Cisco Access Registrar 4.0
Available Languages
PRODUCT OVERVIEW
HIGHLIGHTS, FEATURES, AND BENEFITS
Cisco Access Registrar 4.0 Highlights
• Expanded Extensible Authentication Protocol (EAP) Support-Cisco Access Registrar adds support for Flexible Authentication via Secure Tunneling (FAST) and Subscriber Identity Module (SIM) draft 16.
• Change of Authorization Support-Cisco Access Registrar 4.0 adds Change of Authorization (CoA) support per RFC3576.
• RADIUS Query of Identity Session Cache-In addition to XML query, this version add RADIUS query of the real-time information cache of active users.
• Web-Based Graphical User Interface (GUI)-AR 4.0 introduces a GUI administration interface for basic configuration tasks, session display, statistics and log monitoring.
• Windows Domain Authentication-AR can now authenticate requests to a Windows database.
• RADIUS Client Wildcarding-Specify multiple RADIUS clients with a single definition.
Benefits
• Cisco Access Registrar supports multiple access technologies (dial, wholesale dial, broadband, mobile wireless, wireless LAN, and public wireless LAN) with a single AAA platform.
• Provides service providers with an off-the-shelf, standards-based RADIUS server that offers the flexibility and extensibility previously only available by maintaining internally built versions of public-domain RADIUS software.
• Enables service providers to focus their businesses on specific areas of service delivery by supporting additional wholesale, outsourcing, and roaming service scenarios using proxy RADIUS.
• Reduces operational costs and speeds service rollout by supporting integration with provisioning, billing, and other service-management components using directory or relational database management system (RDBMS) support and scriptable configuration interfaces.
• Efficiently manages resource use by supporting centralized IP address assignment and session limit enforcement across access devices spanning multiple geographic regions and across multiple Cisco Access Registrar servers.
• Allows service providers to extend competitive advantages by rapidly deploying the latest wireless technologies.
PRODUCT ARCHITECTURE
• Whether authentication against a Lightweight Directory Access Protocol (LDAP) directory or Oracle database is required
• Whether a request should be forwarded to an external RADIUS server
• What type of accounting is required
• Whether session limits apply
• Whether an IP address pool has been assigned
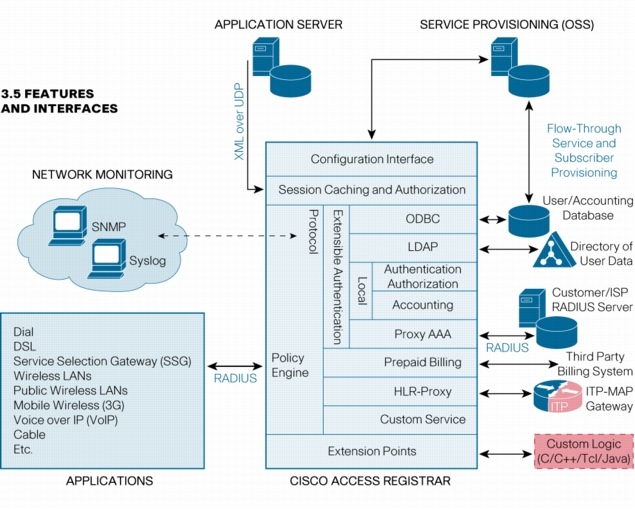
Figure 1. Cisco Access Registrar Architecture
FEATURES
Authentication and Authorization
• High-speed internal embedded user database
• Easy, logical grouping of users
• Easy return attributes and check-item configuration
• Ability to enable and disable user access
• User information can be stored in external datastores
• LDAP directory or Oracle or MySQL database support
– Store return and check-items attributes
– Datastore schema independent
– Add custom logic based on information in user's record
• Authentication to a Windows database
• Advanced RADIUS proxy support for service provider environments
– Include proxy attribute filtering
• EAP support
– Message Digest Algorithm 5 (MD5), LEAP, PEAP (with Microsoft Challenge Handshake Authentication Protocol [MS-CHAP] v2, Generic Token Card (GTC), SIM , TLS, FAST
– EAP Proxy
• HTTP digest authentication for Session Initiation Protocol (SIP) and Web servers
• IETF RADIUS tunnel support (RFC 2867, RFC 2868)
• Automatic and customizable Reply-Message generation
Accounting
• Local file
– Store accounting records in single file or multiple files
– Automatic file rollover based on file age, size, or specific time
• Proxy
– Option to ignore acknowledgements and continue processing
• Database
– Write accounting records directly to an Oracle or MySQL database
– Schema independent
– Buffering option for higher throughput and fault tolerance
Proxy/Database/LDAP Configuration
• Define a list of remote systems to be used in failover or round-robin modes
• Accept All, Reject All, and Drop Packet outage policies available when no remote systems are available
• Define the individual characteristics of each remote system; for example, ports, timeouts, retries, or reactivate timers
• Sophisticated algorithms to detect status of remote systems
Request Processing Decisions
• Process requests using different methods; for example, use LDAP for some access requests, the internal database for others
• Process requests using a combination of these methods; for example, store an accounting request to a local file and proxy it to a number of remote RADIUS servers, in serial or parallel
• Split authentication and authorization by selecting one method for authentication and another for authorization (One-Time Password [OTP] server and Oracle database, for example)
• Decide which method to use based on attributes in the request or on Cisco Access Registrar's `environment' variables, such as source or destination IP address or UDP port
• Easy method selection based on DNS domain, username prefix, dialed number, calling number, or network access server (NAS), using the Cisco Access Registrar Policy Engine
• Built-in feature to track user sessions and allocate resources
• Enforcement of session limits per user and per group
• Allocation of addresses from IP pools
• Allocation of home agents and on-demand address pools
• Real-time query of the session table using the command-line interface (CLI), XML over UDP, or RADIUS
• Add custom information to the session table
• Configure which attributes to store in the session table
• Manual release of sessions and resources
• Query and release sessions based on session age, username, NAS, and other criteria
• Release sessions and generate PoD
• Automatic session release when accounting stop is lost (inactivity timeout)
• Automatic session release when accounting on/off is detected (system accounting)
• In an environment with multiple Cisco Access Registrars, designate one Cisco Access Registrar to manage all sessions to avoid bypass of session limits and to allocate IP addresses and other resources centrally
• Session information is not lost even if Cisco Access Registrar or the system is restarted
• Session tracking for accounting-only servers
• Configure session key on calling number or other attributes
• Send CoA request
System Tuning and System Configuration
• Configure Cisco Access Registrar to listen on multiple UDP ports
• Specify which network interfaces to use
• Set the number of simultaneous requests to be processed
• Enable access accept logging
• Regular and advanced duplicate detection features
• Extensible attribute dictionary
– Populated with latest attribute definitions, including third-party, vendor-specific attributes
– Easy addition of new attributes
– Variable-length vendor type in vendor-specific attributes
• Specify log file rollover rules
Troubleshooting and Monitoring
• Multilevel debugging output
• Real-time query of processing counters
• Reset processing counters without restarting Cisco Access Registrar
• Query status of all Cisco Access Registrar processes and utilities
• Log files for each Cisco Access Registrar process
• Audit log of all configuration changes
• Direct logs to a syslog server
• RADIUS Simple Network Management Protocol (SNMP) RFC 2618-21 support
• SNMP traps generated for critical events
• Utility to generate RADIUS requests
Configuration
• Powerful command-line configuration utility with interactive/noninteractive and full and view-only modes
• Noninteractive modes allow for configuration automation and operations support system (OSS) integration
• Dynamic configuration feature allows configuration changes to take effect without a server restart
• Command and value recall, inline editing, autocommand completion, and a context-sensitive list of options
• Web-based interface for basic tasks and monitoring
• Specify multiple RADIUS clients with a single definition
Resilience
• Automatic configuration replication to other Cisco Access Registrar servers (server redundancy)
• Specify lists of alternate remote systems for each processing method (remote-system redundancy)
• Specify multiple methods to process a request (processing-method redundancy)
• Automatic server restart
Customization
• Add custom logic to the request processing flow using Tool Command Language (TCL), C or C++, or Java
– Access request and response packets
– Modify processing decisions in real time
– Multiple call-out points to target specific requests
• Create custom processing methods
Solutions
• Cisco PDSN for CDMA2000 mobile wireless
– Home agent allocation for balanced home agent access
– Null password support
– Multiple accounting start/stop detection for roaming users
– CDMA2000 vendor-specific attribute support
– Prepaid billing
– QoS and Remote Address Accounting attributes support
– PoD during PDSN handoff
– MN-HA shared key distribution for mobile IP
– DNS update for IP reachability
– Change of Authorization
• Public wireless LAN solution for service providers
• Cisco IOS® Software On-Demand Address Pool Manager
• Broadband aggregation
• Other solutions
– Cisco Gateway GPRS Support Node (GGSN) for GPRS mobile wireless
– Cisco Any Service, Any Port (ASAP) solutions
SYSTEM REQUIREMENTS
Table 1. System Requirements
| Feature |
Description |
|
Disk Space
|
175 MB (minimum) |
|
Hardware
|
Sun SPARC or x86 |
|
Memory
|
64 MB (minimum) |
|
Software
|
Solaris 8 or 9 for Sun SPARC, RedHat Linux 7.3 for x86 |
ORDERING INFORMATION
Table 2. Ordering Information
| Product Name |
Part Number |
| AR-STANDARD |
AR-4.0-BASE-K9 |
| AR-CPU |
AR-4.0-ADD-CPU |
| AR-PREPAID |
AR-4.0-ADD-PRPAID |
| AR-HLR |
AR-4.0-ADD-HLR |
DOWNLOAD THE SOFTWARE
SERVICE AND SUPPORT
FOR MORE INFORMATION
 Feedback
Feedback