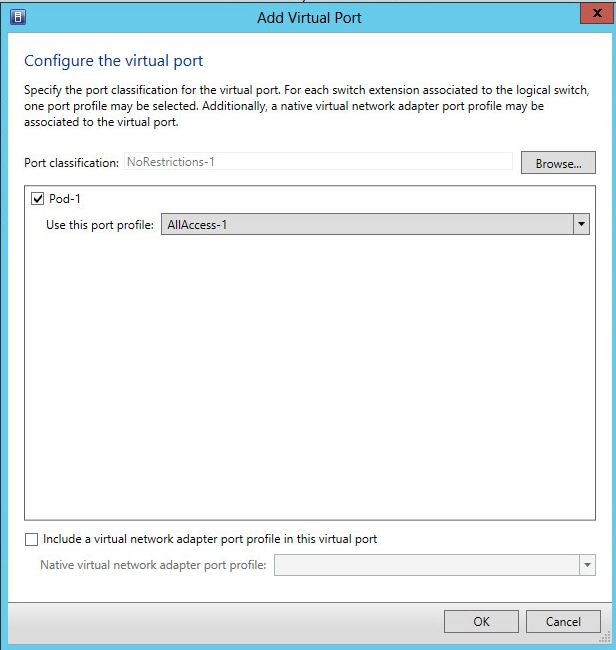
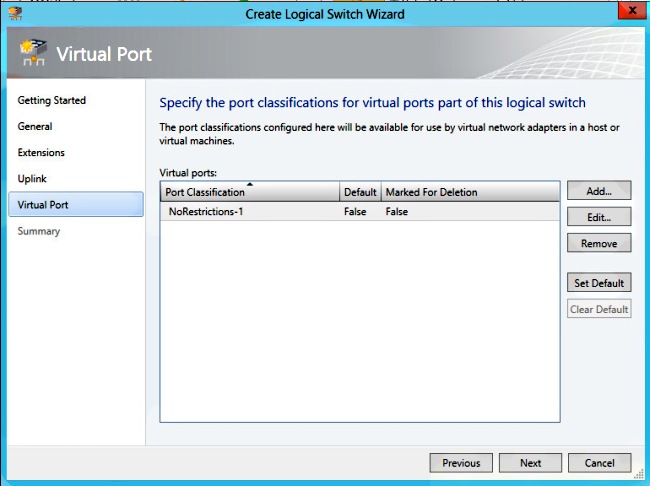
- Click Next. On the next screen, choose Add in order to start the classification wizard.
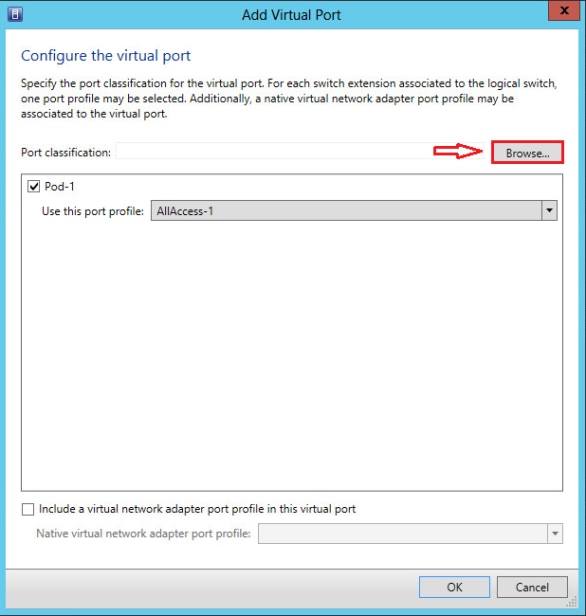
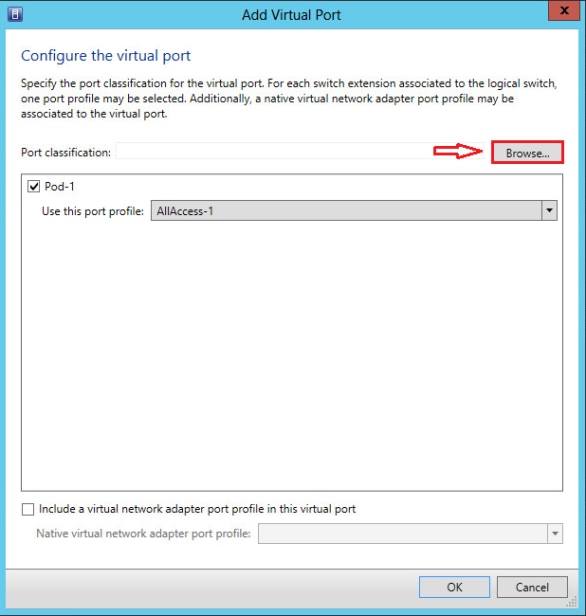
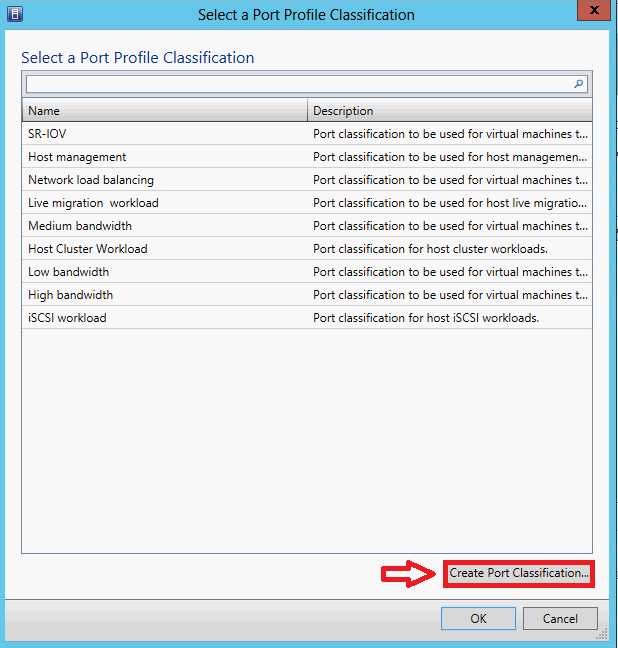
- Choose your VSM and the port-profile you created. Click browse in order to create a port classification. (A port classification is a collection of policies to apply to an interface - remember that this is what the port-profiles define!)
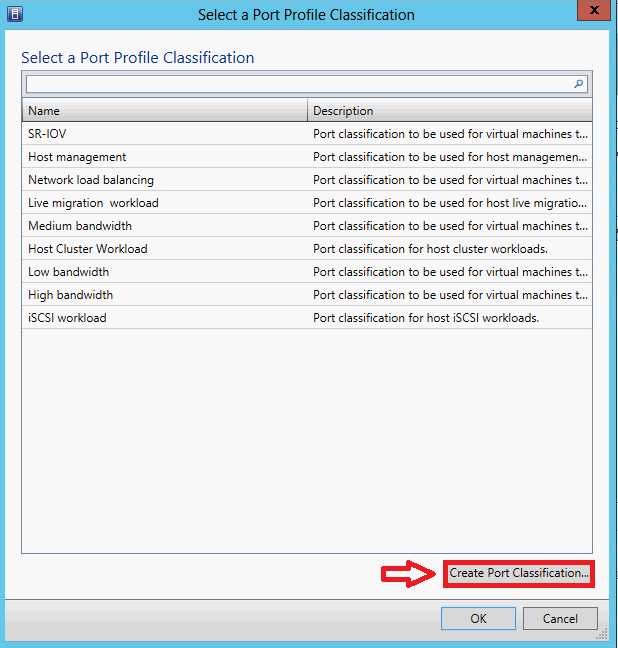
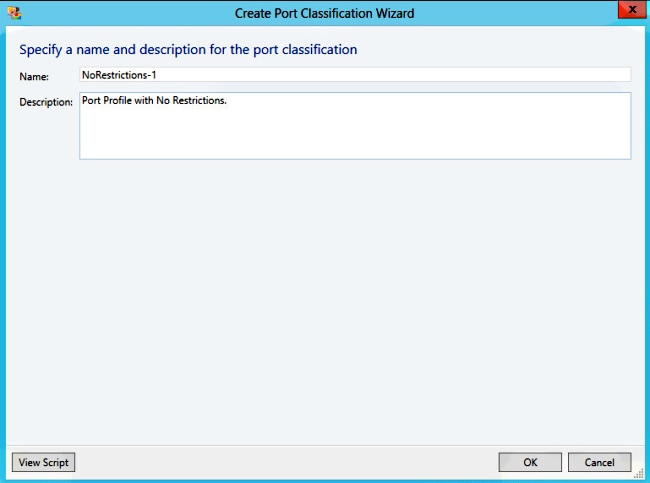
- Specify a name and a description for the port classification.
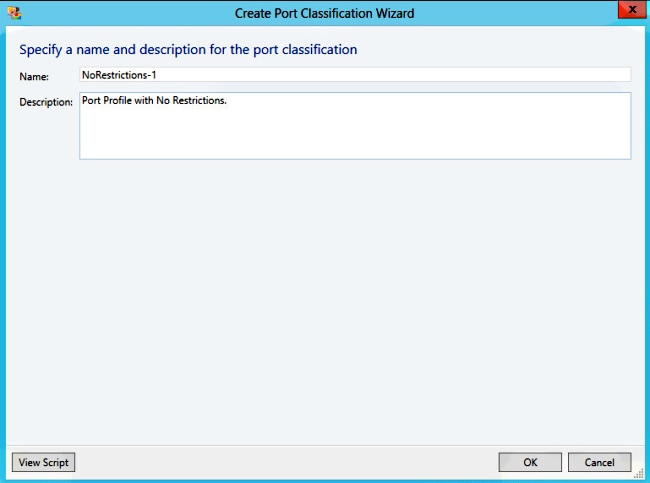
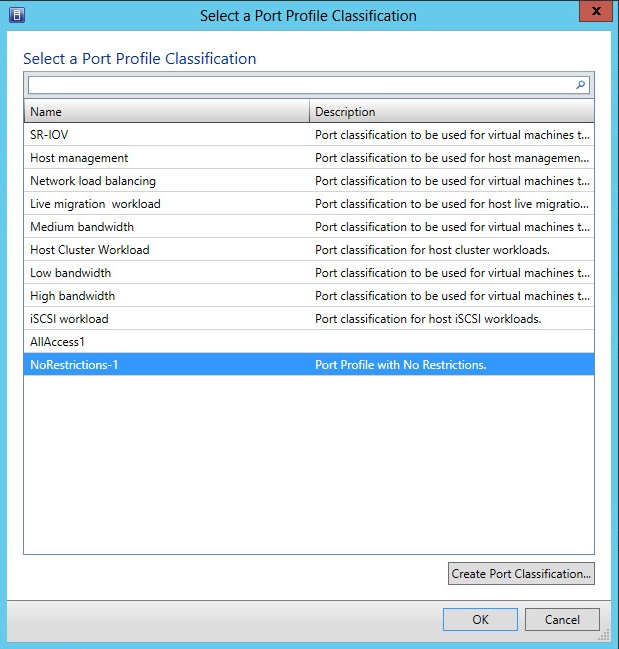
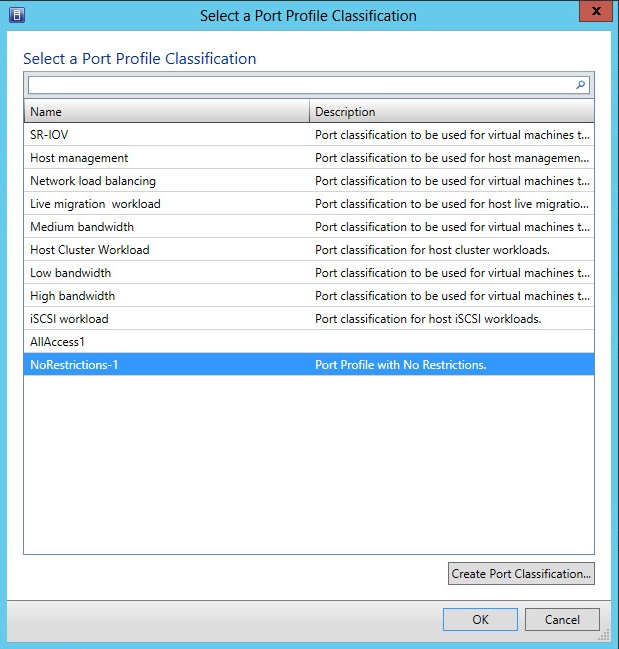
- Choose the port profile classification you just created, and click OK.
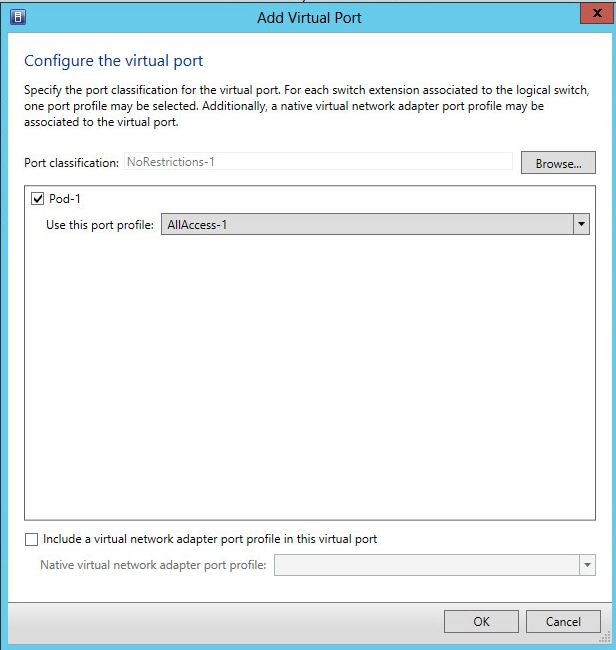
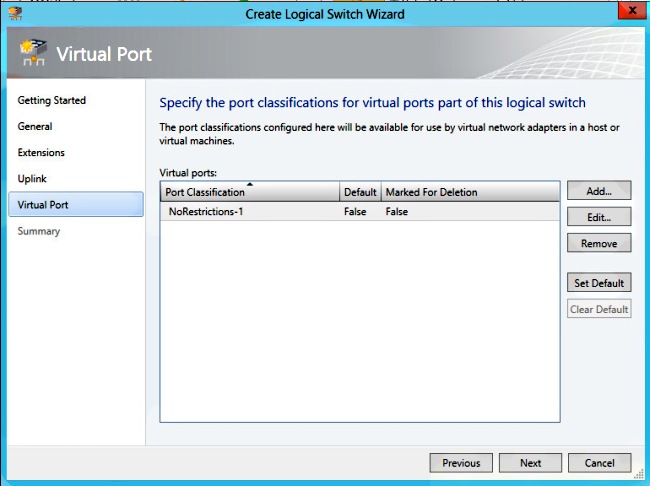
- Click OK in order to finish adding the Virtual Port. Click Next in order to close the Create Logical Switch Wizard window.
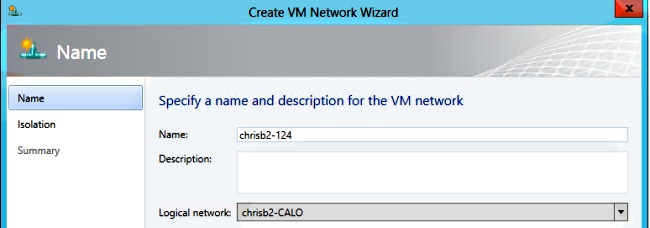
Part 6 - Create VMNetworks Based on the Segments
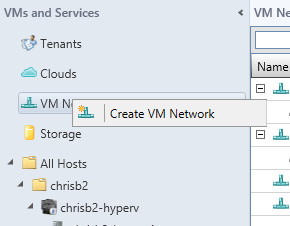
- Go to VMs and Services, right-click VM Networks, and choose Create VM Network.
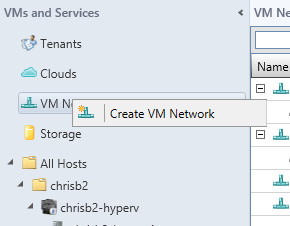
- Give it a descriptive name, select your logical network, and click Next.
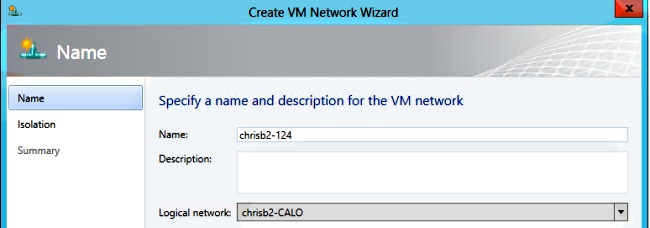
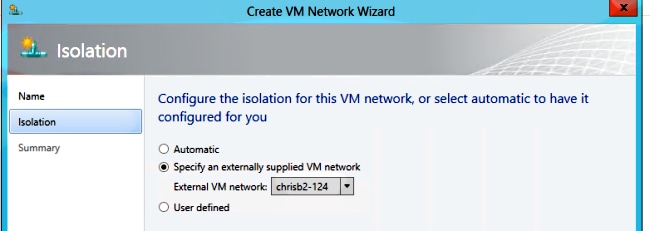
- For Isolation, choose Externally supplied VM network, and choose your network segment.
- Finish the wizard. Now you are able to deploy VMs on this VLAN.
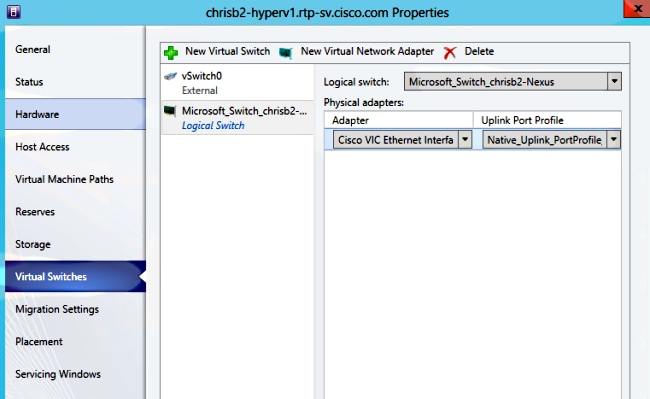
Add Host to DVS
When you add the host to the Logical Switch, the VEM is automatically installed.
- Go to Fabric > All Hosts.
- Right-click the second host, and choose Properties.
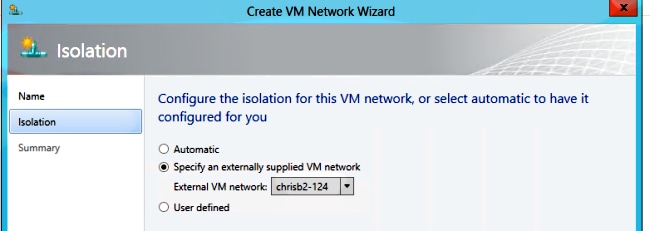
- Click Virtual Switches.
- Choose New Virtual Switch > New Logical Switch.
- Attach a NIC to the Nexus 1000v Logical Switch.
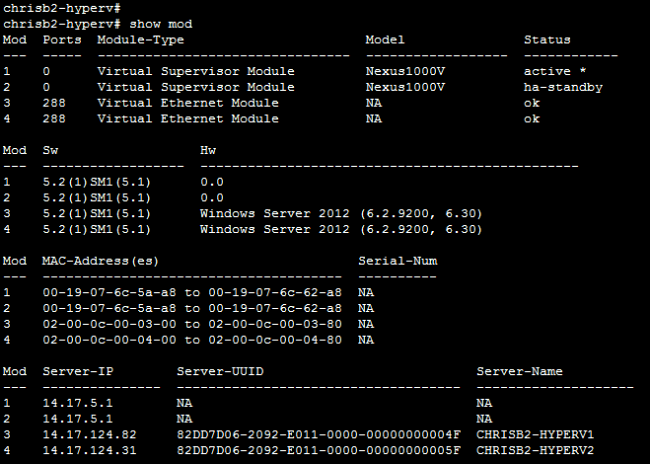
- Verify that the modules appear under show module on the VSM.
- Attach a VM to your created classification and segment, and then verify connectivity.
Manually Install the VEM
If SCVMM did not install the VEM, you can use this command in order to install the VEM:
msiexec.exe /i [Path_to_N1k_bundle]\VEM\Nexus1000v-VEM-5.2.1.SM1.5.1.0.msi
Verify
There is currently no verification procedure available for this configuration.
Troubleshoot
There is currently no specific troubleshooting information available for this configuration.
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
18-Oct-2013 |
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback