LAN-to-LAN VPN Tunnel Between Two PIXes using PDM Configuration Example
Available Languages
Contents
Introduction
This document describes the procedure to configure VPN tunnels between two PIX Firewalls using Cisco PIX Device Manager (PDM). PDM is a browser-based configuration tool designed to help you set up, configure, and monitor your PIX Firewall with a GUI. PIX Firewalls are placed at two different sites.
A tunnel is formed using IPsec. IPsec is a combination of open standards that provide data confidentiality, data integrity, and data origin authentication between IPsec peers.
Prerequisites
Requirements
There are no requirements for this document.
Components Used
The information in this document is based on Cisco Secure PIX 515E Firewalls with 6.x and PDM version 3.0.
Refer to Configuring a Simple PIX-to-PIX VPN Tunnel Using IPsec for a configuration example on the configuration of a VPN tunnel between two PIX devices using the Command Line Interface (CLI).
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
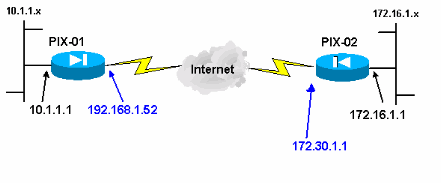
Network Diagram
This document uses this network setup:
Conventions
Refer to the Cisco Technical Tips Conventions for more information on document conventions.
Background Information
IPsec negotiation can be broken down into five steps, and includes two Internet Key Exchange (IKE) phases.
-
An IPsec tunnel is initiated by interesting traffic. Traffic is considered interesting when it travels between the IPsec peers.
-
In IKE Phase 1, the IPsec peers negotiate the established IKE Security Association (SA) policy. Once the peers are authenticated, a secure tunnel is created using Internet Security Association and Key Management Protocol (ISAKMP).
-
In IKE Phase 2, the IPsec peers use the authenticated and secure tunnel to negotiate IPsec SA transforms. The negotiation of the shared policy determines how the IPsec tunnel is established.
-
The IPsec tunnel is created and data is transferred between the IPsec peers based on the IPsec parameters configured in the IPsec transform sets.
-
The IPsec tunnel terminates when the IPsec SAs are deleted or when their lifetime expires.
Note: IPsec negotiation between the two PIXes fails if the SAs on both of the IKE phases do not match on the peers.
Configuration Procedure
Apart from other general configuration on the CLI of PIX to access it through the Ethernet 0 interface, use the commands http server enable and http server <local_ip> <mask> <interface> where <local_ip> and <mask> is the IP address and the mask of the workstation on which PDM is installed. The configuration in this document is for PIX-01. PIX-02 can be configured using the same steps with different addresses.
Complete these steps:
-
Open your browser and type https://<Inside_IP_Address_of_PIX> to access the PIX in PDM.
-
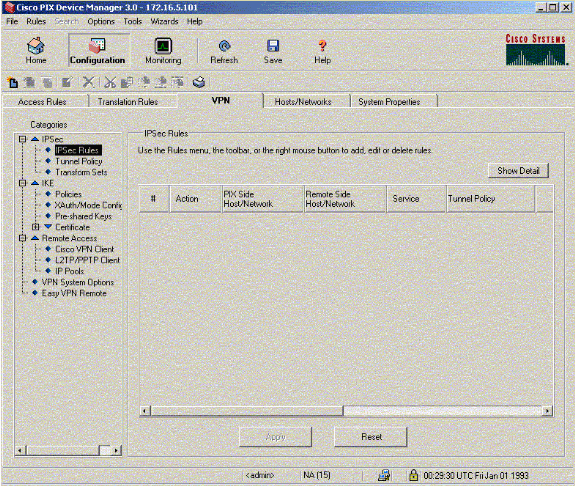
Click Configuration and go to the VPN tab.
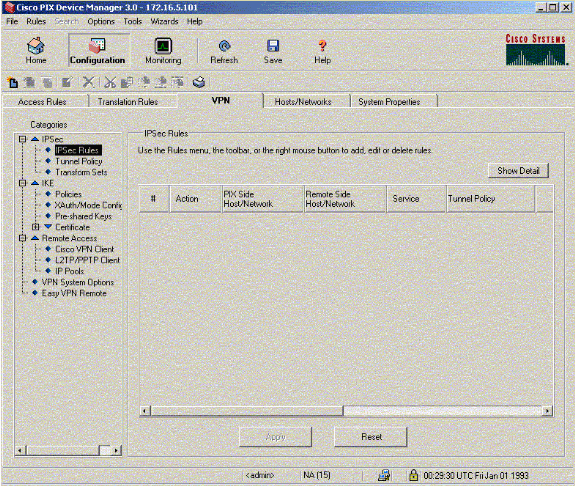
-
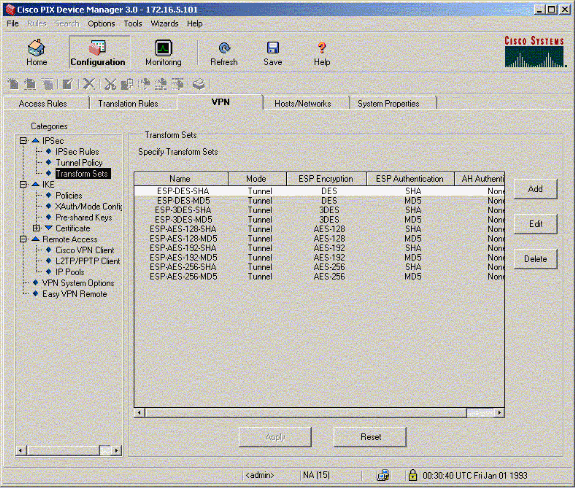
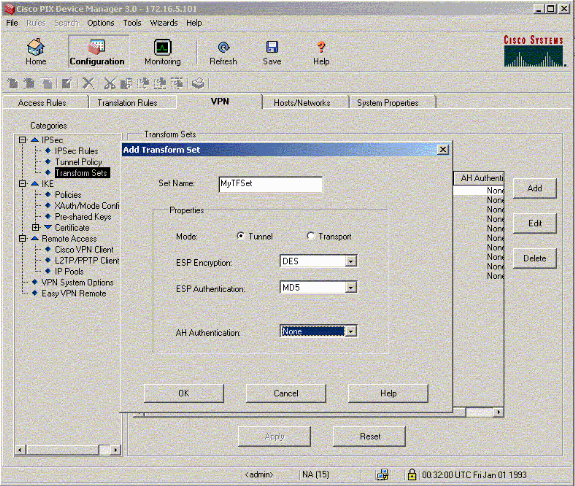
Click Transform Sets under IPSec to create a Transform set.
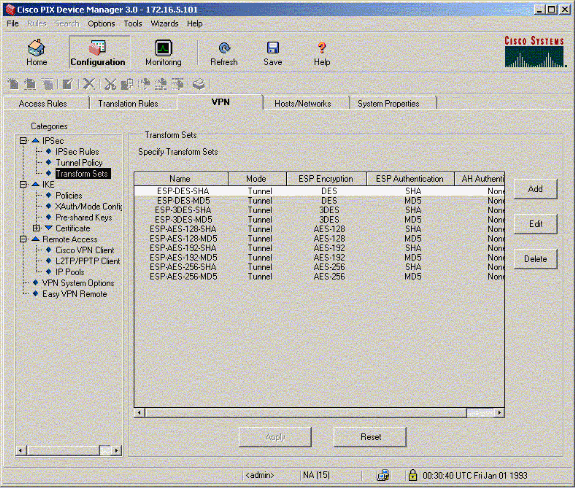
-
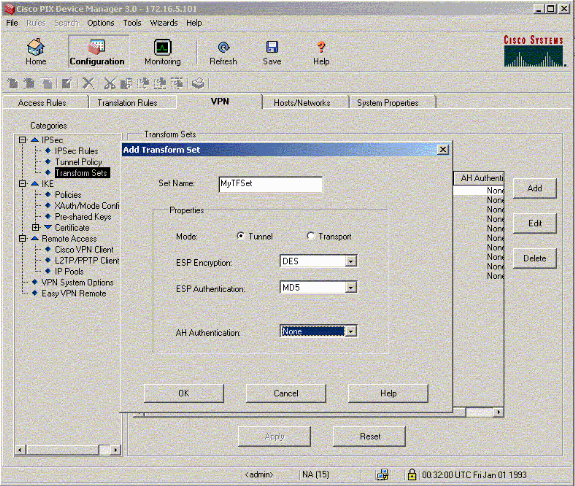
Click Add, select all the appropriate options, and click OK to create a new Transform set.
-
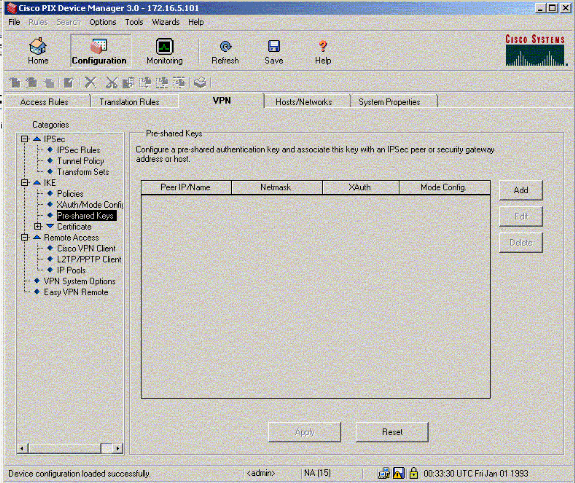
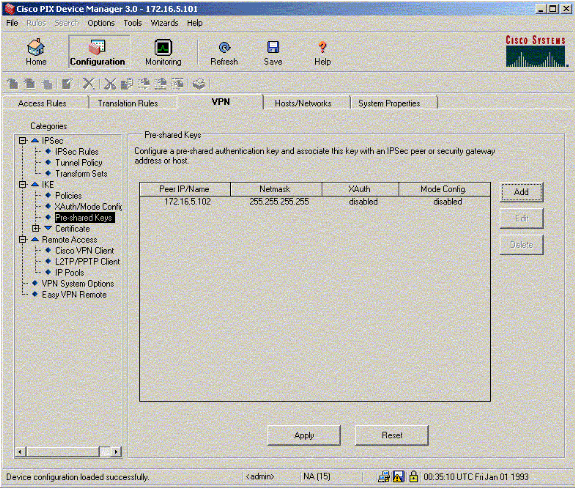
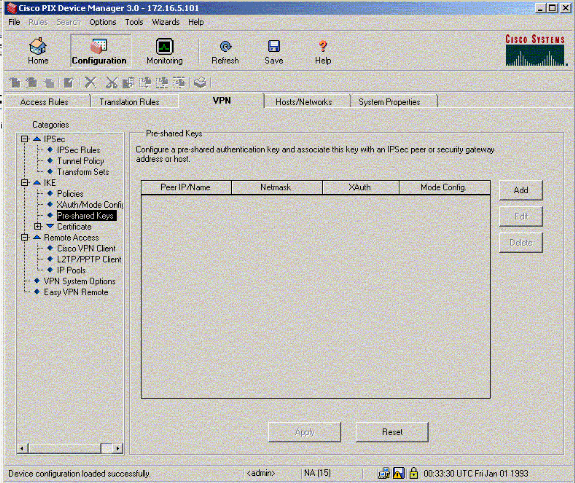
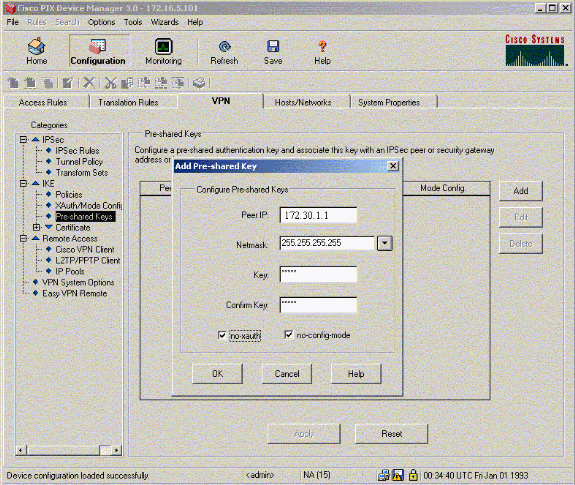
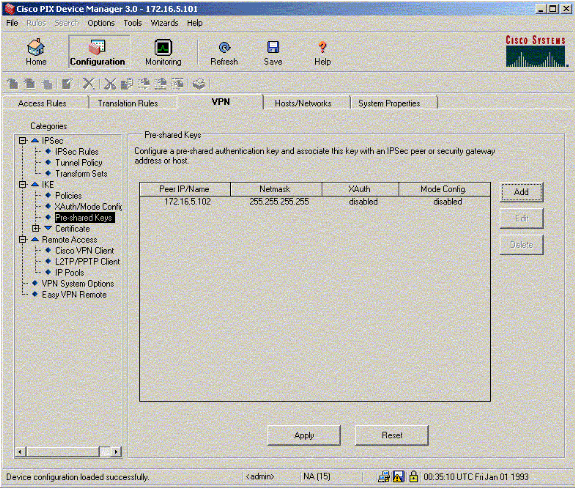
Click Pre-Shared Keys under IKE to configure pre-shared keys.
-
Click Add to add a new pre-shared key.
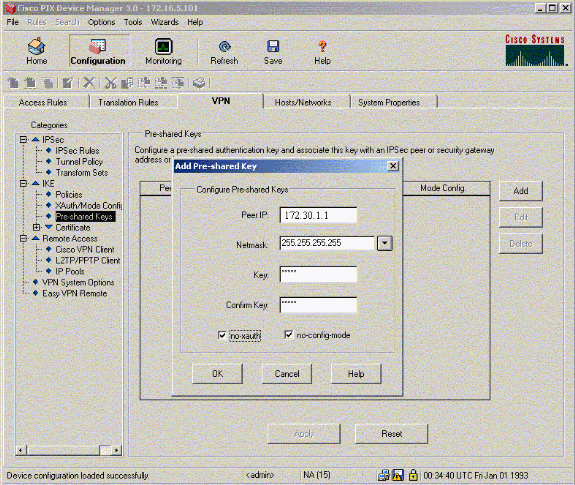
This window shows the key, which is the password for the tunnel association. This has to match on both sides of the tunnel.
-
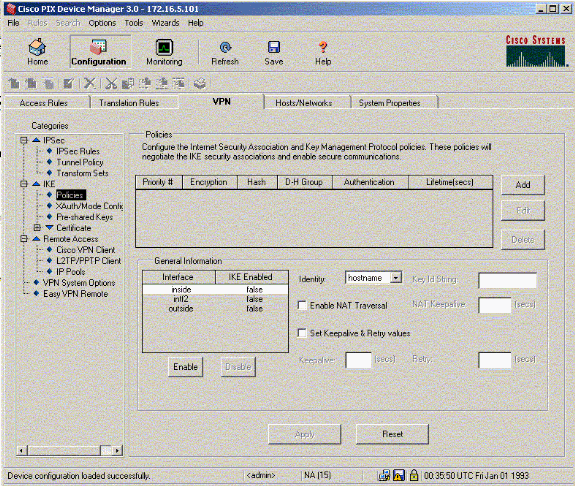
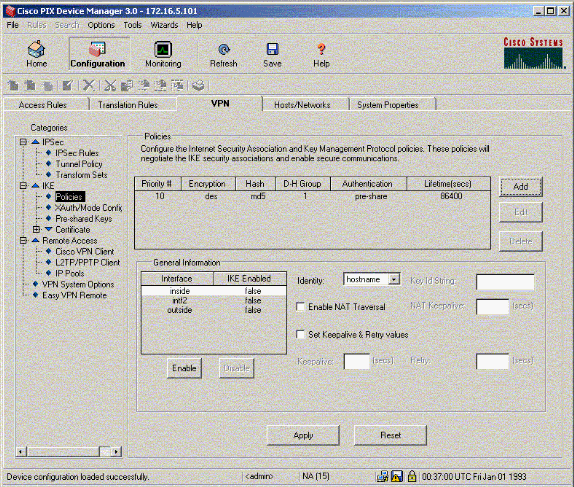
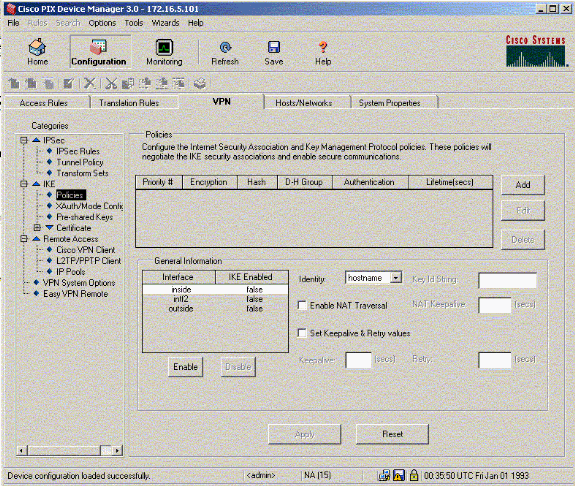
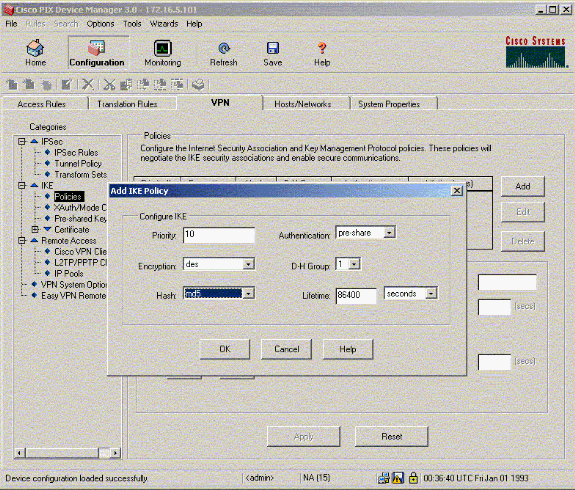
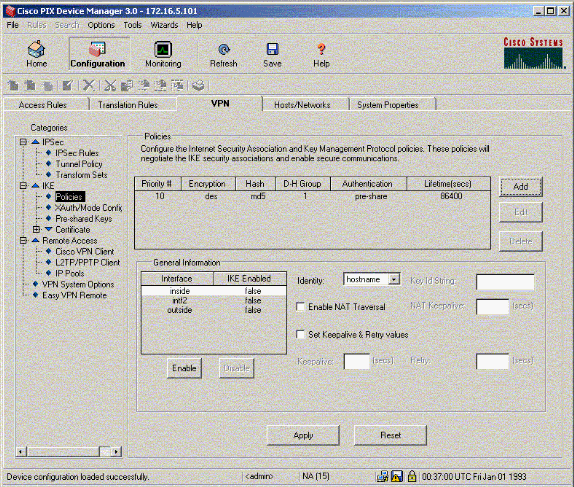
Click Policies under IKE to configure policies.
-
Click Add and fill in the appropriate fields.
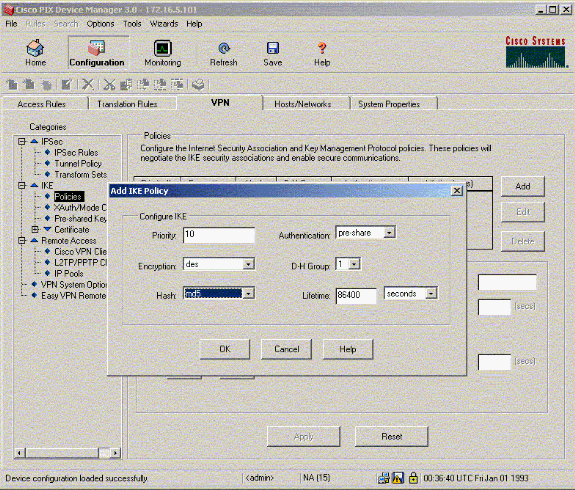
-
Click OK to add a new policy.
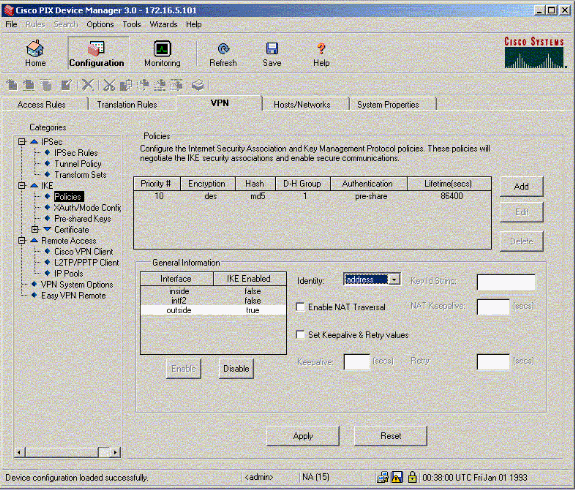
-
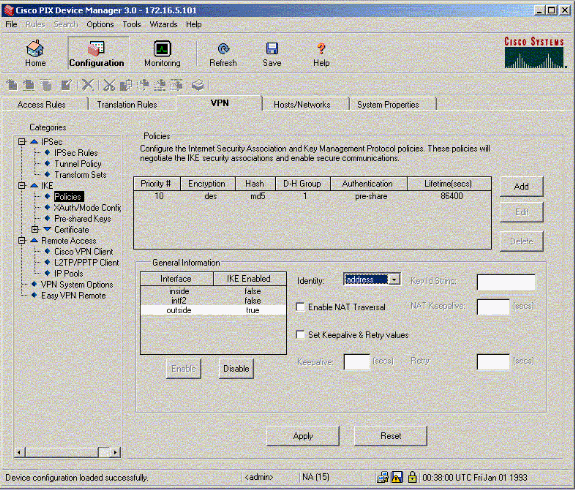
Select the outside interface, click Enable, and from the Identity pull down-menu select address.
-
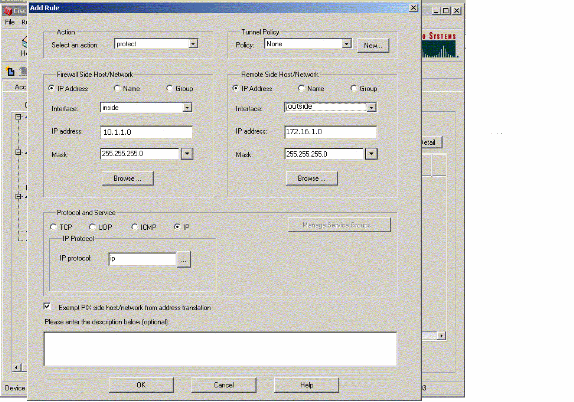
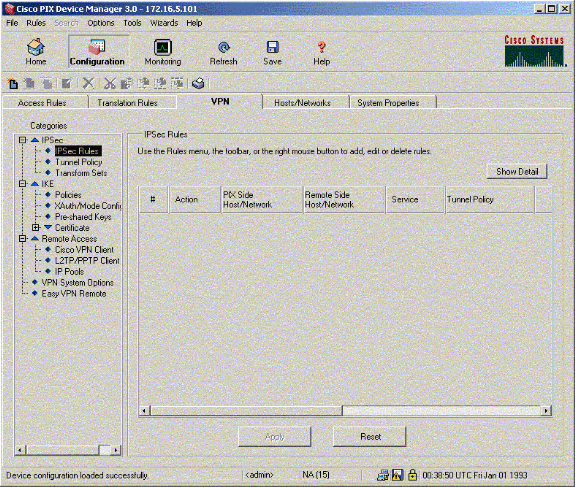
Click IPSec Rules under IPSec to create IPsec rules.
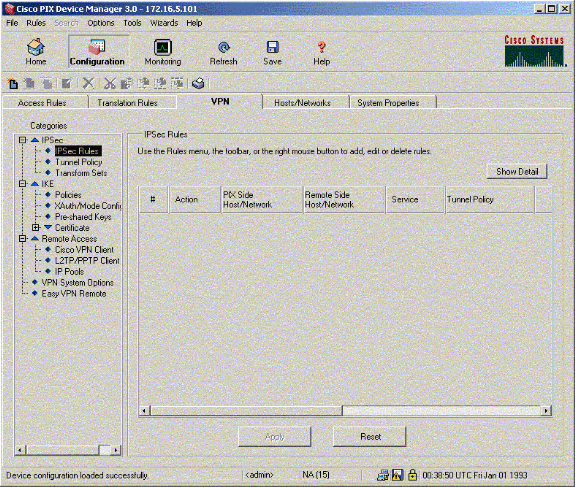
-
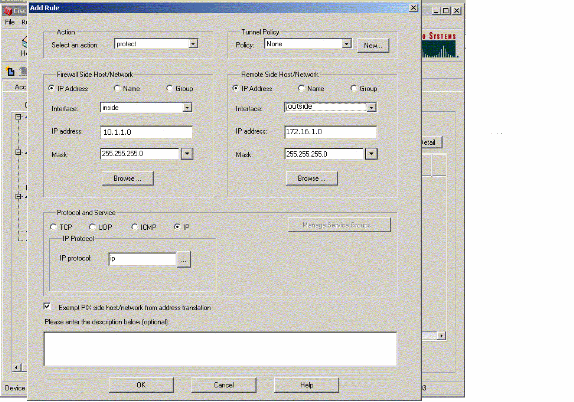
Fill in the appropriate fields.
-
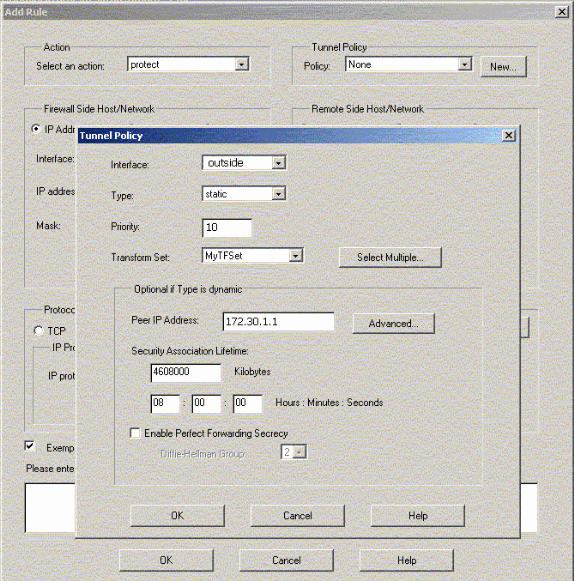
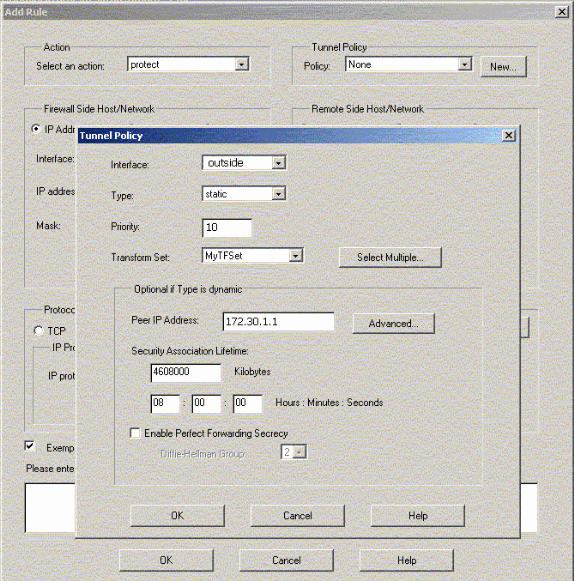
Click New in the Tunnel Policy. A Tunnel Policy window appears. Fill in the appropriate fields.
-
Click OK to see the configured IPsec rule.
-
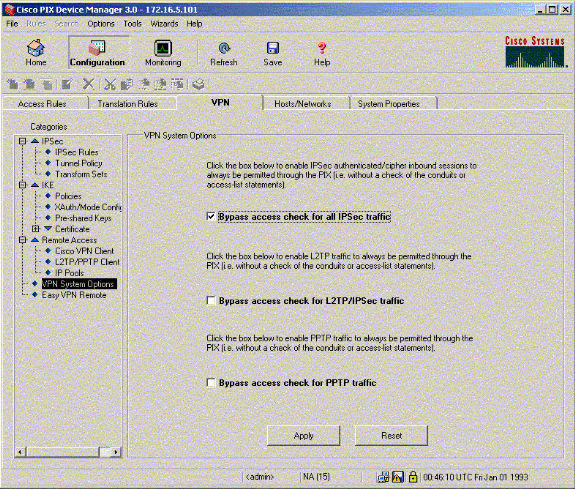
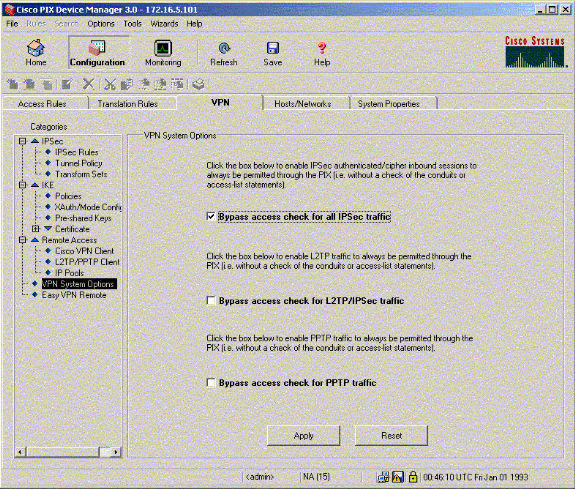
Click VPN Systems Options and check Bypass access check for all IPSec traffic.
Verify
If there is interesting traffic to the peer, the tunnel is established between PIX-01 and PIX-02.
The Output Interpreter Tool (registered customers only) (OIT) supports certain show commands. Use the OIT to view an analysis of show command output.
View the VPN Status under Home in the PDM (highlighted in red) in order to verify the formation of the tunnel.
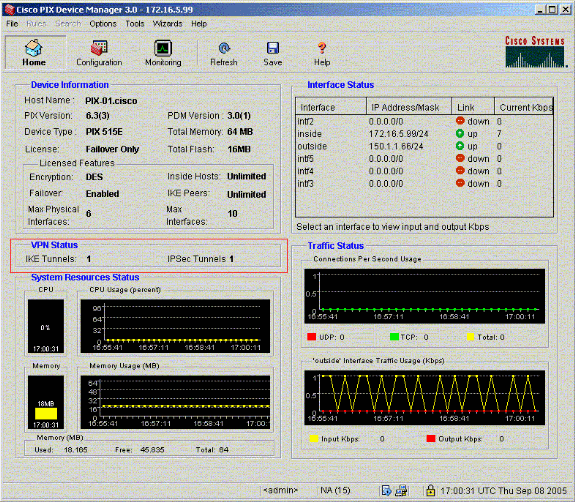
You can also verify the formation of tunnels using CLI under Tools in the PDM. Issue the show crypto isakmp sa command to check the formation of tunnels and issue the show crypto ipsec sa command to observe the number of packets encapsulated, encrypted, and so forth.
Note: The inside interface of the PIX cannot be pinged for the formation of the tunnel unless the management-access command is configured in the global confirguration mode.
PIX-02(config)#management-access inside PIX-02(config)#show management-access management-access inside
Troubleshoot
There is currently no specific troubleshooting information available for this configuration.
Related Information
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
08-Oct-2018 |
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback