Introduction
This document describes how to filter certain IP's so as to not be recorded by NetFlow.
Contributed by Vishal Kothari, Cisco TAC Engineer.
Prerequisites
Requirements
Cisco recommends that you have knowledge of Flexible NetFlow.
Components Used
The information in this document is based on these software and hardware versions:
- 3650 Switch
- Integrated Service Router (ISR) 4351 Router
Note: In order to achieve this required filtering under NetFlow, you will need to install AppxK9 License. For testing, you can make use of Right-To-Use (RTU) AppxK9 license.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Configure
In this section, you are required to filter the list of IPs’ that need not be recorded by NetFlow, which further means, that the router should not send out details about defined IP's source and destination in an ACL. How can you achieve this through flexible NetFlow, you will find out here.
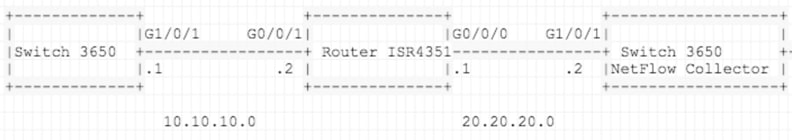
Network Diagram
Configurations
Prepare a list of all those Networks that you want to Filter out while sending it to the NetFlow Collector. In this example, deny/filter Telnet traffic is sent to a collector and permits all other traffic.
ISR4351 Configuration:
IP access-list extended acl-filter
deny tcp host 10.10.10.1 host 10.10.10.2 eq telnet
deny tcp host 10.10.10.2 eq telnet host 10.10.10.1
permit ip any any
flow record type performance-monitor NET-FLOW
match ipv4 tos
match ipv4 protocol
match ipv4 source address
match ipv4 destination address
match transport source-port
match transport destination-port
match interface output
match flow direction
match flow sampler
match application name
collect routing source as
collect routing destination as
collect routing next-hop address ipv4
collect ipv4 source mask
collect ipv4 destination mask
collect transport tcp flags
collect interface input
collect counter bytes
collect counter packets
collect timestamp sys-uptime first
collect timestamp sys-uptime last
!
!
flow exporter NET-FLOW
description NET-FLOW
destination 20.20.20.2
source Loopback28
transport udp 2055
!
!
flow monitor type performance-monitor NET-FLOW
record NET-FLOW
exporter NET-FLOW
class-map match-any class-filter
match access-group name acl-filter
!
policy-map type performance-monitor policy-filter
class class-filter
flow monitor NET-FLOW
interface Loopback28
ip address 10.11.11.28 255.255.255.255
interface GigabitEthernet0/0/1
ip address 10.10.10.2 255.255.255.0
negotiation auto
service-policy type performance-monitor input policy-filter
Verify
Use this section in order to confirm that your configuration works properly.
How to confirm if the networks have been filtered out when you send them out to NetFlow Collector?
In order to prove that you can take Embedded Packet Capture (EPC) on ISR4351 Gi0/0/0 (Interface pointing towards NetFlow Collector). Here is the configuration:
ip access-list extended CAP-FILTER
permit ip host 10.11.11.28 host 20.20.20.2
permit ip host 20.20.20.2 host 10.11.11.28
monitor capture CAP access-list CAP-FILTER buffer size 10 interface GigabitEthernet 0/0/0 both
monitor capture CAP start
++ TEST I
3650: -
telnet 10.10.10.2
Trying 10.10.10.2 ... Open
No Packets were captured for Telnet traffic under EPC, the reason being that the traffic got denied under Access Control List (ACL) (ACL-filter) and rest everything has been permitted.
show monitor capture CAP buffer brief
-------------------------------------------------------------
# size timestamp source destination protocol
-------------------------------------------------------------
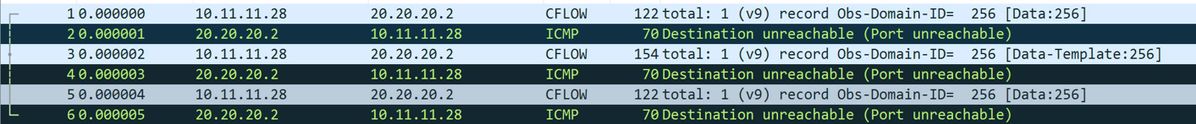
Now in Test 02, generate ping traffic in order to see if it gets matched under EPC:
++ TEST II
3650: -
ping 10.10.10.2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.10.10.2, timeout is 2 seconds:
!!!!!
ISR4351:
show monitor capture CAP buffer brief
-------------------------------------------------------------
# size timestamp source destination protocol
-------------------------------------------------------------
0 122 0.000000 10.11.11.28 -> 20.20.20.2 UDP
1 70 0.001998 20.20.20.2 -> 10.11.11.28 ICMP
Troubleshoot
There is currently no specific troubleshooting information available for this configuration.